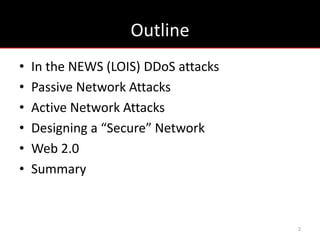
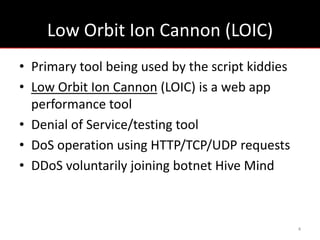
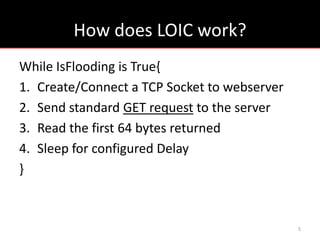
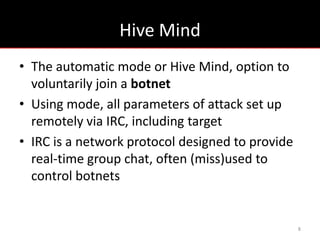
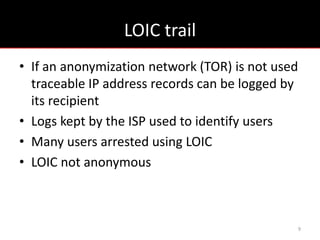
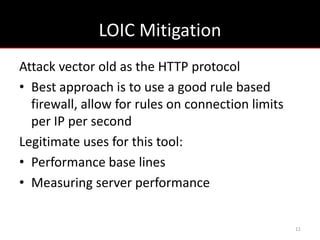
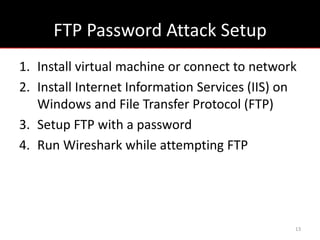
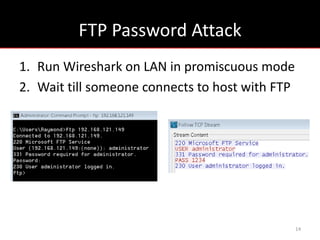
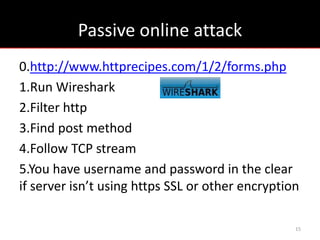
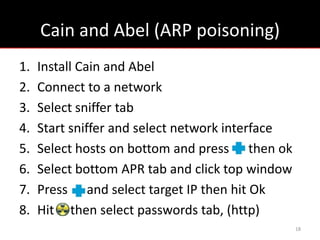
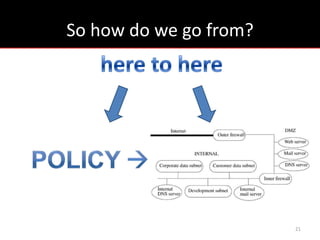
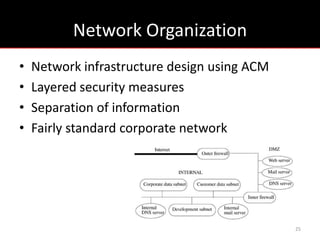
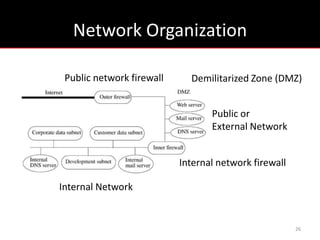
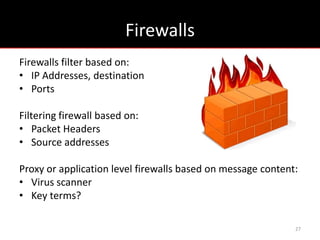
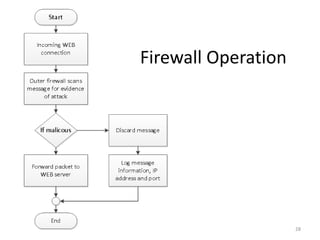
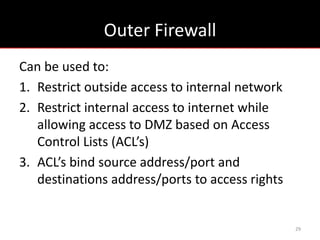
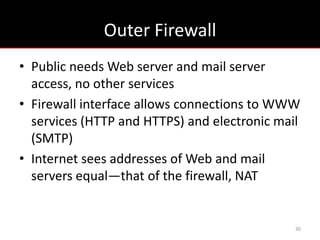
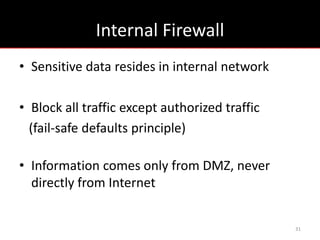
Network security involves designing secure networks through policies and infrastructure to protect against both passive and active attacks. Passive attacks involve monitoring network traffic to obtain sensitive information like passwords transmitted in clear text. Active attacks disrupt networks through techniques like denial of service attacks. Network design separates public, private, and DMZ networks with multiple firewalls that filter traffic between networks based on IP addresses and ports. Recent research shows attackers frequently target web servers using search and common exploits like password cracking and spam. Maintaining secure network design principles with layers of defense can help mitigate risks from both internal and external threats.