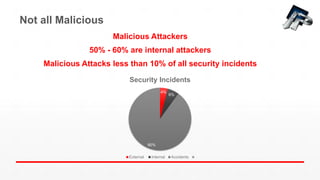
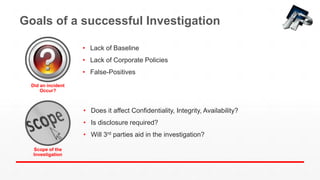
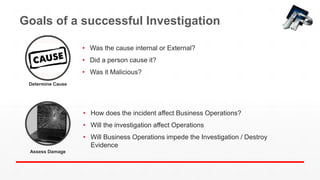
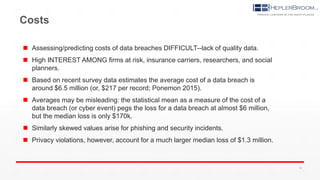
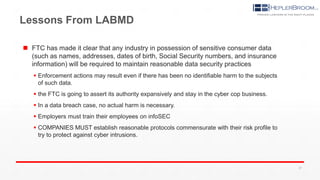
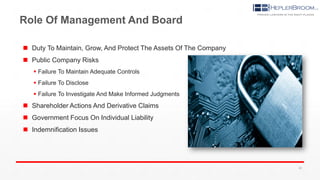
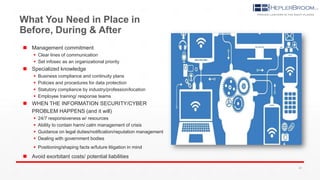
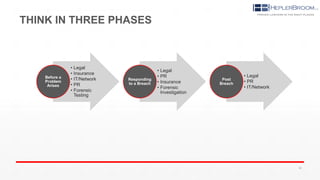
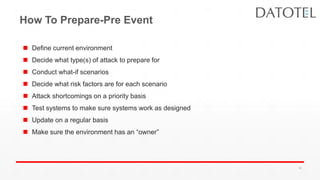
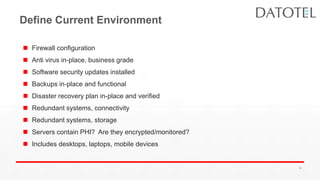
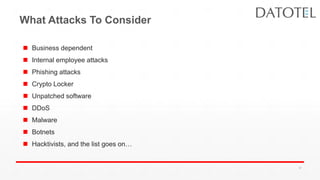
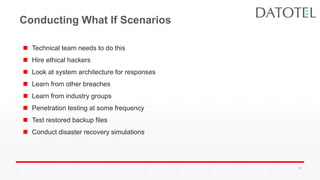
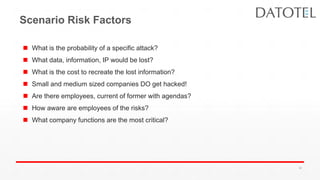
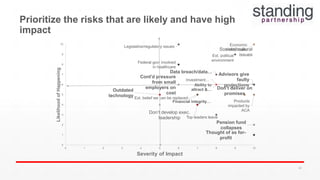
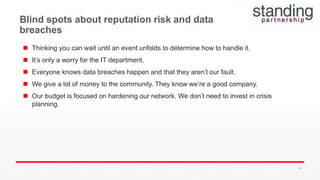
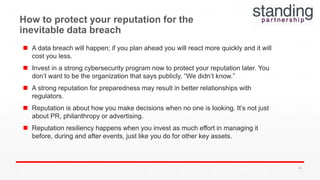
The document discusses preparing for and responding to cybersecurity incidents and data breaches. It provides an overview of Breach Education Alliance, an integrated team approach for responding to breaches. It then discusses best practices for security investigations, including establishing goals and understanding common causes of incidents. Potential mistakes in investigations and security are outlined. The document emphasizes training employees, understanding your environment and business risks, and having the proper resources in place before, during and after a security incident.