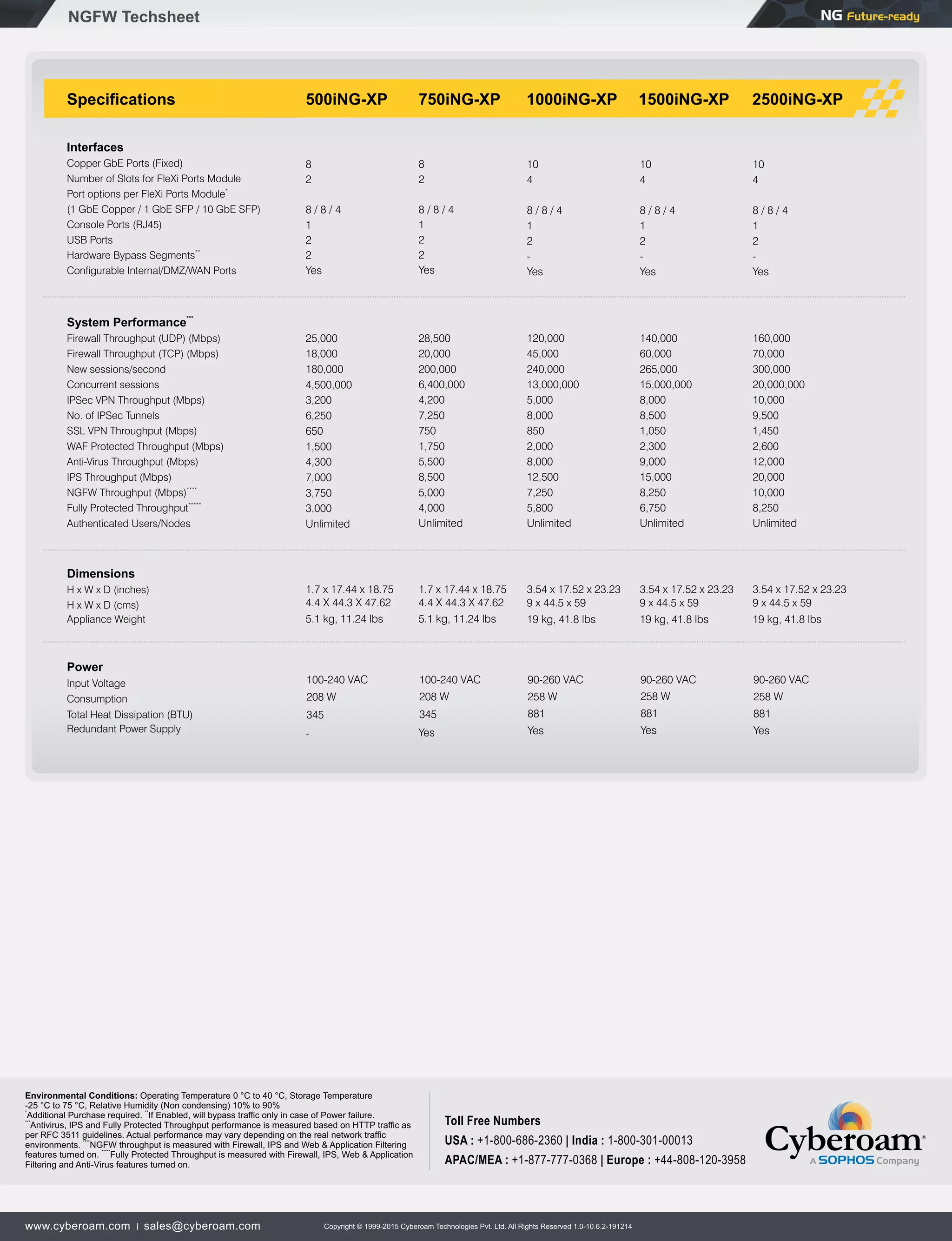
The document discusses Cyberoam next-generation firewalls (NGFW) that offer controls over network layers 2-8 to help enterprises regain security controls lost due to trends like increased mobility, virtualization, and more network users and devices. Cyberoam NGFWs provide features like application inspection and control, website filtering, VPN, bandwidth management, and high performance. They also offer reporting, logging, monitoring, user authentication, and other administrative functions to provide secure and productive connectivity for enterprise networks.