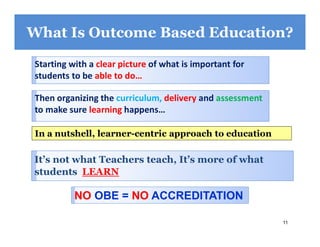
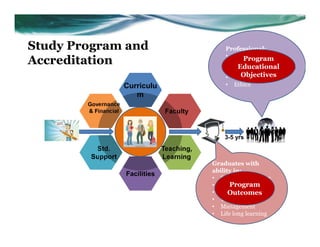
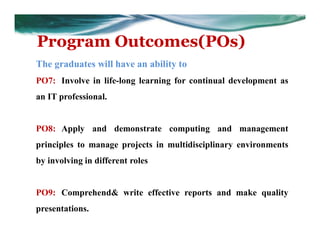
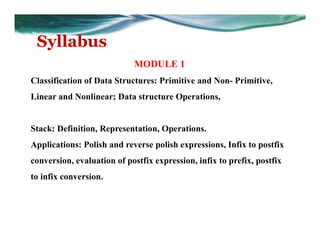
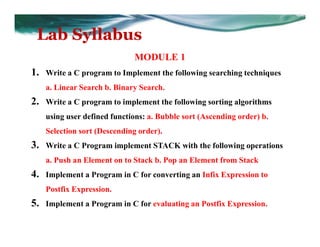
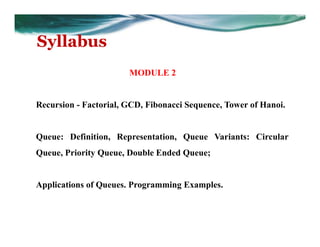
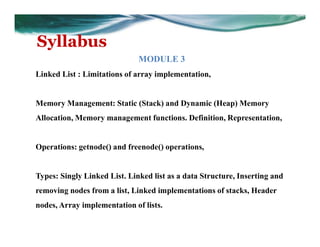
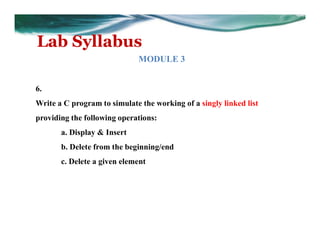
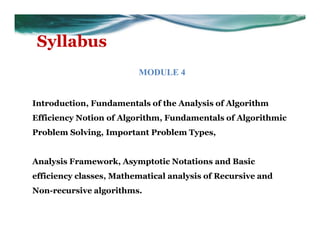
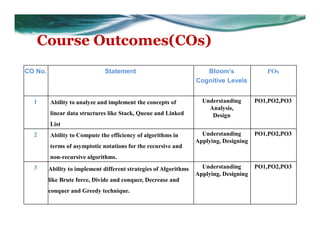
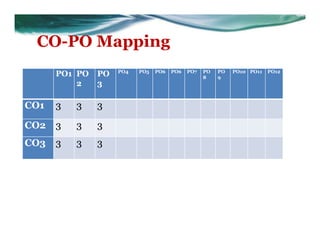
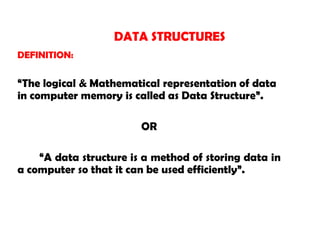
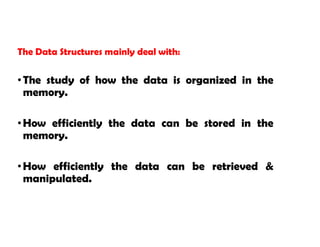
This document provides an overview of data structures and algorithms concepts through a presentation. It begins with an introduction to outcome based education and accreditation standards. It then covers Bloom's taxonomy, vision/mission statements, and defines key terms like program outcomes, course outcomes, and mappings between them. Several data structures are defined, like stacks, queues, and linked lists. Algorithms topics covered include recursion, sorting, searching and complexity analysis. Specific course details are provided like learning objectives, syllabus, and outcome mappings.



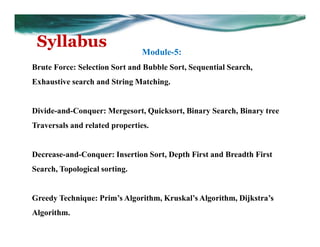
![Syllabus
Data Structures with Algorithms
[As per Choice Based Credit System (CBCS) scheme]
Subject Code: 20MCA11
CIE Marks: 40 SEE Marks: 60 SEE Hours: 03
Course learning objectives:
This course (20MCA11) will enable student to
• Familiarize the knowledge of various types of data structures, operations and
algorithms sorting and searching operations.
• Use the concepts of Stack, Queue, Lists, Trees, Hashing, Searching and
Sorting techniques
• Build solutions for real world problems using concepts of data structures
• Familiarize with different strategies of algorithms.
• Can apply different strategies to solve applications.](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-22-320.jpg)
![// C function for Push Operation.
void push() //function ---1
{
/* check for overflow of stack */
if (top == stack_size-1)
{
printf(“ stack overflow);
return;
}
top = top+1;
S[top] = item;
}](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-46-320.jpg)
![// C function to delete an item from stack.
int pop() //function----2
{
int item_deleted;
if (top == -1)
{
printf(“ Stack Underflow “);
return 0;
}
item_deleted = S[top--];
return item_deleted;
}](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-49-320.jpg)
![Display stack items:
The contents of the stack are displayed from the bottom
to top.
// C function to display the contents of stack/
Void display() //function----3
{
int i;
if ( top == -1 )
{ Printf(“ stack is empty”); }
for( i=0; i<=top; i++ )
{
printf(“%d”, S[i]);
}
}](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-50-320.jpg)
![// C program to implement stack using arrays;
#include <stdio.h>
#include < process.h>
#define STACK_SIZE 5;
int top;
int s[10];
int item;
//function ---1
//function----2
//function----3](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-51-320.jpg)

![General procedure to convert from infix to postfix form :
Step 1 :
initialize top and stack of top
top = -1
s[++top] = ‘#’
j = 0
Step 2 :
As long as the precedence value of the symbol on top of
the stack is greater than the precedence value of the current
input symbol, pop an item from the stack and place it in the
postfix expression.
while ( F(s[top]) > G(symbol) )
{
postfix[ j++ ] = s[ top-- ]
}](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-68-320.jpg)
![Step 3 :
Once the condition in while loop is failed, if the
precedence of the symbol on top of the stack is not equal to
the precedence value of the current input symbol, push the
current symbol on to the stack. Otherwise , delete an item
from the stack but do not place in the postfix expression.
if ( F(s[top]) != G(symbol) )
s[++top] = symbol
else
top--;
Step 4 :
After the complete execution of step 2 and step 3, pop
remaining symbols from stack to postfix expression.
while ( s[top] != ‘#’ )
postfix[j++] = s[top--]](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-69-320.jpg)
![* complete trace of the algorithm :
( A + ( B – C ) * D )
Stack S[top] Symbol F(s[top]) > G(symbol) Postfix
# #
# # ( ( -1 > 9 ) push (
#( ( A ( 0 > 7 ) push A
#(A
#(
A
(
+ ( 8 > 1 ) pop A
( 0 > 1 ) push +
A
#(+ + ( ( 2 > 9 ) push ( A
#(+( ( B ( 0 > 7 ) push B A
#(+(B
#(+(
B
(
- ( 8 > 1 ) pop B
( 0 > 1 ) push -
AB
#(+(- - C ( 2 > 7 ) push C AB
#(+(-C
#(+(-
#(+(
C
-
(
) ( 8 > 0 ) pop C
( 2 > 0 ) pop –
( 0 = 0 ) pop (
Don’t place in postfix expr
ABC
ABC-](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-70-320.jpg)
![* complete trace of the algorithm :
( A + ( B – C ) * D )
Stack S[top] Symbol F(s[top]) > G(symbol) Postfix
#(+ + * ( 2 > 3 ) push * ABC-
#(+* * D (4 > 7) push D ABC-
#(+*D
#(+*
#(+
#(
D
*
+
(
) ( 8 > 0 ) pop D
( 4 > 0 ) pop *
( 2 > 0 ) pop +
( 0 = 0 ) pop (
Don’t place in postfix expr
ABC-D
ABC-D*
ABC-D*+
# # ABC-D*+](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-71-320.jpg)
![/* C function to convert from infix into postfix expression.
void infix_postfix(char infix[], char postfix[])
{ //function 3
int top; int j; int I;
char s[30]; char symbol;
top=-1; Step : 1
S[++top]= ‘#’;
j=0;
for(i=0; i<strlen(infix); i++)
{
Symbol=infix[i];](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-74-320.jpg)
![/* if stack precedence greater , remove symbol from
stack and place into postfix. */
while ( F(s[top]) > G(symbol) ) step : 2
{
postfix[j] = s[top--];
j++;
}
if ( F(s[top]) != G(symbol) ) step : 3
S[++top] = symbol;
else
top--;
}](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-75-320.jpg)
![/* pop remaining symbols and place them in
postfix expression
while ( s[top] != ’#’ ) step : 4
{
postfix[j++] = s[top--];
}
postfix[j]=’0’;
}](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-76-320.jpg)
![// C program to convert an infix expression to postfix
expression
# include < stdio.h>
# include < string.h >
/* include function 1, function 2, function 3. */
void main ()
{
char infix[20];
char postfix[20];
printf (“ Enter the valid infix expression”);
scanf (“ %s ”, infix );
infix_postfix ( infix, postfix);
printf (“ The postfix expression is “ );
printf (“%s”,postfix);
}](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-77-320.jpg)
![General procedure to convert from infix to postfix form :
Step 1 :
initialize top and stack of top
top = -1
s[++top] = ‘#’
j = 0.( reverse the infix expression )
Step 2 :
As long as the precedence value of the symbol on top of
the stack is greater than the precedence value of the current
input symbol, pop an item from the stack and place it in the
postfix expression.
while ( F(s[top]) > G(symbol) )
{
postfix[ j++ ] = s[ top-- ]
}](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-79-320.jpg)
![Step 3 :
Once the condition in while loop is failed, if the
precedence of the symbol on top of the stack is not equal to
the precedence value of the current input symbol, push the
current symbol on to the stack. Otherwise , delete an item
from the stack but do not place in the postfix expression.
if ( F(s[top]) != G(symbol) )
s[++top] = symbol
else
top--;
Step 4 :
After the execution of step 2 and step 3, pop remaining
symbols from stack to postfix expression.
while ( s[top] != ‘#’ )
postfix[j++] = s[top--]](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-80-320.jpg)
![* complete trace of the algorithm :
( A + ( B – C )) = ) ) C – B ( + A (
i.e., CB-A+ = +A-BC
Stack S[top] Symbol F(s[top]) > G(symbol) Postfix
# # ) -1 > 9 push ‘)’
#) ) ) 0 > 9 push ‘)’
#)) ) C 0 > 7 push ‘C’
#))C
#))
C
)
- 8 > 2 pop ‘C’
0 > 2 push ‘-’
C
#))- - B 1 > 7 push ‘B’ C
#))-B
#))-
#))
B
-
)
( 8 > 0 pop ‘B’
1 > 0 pop ‘-’
0 > 0 pop ‘)’
CB
CB-
#) ) + 0 > 2 push ‘+’ CB-
#)+ + A 1 > 7 push ‘+’ CB-
#)+A
#)+
#)
A
+
)
( 8 > 0 pop ‘A’
1 > 0 pop ‘+’
0 > 0 pop ‘)’
CB-A
CB-A+](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-81-320.jpg)
![/* C function to convert from infix into prefix expression.
void infix_prefix(char infix[], char prefix[])
{ function 3
int top; int j; int I;
char s[30]; char symbol;
top=-1; Step : 1
S[++top]= ‘#’;
j=0;
strrev ( infix );
for(i=0; I < strlen (infix); i++)
{
Symbol=infix[i];](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-84-320.jpg)
![/* if stack precedence greater , remove symbol from
stack and place into postfix. */
while ( F(s[top]) > G(symbol) ) step : 2
{
prefix[j] = s[top--];
j++;
}
if ( F(s[top]) != G(symbol) ) step : 3
S[++top] = symbol;
else
top--;
}](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-85-320.jpg)
![/* pop remaining symbols and place them in
postfix expression
while ( s[top] != ’#’ ) step : 4
{
prefix[j++] = s[top--];
}
prefix[j]=’0’;
strrev (prefix );
}](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-86-320.jpg)
![// C program to convert an infix expression to prefix expression
# include < stdio.h>
# include < string.h >
/* include function 1, function 2, function 3. */
void main ()
{
char infix[20];
char prefix[20];
printf (“ Enter the valid infix expression”);
scanf (“ %s ”, infix );
infix_prefix ( infix, prefix);
printf (“ The postfix expression is “ );
printf (“%s”, prefix);
}](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-87-320.jpg)
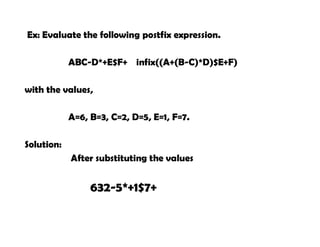
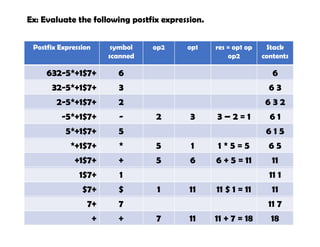
![Evaluation of postfix expression :
Algorithm:
Step 1 : Scan the symbol from left to right.
Step 2: If the scanned symbol is an operand, push it on
to the stack.
Step 3: If the scanned symbol is an operator, pop two
elements from the stack
The first popped element is operand 2 and the
second popped element is operand1
Op2 = s[top--];
Op1 = s[top--];](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-88-320.jpg)
![void main()
{
double s[20] , res , op1 , op2 ;
int top, i ;
char postfix[20] , symbol ;
top = -1;
Printf(“ enter the postfix expression”);
Scanf(“%s”, postfix);
for ( i=0; i<strlen(postfix); i++ )
{
Symbol = postfix[i];](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-93-320.jpg)
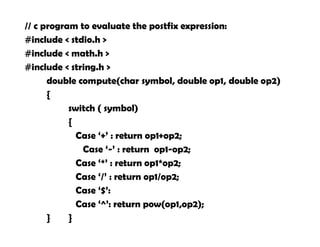
![if ( isdigit(symbol))
S[top++]= symbol;
else
{
op2 = s[top--];
op1 = s[top--];
res = compute(symbol, op1,op2);
S[++top] = res;
}
}
res = s[top--];
printf(“ the result is %fn”, res);
}](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-94-320.jpg)
![Ex; to check whether a give string is palindrome or not using
stack.
# include <stdio.h>
# include <string.h>
int is_palindrome( char str[])
{
int i, top = -1;
char s[30], stk_item;
/* push all the characters of the given string
for( i=0; i<strlen(str); i++ )
{
S[++top]= str[i];
}](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-95-320.jpg)
![/* check whether the string is palindrome or not.
for (i=0; i<strlen(str);i++)
{
Stk_item = s[top--];
if (str[i] != stk_item)
return 0;
}
return 1;
}](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-96-320.jpg)
![void main()
{
Char str[20];
printf(“enter string”);
Scanf(“%s”, str);
if (is_palindrome(str))
printf(“ the string is palindrome”);
else
printf(“ the string is not a palindrome”);
}](https://image.slidesharecdn.com/dsmod1-230705110034-0b816dc0/85/ds_mod1-pdf-97-320.jpg)