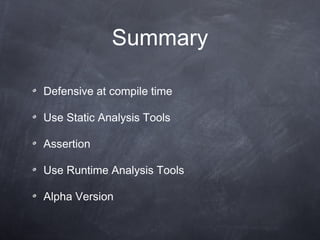
The document discusses techniques for defensive programming including:
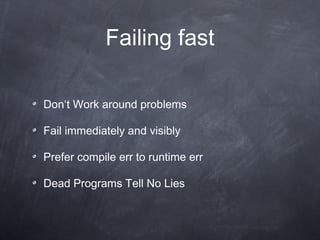
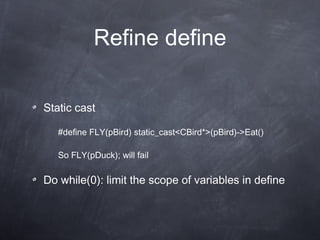
1. Using static analysis tools and assertions at compile time to catch errors early.
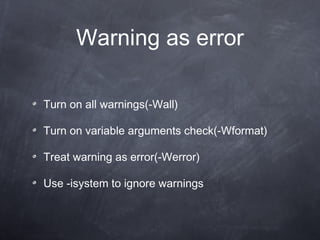
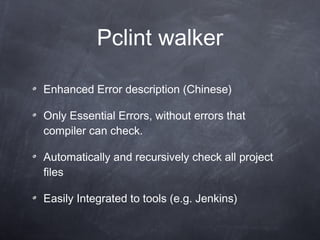
2. Treating warnings as errors and using tools like Pclint to detect issues like uninitialized variables.
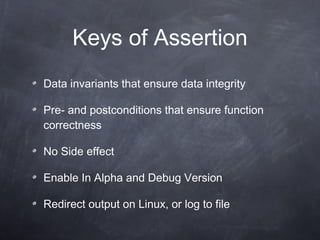
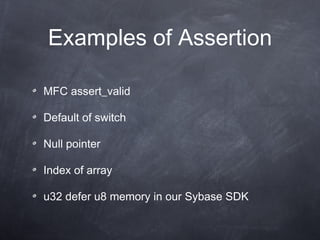
3. Employing assertions to check for data integrity and function pre/postconditions, especially in alpha and debug versions.
4. Leveraging runtime analysis tools like Valgrind to detect issues not caught during compilation such as out-of-bounds memory accesses.
![Pclint Variable have not been initialized new [] / delete mismatch Access out-of-bounds](https://image.slidesharecdn.com/defensiveprogramming-110909084015-phpapp02/85/Defensive-programming-6-320.jpg)
![Valgrind Runtime Analysis Tool More Precise new [] / delete Mismatch Access out-of-bounds Uninitialized Memory](https://image.slidesharecdn.com/defensiveprogramming-110909084015-phpapp02/85/Defensive-programming-10-320.jpg)