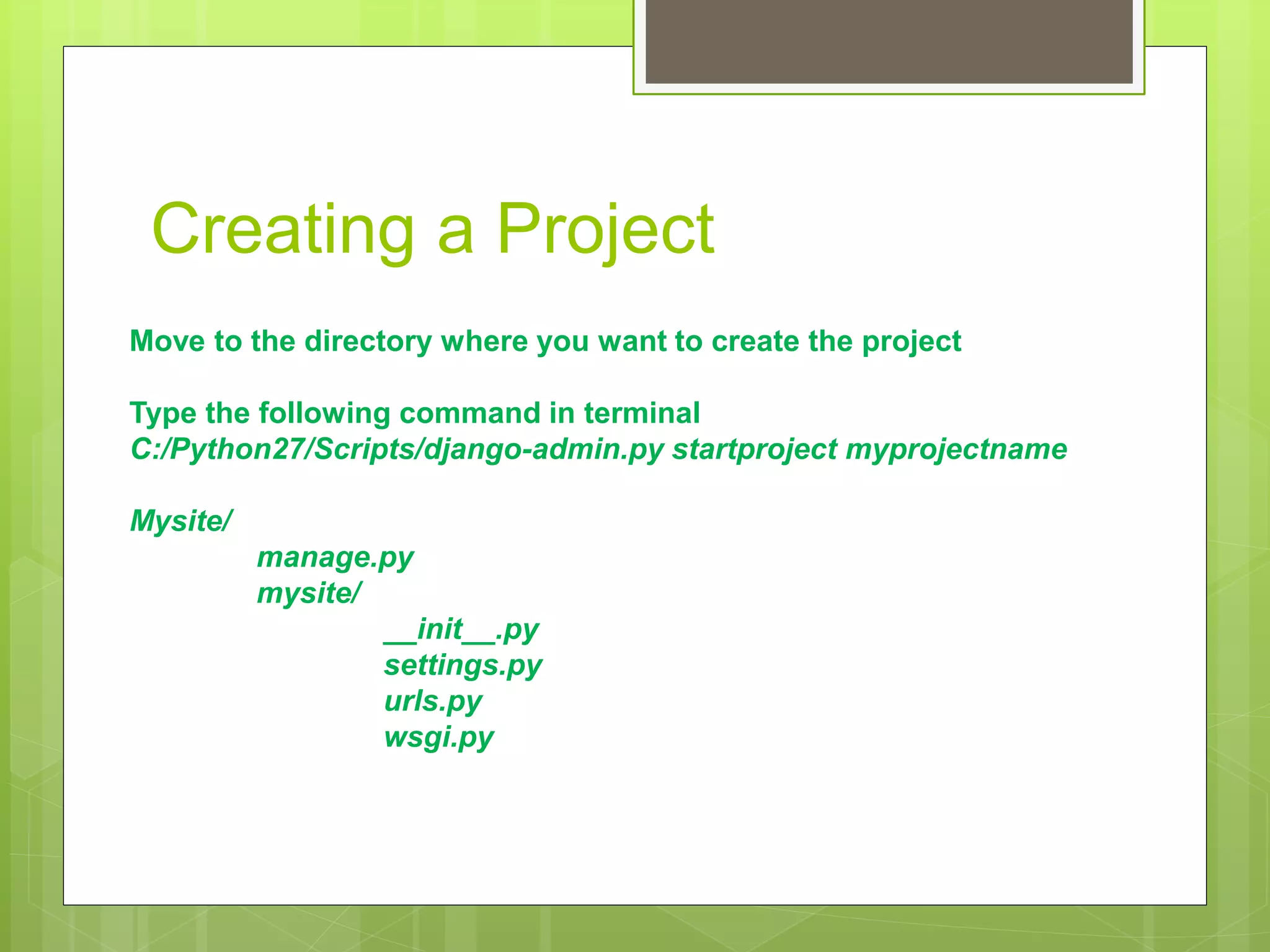
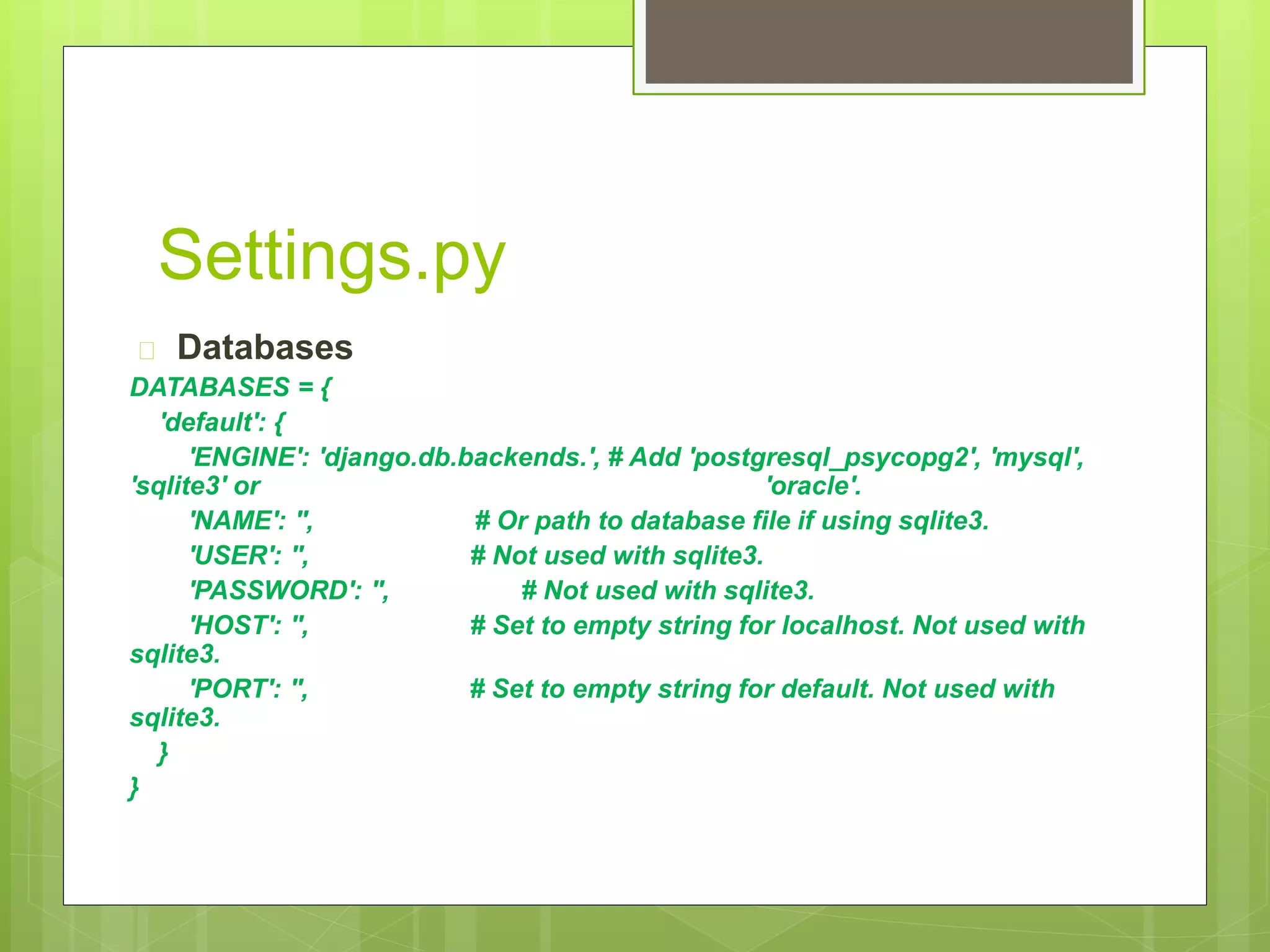
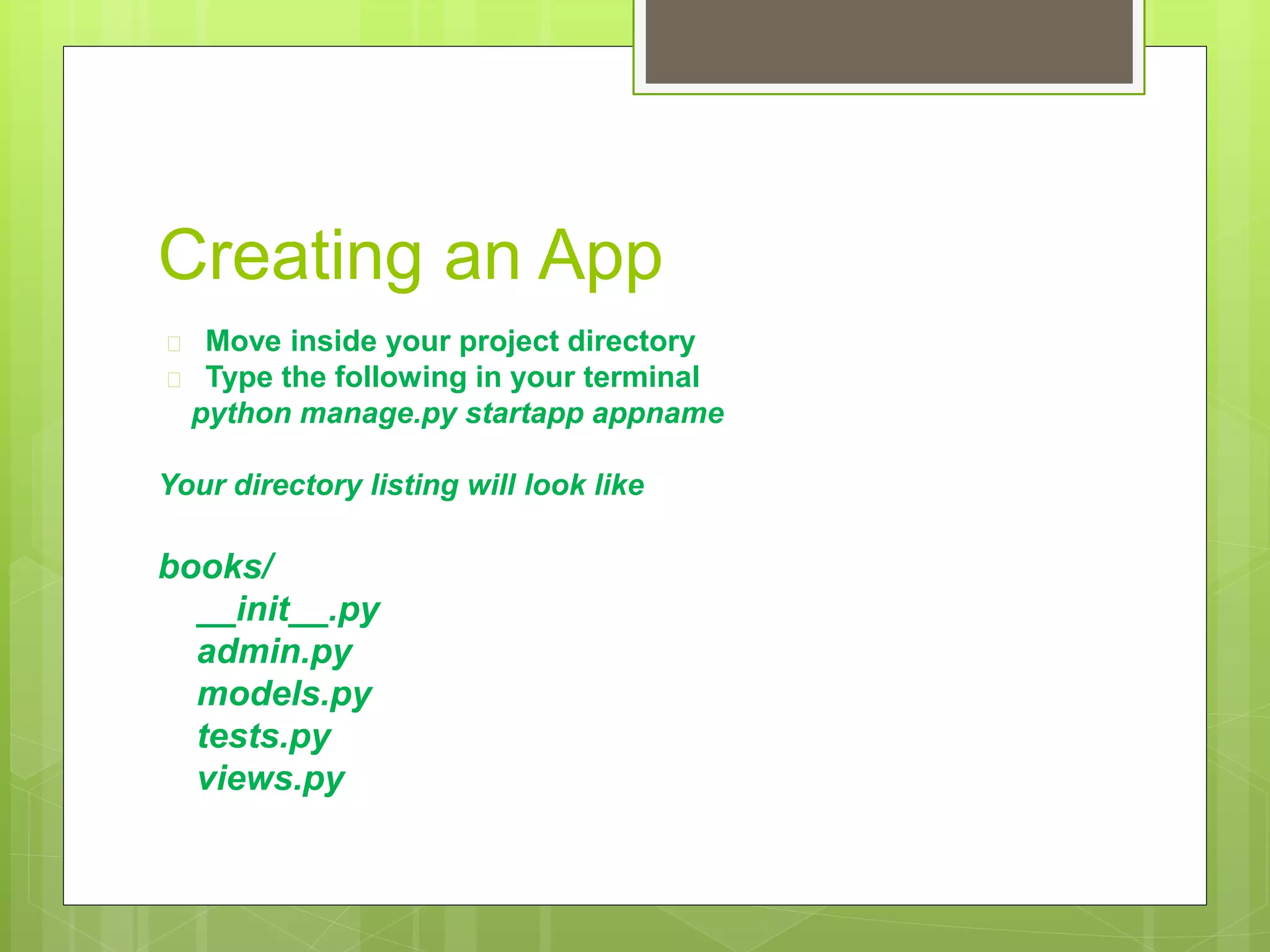
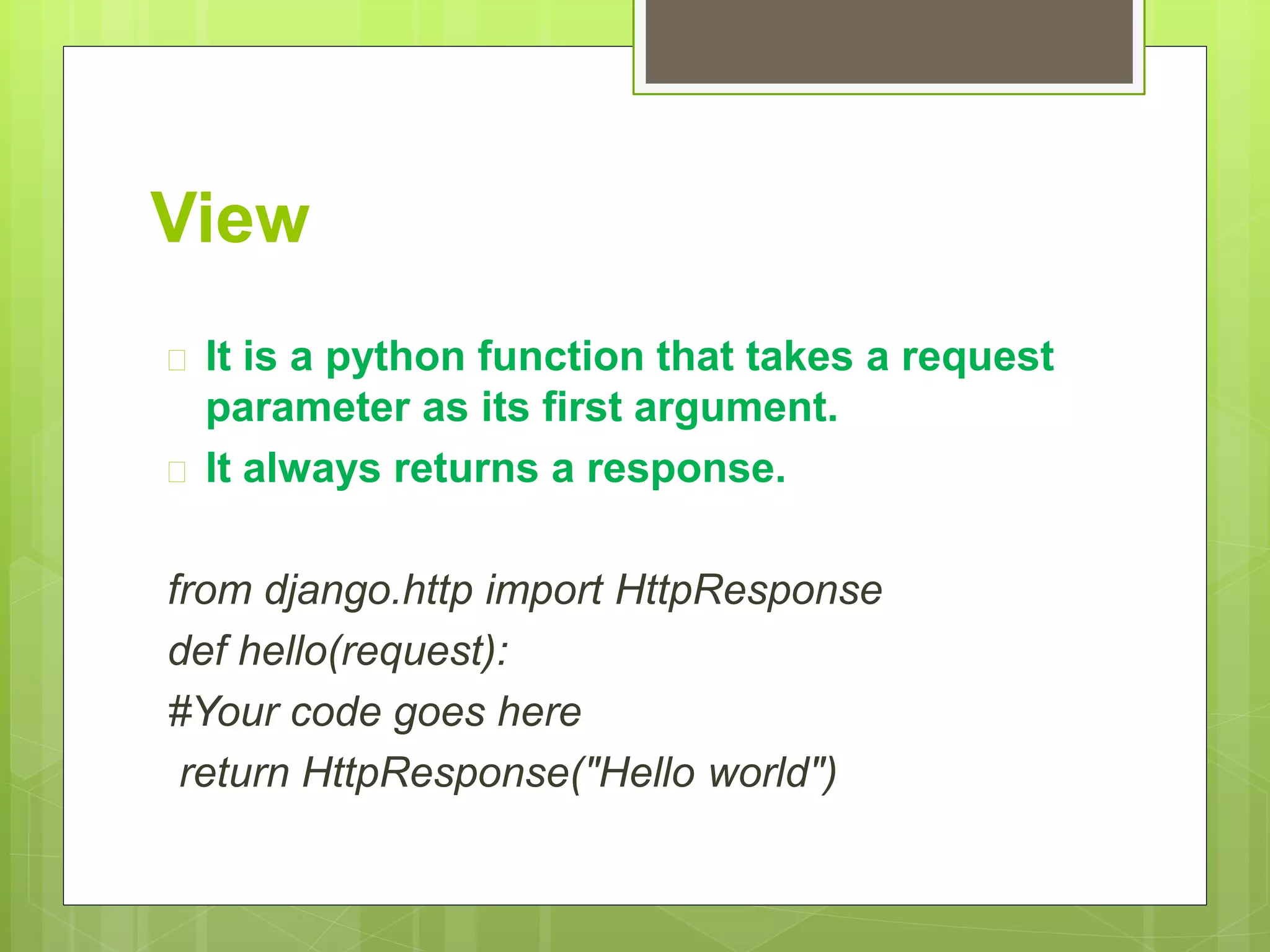
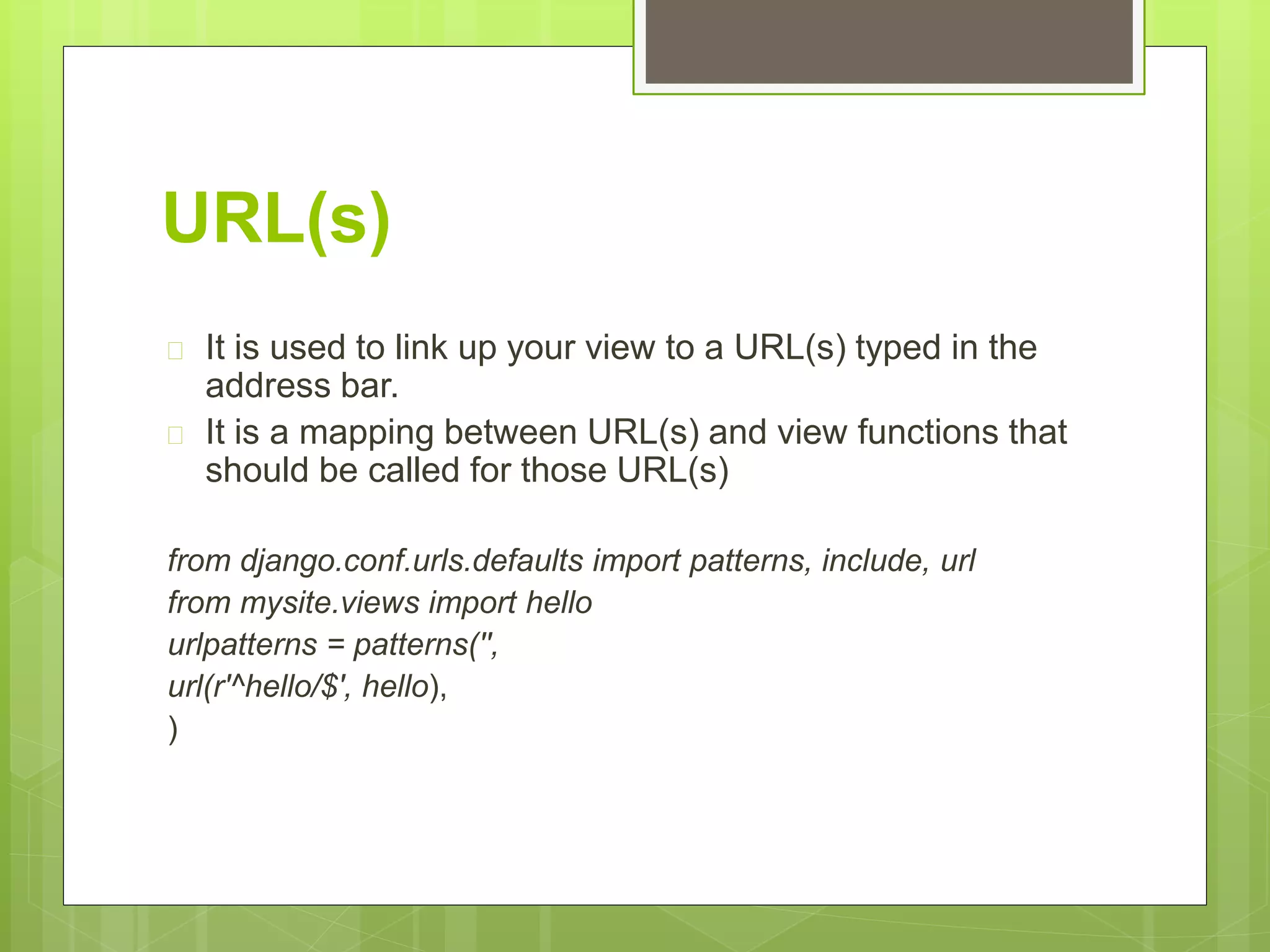
Django is a Python-based web framework that follows the MTV (Model-Template-View) design pattern. It allows developers to create dynamic websites and web applications by handling common tasks like database access, session management, and rendering templates. The document outlines how to create a Django project and app, configure settings like the database, and link views to URLs to handle requests and return responses.