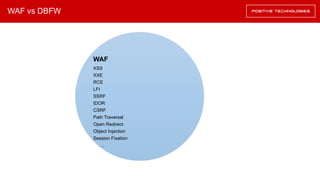
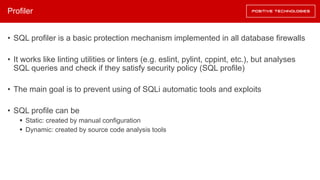
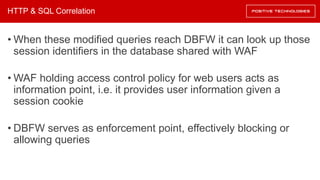
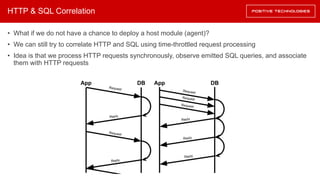
The document outlines the development of a database firewall (dbfw) by the Positive Technologies application firewall research team, detailing its functions, deployment methods, and comparison with web application firewalls (waf). It discusses the architecture of the dbfw, including components like parsers, profilers, and protections against SQL injection, as well as methodologies for effective monitoring and enforcement of access control. Additionally, the document presents related work and a roadmap for future development in application security solutions.












![Example of SQL Profile Rules
Options
["log", 20]
Rule
no-union
["block", 150]max-query-length
["block", 6]max-columns
["block", 0]max-union
["block", "benchmark", "md5", "if"]function-blacklist
["block"]
entity-length
"off"no-subqueries
["block"]no-hex
["block"]no-stacked-queries
["block"]no-comments
["block"]no-os-commands](https://image.slidesharecdn.com/phdays-2017-dbfw-170531084347/85/DBFW-36-320.jpg)



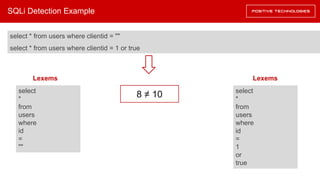
![SQLi Detection Example
GET /app/?id=1%20or%20true HTTP/1.1
Host: example.com
Connection: close
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate, sdch
Accept-Language: ru-RU,ru;q=0.8,en-US;q=0.6,en;q=0.4
/*{"get_args":[{"id":"1 or true"}]}*/ select * from users where clientid = 1 or true](https://image.slidesharecdn.com/phdays-2017-dbfw-170531084347/85/DBFW-55-320.jpg)
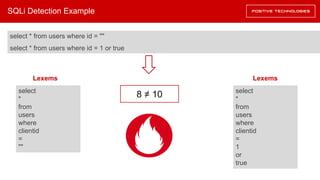
![SQLi Detection Example
GET /app/?id=1%20or%20true HTTP/1.1
Host: example.com
Connection: close
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate, sdch
Accept-Language: ru-RU,ru;q=0.8,en-US;q=0.6,en;q=0.4
/*{"get_args":[{"id":"1 or true"}]}*/ select * from users where clientid = 1 or true
select * from users where clientid = ""
select * from users where clientid = 1 or true](https://image.slidesharecdn.com/phdays-2017-dbfw-170531084347/85/DBFW-56-320.jpg)


![ALFAScript Policy Example
interface Entity {
abstract id: String;
}
interface SQLEntity <: Entity {
database: String;
table: String;
column: String;
level: Number;
tags: [String];
}
interface Subject <: Entity {
name: String;
level: Number;
tags: [String];
}](https://image.slidesharecdn.com/phdays-2017-dbfw-170531084347/85/DBFW-65-320.jpg)
![Angine Example
from Angine.policy import Policy
from Angine.pip import PIP
from Angine.pdp import PDP
def pep():
...
request = get_request(network)
policy = Policy(alfa_mysql_policy)
pip = PIP.init_data(mongo_connection)
pdp = PDP(policy.get_lua_policy())
ctx = pip.create_ctx(request)
response = pdp.evaluate(ctx)
if response["result"]["decision"] != "permit":
return None
else:
return process(request)](https://image.slidesharecdn.com/phdays-2017-dbfw-170531084347/85/DBFW-68-320.jpg)


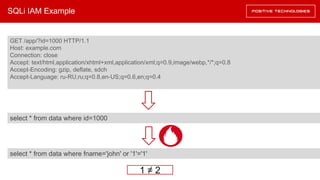
![SQL IAM Example
…
$sql = "select * from data where id= intval(".$_POST["id"])
$result = mysql_query($sql, $connection)
$row = mysql_fetch_row($result)
$sql = "select * from data where fname=' ".$row[2]. " ' "](https://image.slidesharecdn.com/phdays-2017-dbfw-170531084347/85/DBFW-75-320.jpg)
![SQL IAM Example
…
$sql = "select * from data where id= intval(".$_POST["id"])
$result = mysql_query($sql, $connection)
$row = mysql_fetch_row($result)
$sql = "select * from data where fname=' ".$row[2]. " ' "
Untrusted data read from database.
What if fname is ' or '1' = '1 ?](https://image.slidesharecdn.com/phdays-2017-dbfw-170531084347/85/DBFW-76-320.jpg)
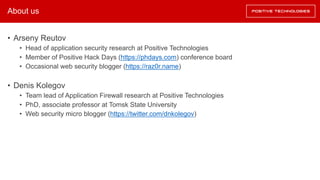
![SQL IAM Example
…
$sql = "select * from data where id= intval(".$_POST["id"])
$result = mysql_query($sql, $connection)
$row = mysql_fetch_row($result)
$sql = "select * from data where fname=' ".$row[2]. " ' "
The main SQL injection feature:
a number of tokens more that one](https://image.slidesharecdn.com/phdays-2017-dbfw-170531084347/85/DBFW-77-320.jpg)
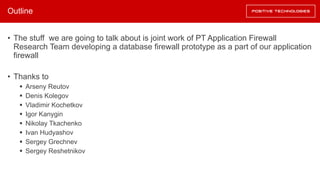
![SQL IAM Example
…
$sql = "select * from data where id= intval(".$_POST["id"])
$result = mysql_query($sql, $connection)
$row = mysql_fetch_row($result)
$sql = "select * from data where fname=' ".$row[2]. " ' "
(concat "select * from data where fname=" (
concat (index-access row 2) "'"))](https://image.slidesharecdn.com/phdays-2017-dbfw-170531084347/85/DBFW-78-320.jpg)
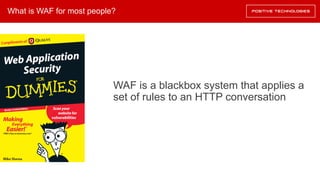
![SQL IAM Example
…
$sql = "select * from data where id= intval(".$_POST["id"])
$result = mysql_query($sql, $connection)
$row = mysql_fetch_row($result)
$sql = "select * from data where fname=' ".$row[2]. " ' "
(concat "select * from data where fname=" (
concat (index-access row 2) "'"))
(call mysql_fetch_row (call mysql_query (concat
"select * from data where id=intval(" (concat (index-
access POST, "id") ")")) connection))](https://image.slidesharecdn.com/phdays-2017-dbfw-170531084347/85/DBFW-79-320.jpg)
![SQL IAM Example
…
$sql = "select * from data where id= intval(".$_POST["id"])
$result = mysql_query($sql, $connection)
$row = mysql_fetch_row($result)
$sql = "select * from data where fname=' ".$row[2]. " ' "
№ Query hash Index Tokens
1 87248237482347 [(28,-1)] 1
2 13475837458758 [(32,-1)] 1](https://image.slidesharecdn.com/phdays-2017-dbfw-170531084347/85/DBFW-80-320.jpg)