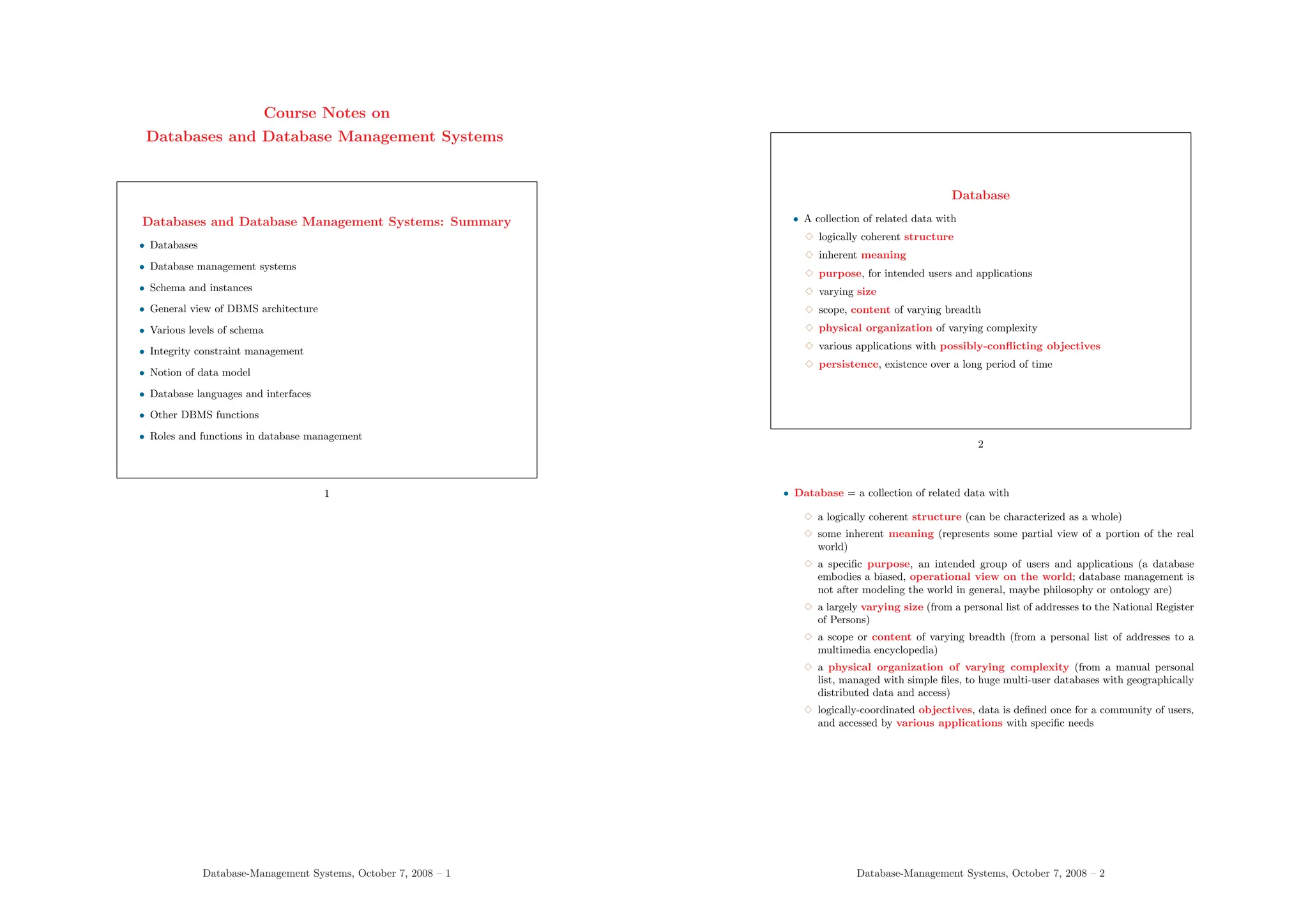
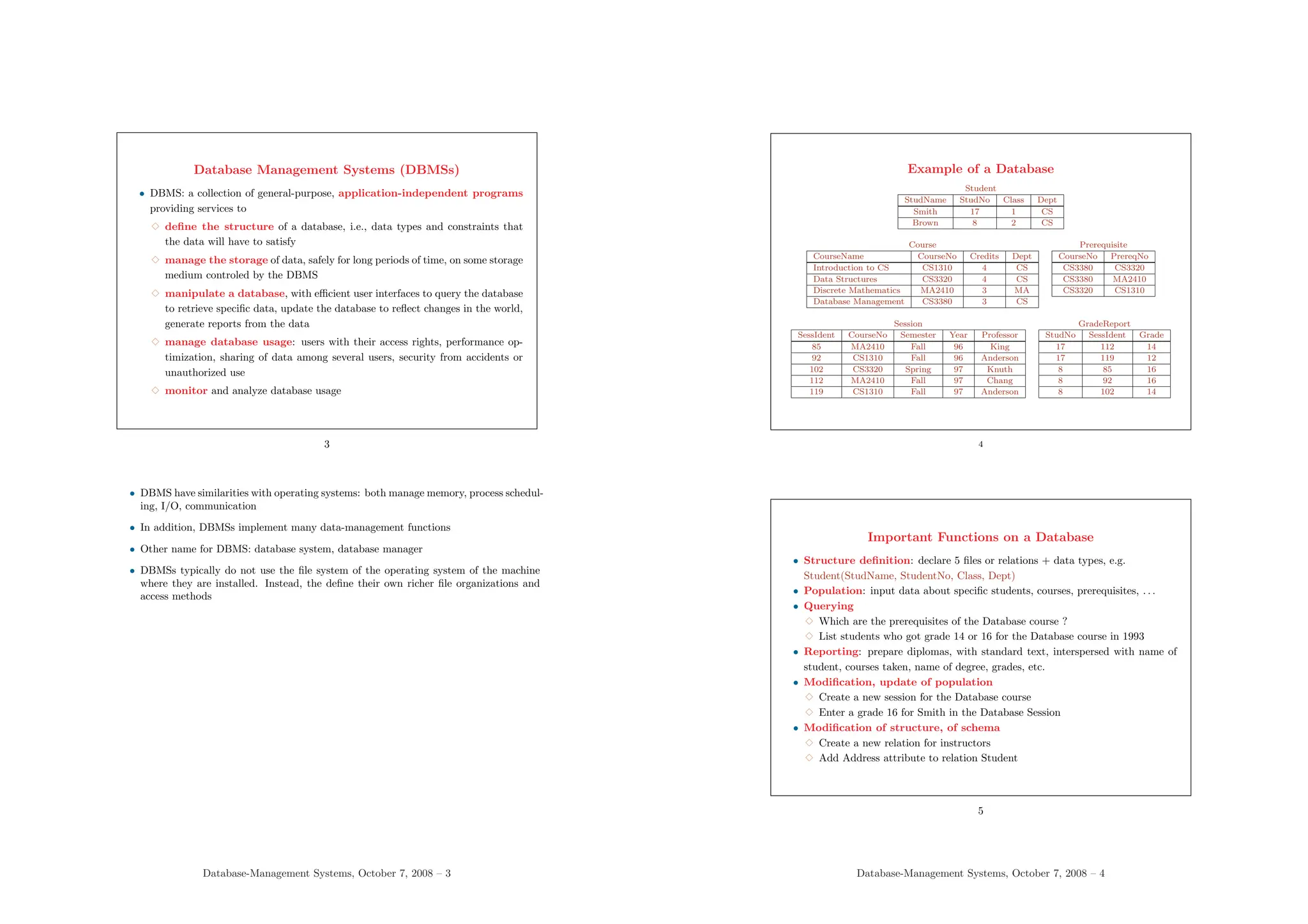
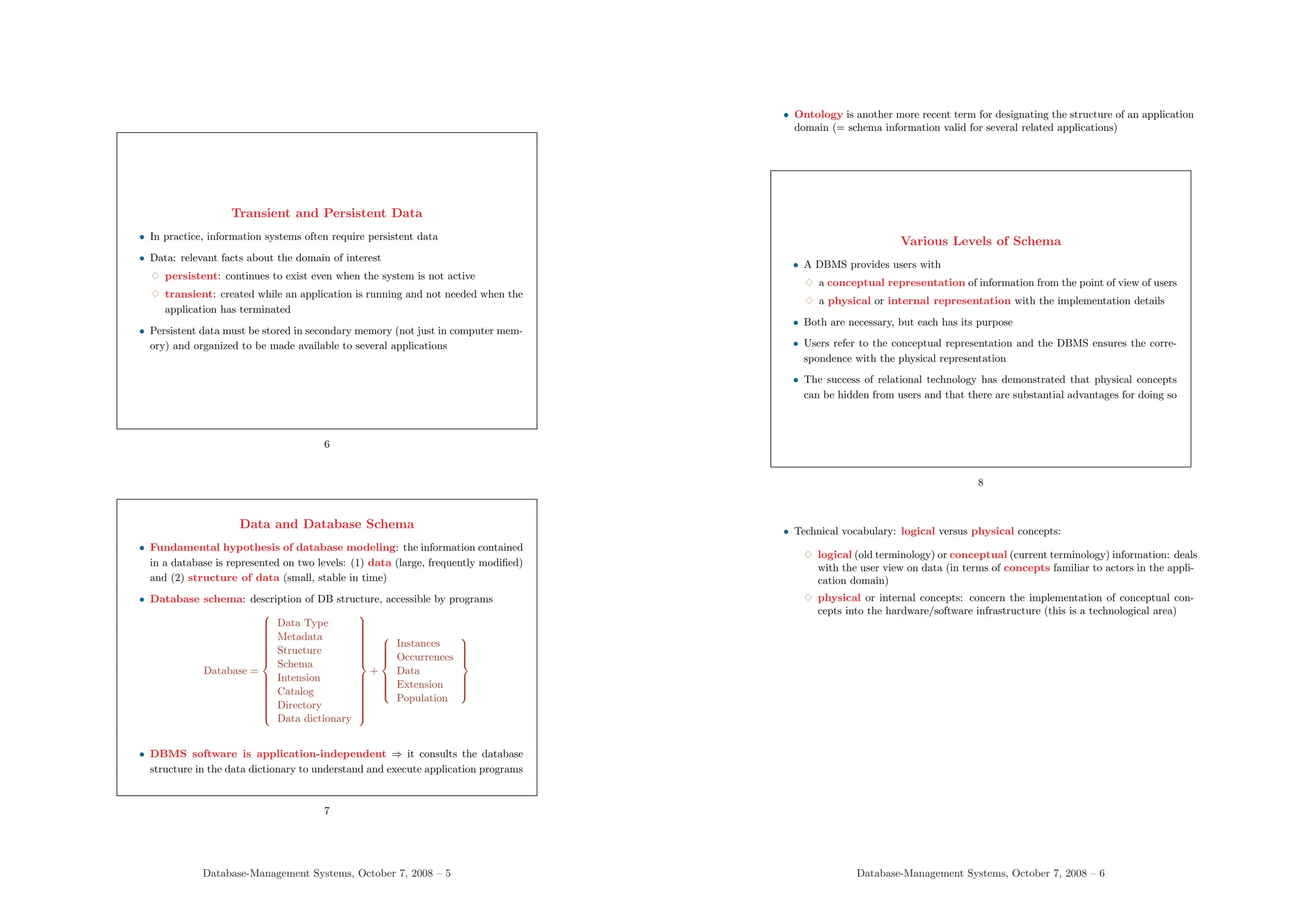
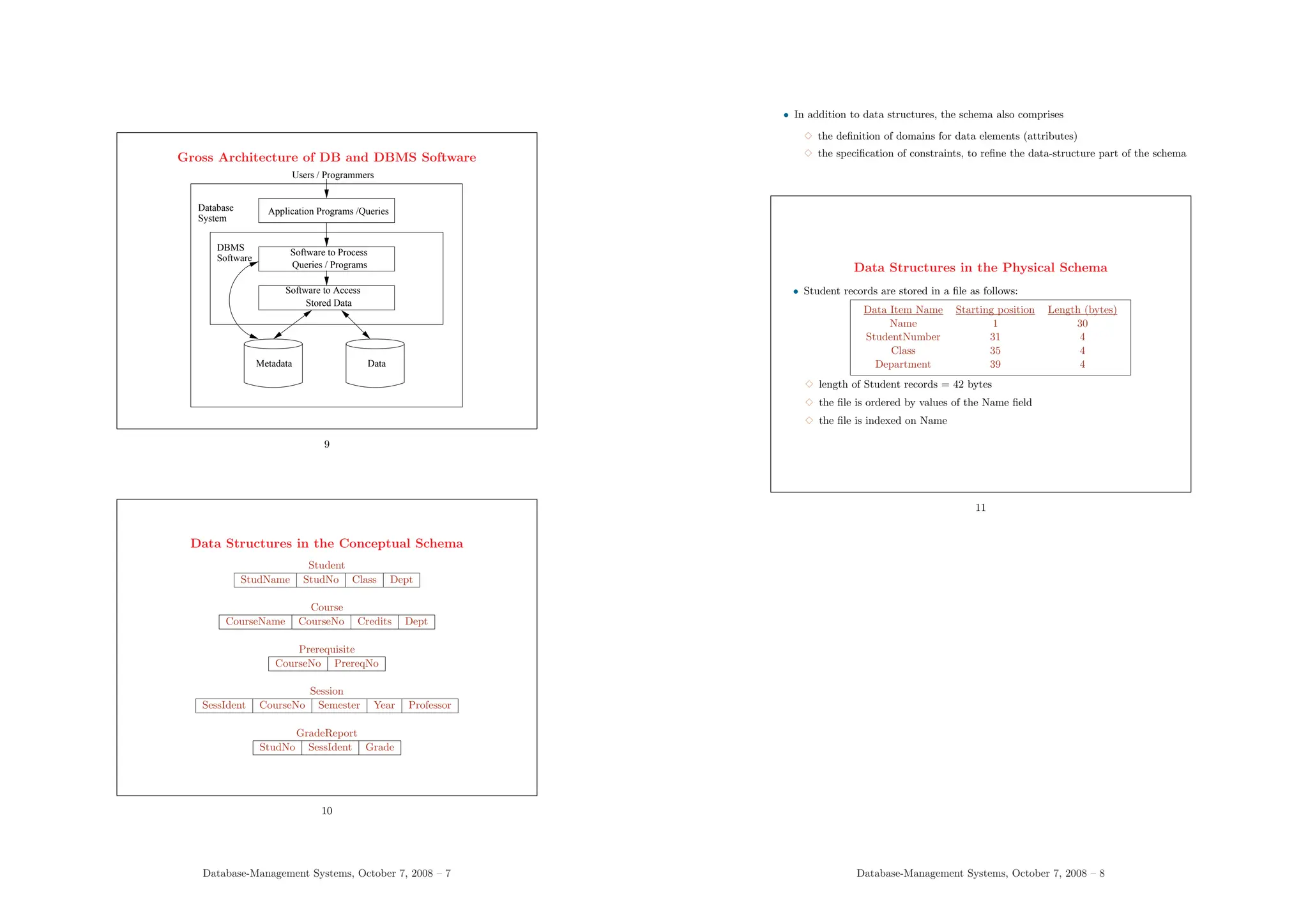
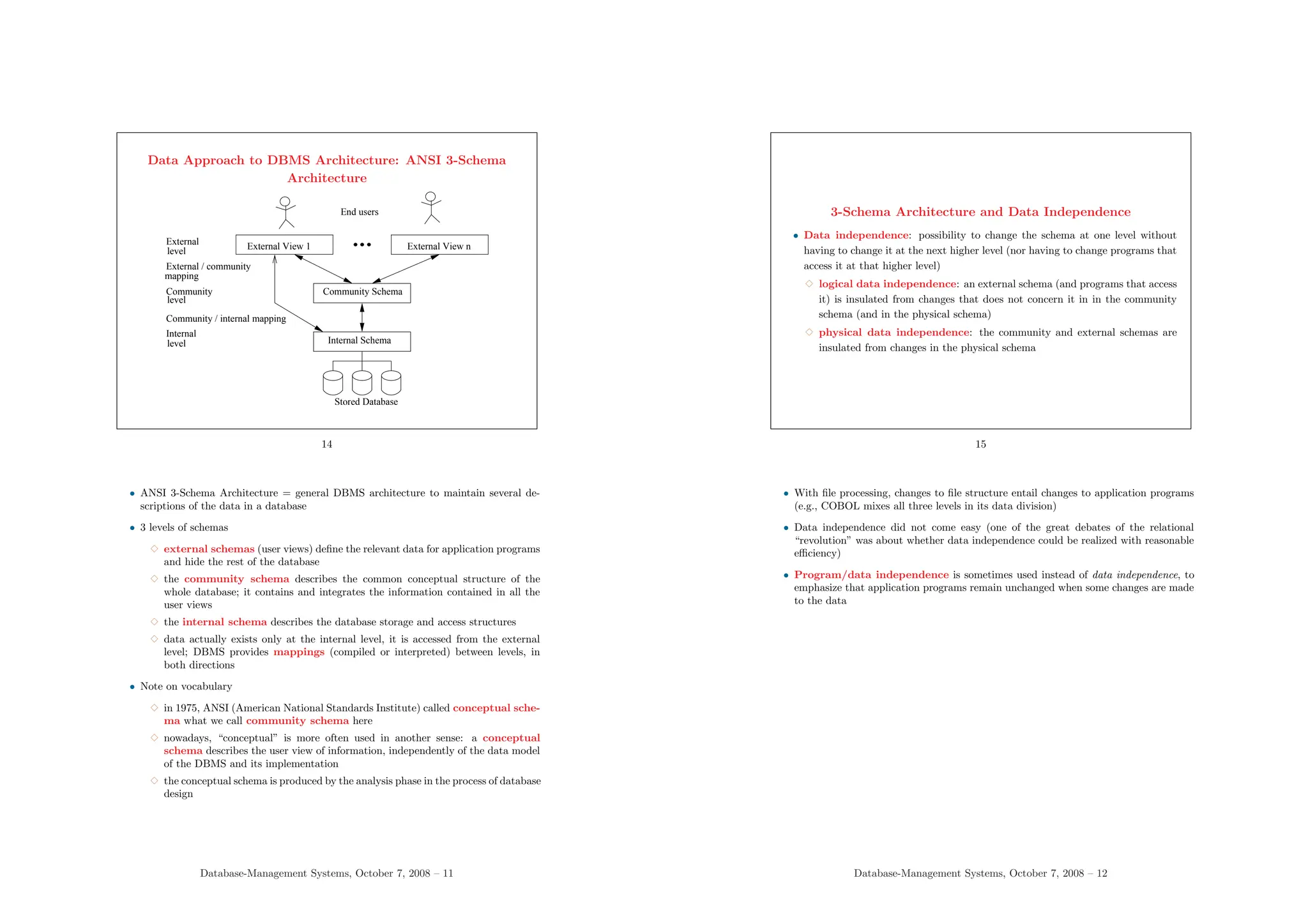
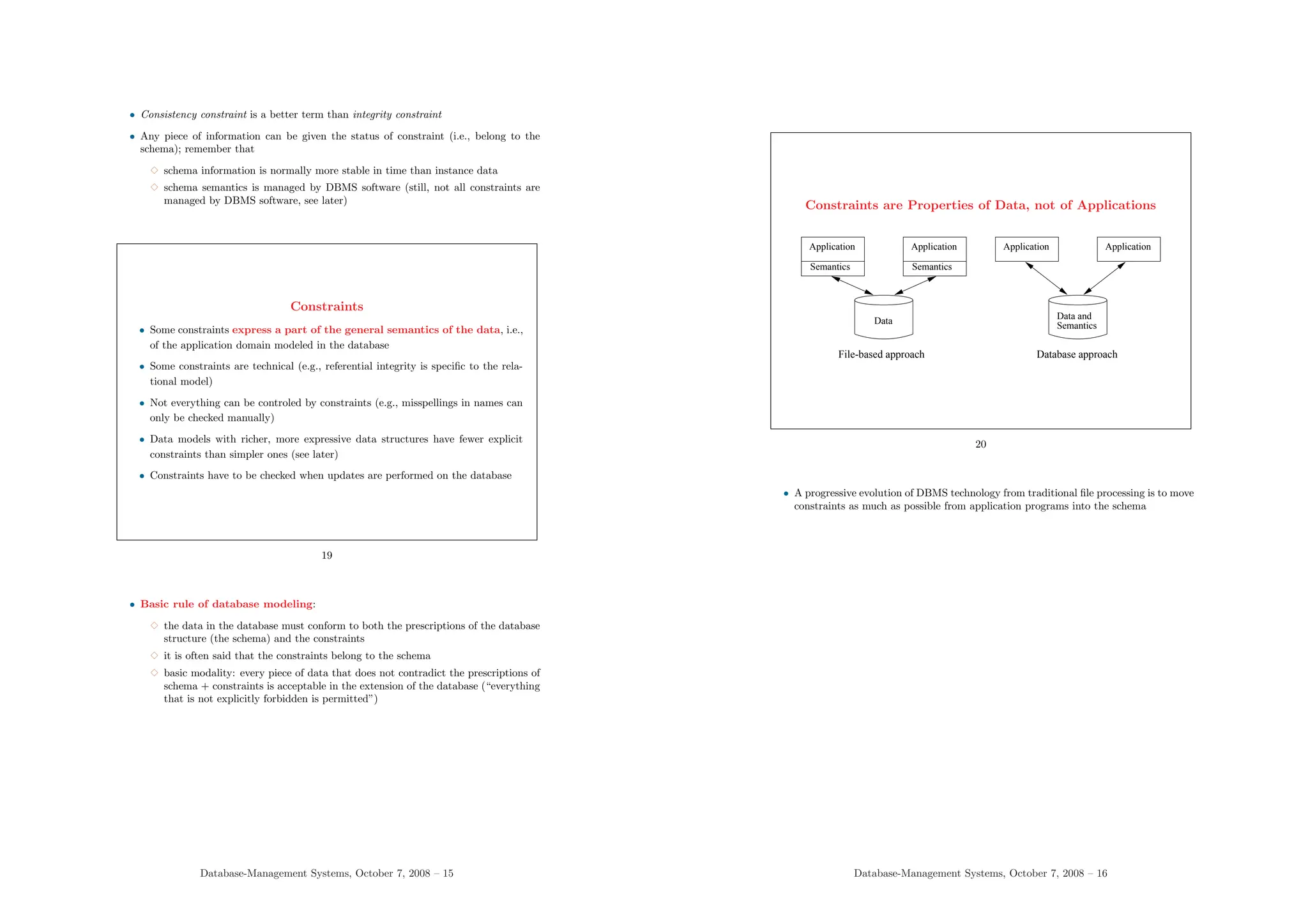
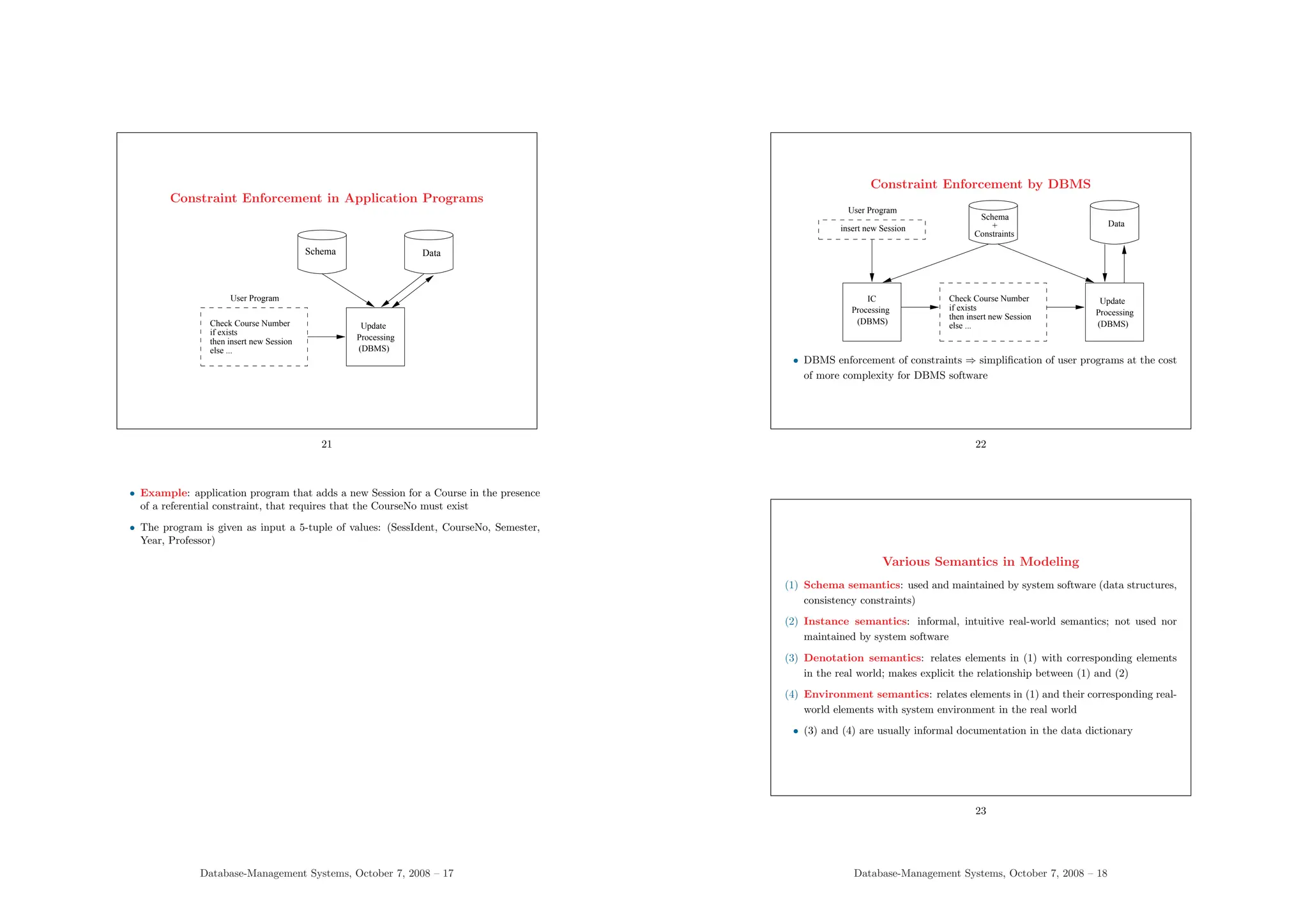
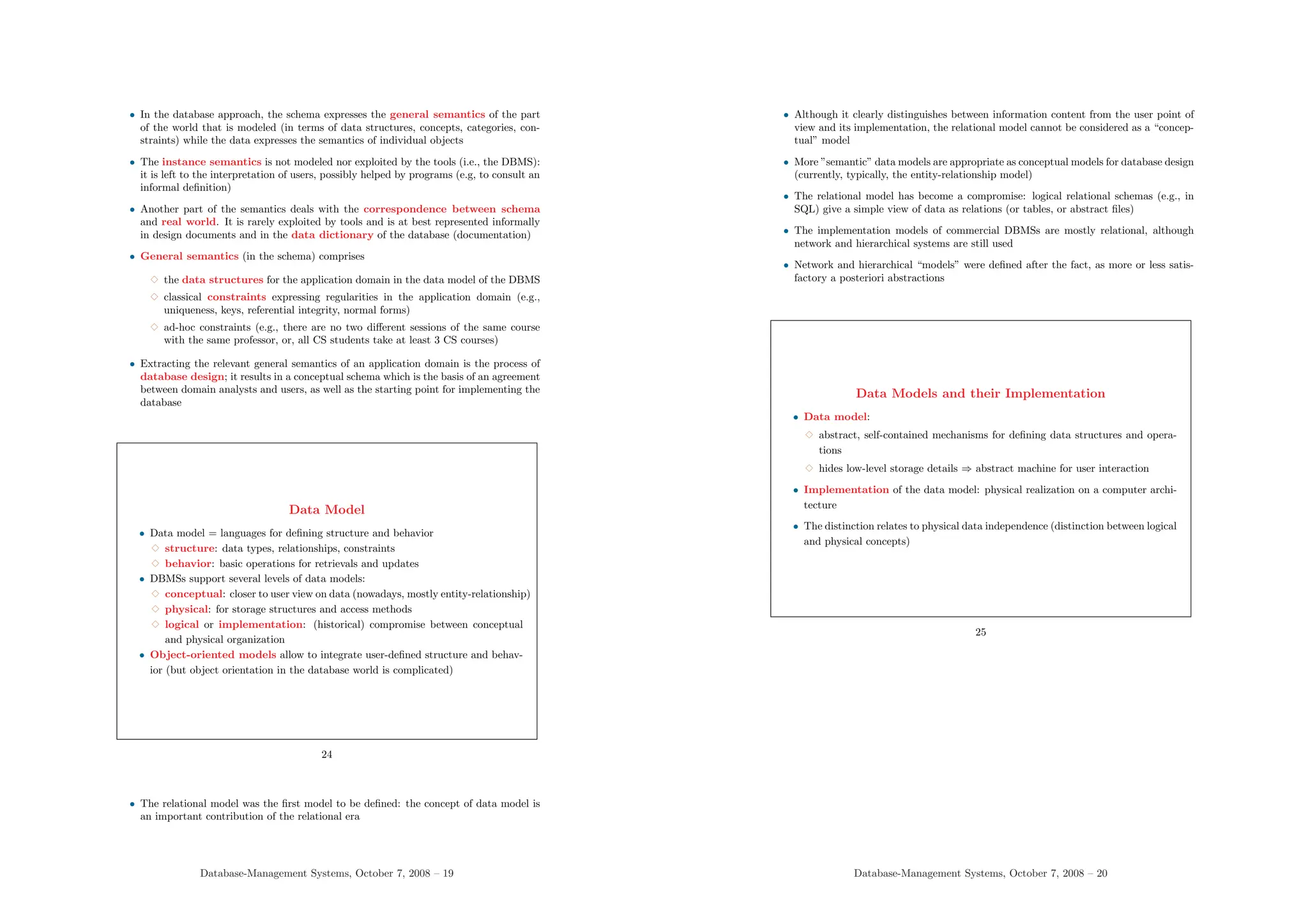
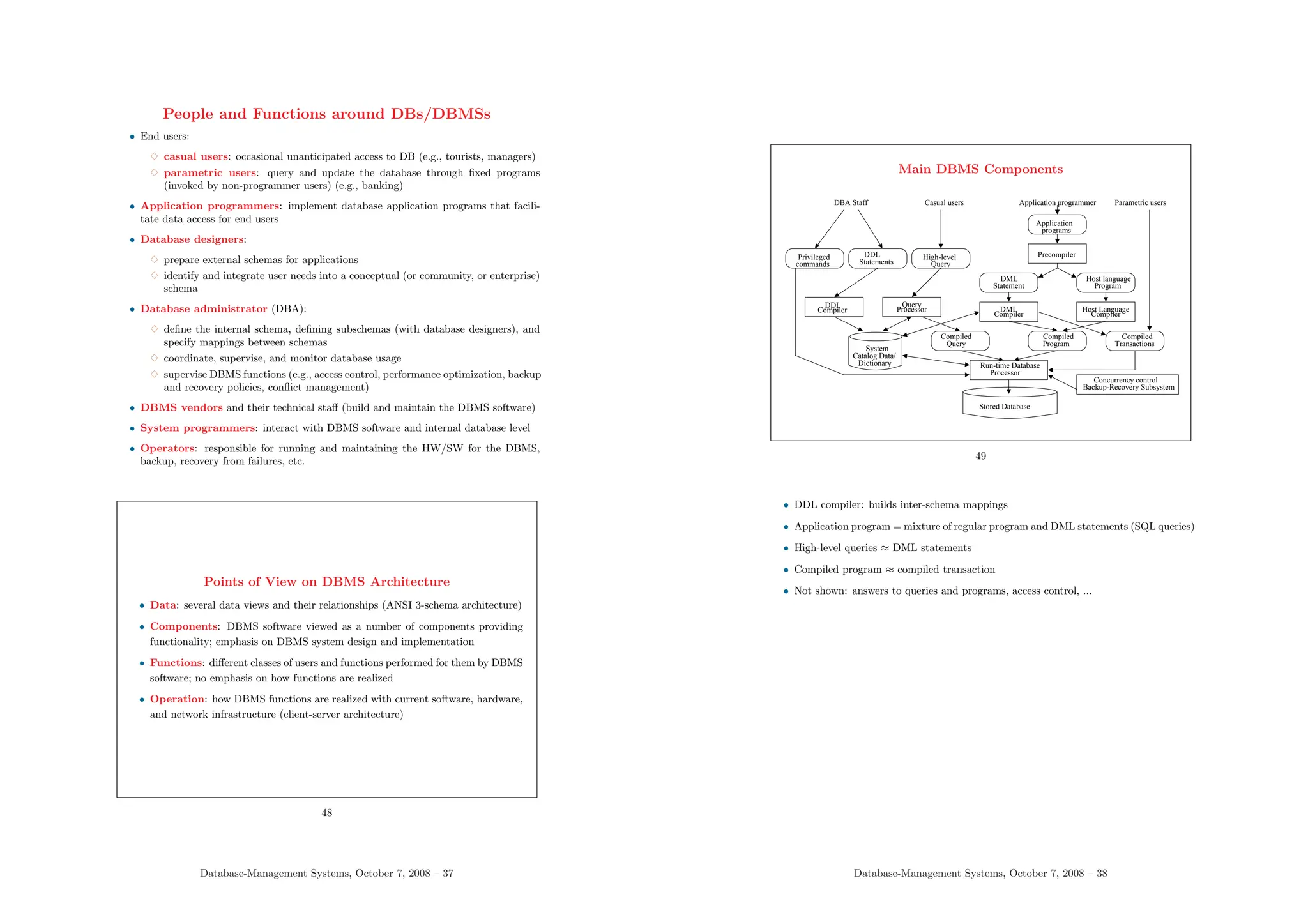
Este documento aborda la gestión de bases de datos y sistemas de gestión de bases de datos (DBMS), destacando la definición de bases de datos, sus estructuras, la arquitectura de los DBMS y la gestión de restricciones de integridad. Se discuten las funciones de los DBMS, como la definición de estructuras de datos, la gestión del almacenamiento y la manipulación de bases de datos a través de interfaces de usuario. Además, se enfatiza la importancia de la independencia de datos, que permite cambios en la estructura sin afectar los programas de aplicación.