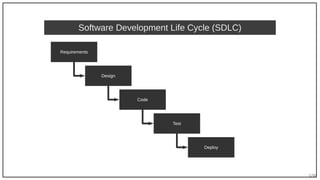
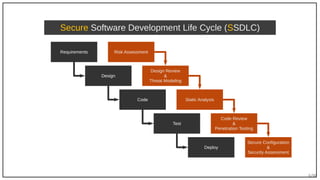
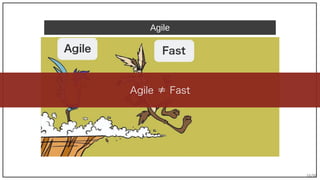
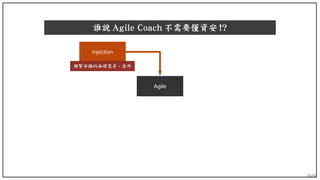
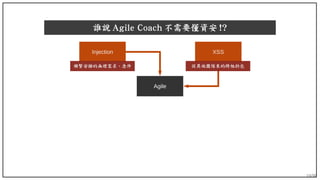
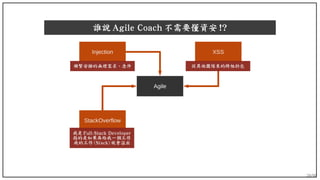
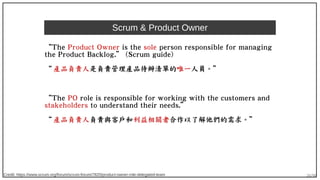
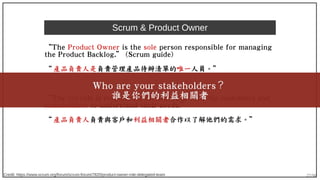
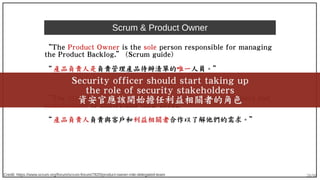
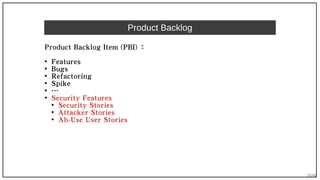
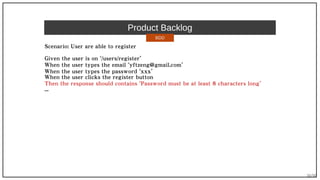
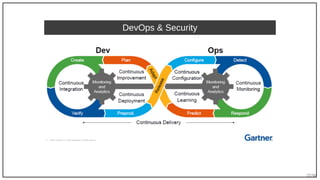
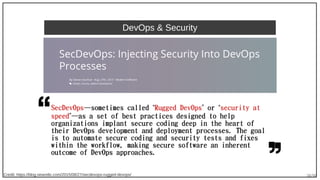
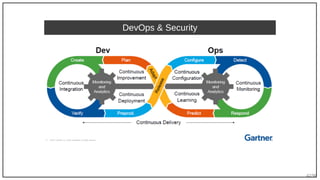
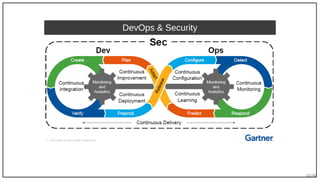
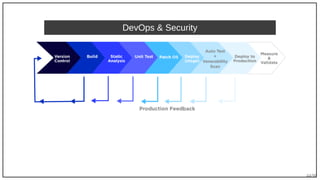
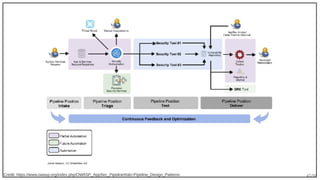
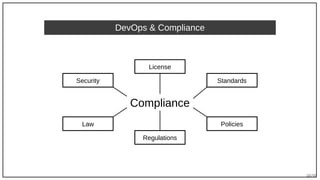
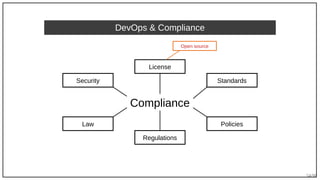
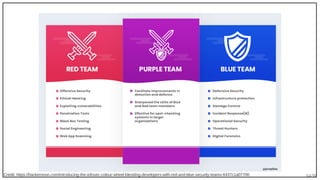
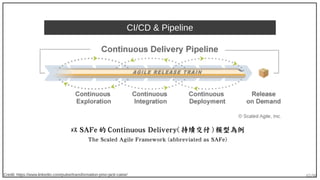
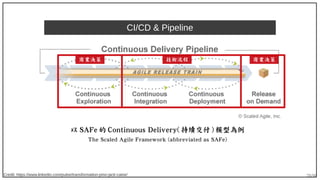
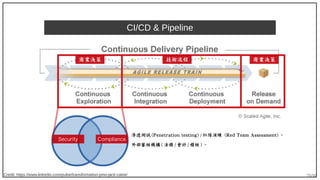
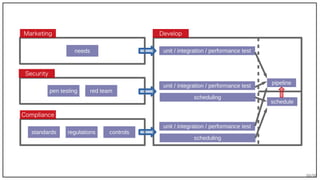
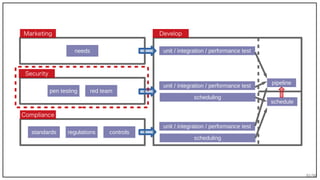
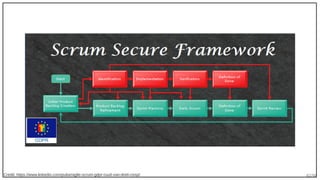
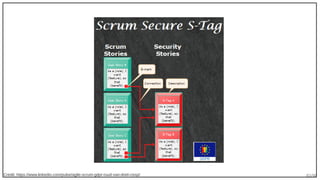
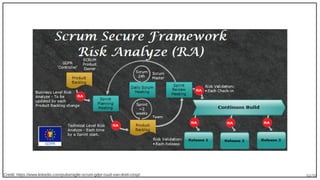
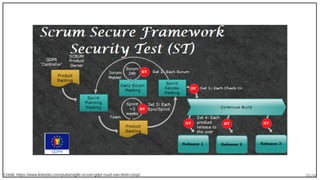
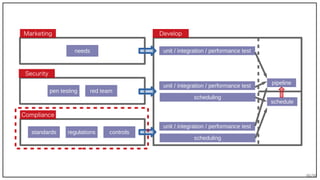
The document discusses the integration of security within DevOps and Agile methodologies, emphasizing the need for a DevSecOps culture that embeds security throughout the software development lifecycle (SDLC). It outlines various practices such as secure coding, compliance with regulations like GDPR, and the importance of involving security stakeholders in the development process. The author highlights challenges in maintaining security during Agile practices and the necessity of automated security testing within continuous integration and delivery pipelines.






![87/90
程式提交程式提交 ………… 授權分析授權分析 授權白名單授權白名單 授權黑名單授權黑名單 授權灰名單授權灰名單 程式通過程式通過
靜態分析靜態分析
動態分析動態分析
註解分析註解分析
相容分析相容分析
X
問題清單問題清單
MIT
Apache-2.0
BSD-2-Clause
BSD-3-Clause
……
AGPL-3.0
CPAL
OSL
SSPL
……
LGPL-2.1 / 動態連結 → OK
LGPL-2.1 / 靜態連結 → NO
LGPL-3.0 / 動態連結 → OK
LGPL-3.0 / 靜態連結 → NO
……
X Xhttps://github.com/fossology/fossology
https://github.com/google/licenseclassifier
https://github.com/github/licensed
https://github.com/dmgerman/ninka
https://github.com/jslicense/licensee.js [npm]
https://github.com/davglass/license-checker [npm]
https://github.com/pmezard/licenses [Go]
https://github.com/Comcast/php-legal-licenses [PHP]
https://github.com/composer/spdx-licenses [SPDX]](https://image.slidesharecdn.com/2019-07-11devsecops-architectureforsecurityandcompliance-190711165146/85/Dev-Sec-Ops-Architecture-for-Security-and-Compliance-87-320.jpg)