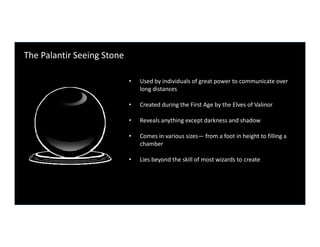
The Palantir Seeing Stone
•
5 likes•2,481 views
Presentation given at Enterprise 2.0 San Francisco 2009
Report
Share
Report
Share
Download to read offline
Recommended
Palantir, Quid, RecordedFuture: Augmented Intelligence Frontier

Origins of "Augmented Intelligence" concept (based on the Shyam Sankar's TED talk)
List of top 3 Augmented Intelligence companies with deep dive into their products' details (and quick look into their business models, w/o numbers).
Deep dive into the "Augmented Intelligence" technology (by using Palantir as an example).
A look at the future of the Augmented Intelligence.
Big Data and Analytics: The IBM Perspective

Gareth Mitchell-Jones, Associate Partner Big Data & Analytics at IBM, shares his thoughts on the hot topic of Big Data from his unique perspective at an IPA 44 Club event in London. To learn more about The IPA visit www.ipa.co.uk and The 44 Club here http://www.ipa.co.uk/groups/44-club-2
Personal Finance for Engineers (Palantir 2014)

This is the version of my talk, Personal Finance for Engineers, given at Palantir in Palo Alto, CA on April 7, 2014.
How does Microsoft solve Big Data?

So you got a handle on what Big Data is and how you can use it to find business value in your data. Now you need an understanding of the Microsoft products that can be used to create a Big Data solution. Microsoft has many pieces of the puzzle and in this presentation I will show how they fit together. How does Microsoft enhance and add value to Big Data? From collecting data, transforming it, storing it, to visualizing it, I will show you Microsoft’s solutions for every step of the way
Virdata: lessons learned from the Internet of Things and M2M Cloud Services @...

Presentation I gave at the IBM Big Data Developers meetup group in San Jose, CA.
There is also a video available of this talk at:
https://www.youtube.com/watch?v=TSt49yPBmW0&t=7m59s
Recommended
Palantir, Quid, RecordedFuture: Augmented Intelligence Frontier

Origins of "Augmented Intelligence" concept (based on the Shyam Sankar's TED talk)
List of top 3 Augmented Intelligence companies with deep dive into their products' details (and quick look into their business models, w/o numbers).
Deep dive into the "Augmented Intelligence" technology (by using Palantir as an example).
A look at the future of the Augmented Intelligence.
Big Data and Analytics: The IBM Perspective

Gareth Mitchell-Jones, Associate Partner Big Data & Analytics at IBM, shares his thoughts on the hot topic of Big Data from his unique perspective at an IPA 44 Club event in London. To learn more about The IPA visit www.ipa.co.uk and The 44 Club here http://www.ipa.co.uk/groups/44-club-2
Personal Finance for Engineers (Palantir 2014)

This is the version of my talk, Personal Finance for Engineers, given at Palantir in Palo Alto, CA on April 7, 2014.
How does Microsoft solve Big Data?

So you got a handle on what Big Data is and how you can use it to find business value in your data. Now you need an understanding of the Microsoft products that can be used to create a Big Data solution. Microsoft has many pieces of the puzzle and in this presentation I will show how they fit together. How does Microsoft enhance and add value to Big Data? From collecting data, transforming it, storing it, to visualizing it, I will show you Microsoft’s solutions for every step of the way
Virdata: lessons learned from the Internet of Things and M2M Cloud Services @...

Presentation I gave at the IBM Big Data Developers meetup group in San Jose, CA.
There is also a video available of this talk at:
https://www.youtube.com/watch?v=TSt49yPBmW0&t=7m59s
Personal Finance for Palantir (June 2015)

This is the version of my talk, Personal Finance for Engineers, that was given at Palantir on June 3, 2015.
Natural Language Processing with Graph Databases and Neo4j

Originally presented at DataDay Texas in Austin, this presentation shows how a graph database such as Neo4j can be used for common natural language processing tasks, such as building a word adjacency graph, mining word associations, summarization and keyword extraction and content recommendation.
Four ways data is improving healthcare operations

Here are four ways data is improving various aspects of healthcare operations, from population health management to revenue cycle management.
Tableau Drive, A new methodology for scaling your analytic culture

Tableau Drive is a methodology for scaling out self-service analytics. Drive is based on best practices from successful enterprise deployments. The methodology relies on iterative, agile methods that are faster and more effective than traditional long-cycle deployment. A cornerstone of the approach is a new model of a partnership between business and IT.
The Drive Methodology is available for free. Some organizations will choose to execute Drive themselves; others will look to Tableau Services or Tableau Partners for expert help.
Artificial Intelligence

This Presentation will give you an overview about Artificial Intelligence : definition, advantages , disadvantages , benefits , applications .
We hope it to be useful .
Big Data Analytics with Hadoop

Hadoop, flexible and available architecture for large scale computation and data processing on a network of commodity hardware.
Corporate Intelligence: Bridging the security and intelligence community

Presentation given at Rochester 2600 about the similarities between competitive intelligence/corporate spying and infosec.
Open Secrets of the Defense Industry: Building Your Own Intelligence Program ...

Respond proactively to threats like a defense contractor. It’s more realistic than you might think!
A practical guide of how to build intelligence-driven cyber defenses using open source software, based on real implementations of best practices, adapted from the Lockheed Martin Cyber Kill Chain model.
Managing infrastructure for an Internet of Things, Rachel Chalmers n•fluence ...

Rachel Chalmers' presentation from n•fluence 2012.
For more information on Nimsoft, visit: http://www.nimsoft.com.
WSO2Con EU 2015: Open Source Journey at Ordnance Survey

WSO2Con EU 2015: Open Source Journey at Ordnance Survey
When five years ago the outgoing Minister of Finance Liam Burne left a note at the treasury that said “there’s no cash left” it concentrated minds in the Civil Service and an ‘Open Source First’ policy was born. This led to a successful WSO2 engagement, the proliferation of open source solutions at OS, and ultimately a significant saving in software costs. This session will discusses the highlights and pitfalls along the way.
Presenter:
Hillary Corney
Principle Architect,
Ordnance Survey
Deploying, Managing, and Leveraging Honeypots in the Enterprise using Open So...

2015 is turning out to be the most spectacular year of high profile compromises across almost every vertical and many companies are starting to consider new options to raise the bar for intrusion detection and incident response, including deploying honeypots.
In this workshop we will present an overview of the current state of the art of leveraging open source tools to build a novel intrusion detection system inside the enterprise. We will discuss the pros/cons and ins/outs of several major open source honeypots as well as how to manage and deploy these sensors using the Modern Honey Network, Splunk, as well as integration into other systems such as ArcSight. We will discuss real world deployments of honeypots, what worked and what didn't as well as recommendations for getting the most out of these non-convention network sensors.
Being open (source) in the traditionally secretive field of quant finance.

The field of quantitative finance is intensely competitive and maniacally secretive as a rule. The tendency toward secrecy is perhaps unsurprising given that the smallest of competitive advantages can translate to substantial profits. Indeed, over the past decade a growing list of legal prosecutions for alleged code theft or misuse have underscored how high the stakes can be for developers looking to leverage and contribute to open source projects. Notable exceptions to this approach include work from Wes McKinney and Travis Oliphant, whose work on open source projects like pandas and numpy, which have gained widespread adoption. In this talk we will review some of the costs and benefits of engaging with open source as a “two way street” and frame the modern quant workflow as a mosaic of open sourced, third party, and proprietary components.
OSINT- Leveraging data into intelligence

Open-source intelligence (OSINT) is intelligence collected from publicly available sources. In the intelligence community (IC), the term "open" refers to overt, publicly available sources (as opposed to covert or clandestine sources); it is not related to open-source software or public intelligence.
Privacy is an Illusion and you’re all losers! - Cryptocow - Infosecurity 2013

Privacy is an illusion and you’re all losers!
or how 1984 was a manual for our panopticon society
By Cain Ransbottyn - @ransbottyn
More Related Content
Viewers also liked
Personal Finance for Palantir (June 2015)

This is the version of my talk, Personal Finance for Engineers, that was given at Palantir on June 3, 2015.
Natural Language Processing with Graph Databases and Neo4j

Originally presented at DataDay Texas in Austin, this presentation shows how a graph database such as Neo4j can be used for common natural language processing tasks, such as building a word adjacency graph, mining word associations, summarization and keyword extraction and content recommendation.
Four ways data is improving healthcare operations

Here are four ways data is improving various aspects of healthcare operations, from population health management to revenue cycle management.
Tableau Drive, A new methodology for scaling your analytic culture

Tableau Drive is a methodology for scaling out self-service analytics. Drive is based on best practices from successful enterprise deployments. The methodology relies on iterative, agile methods that are faster and more effective than traditional long-cycle deployment. A cornerstone of the approach is a new model of a partnership between business and IT.
The Drive Methodology is available for free. Some organizations will choose to execute Drive themselves; others will look to Tableau Services or Tableau Partners for expert help.
Artificial Intelligence

This Presentation will give you an overview about Artificial Intelligence : definition, advantages , disadvantages , benefits , applications .
We hope it to be useful .
Big Data Analytics with Hadoop

Hadoop, flexible and available architecture for large scale computation and data processing on a network of commodity hardware.
Viewers also liked (10)
Natural Language Processing with Graph Databases and Neo4j

Natural Language Processing with Graph Databases and Neo4j
Tableau Drive, A new methodology for scaling your analytic culture

Tableau Drive, A new methodology for scaling your analytic culture
Similar to The Palantir Seeing Stone
Corporate Intelligence: Bridging the security and intelligence community

Presentation given at Rochester 2600 about the similarities between competitive intelligence/corporate spying and infosec.
Open Secrets of the Defense Industry: Building Your Own Intelligence Program ...

Respond proactively to threats like a defense contractor. It’s more realistic than you might think!
A practical guide of how to build intelligence-driven cyber defenses using open source software, based on real implementations of best practices, adapted from the Lockheed Martin Cyber Kill Chain model.
Managing infrastructure for an Internet of Things, Rachel Chalmers n•fluence ...

Rachel Chalmers' presentation from n•fluence 2012.
For more information on Nimsoft, visit: http://www.nimsoft.com.
WSO2Con EU 2015: Open Source Journey at Ordnance Survey

WSO2Con EU 2015: Open Source Journey at Ordnance Survey
When five years ago the outgoing Minister of Finance Liam Burne left a note at the treasury that said “there’s no cash left” it concentrated minds in the Civil Service and an ‘Open Source First’ policy was born. This led to a successful WSO2 engagement, the proliferation of open source solutions at OS, and ultimately a significant saving in software costs. This session will discusses the highlights and pitfalls along the way.
Presenter:
Hillary Corney
Principle Architect,
Ordnance Survey
Deploying, Managing, and Leveraging Honeypots in the Enterprise using Open So...

2015 is turning out to be the most spectacular year of high profile compromises across almost every vertical and many companies are starting to consider new options to raise the bar for intrusion detection and incident response, including deploying honeypots.
In this workshop we will present an overview of the current state of the art of leveraging open source tools to build a novel intrusion detection system inside the enterprise. We will discuss the pros/cons and ins/outs of several major open source honeypots as well as how to manage and deploy these sensors using the Modern Honey Network, Splunk, as well as integration into other systems such as ArcSight. We will discuss real world deployments of honeypots, what worked and what didn't as well as recommendations for getting the most out of these non-convention network sensors.
Being open (source) in the traditionally secretive field of quant finance.

The field of quantitative finance is intensely competitive and maniacally secretive as a rule. The tendency toward secrecy is perhaps unsurprising given that the smallest of competitive advantages can translate to substantial profits. Indeed, over the past decade a growing list of legal prosecutions for alleged code theft or misuse have underscored how high the stakes can be for developers looking to leverage and contribute to open source projects. Notable exceptions to this approach include work from Wes McKinney and Travis Oliphant, whose work on open source projects like pandas and numpy, which have gained widespread adoption. In this talk we will review some of the costs and benefits of engaging with open source as a “two way street” and frame the modern quant workflow as a mosaic of open sourced, third party, and proprietary components.
OSINT- Leveraging data into intelligence

Open-source intelligence (OSINT) is intelligence collected from publicly available sources. In the intelligence community (IC), the term "open" refers to overt, publicly available sources (as opposed to covert or clandestine sources); it is not related to open-source software or public intelligence.
Privacy is an Illusion and you’re all losers! - Cryptocow - Infosecurity 2013

Privacy is an illusion and you’re all losers!
or how 1984 was a manual for our panopticon society
By Cain Ransbottyn - @ransbottyn
Cortana Analytics Workshop: The Future of Analytics

Joseph Sirosh. A new era of analytics is being engendered by cloud computing. The cloud gives us the power to collect and integrate data from an enormous variety of sources, to process big data at amazing scale and economics, to dramatically simplify development and deployment, and offer amazing intelligent APIs and applications as hosted services. In this keynote talk, Joseph will review with demos and examples how these game-changing developments will change how we live, work and play, and show the enormous opportunities for customers and partners to capitalize on these innovations. Go to https://channel9.msdn.com/ to find the recording of this session.
Building and Deploying a Global Intranet with Liferay

As we all know, Enterprise 2.0 is no longer a hype but a necessity in a new era where more organizations are starting to have a global presence. It has become crucial for global enterprises to provide their employees with an effective means of collaboration, communication and socialization to not just increase productivity, but also strengthen employee loyalty.
This presentation will discuss how Liferay Portal facilitates the architecture of global intranets that meets common challenges, along with practical examples of how it can be used to achieve the results expected from an Enterprise 2.0 intranet.
Distributed Sensor Data Contextualization for Threat Intelligence Analysis

As organizations operationalize diverse network sensors of various types, from passive sensors to DNS sinkholes to honeypots, there are many opportunities to combine this data for increased contextual awareness for network defense and threat intelligence analysis. In this presentation, we discuss our experiences by analyzing data collected from distributed honeypot sensors, p0f, snort/suricata, and botnet sinkholes as well as enrichments from PDNS and malware sandboxing. We talk through how we can answer the following questions in an automated fashion: What is the profile of the attacking system? Is the host scanning/attacking my network an infected workstation, an ephemeral scanning/exploitation box, or a compromised web server? If it is a compromised server, what are some possible vulnerabilities exploited by the attacker? What vulnerabilities (CVEs) has this attacker been seen exploiting in the wild and what tools do they drop? Is this attack part of a distributed campaign or is it limited to my network?
Introduction to Neo4j

With the introduction of the Neo4j Graph Platform and increased adoption of graph database technology across all industries, now is a better time than ever to get started with graphs.
Join us for this introduction to Neo4j and graph databases. We'll discuss the primary use cases for graph databases and explore the properties of Neo4j that make those use cases possible.
Big Data Landscape 2018

By Salman Jaffer, CFA - Singapore Technology Lead, TMS, Thomson Reuters Singapore.
A look at Big Data technologies, trends and applications.
Catching the Golden Snitch- Leveraging Threat Intelligence Platforms to Defen...

Catching the Golden Snitch- Leveraging Threat Intelligence Platforms to Defen...Chi En (Ashley) Shen
Speaker: Ashley Shen, Zha0Similar to The Palantir Seeing Stone (20)
Corporate Intelligence: Bridging the security and intelligence community

Corporate Intelligence: Bridging the security and intelligence community
Open Secrets of the Defense Industry: Building Your Own Intelligence Program ...

Open Secrets of the Defense Industry: Building Your Own Intelligence Program ...
Managing infrastructure for an Internet of Things, Rachel Chalmers n•fluence ...

Managing infrastructure for an Internet of Things, Rachel Chalmers n•fluence ...
WSO2Con EU 2015: Open Source Journey at Ordnance Survey

WSO2Con EU 2015: Open Source Journey at Ordnance Survey
Deploying, Managing, and Leveraging Honeypots in the Enterprise using Open So...

Deploying, Managing, and Leveraging Honeypots in the Enterprise using Open So...
Being open (source) in the traditionally secretive field of quant finance.

Being open (source) in the traditionally secretive field of quant finance.
Privacy is an Illusion and you’re all losers! - Cryptocow - Infosecurity 2013

Privacy is an Illusion and you’re all losers! - Cryptocow - Infosecurity 2013
Cortana Analytics Workshop: The Future of Analytics

Cortana Analytics Workshop: The Future of Analytics
Building and Deploying a Global Intranet with Liferay

Building and Deploying a Global Intranet with Liferay
Distributed Sensor Data Contextualization for Threat Intelligence Analysis

Distributed Sensor Data Contextualization for Threat Intelligence Analysis
Catching the Golden Snitch- Leveraging Threat Intelligence Platforms to Defen...

Catching the Golden Snitch- Leveraging Threat Intelligence Platforms to Defen...
More from Enterprise 2.0 Conference
The Hardest Problem in E2.0 - Changing Our Culture

Bert Sandie, Director, Learning & Development, Electronic Arts, Inc's Keynote Address at the Enterprise 2.0 Conference in Boston 2011.
Using real-world experiences to demonstrate the critical importance of why culture and employee behaviors need our full attention to full leverage collaboration and knowledge sharing inside our organizations.
The Ex-CXO: Why Your Employees Will be Running Your Enterprise in 5 Years, an...

The Ex-CXO: Why Your Employees Will be Running Your Enterprise in 5 Years, an...Enterprise 2.0 Conference
Sara M. Roberts, Book Author and President & CEO, Roberts Golden Consulting, Keynote Address from the Enterprise 2.0 Conference in Boston 2011.
The mandate for today’s enterprise is adapting itself to the millions of decisions made every day by its employees—the key people on the ground who are seeing operational short-cuts and competitive advantage in real time. Enterprises must embrace this sea change, driven by ever more democratic collaboration and communications tools, and prepare to support, adapt, and leverage the wisdom of the many.
Social Business Intelligence: The Future of Listening

Lee Bryant, Co-founder and Director, Headshift, Keynotes at the Enterprise 2.0 Conference in Boston 2011.
Social media monitoring and listening has become a hot topic recently, but cutting through the noise to identify actionable insights is not easy, and current practice often goes no further than the marketing department. This talk will look at how social analytics can leverage internal networks to make sense of customer insights and help drive business improvement.
Pulling It Together: Connecting External Activities With Internal Conversations

Pulling It Together: Connecting External Activities With Internal ConversationsEnterprise 2.0 Conference
Ming Kwan, Global Digital Marketing Manager, Nokia's Keynote address at the Enterprise 2.0 Conference in Boston 2011.
Social activities in organizations are currently focused on three, distinct, areas. Internal – Enterprise 2.0, External – consumer engagement and Partner collaboration. This has led to different parts of our organization working on their own social initiatives, creating social silos. We are now connecting insights from our external activities with internal systems to reap the benefits of ownership, visibility & transparency.
Performance and Passion: Creating New Connections

John Hagel, The Power of Pull and Co-Chairman, Center for the Edge, Deloitte & Touche's Keynote presentaion from Enterprise 2.0 Conference in Boston on June 21, 2011.
The successful transition to Enterprise 2.0 hinges on explicitly tying social software deployments to performance metrics that matter. But these metrics have an even more powerful, second-order effect: they foster passion among participants in ways that accelerate learning and performance improvement. Weaving together performance and passion gives companies a significant advantage in a world of steadily increasing economic pressure.
Developing a Cutting Edge Social Enterprise Software Strategy that Leverages ...

Developing a Cutting Edge Social Enterprise Software Strategy that Leverages ...Enterprise 2.0 Conference
The Promise of Enterprise Prediction Markets

Presentation by CrowdCast given at Enterprise 2.0 Boston 2009
Driving Virtual Team Productivity

Presentation by Volvo Information Technology at Enterprise 2.0 Boston 2009.
Applying the Successful Strategies of Social Networks to the Enterprise

Presentation given by Aaron Levie, CEO and Co-Founder of Box.net at Enterprise 2.0 Boston 2009.
Multi-Enterprise 2.0 - Leveraging Social Software for Real ROI

Presentation given by Nick Parnaby, Founder & COO of RollStream at Enterprie 2.0 Boston 2009
Ignite Technologies Overview

Presentation on Ignite Technologies, Inc. given at Enterprise 2.0 Boston 2009
Sincere Marketing in an Age of Skepticism: Unthinking the Consumer Experience

Sincere Marketing in an Age of Skepticism: Unthinking the Consumer ExperienceEnterprise 2.0 Conference
Presentation given by Romi Mahajan, Chief Marketing Officer of Ascentium Corporation at Enterprise 2.0 Boston 2009Angels & Demons

Presentation given by Karyn German, VP of Enterprise Practice Management at newsgator at Enterprise 2.0 Boston 2009
Jump Starting Collaboration with Social Search

Presentation given by Tom Smithyman of Vivisimo at Enterprise 2.0 Boston 2009
Connecting the Dots with Conectbeam Social Networking Services

Presentation given by Farsheed Tari, VP of Product Management of Connectbeam at Enterprise 2.0 Boston 2009.
Real World: Customer Edition Panel "Stories about Social Computing Deployment"

Real World: Customer Edition Panel "Stories about Social Computing Deployment"Enterprise 2.0 Conference
Panel discussion led by Alina Fu, Product Manager of Microsoft at Enterprise 2.0 Boston 2009Is Enterprise Search Ripe for Open Source Disruption?

Presentation given by Larry Cannell, Senior Analyst of Burton Group at Enterprise 2.0 Boston 2009
Enterprise 2.0 Anti-Patterns, ROI and Metrics

Presentation given by Jennifer Okimoto, Senior Managing Consultant, Human Capital Management of IBM at Enterprise 2.0 Boston 2009
Reality 2.0: Enterprise Social Networks (A Field Research Study)

Presentation given by Michael Gotta, Principal Analyst of Burton Group at Enterprise 2.0 Boston 2009
More from Enterprise 2.0 Conference (20)
The Hardest Problem in E2.0 - Changing Our Culture

The Hardest Problem in E2.0 - Changing Our Culture
The Ex-CXO: Why Your Employees Will be Running Your Enterprise in 5 Years, an...

The Ex-CXO: Why Your Employees Will be Running Your Enterprise in 5 Years, an...
Social Business Intelligence: The Future of Listening

Social Business Intelligence: The Future of Listening
Pulling It Together: Connecting External Activities With Internal Conversations

Pulling It Together: Connecting External Activities With Internal Conversations
Developing a Cutting Edge Social Enterprise Software Strategy that Leverages ...

Developing a Cutting Edge Social Enterprise Software Strategy that Leverages ...
Applying the Successful Strategies of Social Networks to the Enterprise

Applying the Successful Strategies of Social Networks to the Enterprise
Multi-Enterprise 2.0 - Leveraging Social Software for Real ROI

Multi-Enterprise 2.0 - Leveraging Social Software for Real ROI
Sincere Marketing in an Age of Skepticism: Unthinking the Consumer Experience

Sincere Marketing in an Age of Skepticism: Unthinking the Consumer Experience
Connecting the Dots with Conectbeam Social Networking Services

Connecting the Dots with Conectbeam Social Networking Services
Real World: Customer Edition Panel "Stories about Social Computing Deployment"

Real World: Customer Edition Panel "Stories about Social Computing Deployment"
Is Enterprise Search Ripe for Open Source Disruption?

Is Enterprise Search Ripe for Open Source Disruption?
Reality 2.0: Enterprise Social Networks (A Field Research Study)

Reality 2.0: Enterprise Social Networks (A Field Research Study)
Recently uploaded
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
A tale of scale & speed: How the US Navy is enabling software delivery from l...

Rapid and secure feature delivery is a goal across every application team and every branch of the DoD. The Navy’s DevSecOps platform, Party Barge, has achieved:
- Reduction in onboarding time from 5 weeks to 1 day
- Improved developer experience and productivity through actionable findings and reduction of false positives
- Maintenance of superior security standards and inherent policy enforcement with Authorization to Operate (ATO)
Development teams can ship efficiently and ensure applications are cyber ready for Navy Authorizing Officials (AOs). In this webinar, Sigma Defense and Anchore will give attendees a look behind the scenes and demo secure pipeline automation and security artifacts that speed up application ATO and time to production.
We will cover:
- How to remove silos in DevSecOps
- How to build efficient development pipeline roles and component templates
- How to deliver security artifacts that matter for ATO’s (SBOMs, vulnerability reports, and policy evidence)
- How to streamline operations with automated policy checks on container images
Quantum Computing: Current Landscape and the Future Role of APIs

The current state of quantum computing and the role of APIs to take it mainstream.
Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...

The choice of an operating system plays a pivotal role in shaping our computing experience. For decades, Microsoft's Windows has dominated the market, offering a familiar and widely adopted platform for personal and professional use. However, as technological advancements continue to push the boundaries of innovation, alternative operating systems have emerged, challenging the status quo and offering users a fresh perspective on computing.
One such alternative that has garnered significant attention and acclaim is Nitrux Linux 3.5.0, a sleek, powerful, and user-friendly Linux distribution that promises to redefine the way we interact with our devices. With its focus on performance, security, and customization, Nitrux Linux presents a compelling case for those seeking to break free from the constraints of proprietary software and embrace the freedom and flexibility of open-source computing.
Essentials of Automations: The Art of Triggers and Actions in FME

In this second installment of our Essentials of Automations webinar series, we’ll explore the landscape of triggers and actions, guiding you through the nuances of authoring and adapting workspaces for seamless automations. Gain an understanding of the full spectrum of triggers and actions available in FME, empowering you to enhance your workspaces for efficient automation.
We’ll kick things off by showcasing the most commonly used event-based triggers, introducing you to various automation workflows like manual triggers, schedules, directory watchers, and more. Plus, see how these elements play out in real scenarios.
Whether you’re tweaking your current setup or building from the ground up, this session will arm you with the tools and insights needed to transform your FME usage into a powerhouse of productivity. Join us to discover effective strategies that simplify complex processes, enhancing your productivity and transforming your data management practices with FME. Let’s turn complexity into clarity and make your workspaces work wonders!
Climate Impact of Software Testing at Nordic Testing Days

My slides at Nordic Testing Days 6.6.2024
Climate impact / sustainability of software testing discussed on the talk. ICT and testing must carry their part of global responsibility to help with the climat warming. We can minimize the carbon footprint but we can also have a carbon handprint, a positive impact on the climate. Quality characteristics can be added with sustainability, and then measured continuously. Test environments can be used less, and in smaller scale and on demand. Test techniques can be used in optimizing or minimizing number of tests. Test automation can be used to speed up testing.
Video Streaming: Then, Now, and in the Future

In his public lecture, Christian Timmerer provides insights into the fascinating history of video streaming, starting from its humble beginnings before YouTube to the groundbreaking technologies that now dominate platforms like Netflix and ORF ON. Timmerer also presents provocative contributions of his own that have significantly influenced the industry. He concludes by looking at future challenges and invites the audience to join in a discussion.
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™

In questo evento online gratuito, organizzato dalla Community Italiana di UiPath, potrai esplorare le nuove funzionalità di Autopilot, il tool che integra l'Intelligenza Artificiale nei processi di sviluppo e utilizzo delle Automazioni.
📕 Vedremo insieme alcuni esempi dell'utilizzo di Autopilot in diversi tool della Suite UiPath:
Autopilot per Studio Web
Autopilot per Studio
Autopilot per Apps
Clipboard AI
GenAI applicata alla Document Understanding
👨🏫👨💻 Speakers:
Stefano Negro, UiPath MVPx3, RPA Tech Lead @ BSP Consultant
Flavio Martinelli, UiPath MVP 2023, Technical Account Manager @UiPath
Andrei Tasca, RPA Solutions Team Lead @NTT Data
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
UiPath Community Day Dubai: AI at Work..

Welcome to the first live UiPath Community Day Dubai! Join us for this unique occasion to meet our local and global UiPath Community and leaders. You will get a full view of the MEA region's automation landscape and the AI Powered automation technology capabilities of UiPath. Also, hosted by our local partners Marc Ellis, you will enjoy a half-day packed with industry insights and automation peers networking.
📕 Curious on our agenda? Wait no more!
10:00 Welcome note - UiPath Community in Dubai
Lovely Sinha, UiPath Community Chapter Leader, UiPath MVPx3, Hyper-automation Consultant, First Abu Dhabi Bank
10:20 A UiPath cross-region MEA overview
Ashraf El Zarka, VP and Managing Director MEA, UiPath
10:35: Customer Success Journey
Deepthi Deepak, Head of Intelligent Automation CoE, First Abu Dhabi Bank
11:15 The UiPath approach to GenAI with our three principles: improve accuracy, supercharge productivity, and automate more
Boris Krumrey, Global VP, Automation Innovation, UiPath
12:15 To discover how Marc Ellis leverages tech-driven solutions in recruitment and managed services.
Brendan Lingam, Director of Sales and Business Development, Marc Ellis
By Design, not by Accident - Agile Venture Bolzano 2024

As presented at the Agile Venture Bolzano, 4.06.2024
Recently uploaded (20)
A tale of scale & speed: How the US Navy is enabling software delivery from l...

A tale of scale & speed: How the US Navy is enabling software delivery from l...
Quantum Computing: Current Landscape and the Future Role of APIs

Quantum Computing: Current Landscape and the Future Role of APIs
Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...

Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...
Assure Contact Center Experiences for Your Customers With ThousandEyes

Assure Contact Center Experiences for Your Customers With ThousandEyes
Essentials of Automations: The Art of Triggers and Actions in FME

Essentials of Automations: The Art of Triggers and Actions in FME
Climate Impact of Software Testing at Nordic Testing Days

Climate Impact of Software Testing at Nordic Testing Days
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™

Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
By Design, not by Accident - Agile Venture Bolzano 2024

By Design, not by Accident - Agile Venture Bolzano 2024
The Palantir Seeing Stone
- 1. The Palantir Seeing Stone • Used by individuals of great power to communicate over long distances • Created during the First Age by the Elves of Valinor • y g p Reveals anything except darkness and shadow • Comes in various sizes— from a foot in height to filling a chamber • Lies beyond the skill of most wizards to create
- 2. The Palantir Analysis Platform • Used by the governments of the western world and their allies to collaborate over complex data sets • Replaces billion dollar programs at 5% the cost, 1% the time, and works out of the box (0% of the risk) • C d i 2004 b h f d fP P l d Created in 2004 by the co‐founder of PayPal and a team of Stanford computer scientists • Integrates data sets of various sizes from a few Integrates data sets of various sizes— from a few thousand records to hundreds of millions records– for thousands of analysts to collaborate on • Lies beyond the skill of typical coders to create
- 3. PayPal >>>>> Palantir • PayPal wasn’t about sending money; it was about sending money without being defrauded by the sending money without being defrauded by the Russian mob.
- 4. AI/Machine Learning Isn’t Enough... • Artificial Intelligence (AI) • Intelligence Augmentation (IA) • Machines couldn’t catch the fraud, Humans couldn’t scale to the data
- 5. What Does Work? • Human‐Driven Analysis • Using the Computer as a massive lever • Augmenting Human Intelligence
- 7. Escaping The False Tradeoff Combating Terrorism Protecting Civil Liberties
- 8. Same Problem, Different Mission, Different Bespoke Project… Same Product p j Products, not Projects
- 10. Data Integration • Structured & Unstructured Data • Everything from the Enterprise to the Desktop y g p p • Full Enforcement of Security across data sources • Federated Search • Sits on top of, doesn’t replace, your data sources … • Palantir is your Enterprise Data Layer
- 12. Search & Discovery • Search all your enterprise data from a single interface • Use Palantir as a search service (SOA) Use Palantir as a search service (SOA) • Conceptual Searches, Persistent Searches, GeoSearches • Statistical, Temporal, and Geospatial Discovery • Full security across searches ICD 501 compliant Full security across searches, ICD 501 compliant … • Palantir is your Enterprise Search Service Palantir is your Enterprise Search Service
- 17. Knowledge Management • A secure repository for analysis • Analysts can build on each others work Analysts can build on each others’ work • Most robust security model in the IC • Manages resolutions across datasources and security Manages resolutions across datasources and security levels • Revolutionary Revisioning Database Revolutionary Revisioning Database … • Palantir is your Knowledge Management solution Palantir is your Knowledge Management solution
- 18. Collaboration
- 19. Collaboration • Not lip service, real collaboration • Share more than data, share analysis Share more than data share analysis • Inside and across agencies • Across compartments, across classification Across compartments, across classification • Concepts based on how engineers collaborate • Only system designed with civil liberties and privacy y y g p y protections … • Palantir is the Collaborative solution
- 20. Projects – The Platform in IC/Defense – Regulation, Oversight, Transparency – Healthcare Open Projects – GhostNet – Sinjar Records d – GreyGoose – CPI’s subprime meltdown CPI’s subprime meltdown
- 23. Who Broke Into The Computer? The Office of His Holiness The Dalai Lama
