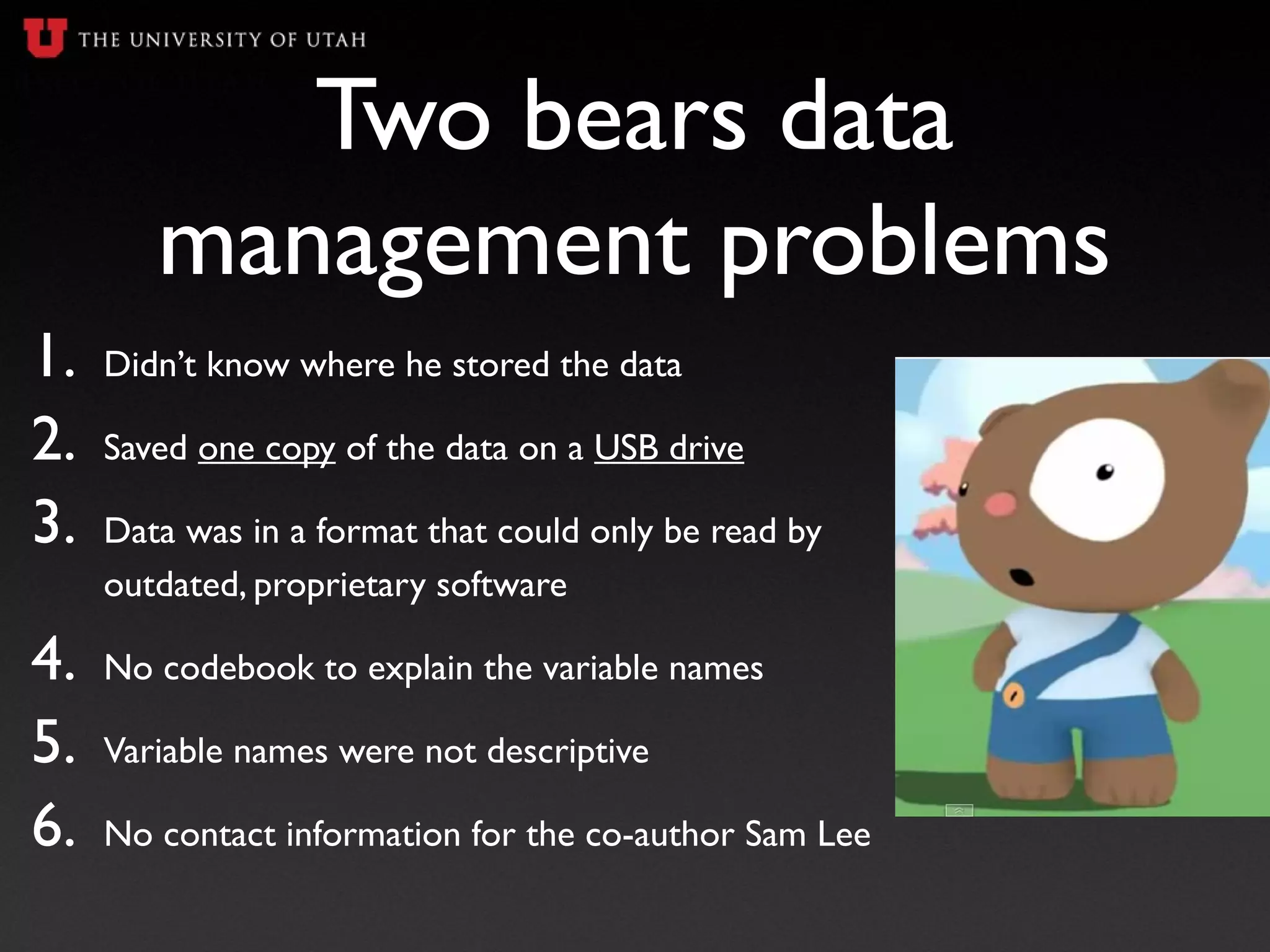
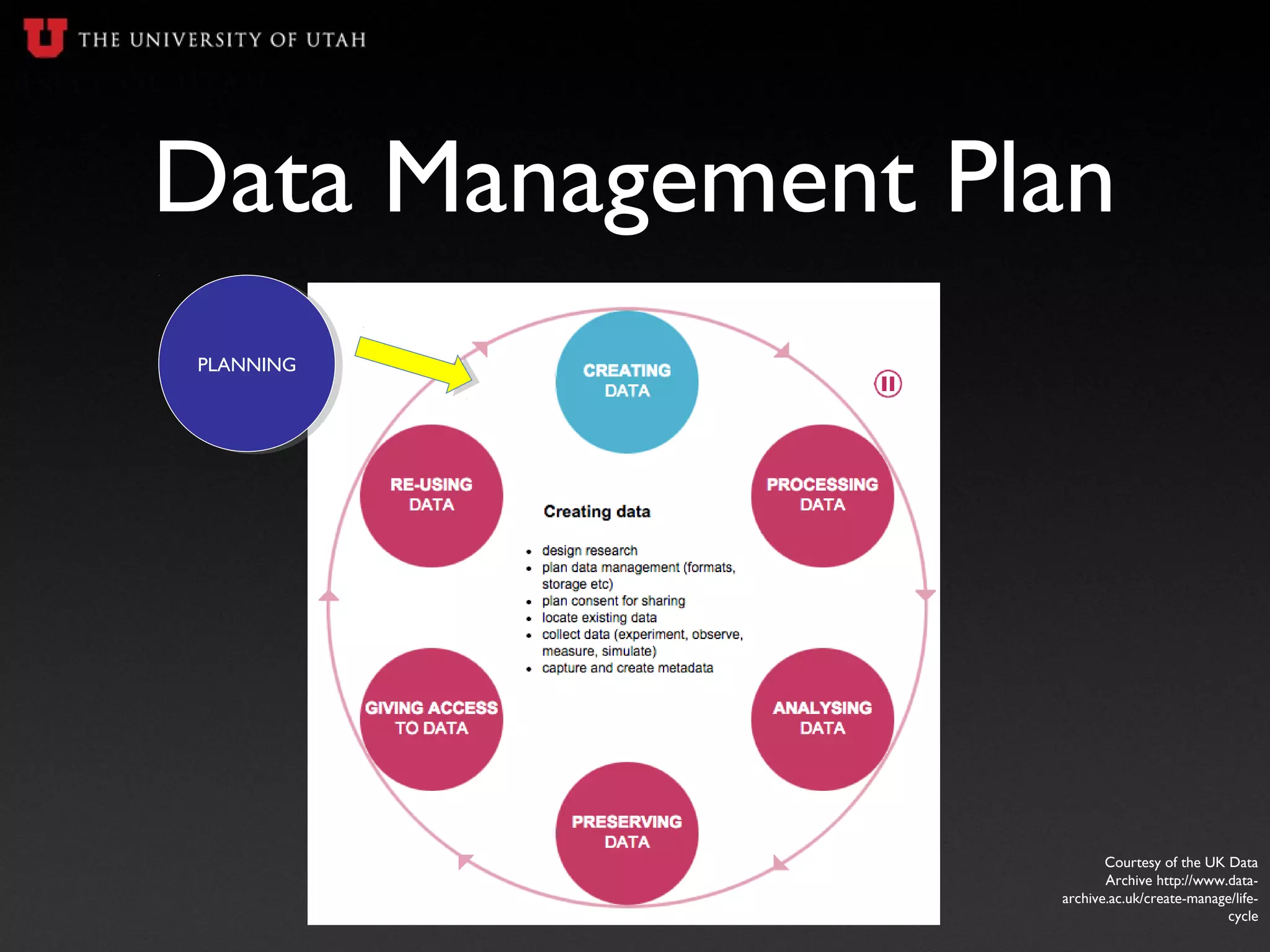
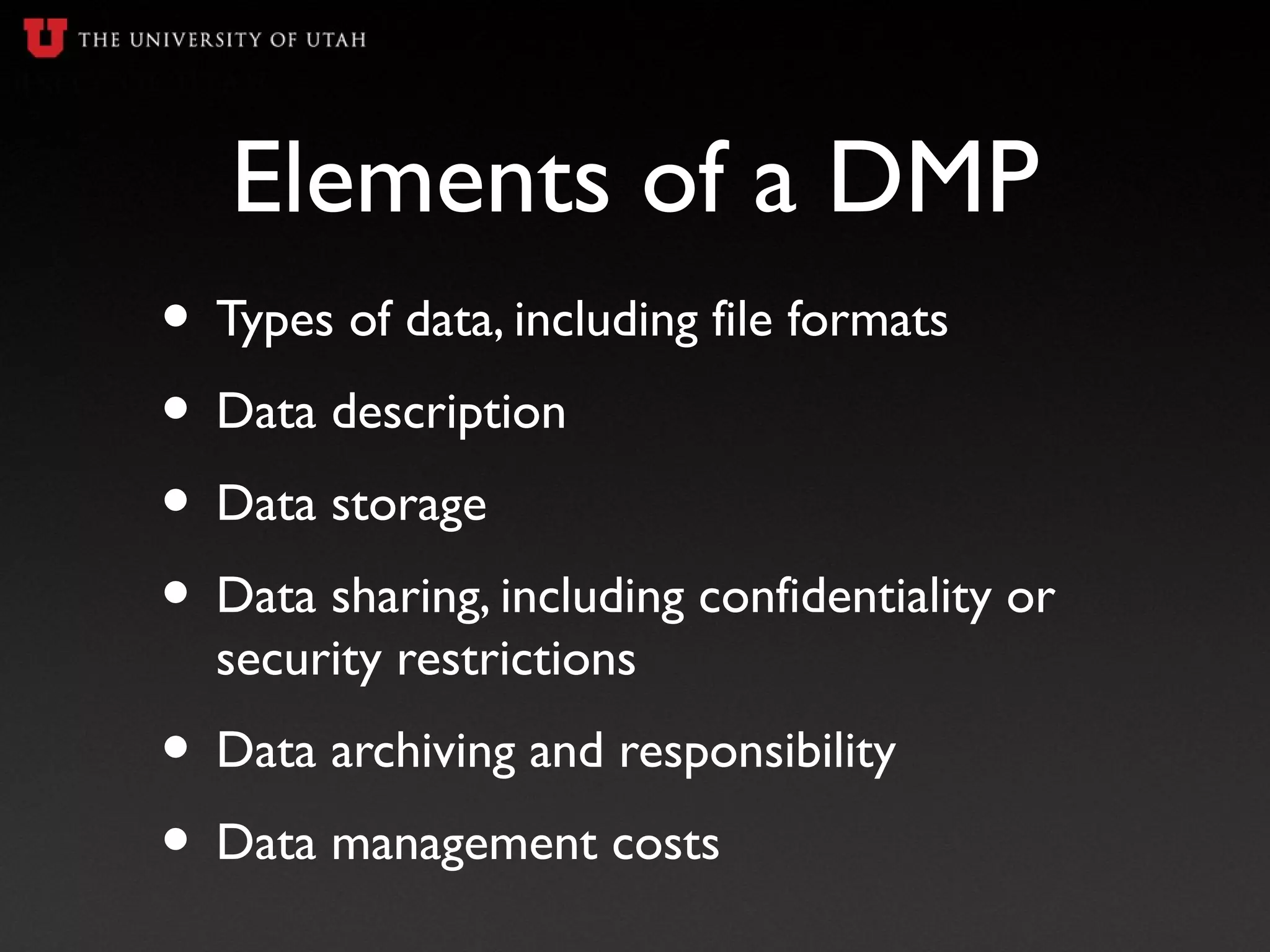
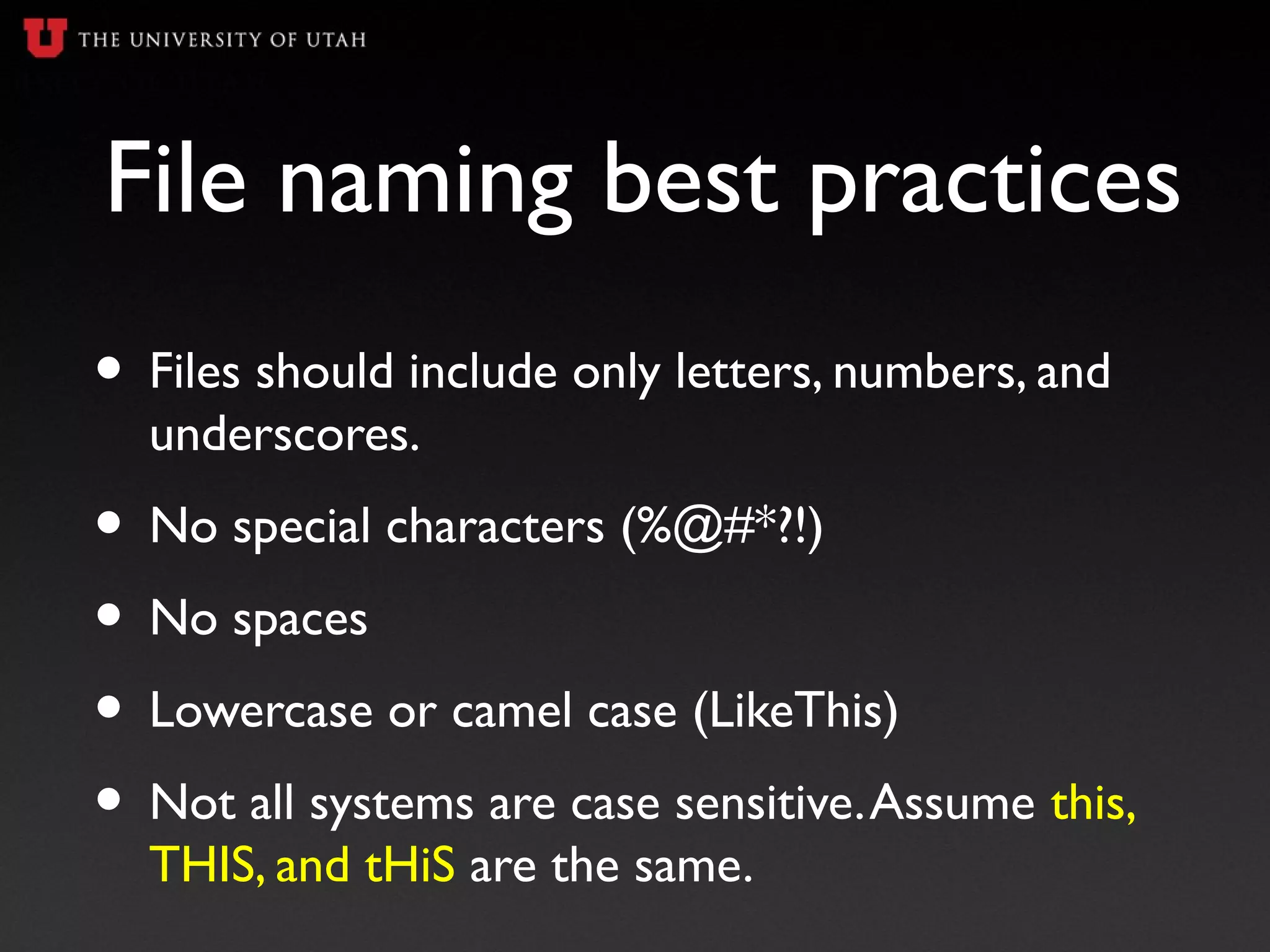
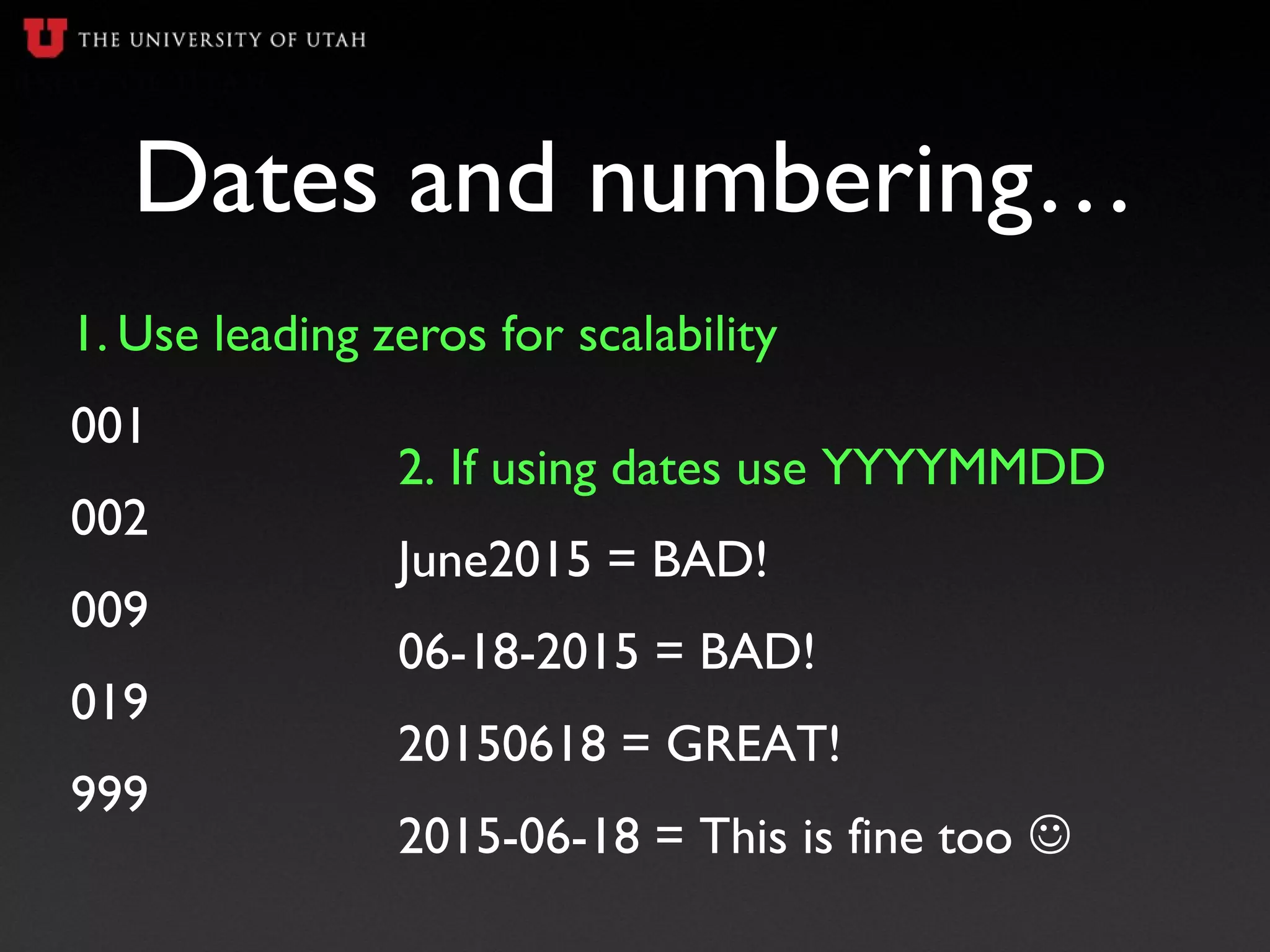
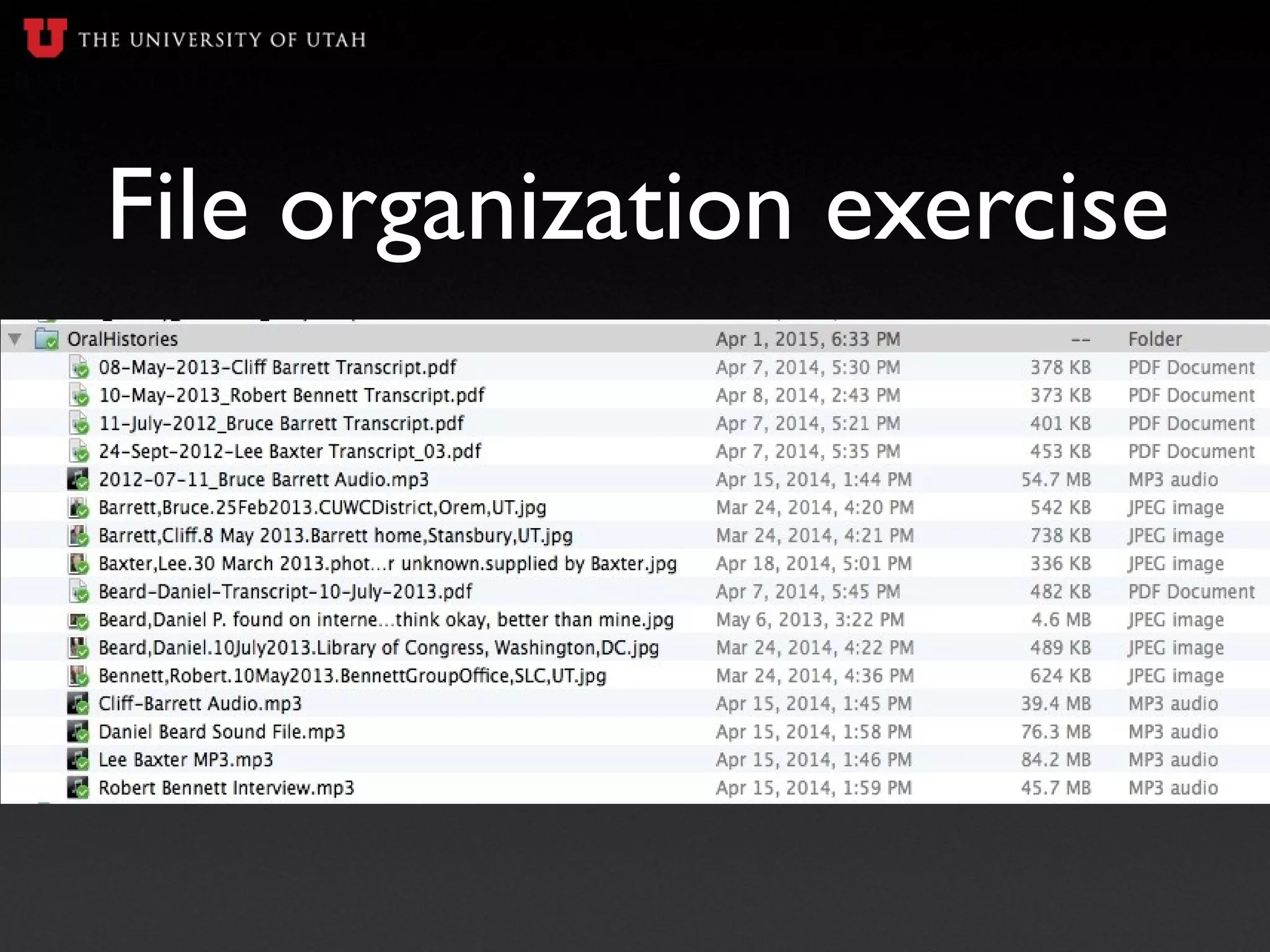
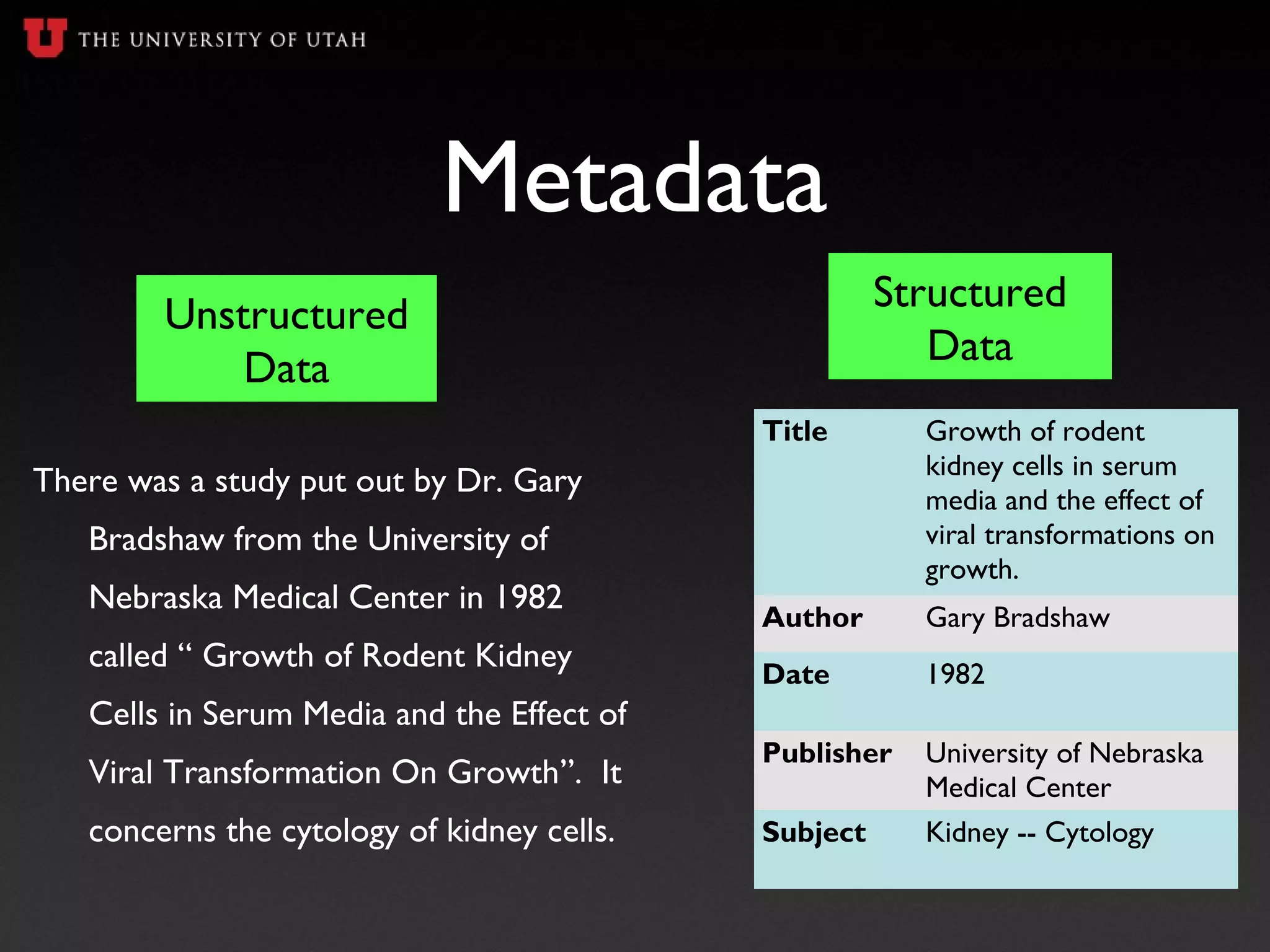
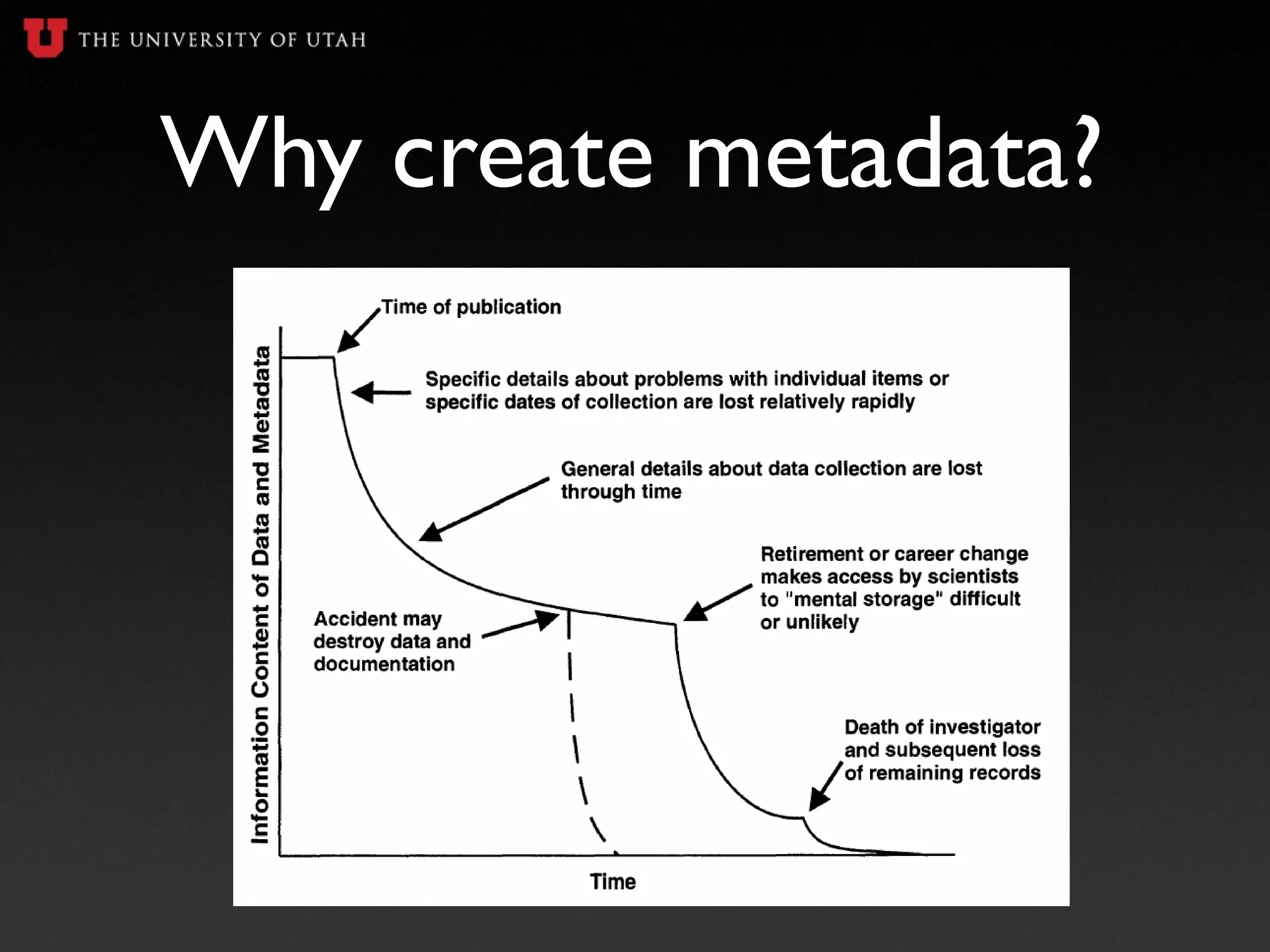
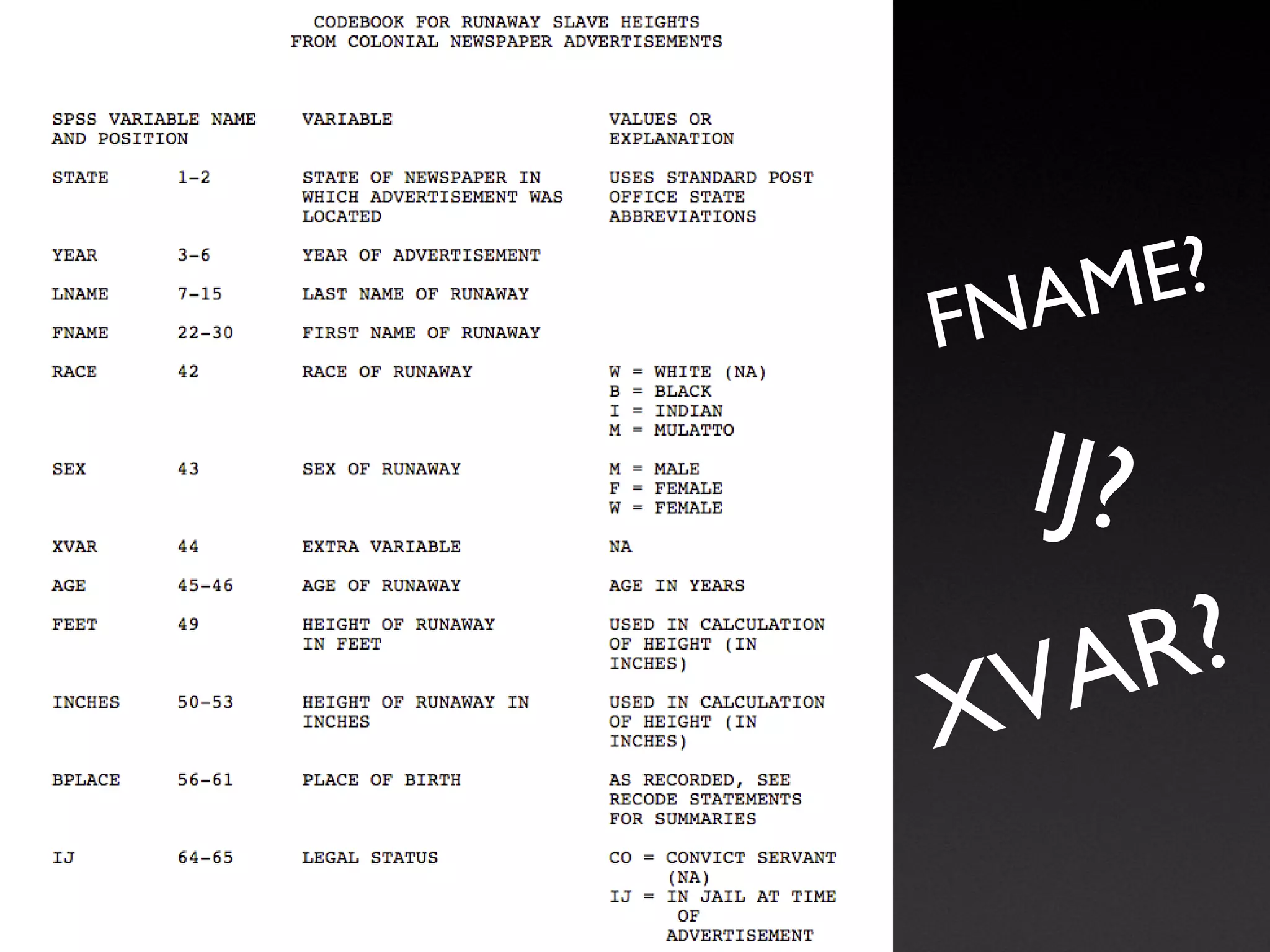
The document is a presentation on data management for undergraduate researchers, highlighting the importance of managing data effectively throughout the research process. It covers essential topics including data management plans, file naming conventions, metadata, and storage options to ensure research reproducibility and compliance with grant requirements. Key takeaways emphasize starting data management early, documenting data clearly, and planning for long-term data archiving.