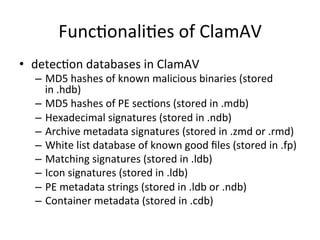
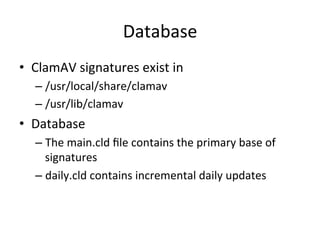
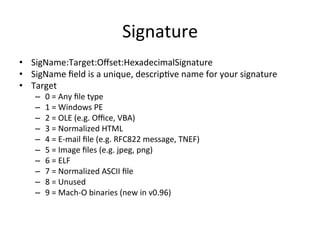
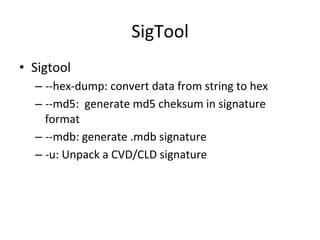
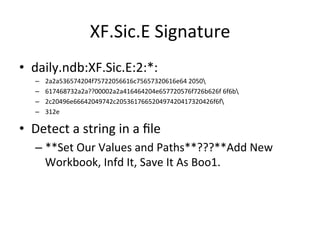
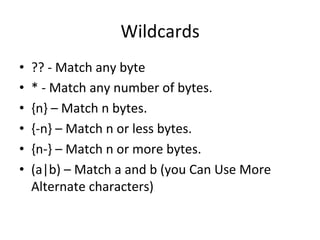
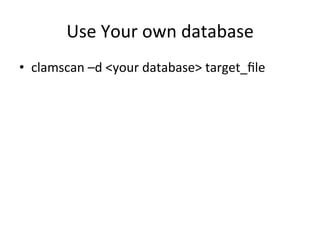
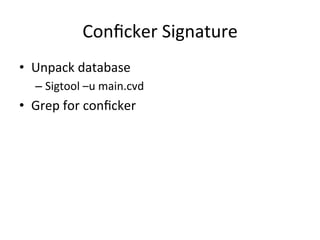
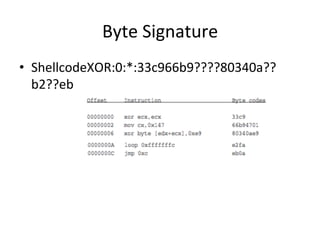
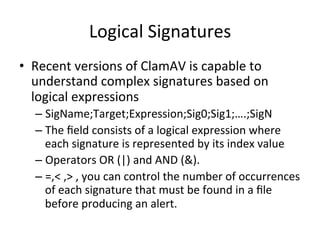
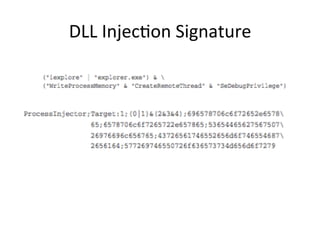
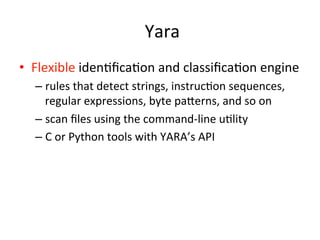
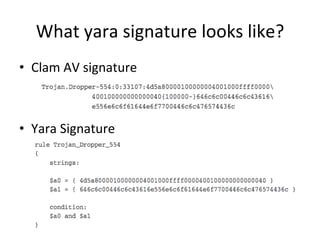
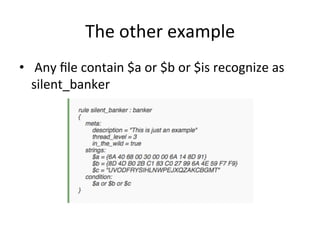
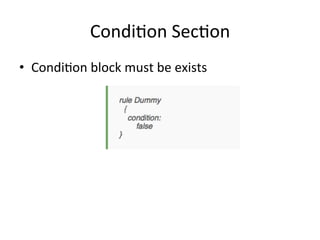
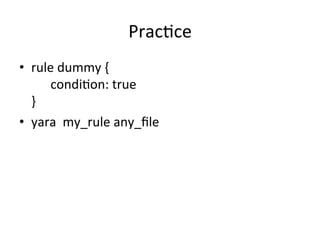
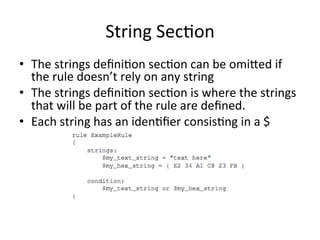
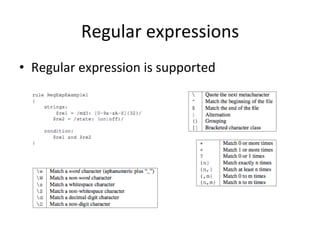
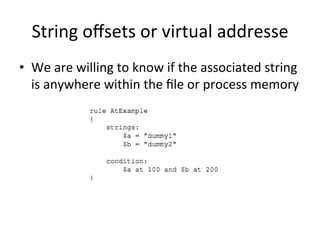
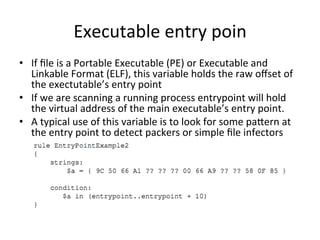
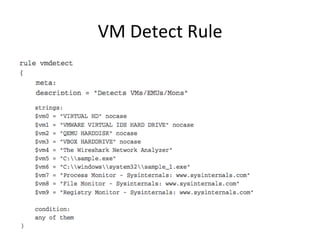
This document discusses tools for static analysis of files, including ClamAV and YARA. ClamAV is an open-source antivirus engine that uses signatures to detect malware. Signatures can include strings, hashes, and byte patterns. YARA allows for more flexible identification of malware through rules that can detect strings, regular expressions, and byte patterns. Examples of ClamAV and YARA signatures are provided.