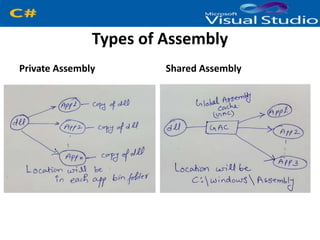
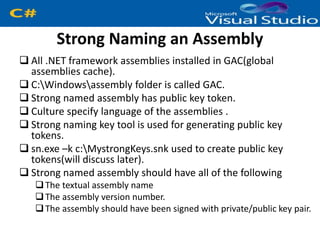
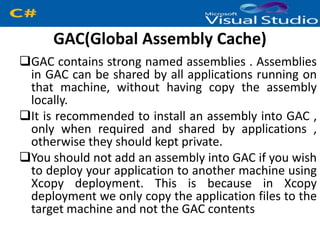
This document discusses assemblies in .NET. It begins with an introduction to assemblies, which are compiled .NET code files with the extension .exe or .dll. Assemblies include metadata and intermediate language code. There are two types of assemblies: private assemblies used only by one application, and shared assemblies stored in the global assembly cache (GAC) to be used by multiple applications. The document then covers strong naming assemblies, which involves assigning an assembly a unique name, version number, culture, and public key for deployment and security. Finally, it discusses the GAC which stores strongly named assemblies to be shared across applications on a machine.