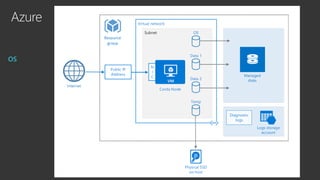
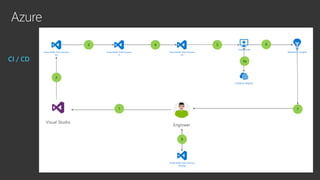
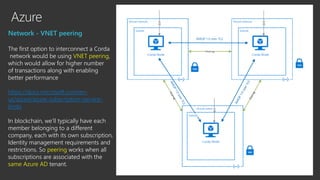
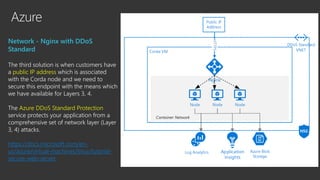
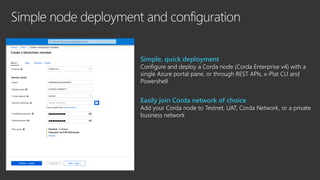
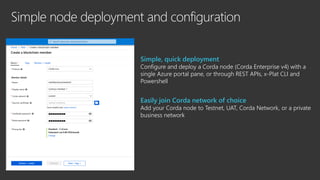
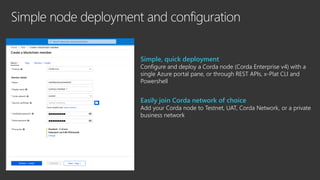
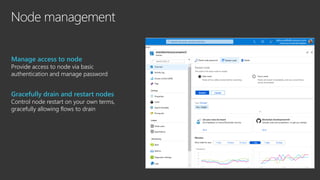
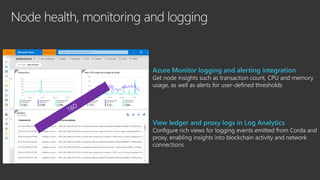
Corda on Azure provides an automated way to deploy Corda nodes on Microsoft Azure with integrated networking and security. It simplifies node deployment through the Azure portal. Nodes can easily join existing Corda networks. Azure services like Key Vault integrate with Corda for certificate management. Virtual networks secure node communication, with options for VNET peering or site-to-site VPN. Continuous integration deploys updates. Monitoring integrates with Azure services for node insights.