This document provides information about cookies including:
- Cookies were invented by Netscape to create online shopping carts that could persist between browser sessions.
- Cookies are small pieces of data stored in text files on a user's device by websites visited by the user.
- Cookies can store information like login details, preferences, and shopping cart contents to enhance user experience on websites.
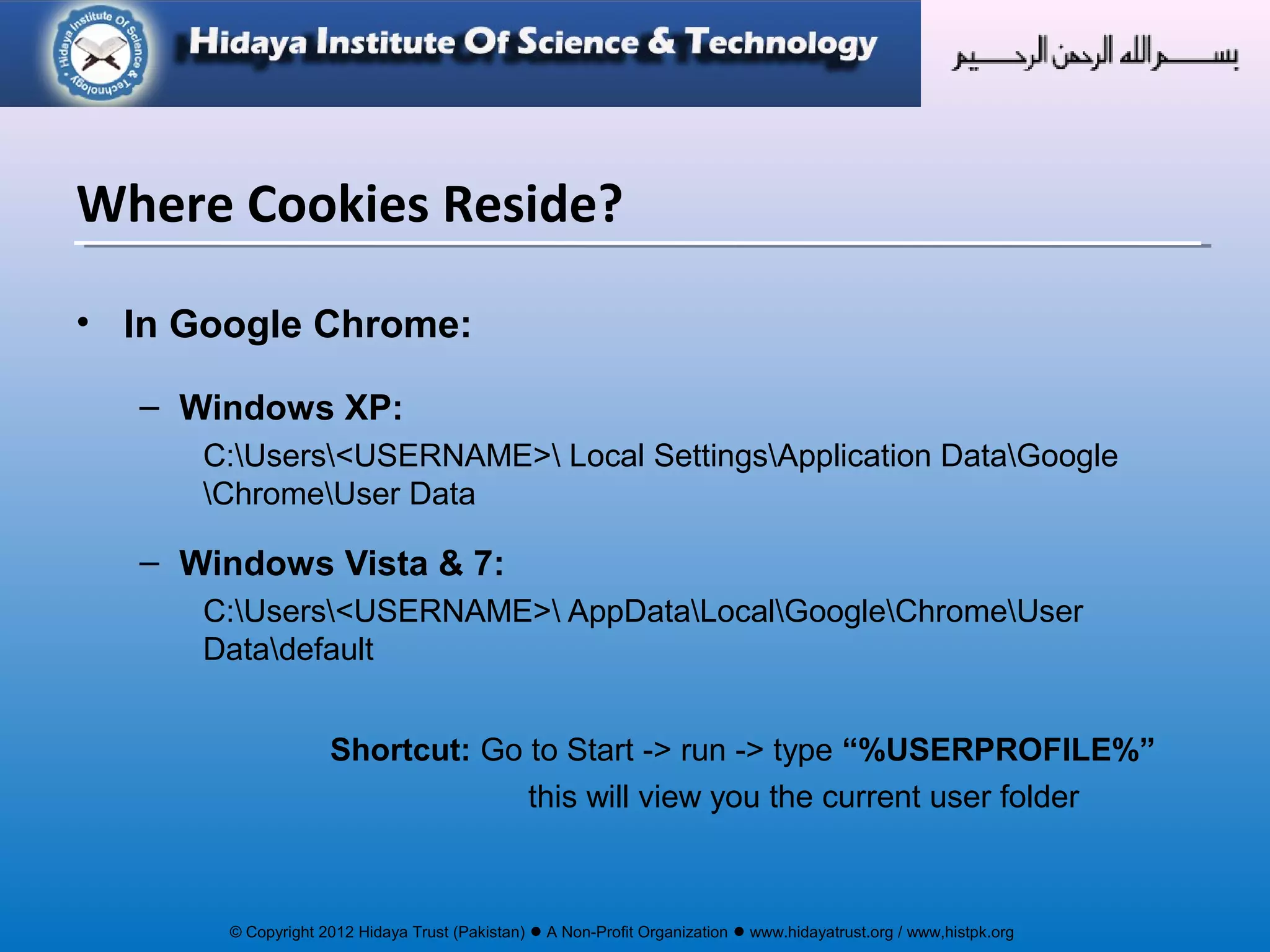
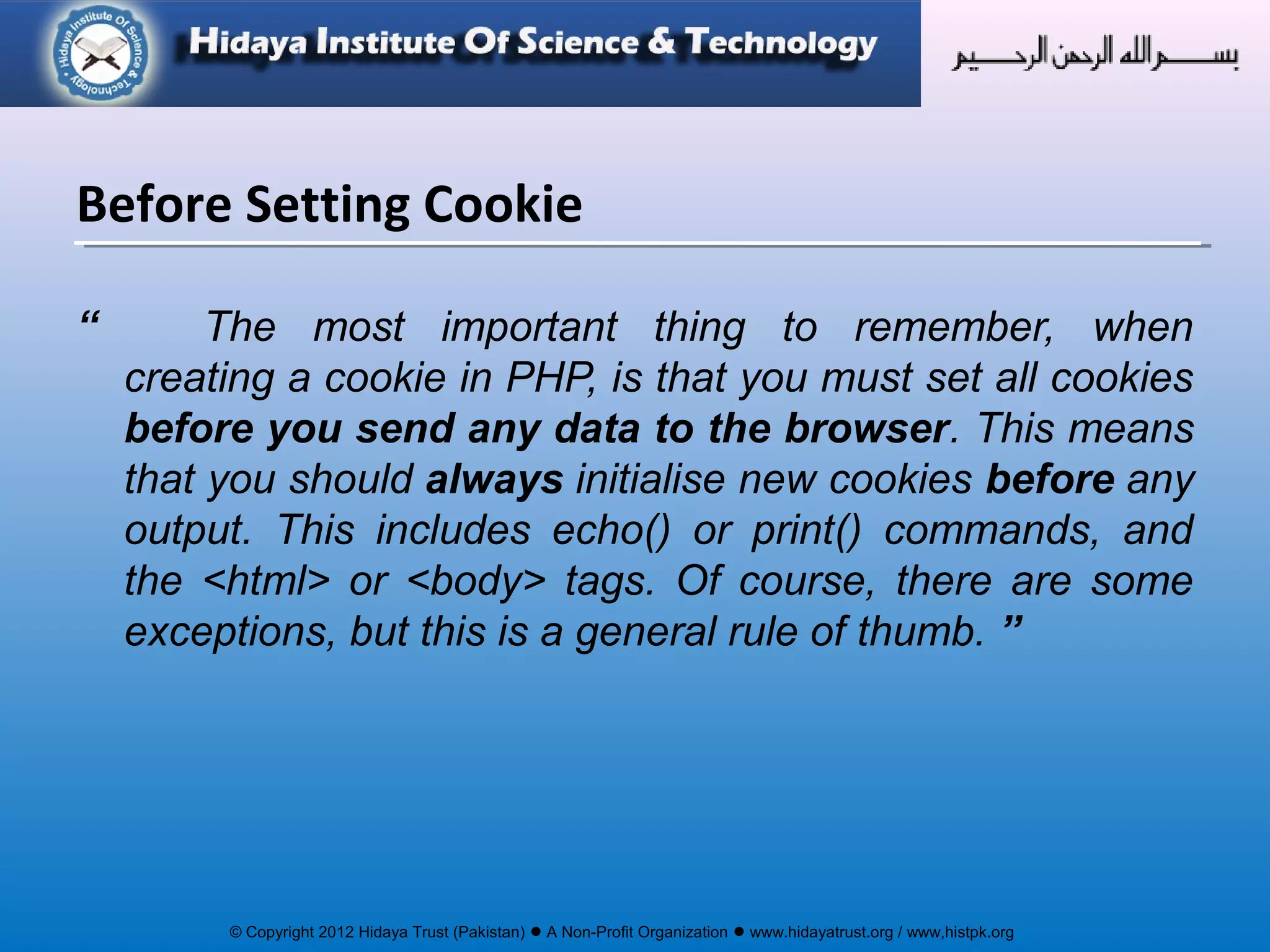
- The document discusses how cookies work, where they are stored, how to enable them, and different types of cookies like session and persistent cookies.
![© Copyright 2012 Hidaya Trust (Pakistan) ● A Non-Profit Organization ● www.hidayatrust.org / www,histpk.org
setcookie() function is use to create the cookie
bool setcookie ( string name [, string value])
• name: This argument sets the name of the cookie.
for example setcookie(‘mycookie’, …) will set mycookie and is called
$_COOKIE['mycookie'] at server side.
• value: This will set the value of the cookie. Since this values is
stored on the client browser extra care must be taken that it does
not store some secure information e.g non-encrypted passwords.
The value is accessed by $_COOKIE['mycookie'] at the web server.
• All the attributes are optional, only the first (name) is not optional.
Session Cookies (contd…)](https://image.slidesharecdn.com/cookieslec1-141221140953-conversion-gate01/75/Cookies-in-php-lecture-1-22-2048.jpg)
![© Copyright 2012 Hidaya Trust (Pakistan) ● A Non-Profit Organization ● www.hidayatrust.org / www,histpk.org
<?php
setcookie(‘username‘,’admin’);
?>
<?php
echo $_COOKIE[‘username’];
?>
Setting and Retrieving Cookies](https://image.slidesharecdn.com/cookieslec1-141221140953-conversion-gate01/75/Cookies-in-php-lecture-1-23-2048.jpg)
![© Copyright 2012 Hidaya Trust (Pakistan) ● A Non-Profit Organization ● www.hidayatrust.org / www,histpk.org
• Once a cookie has been set for a domain, it becomes available in the special
$_COOKIE associative array, and its value may be accessed using standard array
notation.
<?php
// if cookie present, use it
// else display generic message
if ($_COOKIE['username'])
{
echo "Welcome back, " . $_COOKIE['username'];
}
else
{
echo “You are not signed in";
}
?>
• To check whether your cookies are working correctly, use the statement <?php
print_r($_COOKIE); ?> to look inside PHP’s special $_COOKIE array.
Retrieving Cookie Data](https://image.slidesharecdn.com/cookieslec1-141221140953-conversion-gate01/75/Cookies-in-php-lecture-1-24-2048.jpg)