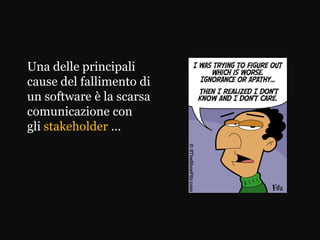
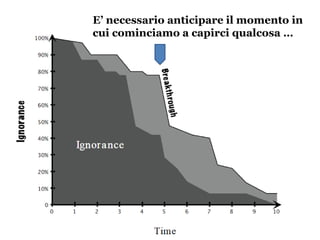
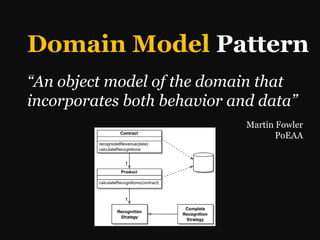
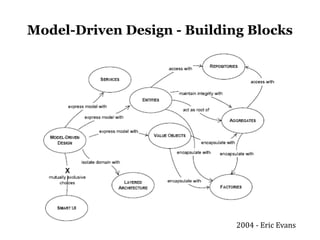
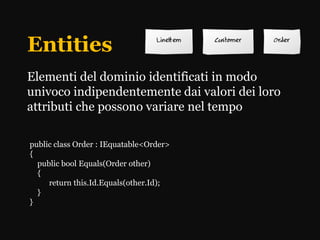
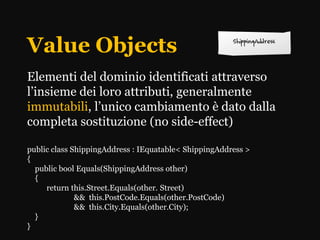
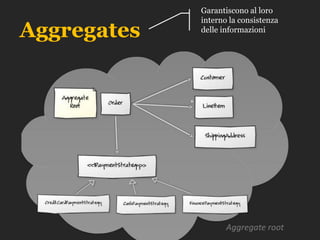
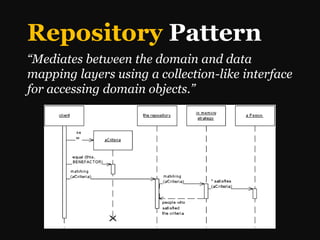
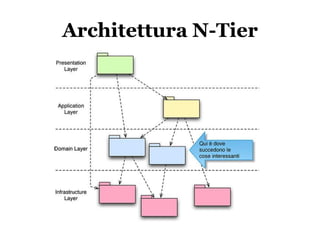
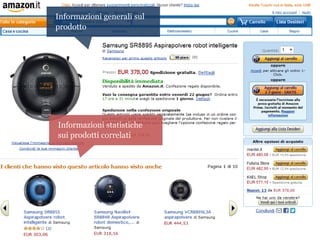
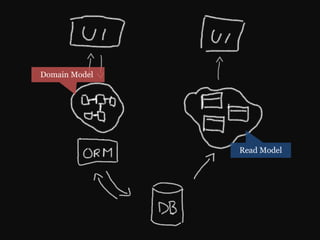
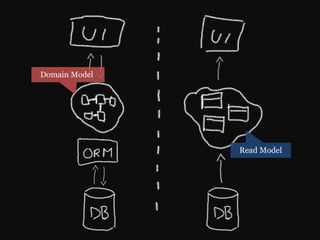
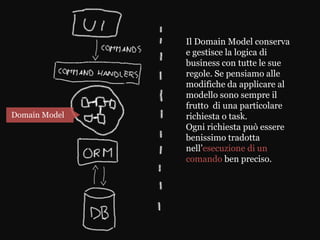
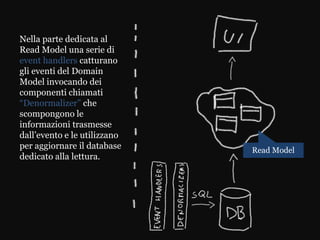
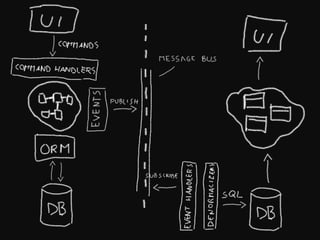
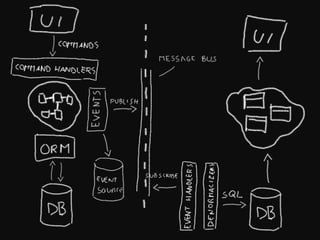
Il documento discute il Domain Driven Design (DDD) come un insieme di principi per migliorare il processo di sviluppo software, enfatizzando l'importanza di una comunicazione efficace tra gli stakeholder e l'uso di un linguaggio comune. Illustra la necessità di creare modelli concettuali del dominio e separare i modelli di dominio e read model per gestire logicamente e efficacemente le operazioni di business. Presenta anche concetti chiave come aggregates, value objects, e il pattern repository per ottimizzare l'accesso ai dati.