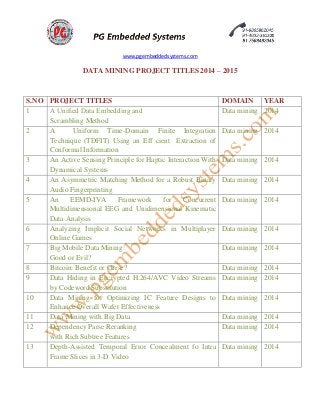
IEEE 2014 - 2015 DATA MINING PROJECT TITLES
- 1. www.pgembeddedsystems.com DATA MINING PROJECT TITLES 2014 – 2015 S.NO PROJECT TITLES DOMAIN YEAR 1 A Unified Data Embedding and Scrambling Method Data mining 2014 2 A Uniform Time-Domain Finite Integration Technique (TDFIT) Using an Eff cient Extraction of Conformal Information Data mining 2014 3 An Active Sensing Principle for Haptic Interaction With Dynamical Systems Data mining 2014 4 An Asymmetric Matching Method for a Robust Binary Audio Fingerprinting Data mining 2014 5 An EEMD-IVA Framework for Concurrent Multidimensional EEG and Unidimensional Kinematic Data Analysis Data mining 2014 6 Analyzing Implicit Social Networks in Multiplayer Online Games Data mining 2014 7 Big Mobile Data Mining: Good or Evil? Data mining 2014 8 Bitcoin: Benefit or Curse? Data mining 2014 9 Data Hiding in Encrypted H.264/AVC Video Streams by Codeword Substitution Data mining 2014 10 Data Mining for Optimizing IC Feature Designs to Enhance Overall Wafer Effectiveness Data mining 2014 11 Data Mining with Big Data Data mining 2014 12 Dependency Parse Reranking with Rich Subtree Features Data mining 2014 13 Depth-Assisted Temporal Error Concealment fo Intra Frame Slices in 3-D Video Data mining 2014
- 2. www.pgembeddedsystems.com 14 Developing Vehicular Data Cloud Services in the IoT Environment Data mining 2014 15 Discriminative Multimetric Learning for Kinship Verification Data mining 2014 16 Generating Summary Risk Scores for Mobile Applications Data mining 2014 17 Guest Editorial: Data Mining in Bioinformatics,Biomedicine, and Healthcare Informatics Data mining 2014 18 Investigation of Dominant Failure Mode(s) for Field- Aged Crystalline Silicon PV Modules Under Desert Climatic Conditions Data mining 2014 19 Local State Space Analysis Leads to Better Partial Order Reduction Data mining 2014 20 Mining Gene Expression Data Focusing Cancer Therapeutics: A Digest Data mining 2014 21 Mining Private information from Public data: the transantiago case Data mining 2014 22 Mining Sensor Data in Cyber-Physical Systems Data mining 2014 23 Multilabel Image Classification via High-Order Label Correlation Driven Active Learning Data mining 2014 24 Persistent Homology of Delay Embeddings and its Application to Wheeze Detection Data mining 2014 25 SAR Image Categorization Using Parametric and Nonparametric Approaches Within a Dual Tree CWT Data mining 2014 26 Signal-Integrity Optimization for Complicated Multiple- Input Multiple-Output Networks Based on Data Mining of S-Parameters Data mining 2014 27 Sport Type Classification of Mobile Videos Data mining 2014 28 Topic-Sensitive Influencer Mining in Interest-Based Social Media Networks via Hypergraph Learning Data mining 2014
- 3. www.pgembeddedsystems.com 29 Online Feature Selection and Its Applications Data mining 2014 30 Imaging of Compact Objects Buried in Underwater Sediments Using Electrical Impedance Tomography Data mining 2014 31 A Differential Sequence Component Protection Scheme for Microgrids With Inverter-Based Distributed Generators Data mining 2014 32 Decision Trees for Mining Data Streams Based on the Gaussian Approximation Data mining 2014 33 Discovering Conservation Rules Data mining 2014 34 A Cocktail Approach for Travel Package Recommendation Data mining 2014 35 A Compressive Sensing based Secure Watermark Detection and Privacy Preserving Storage Framework Data mining 2014 36 A Flexible Approach to Finding Representative Pattern Sets Data mining 2014 37 A Framework for Goal-Oriented Discovery of Resources in the RESTful Architecture Data mining 2014 38 A Framework for Periodic Outlier Pattern Detection in Time-Series Sequences Data mining 2014 39 A Group Incremental Approach to Feature Selection Applying Rough Set Technique Data mining 2014 40 A K-Main Routes Approach to Spatial Network Activity Summarization Data mining 2014 41 A Multiple Migration and Stacking Algorithm Designed for Land Mine Detection Data mining 2014 42 A New Multiobjective Evolutionary Algorithm for Mining a Reduced Set of Interesting Positive and Negative Quantitative Association Rules Data mining 2014 43 A Nonlinear Semantic-Preserving Projection Approach to Visualize Multivariate Periodical Time Series Data mining 2014
- 4. www.pgembeddedsystems.com 44 A Novel Graph-Based Estimation of the Distribution Algorithm and Its Extension Using Reinforcement Learning Data mining 2014 45 A Novel Methodology for Assessing the Fall Risk Using Low-Cost and Off-the-Shelf Devices Data mining 2014 46 A Novel Protein Complex Identification Algorithm Based on Connected Affinity Clique Extension (CACE) Data mining 2014 47 A Probabilistic Approach to String Transformation Data mining 2014 48 A Retrieval Strategy for Case-Based Reasoning Using Similarity and Association Knowledge Data mining 2014 49 A Review on Multi-Label Learning Algorithms Data mining 2014 50 A Rough Hypercuboid Approach for Feature Selection in Approximation Spaces Data mining 2014 51 A Scalable Two-Phase Top-Down Specialization Approach for Data Anonymization Using MapReduce on Cloud Data mining 2014 52 A Segmentation-Based Method to Extract Structural and Evolutionary Features for Protein Fold Recognition Data mining 2014 53 A Segmentation-Based Method to Extract Structural and Evolutionary Features for Protein Fold Recognition Data mining 2014 54 A System for Automatic Notification and Severity Estimation of Automotive Accidents Data mining 2014 55 A Two-Level Topic Model Towards Knowledge Discovery from Citation Networks Data mining 2014 56 A Unified Data Embedding and Scrambling Method Data mining 2014 57 A Unified Framework for Outlier Detection in Trace Data Analysis Data mining 2014 58 Activity Detection in Scientific Visualization Data mining 2014
- 5. www.pgembeddedsystems.com 59 Adaptation Regularization: A General Framework for Transfer Learning Data mining 2014 60 Adaptive Operator Selection With Bandits for a Multiobjective Evolutionary Algorithm Based on Decomposition Data mining 2014 61 An EEMD-IVA Framework for Concurrent Multidimensional EEG and Unidimensional Kinematic Data Analysis Data mining 2014 62 An Efficient Approach for Outlier Detection with Imperfect Data Labels Data mining 2014 63 An Efficient Recommendation Method for Improving Business Process Modeling Data mining 2014 64 An Evolutionary Multiobjective Approach for Community Discovery in Dynamic Networks Data mining 2014 65 An Integrated System for Regional Environmental Monitoring and Management Based on Internet of Things Data mining 2014 66 An Intelligent Decision Support System for the Operating Theater: A Case Study Data mining 2014 67 An Ontology-Based Text Mining Method to Develop D- Matrix from Unstructured Text Data mining 2014 68 Automatic GCP Extraction of Fully Polarimetric SAR Images Data mining 2014 69 Automatic Generation of the Domain Module from Electronic Textbooks: Method and Validation Data mining 2014 70 Automatic Identification of Large Fragments in a Pile of Broken Rock Using a Time-of-Flight Camera Data mining 2014 71 Automatic Spectral–Spatial Classification Framework Based on Attribute Profiles and Supervised Feature Extraction Data mining 2014
- 6. www.pgembeddedsystems.com 72 Chaos Theory-Based Data-Mining Technique for Image Endmember Extraction: Laypunov Index and Correlation Dimension (L and D) Data mining 2014 73 CoDe Modeling of Graph Composition for Data Warehouse Report Visualization Data mining 2014 74 Collaborative Online Multitask Learning Data mining 2014 75 Collaborative Policy Administration Data mining 2014 76 CommTrust: Computing Multi-Dimensional Trust by Mining E-Commerce Feedback Comments Data mining 2014 77 Commuter Route Optimized Energy Management of Hybrid Electric Vehicles Data mining 2014 78 Complex Network Clustering by Multiobjective Discrete Particle Swarm Optimization Based on Decomposition Data mining 2014 79 COMPOSE: A Semisupervised Learning Framework for Initially Labeled Nonstationary Streaming Data Data mining 2014 80 Consistency of Measurements of Wavelength Position From Hyperspectral Imagery: Use of the Ferric Iron Crystal Field Absorption at ∼900 nm as an Indicator of Mineralogy Data mining 2014 81 CoRE: A Context-Aware Relation Extraction Method for Relation Completion Data mining 2014 82 Data Hiding in Encrypted H.264/AVC Video Streams by Codeword Substitution Data mining 2014 83 Data Mining with Big Data Data mining 2014 84 Dealing With Concept Drifts in Process Mining Data mining 2014 85 Dependency Parse Reranking with Rich Subtree Features Data mining 2014 86 Depth-Assisted Temporal Error Concealment for Intra Frame Slices in 3-D Video Data mining 2014
- 7. www.pgembeddedsystems.com 87 Determining Process Model Precision and Generalization with Weighted Artificial Negative Events Data mining 2014 88 Developing Vehicular Data Cloud Services in the IoT Environment Data mining 2014 89 Discovering the Top-k k Unexplained Sequences in Time-Stamped Observation Data Data mining 2014 90 Discriminative Multimetric Learning for Kinship Verification Data mining 2014 91 Efficient Enumeration of Minimal Unsafe States in Complex Resource Allocation Systems Data mining 2014 92 Enhancing Memory Recall via an Intelligent Social Contact Management System Data mining 2014 93 Ensembles of -Trees for Imbalanced Classification Problems Data mining 2014 94 Exploiting Environmental Information for Improved Underwater Target Classification in Sonar Imagery Data mining 2014 95 Extensions of Kmeans-Type Algorithms: A New Clustering Framework by Integrating Intracluster Compactness and Intercluster Separation Data mining 2014 96 Fault Isolation of Nonlinear Processes Based on Fault Directions and Features Data mining 2014 97 Feature Learning for Image Classification via Multiobjective Genetic Programming Data mining 2014 98 Feature-Based Analysis of Plasma-Based Particle Acceleration Data Data mining 2014 99 Frame-Based Recovery of Corrupted Video Files Using Video Codec Specifications Data mining 2014 100 From Principal Curves to Granular Principal Curves Data mining 2014 101 Generating Summary Risk Scores for Mobile Applications Data mining 2014
- 8. www.pgembeddedsystems.com 102 HEigen: Spectral Analysis for Billion-Scale Graphs Data mining 2014 103 Hybrid Method Inference for the Construction of Cooperative Regulatory Network in Human Data mining 2014 104 Hypercube-Based Multipath Social Feature Routing in Human Contact Networks Data mining 2014 105 Identifying Features in Opinion Mining via Intrinsic and Extrinsic Domain Relevance Data mining 2014 106 Improved and Promising Identification of Human MicroRNAs by Incorporating a High-Quality Negative Set Data mining 2014 107 Infrequent Weighted Itemset Mining Using Frequent Pattern Growth Data mining 2014 108 Instance-Level Constraint-Based Semisupervised Learning With Imposed Space-Partitioning Data mining 2014 109 Interpreting the Public Sentiment Variations on Twitter Data mining 2014 110 Knowledge Fusion for Probabilistic Generative Classifiers with Data Mining Applications Data mining 2014 111 Large-Scale Experimental Evaluation of Cluster Representations for Multi objective Evolutionary Clustering Data mining 2014 112 Large-Scale Overlays and Trends: Visually Mining, Panning and Zooming the Observable Universe Data mining 2014 113 Learning Phenotype Structure Using Sequence Model Data mining 2014 114 Local State Space Analysis Leads to Better Partial Order Reduction Data mining 2014 115 Local Thresholding in General Network Graphs Data mining 2014
- 9. www.pgembeddedsystems.com 116 Maiter: An Asynchronous Graph Processing Framework for Delta-Based Accumulative Iterative Computation Data mining 2014 117 Measuring the Effects of Lighting Distribution on Walking Speed and Head Pitch With Wearable Inertial Measurement Units Data mining 2014 118 Mining Gene Expression Data Focusing Cancer Therapeutics: A Digest Data mining 2014 119 Mining Probabilistically Frequent Sequential Patterns in Large Uncertain Databases Data mining 2014 120 Mining Recurring Concepts in a Dynamic Feature Space Data mining 2014 121 Mining Statistically Significant Co-location and Segregation Patterns Data mining 2014 122 Mining Weakly Labeled Web Facial Images for Search- Based Face Annotation Data mining 2014 123 Mobile App Classification with Enriched Contextual Information Data mining 2014 124 Multi-Aspect + Transitivity + Bias: An Integral Trust Inference Model Data mining 2014 125 MultiComm: Finding Community Structure in Multi- Dimensional Networks Data mining 2014 126 Multifrequency Excitation and Support Vector Machine Regressor for ECT Defect Characterization Data mining 2014 127 Multilabel Image Classification via High-Order Label Correlation Driven Active Learning Data mining 2014 128 Nationwide Prediction of Drought Conditions in Iran Based on Remote Sensing Data Data mining 2014 129 Novel Just-In-Time Learning-Based Soft Sensor Utilizing Non-Gaussian Information Data mining 2014
- 10. www.pgembeddedsystems.com 130 OCCT: A One-Class Clustering Tree for Implementing One-to-Many Data Linkage Data mining 2014 131 Occurrence-Oriented Design Strategy for Developing Business Process Monitoring Systems Data mining 2014 132 On the Influence Propagation of Web Videos Data mining 2014 133 On the Use of Side Information for Mining Text Data Data mining 2014 134 Online Discovery of Gathering Patterns over Trajectories Data mining 2014 135 Optimization of Wind Power and Its Variability With a Computational Intelligence Approach Data mining 2014 136 Parameters Affecting Interferometric Coherence—The Case of a Dynamic Agricultural Region Data mining 2014 137 Personalized Recommendation Combining User Interest and Social Circle Data mining 2014 138 Population Classification in Fire Evacuation: A Multiobjective Particle Swarm Optimization Approach Data mining 2014 139 Prediction of Human Activity by Discovering Temporal Sequence Patterns Data mining 2014 140 Probabilistic Aspect Mining Model for Drug Reviews Data mining 2014 141 Probabilistic Framework for Assessing the Accuracy of Data Mining Tool for Online Prediction of Transient Stability Data mining 2014 142 Quantum to Classical Randomness Extractors Data mining 2014 143 QueRIE: Collaborative Database Exploration Data mining 2014 144 Random Projection Random Discretization Ensembles—Ensembles of Linear Multivariate Decision Trees Data mining 2014 145 Reacting to Different Types of Concept Drift: The Accuracy Updated Ensemble Algorithm Data mining 2014
- 11. www.pgembeddedsystems.com 146 Reliability-Based Design Optimization for Cloud Migration Data mining 2014 147 REPENT: Analyzing the Nature of Identifier Renamings Data mining 2014 148 Retrieval-Based Face Annotation by Weak Label Regularized Local Coordinate Coding Data mining 2014 149 Right-Protected Data Publishing with Provable Distance-Based Mining Data mining 2014 150 Road Centerline Extraction in Complex Urban Scenes From LiDAR Data Based on Multiple Features Data mining 2014 151 Rough Sets, Kernel Set, and Spatiotemporal Outlier Detection Data mining 2014 152 SAR Automatic Target Recognition Using Discriminative Graphical Models Data mining 2014 153 Scalable Similarity Search With Topology Preserving Hashing Data mining 2014 154 Searching Dimension Incomplete Databases Data mining 2014 155 Secure Mining of Association Rules in Horizontally Distributed Databases Data mining 2014 156 Secure Two-Party Differentially Private Data Release for Vertically Partitioned Data Data mining 2014 157 Self-Adaptive Semantic Focused Crawler for Mining Services Information Discovery Data mining 2014 158 Semantic-Based Resource Discovery and Orchestration in Home and Building Automation: A Multi-Agent Approach Data mining 2014 159 Semi-supervised Linear Discriminant Clustering Data mining 2014 160 Semisupervised Classification Through the Bag-of- Paths Group Betweenness Data mining 2014 161 Semisupervised Kernel Feature Extraction for Remote Sensing Image Analysis Data mining 2014
- 12. www.pgembeddedsystems.com 162 Semisupervised Wrapper Choice and Generation for Print-Oriented Documents Data mining 2014 163 Set Predicates in SQL: Enabling Set-Level Comparisons for Dynamically Formed Groups Data mining 2014 164 Signal-Integrity Optimization for Complicated Multiple- Input Multiple-Output Networks Based on Data Mining of S-Parameters Data mining 2014 165 Similarity Searching for Defective Wafer Bin Maps in Semiconductor Manufacturing Data mining 2014 166 Social Network Modeling and Agent-Based Simulation in Support of Crisis De-Escalation Data mining 2014 167 Social Voting Advice Applications - Definitions, Challenges, Datasets and Evaluation Data mining 2014 168 Sparse MIMO Array Forward-Looking GPR Imaging Based on Compressed Sensing in Clutter Environment Data mining 2014 169 Spatially Aware Term Selection for Geotagging Data mining 2014 170 Spatiotemporal Patterns in Large-Scale Traffic Speed Prediction Data mining 2014 171 Sport Type Classification of Mobile Videos Data mining 2014 172 Subgroup Discovery in Smart Electricity Meter Data Data mining 2014 173 Survey of Multiobjective Evolutionary Algorithms for Data Mining: Part II Data mining 2014 174 Temporal Analysis of Motif Mixtures Using Dirichlet Processes Data mining 2014 175 The Places of Our Lives: Visiting Patterns and Automatic Labeling from Longitudinal Smartphone Data Data mining 2014 176 The Role of Hubness in Clustering High-Dimensional Data Data mining 2014
- 13. www.pgembeddedsystems.com 177 The Sum-over-Forests Density Index: Identifying Dense Regions in a Graph Data mining 2014 178 Thermography-Based Virtual MPPT Scheme for Improving PV Energy Efficiency Under Partial Shading Conditions Data mining 2014 179 Topic-Sensitive Influencer Mining in Interest-Based Social Media Networks via Hypergraph Learning Data mining 2014 180 TotalPLS: Local Dimension Reduction for Multicategory Microarray Data Data mining 2014 181 Trajectory Improves Data Delivery in Urban Vehicular Networks Data mining 2014 182 Transfer Learning with Graph Co-Regularization Data mining 2014 183 Uncertain One-Class Learning and Concept Summarization Learning on Uncertain Data Streams Data mining 2014 184 Unified Design of a Feature-Based ADAC System for Mine Hunting Using Synthetic Aperture Sonar Data mining 2014 185 Using Delayed Observations for Long-Term Vehicle Tracking in Large Environments Data mining 2014 186 Using Incomplete Information for Complete Weight Annotation of Road Networks Data mining 2014 187 Variability Mining: Consistent Semi-automatic Detection of Product-Line Features Data mining 2014 188 Wireless Spectrum Occupancy Prediction Based on Partial Periodic Pattern Mining Data mining 2014 189 Performance Metric Ensemble for Multiobjective Evolutionary Algorithms Data mining 2014 190 Effective and Efficient Clustering Methods for Correlated Probabilistic Graphs Data mining 2014 191 Data Mining for Optimizing IC Feature Designs to Enhance Overall Wafer Effectiveness Data mining 2014