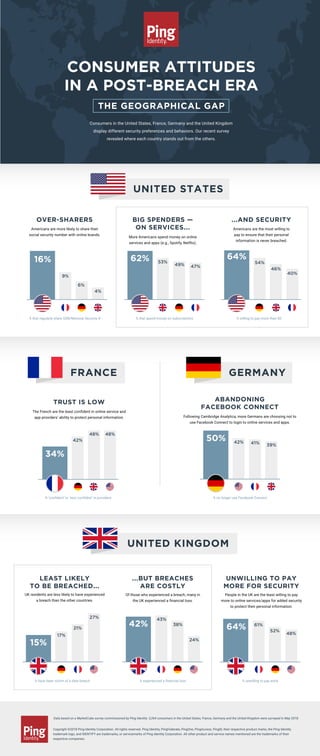
Consumer Attitudes in a Post-breach Era: The Geographical Gap
•
1 like•920 views
Ping Identity’s consumer survey on security perceptions and behavior revealed significant differences between residents of the U.S., France, Germany and the UK. Some are more carefree with their information, while others have less trust in brands.
Report
Share
Report
Share
Recommended
2018 Survey: Consumer Attitudes in a Post-Breach Era - The Generational Gap

Consumers under 35 and over 55 have significant differences in the way they think about security, willingness to share personal information, investment in data protection and use of technology like biometrics. Check out the infographic to see where Ping Identity’s survey revealed the biggest differences.
Security Concerns Around the World | Infographic

Ping Identity’s 2019 consumer survey reveals interesting insights about where residents of the U.S., Australia, France and Germany differ from one another in their cybersecurity concerns and behavioral trends. Check out the infographic to see which country’s respondents are most concerned about surveillance, which are least likely to sign-on to their accounts through a third-party service and more.
Security Practices: The Generational Gap | Infographic

Ping Identity’s 2019 survey reveals that consumers of different ages have different responses to the rampant data misuse and data breaches that have become increasingly regular in today’s world. Check out the infographic to see how the generations differ in their security practices and trusting tendencies.
Unisys Security Insights Infographic: Netherlands

Read full report: http://www.unisys.com/ms/unisys-security-insights/netherlands
Mobile E-commerce: Friend or Foe

This infographic highlights key stats and messages from the analyst report from J.Gold Associates that addresses the growing economic impact of mobile cybercrime and fraud.
Fraudsters Hackers & Thieves!

How can we better protect our customers?
It’s official: consumers do not feel their private data is being kept private. Looking around at the headlines, where high profile breach after high-profile breach is documented, the lack of trust in data security is no surprise.
In this graphical report, we delve into the fears surrounding online security and the economic impact of losing your customers’ trust.
5 Quest Fake News Survey Results June 2020

The results of the Fake News survey are in! Please follow us on the ZIGRAM Linkedin channel to stay up to date with more surveys and results. https://bit.ly/2XTgQEM
Its 2018... Should Pharma Still be Scared of Digital?

One of Pharma's biggest fears when it comes to adopting digital and new technology, is fear of regulations and compliance. To see how much of an issue this really is, breaches of the ABPI code of practice were analyzed over 2017 & 2016, across all channels. The results are interesting...
Recommended
2018 Survey: Consumer Attitudes in a Post-Breach Era - The Generational Gap

Consumers under 35 and over 55 have significant differences in the way they think about security, willingness to share personal information, investment in data protection and use of technology like biometrics. Check out the infographic to see where Ping Identity’s survey revealed the biggest differences.
Security Concerns Around the World | Infographic

Ping Identity’s 2019 consumer survey reveals interesting insights about where residents of the U.S., Australia, France and Germany differ from one another in their cybersecurity concerns and behavioral trends. Check out the infographic to see which country’s respondents are most concerned about surveillance, which are least likely to sign-on to their accounts through a third-party service and more.
Security Practices: The Generational Gap | Infographic

Ping Identity’s 2019 survey reveals that consumers of different ages have different responses to the rampant data misuse and data breaches that have become increasingly regular in today’s world. Check out the infographic to see how the generations differ in their security practices and trusting tendencies.
Unisys Security Insights Infographic: Netherlands

Read full report: http://www.unisys.com/ms/unisys-security-insights/netherlands
Mobile E-commerce: Friend or Foe

This infographic highlights key stats and messages from the analyst report from J.Gold Associates that addresses the growing economic impact of mobile cybercrime and fraud.
Fraudsters Hackers & Thieves!

How can we better protect our customers?
It’s official: consumers do not feel their private data is being kept private. Looking around at the headlines, where high profile breach after high-profile breach is documented, the lack of trust in data security is no surprise.
In this graphical report, we delve into the fears surrounding online security and the economic impact of losing your customers’ trust.
5 Quest Fake News Survey Results June 2020

The results of the Fake News survey are in! Please follow us on the ZIGRAM Linkedin channel to stay up to date with more surveys and results. https://bit.ly/2XTgQEM
Its 2018... Should Pharma Still be Scared of Digital?

One of Pharma's biggest fears when it comes to adopting digital and new technology, is fear of regulations and compliance. To see how much of an issue this really is, breaches of the ABPI code of practice were analyzed over 2017 & 2016, across all channels. The results are interesting...
2015 TRUSTe US Consumer Privacy Confidence Index – Infographic

Infographic on the consumer concerns on data privacy, business impact of neglecting consumer privacy and 6 ways to improve consumer trust in the US from TRUSTe.
Download the infographic http://www.truste.com/us-consumer-confidence-index-2015/
Its 2019 - Should Pharma Still Be Scared of Digital?

Updated deck with 2018 ABPI data on UK breaches to the code of practice by Pharma and how much of role did digital play?
One of Pharma's biggest fears when it comes to adopting digital and new technology, is fear of regulations and compliance. To see how much of an issue this really is, breaches of the ABPI code of practice were analyzed over 2017 & 2016, across all channels. The results are interesting...
Is Your Dating App Breaking Your Heart?

50% of companies have employees who use dating apps on work devices. This is great news for hackers, who have the means to try to access sensitive data, including users' billing information and GPS location, via the mobile channel.
TeleSign’s Findings on the Future of Digital Identity, Guillaume Bourcy

TeleSign’s Findings on the Future of Digital Identity
Guillaume Bourcy, Data Growth and Strategy at TeleSign
COVID-19, A sign of What’s to Come: Accelerated Digital Transformation brings vulnerabilities, even with basic mitigation practice.
How Fraud is Endemic: Shifting from offline to online increases the need to establish trusted digital identities in real-time.
Today weaknesses, myth and reality of current solutions: Evolving government regulations have a serious impact on global industries.
Mitigating friction, while adhering to regulation and enhanced security processes, can be challenging.
Rising need for Ubiquity: A single, reliable partner to enable engagement and provide security insights.
Privacy and Tracking Protection in Firefox

Surveillance is a growing concern in Europe, and Mozilla believes that privacy and security should be treated as fundamental and not optional in the browsing experience. That's why Firefox has introduced new features for tracking protection and private browsing. Do not track is not only a way to navigate the web, it might also become part of a new privacy law in the EU. We will discuss how this has been implemented in the newest version of Firefox, next steps, and why it's important to have transparency and control in our online experiences.
https://fosdem.org/2016/schedule/event/mozilla_privacy_tracking_protection_firefox/
INFOGRAPHIC: The Evolution of Data Privacy

The EU’s new General Data Protection Regulation
has left many businesses wondering if they are
ready to comply.
INFOGRAPHIC: Here are the reasons why
Seven Stats on Social Media Security (Nov 2013)

Seven stats on social media security, taken from Nexgate's corpus of over 100 million pieces of scanned social media content.
For more information, visit out stat center: http://nx.gt/statcenter
Cyber security awareness & training 2.1

This is a short presentation Skibo has been delivering to companies over the past 12 months, based on real-world experience in dealing with cyber security incidents,
Norton Mobile Apps Survey Report

Symantec surveyed consumers around the globe to gauge perceptions toward mobile privacy against the realities of today’s connected world.
11 Reasons Why Your Company Could Be In Danger

In today’s interconnected world, few things terrify CEOs and CTOs more than electronic security (well, a breach of that security, anyway). Most of our records, personal information, corporate information, and sensitive data exist online or on Internet-connected hardware. Mobile, with all it’s advantages for enterprises, actually poses one of the largest emerging threats to those enterprises’ data security. As such, we wanted to share some statistics that demonstrate the severity of the problem and highlight the importance of mobile security for your business.
2016 Cyber Security Breaches Survey for the UK

PIB Insurance Brokers is proud to present our report summarising the 2016 Cyber Security Breaches Survey for the United Kingdom, commissioned by the Department for Culture, Media & Sport as part of the National Cyber Security Programme.
Better Security Through Big Data Analytics

Think Big Data Analytics can't help you with your security? Do these stats make you nervous?
Attackers Moving Faster, defenses are not; 5 out of 6 large companies attacked; a 40% increase over 2013
More than 317 million new pieces of malware created last year; 1 million new threats created daily
60% of all targeted attacks struck small- and medium-sized organizations
Retail Remains Hot Spot for Identities: 1 billion stolen in the last 2 years; 59% of all identities exposed in 2014 came from the retail sector
Top 5 zero-days left companies without a patch for 295 days
Digital extortion on the rise: 113% increase in ransomeware; 45 times more people had their devices held hostage by vicious crypto-ransomeware
Malware gets smarter -- 28% of all malware was “virtual machine aware “
2014 had an all-time high of 24 discovered zero-day vulnerabilities
The State of Privacy Report

Check the original report at the https://figleaf.com/blog/privacy-guides/the-state-of-privacy/
MEF Global Consumer Trust Report

MEF Global Consumer Trust Report.
The study explores the key areas of trust, privacy, transparency and security to identify their impact on mobile consumers globally from purchasing a new device to downloading apps or paying for goods and services.
Infographic: Philippines B2C E-Commerce Market 2019

Free infographic from our report "Philippines B2C E-Commerce Market 2019".
Find it here: https://www.ystats.com/infographic-philippines-b2c-e-commerce-market-2019/
Find the report available for purchase here: https://www.ystats.com/market-reports/philippines-b2c-e-commerce-market-2019/
Fraudsters Hackers & Thieves

It’s official: your customers do not feel their private data is being kept private. In this graphical report, we delve into the fears surrounding online security and the economic impact of losing your customers’ trust.
More Related Content
What's hot
2015 TRUSTe US Consumer Privacy Confidence Index – Infographic

Infographic on the consumer concerns on data privacy, business impact of neglecting consumer privacy and 6 ways to improve consumer trust in the US from TRUSTe.
Download the infographic http://www.truste.com/us-consumer-confidence-index-2015/
Its 2019 - Should Pharma Still Be Scared of Digital?

Updated deck with 2018 ABPI data on UK breaches to the code of practice by Pharma and how much of role did digital play?
One of Pharma's biggest fears when it comes to adopting digital and new technology, is fear of regulations and compliance. To see how much of an issue this really is, breaches of the ABPI code of practice were analyzed over 2017 & 2016, across all channels. The results are interesting...
Is Your Dating App Breaking Your Heart?

50% of companies have employees who use dating apps on work devices. This is great news for hackers, who have the means to try to access sensitive data, including users' billing information and GPS location, via the mobile channel.
TeleSign’s Findings on the Future of Digital Identity, Guillaume Bourcy

TeleSign’s Findings on the Future of Digital Identity
Guillaume Bourcy, Data Growth and Strategy at TeleSign
COVID-19, A sign of What’s to Come: Accelerated Digital Transformation brings vulnerabilities, even with basic mitigation practice.
How Fraud is Endemic: Shifting from offline to online increases the need to establish trusted digital identities in real-time.
Today weaknesses, myth and reality of current solutions: Evolving government regulations have a serious impact on global industries.
Mitigating friction, while adhering to regulation and enhanced security processes, can be challenging.
Rising need for Ubiquity: A single, reliable partner to enable engagement and provide security insights.
Privacy and Tracking Protection in Firefox

Surveillance is a growing concern in Europe, and Mozilla believes that privacy and security should be treated as fundamental and not optional in the browsing experience. That's why Firefox has introduced new features for tracking protection and private browsing. Do not track is not only a way to navigate the web, it might also become part of a new privacy law in the EU. We will discuss how this has been implemented in the newest version of Firefox, next steps, and why it's important to have transparency and control in our online experiences.
https://fosdem.org/2016/schedule/event/mozilla_privacy_tracking_protection_firefox/
INFOGRAPHIC: The Evolution of Data Privacy

The EU’s new General Data Protection Regulation
has left many businesses wondering if they are
ready to comply.
INFOGRAPHIC: Here are the reasons why
Seven Stats on Social Media Security (Nov 2013)

Seven stats on social media security, taken from Nexgate's corpus of over 100 million pieces of scanned social media content.
For more information, visit out stat center: http://nx.gt/statcenter
Cyber security awareness & training 2.1

This is a short presentation Skibo has been delivering to companies over the past 12 months, based on real-world experience in dealing with cyber security incidents,
Norton Mobile Apps Survey Report

Symantec surveyed consumers around the globe to gauge perceptions toward mobile privacy against the realities of today’s connected world.
11 Reasons Why Your Company Could Be In Danger

In today’s interconnected world, few things terrify CEOs and CTOs more than electronic security (well, a breach of that security, anyway). Most of our records, personal information, corporate information, and sensitive data exist online or on Internet-connected hardware. Mobile, with all it’s advantages for enterprises, actually poses one of the largest emerging threats to those enterprises’ data security. As such, we wanted to share some statistics that demonstrate the severity of the problem and highlight the importance of mobile security for your business.
2016 Cyber Security Breaches Survey for the UK

PIB Insurance Brokers is proud to present our report summarising the 2016 Cyber Security Breaches Survey for the United Kingdom, commissioned by the Department for Culture, Media & Sport as part of the National Cyber Security Programme.
Better Security Through Big Data Analytics

Think Big Data Analytics can't help you with your security? Do these stats make you nervous?
Attackers Moving Faster, defenses are not; 5 out of 6 large companies attacked; a 40% increase over 2013
More than 317 million new pieces of malware created last year; 1 million new threats created daily
60% of all targeted attacks struck small- and medium-sized organizations
Retail Remains Hot Spot for Identities: 1 billion stolen in the last 2 years; 59% of all identities exposed in 2014 came from the retail sector
Top 5 zero-days left companies without a patch for 295 days
Digital extortion on the rise: 113% increase in ransomeware; 45 times more people had their devices held hostage by vicious crypto-ransomeware
Malware gets smarter -- 28% of all malware was “virtual machine aware “
2014 had an all-time high of 24 discovered zero-day vulnerabilities
The State of Privacy Report

Check the original report at the https://figleaf.com/blog/privacy-guides/the-state-of-privacy/
MEF Global Consumer Trust Report

MEF Global Consumer Trust Report.
The study explores the key areas of trust, privacy, transparency and security to identify their impact on mobile consumers globally from purchasing a new device to downloading apps or paying for goods and services.
Infographic: Philippines B2C E-Commerce Market 2019

Free infographic from our report "Philippines B2C E-Commerce Market 2019".
Find it here: https://www.ystats.com/infographic-philippines-b2c-e-commerce-market-2019/
Find the report available for purchase here: https://www.ystats.com/market-reports/philippines-b2c-e-commerce-market-2019/
What's hot (20)
2015 TRUSTe US Consumer Privacy Confidence Index – Infographic

2015 TRUSTe US Consumer Privacy Confidence Index – Infographic
Its 2019 - Should Pharma Still Be Scared of Digital?

Its 2019 - Should Pharma Still Be Scared of Digital?
TeleSign’s Findings on the Future of Digital Identity, Guillaume Bourcy

TeleSign’s Findings on the Future of Digital Identity, Guillaume Bourcy
TRUSTe 2014 US Consumer Confidence Privacy Report Consumer Opinion and Busine...

TRUSTe 2014 US Consumer Confidence Privacy Report Consumer Opinion and Busine...
Infographic: Philippines B2C E-Commerce Market 2019

Infographic: Philippines B2C E-Commerce Market 2019
Aligning Today's IT with the Future of Government - Peter Pin

Aligning Today's IT with the Future of Government - Peter Pin
Similar to Consumer Attitudes in a Post-breach Era: The Geographical Gap
Fraudsters Hackers & Thieves

It’s official: your customers do not feel their private data is being kept private. In this graphical report, we delve into the fears surrounding online security and the economic impact of losing your customers’ trust.
Moving beyond passwords - Consumer attitudes on online authentication

Mise en évidence des difficultés relatives à la mise en place de mesures d’identification et d’authentification au sein des entreprises.
The Privacy Advantage 2016 - Amit Pau

Ariadne Capital discusses the financial opportunity presented by a shift in personal data capital ownership
Norton Cyber Security Insights Report 2017

Let’s understand about the “2017 Norton Cyber Security Insights Report”, the main topics of this reports are Cybercrime by the Numbers, Portrait of a Cybercrime Victim, Consumers’ Contradicting Beliefs, and State of Consumers’ Trust.
Uk Cyber Security Survey 2019

The National Cyber Security Centre and Department for Digital, Culture, Media and Sport have released findings from the UK Cyber Survey conducted by Ipsos MORI. These findings are from a study of UK individuals to measure and understand awareness and attitudes towards cyber security, and related behaviours. They are part of a wider research project to provide insight to inform HM Government’s approach to encourage positive behaviour amongst the public in protecting themselves against cyber threats.
Delivering Imperatives of Modern Organizations Such As Cybersecurity and Open...

Delivering Imperatives of Modern Organizations Such As Cybersecurity and Open Data - Eric Swedersky (Slides)
Consumer Mobile Policy & Security - Lightspeed & Kantar

at Market Research in the Mobile World Europe
23 - 26 September 2014, Belin, Germany
This event is proudly organised by Merlien Institute
Check out our upcoming events by visiting http://www.mrmw.net
White Paper: The 2015 State of Consumer Privacy & Personalization

The 2015 State of Privacy & Personalization
White Paper: The 2015 State of Consumer Privacy & Personalization

This year’s survey results illustrate increased growth and intensity in consumer desire for data privacy and personalized user experiences. While social login usage continues to skyrocket, consumers are also showing a marked interest in next-generation authentication methods, including payment providers and biometrics, indicating a clear evolution of the concept of digital identity: Identity 3.0.
Europe and the Internet: It’s complicated

European public and policy elite views of US tech companies
This presentation explores consumer attitudes to US tech companies in France, Germany, the UK and Brussels, how that interacts with media coverage, and what is driving the European regulatory agenda towards the internet and technology companies.
For more information please contact:
Chris Blundell: http://www.brunswickgroup.com/people/directory/chris-blundell/
Philippe Blanchard: http://www.brunswickgroup.com/people/directory/philippe-blanchard/
Chinese Social Credit Score: Utopian Big Data Bliss Or Black Mirror On Steroids?

By 2020, the Chinese social credit score system will be fully operational and have searchable records and a social credit score to rate trustworthiness for each of its 1.4 billion citizens. We review what the Chinese social credit score system is, how it's generated, and the implications.
Data Privacy Compliance (Series: Corporate & Regulatory Compliance Bootcamp)

All levels of society rely upon information technology systems. Network operations are pervasive and impact nearly every aspect of our society. The desire of companies to collect, use, store, and secure information about customers, employees, and other individuals is a requirement of the new economy. It is no wonder that the prevalence of electronic communications and a growing dependency on cyber structures and operations also create potential vulnerabilities to cyberattacks. It is critical to preserve information systems and address and prevent weaknesses in cyber protection efforts. This webinar examines the means for companies to reach data goals ethically, efficiently and legally. Best practices and model comprehensive privacy and cybersecurity policies are discussed. And, data breach response and related litigation, including class action litigation issues and fiduciary duty violations under corporate law, are discussed.
To view the accompanying webinar, go to: https://www.financialpoise.com/financial-poise-webinars/data-privacy-compliance-2019/
Adobe Digital Insights -- Diversity In Advertising 2019 (AUS)

As part of Adobe's look into the 25th anniversary of digital advertising, and to get to the root of whether or not diversity in advertising has changed in the eyes of the people who consume it, Adobe conducted a global survey of over 1,000 consumers. We looked across generation, gender, ethnicity and sexual orientation in Australia to reveal some interesting takeaways and understand how diversity in creative and the way diverse ads are delivered and targeted translate into brand advocacy and consumer engagement.
Similar to Consumer Attitudes in a Post-breach Era: The Geographical Gap (20)
Moving beyond passwords - Consumer attitudes on online authentication

Moving beyond passwords - Consumer attitudes on online authentication
TeleSign Consumer Account Security Report 2015 FINAL

TeleSign Consumer Account Security Report 2015 FINAL
Delivering Imperatives of Modern Organizations Such As Cybersecurity and Open...

Delivering Imperatives of Modern Organizations Such As Cybersecurity and Open...
Consumer Mobile Policy & Security - Lightspeed & Kantar

Consumer Mobile Policy & Security - Lightspeed & Kantar
White Paper: The 2015 State of Consumer Privacy & Personalization

White Paper: The 2015 State of Consumer Privacy & Personalization
White Paper: The 2015 State of Consumer Privacy & Personalization

White Paper: The 2015 State of Consumer Privacy & Personalization
Chinese Social Credit Score: Utopian Big Data Bliss Or Black Mirror On Steroids?

Chinese Social Credit Score: Utopian Big Data Bliss Or Black Mirror On Steroids?
Data Privacy Compliance (Series: Corporate & Regulatory Compliance Bootcamp)

Data Privacy Compliance (Series: Corporate & Regulatory Compliance Bootcamp)
Adobe Digital Insights -- Diversity In Advertising 2019 (AUS)

Adobe Digital Insights -- Diversity In Advertising 2019 (AUS)
More from Ping Identity
Healthcare Patient Experiences Matter

Join your patient's journey and see critical touch points that impact revenue. These stats prove superb patient experiences move business forward.
Optimize Your Zero Trust Infrastructure

See how you can create seamless and secure experiences for your employees and customers by optimizing and adding intelligence to your Zero Trust infrastructure.
Ping’s Technology Partner Program

Scale your business by partnering with the leading intelligent cloud identity platform and expose your solution to thousands of Ping customers.
Remote Work Fuels Zero Trust Growth

See what Ping’s Executive Survey reveals about the security impacts of the shift to remote work.
Identity Verification: Who’s Really There? 

Customers are knocking on your digital front door, but who’s really there? Get the facts on why identity verification is now more important than ever.
Extraordinary Financial Customer Experiences

Join your financial customer’s journey and see critical touchpoints that impact revenue. These stats prove superb customer experiences move business forward.
Extraordinary Retail Customer Experiences

Join your retail customer’s journey and see critical touchpoints that impact revenue. These stats prove superb customer experiences move business forward.
Hybrid IAM: Fuelling Agility in the Cloud Transformation Journey | Gartner IA...

Presenter: Loren Russon, VP Product Management at Ping Identity.
As your organisation evolves on its cloud transformation journey, your identity and access management (IAM) system must allow you to navigate multiple cloud environments, managing access to mobile, API and traditional applications. Modern identity services like multi-factor authentication (MFA) and identity intelligence help deliver secure and seamless access for any user, environment and use case. Learn how to transform your IAM system to a modern, API and cloud-first hybrid solution, enabling developers, administrators and users with the self-service applications and tools they need to keep pace with the accelerating demand for mobile and cloud-based applications.
LES ATTITUDES DES CONSOMMATEURS À L’ÈRE DES CYBERATTAQUES

Les consommateurs présents aux Etats-Unis, en France, en Allemagne et au Royaume-Uni montrent des préférences de sécurité et des comportements différents. Notre étude récente révèle comment chaque pays se démarque des autres.
WIE TICKEN VERBRAUCHER IM ZEITALTER DER DATENSCHUTZVERLETZUNGEN?

Wenn es um Themen wie Sicherheitsempfinden und Sicherheitspraktiken geht, haben die jüngere und die ältere Generation schon mal recht unterschiedliche Ansichten. So stellte eine aktuelle Verbraucherumfrage Abweichungen z. B. beim Markenvertrauen, bei der Bereitschaft, in Datenschutz zu investieren und bei der Akzeptanz biometrischer Sicherheitslösungen fest.
Standard Based API Security, Access Control and AI Based Attack - API Days Pa...

As APIs continue to drive digital transformation efforts in the enterprise and support innovative customer experiences, securing them has never been more important.
Principal Regional Solution Architect, Philippe Dubuc introduces how to leverage OpenID Connect, OAuth2 and new emerging standards to protect APIs at API Days Paris on 11 December, 2018. In addition, Philippe goes over how the Intelligent Ping Identity Platform can be used to protect APIs in a pro-active way and how AI can help to protect against attacks.
Learn more: http://ow.ly/2Ojm30n1rCT
ATTITUDES DES CONSOMMATEURS A L’ERE DES PIRATAGES LE CONFLIT DE GENERATIONS

Concernant les attitudes et les pratiques en matière de sécurité, la jeune et l’ancienne génération ne sont pas toujours en phase. Une récente enquête révèle des différences marquées touchant la confiance envers les marques, la volonté de payer pour la protection des données, l’adoption de la biométrie, etc.
WIE TICKEN VERBRAUCHER IM ZEITALTER DER DATENSCHUTZVERLETZUNGEN? ALLES EINE F...

Wenn es um Themen wie Sicherheitsempfinden und Sicherheitspraktiken geht, haben die jüngere und die ältere Generation schon mal recht unterschiedliche Ansichten. So stellte eine aktuelle Verbraucherumfrage Abweichungen z. B. beim Markenvertrauen, bei der Bereitschaft, in Datenschutz zu investieren und bei der Akzeptanz biometrischer Sicherheitslösungen fest.
API Security Needs AI Now More Than Ever

API security is increasingly difficult for enterprise security teams to tackle. APIs are spreading fast and a tempting target for cyberattacks. Learn about the challenges overwhelming security teams today that can be overcome with an intelligent API security solution. Learn more: http://ow.ly/FEtG30lNsHm
Fishing for a CIAM Platform? 11 Question to Ask Before You Buy

On the hook to select a customer IAM platform? Be sure to ask these 11 questions before you settle on a solution. Or you could get in too deep. Read the infographic to discover why enlisting IT’s help early in the selection process will ensure your CIAM platform is watertight.
Criteria for Effective Modern IAM Strategies (Gartner IAM 2018)

Presenter: Loren Russon, Ping Identity VP of Products Management and Design.
Managing digital identities and access control for users, applications and things remains one of the greatest challenges facing cloud computing today. This has led to a new cloud security service paradigm that requires your organization to reevaluate the criteria for designing and implementing identity and access management (IAM) services across data centers, and private and public cloud infrastructure. This new criteria addresses the continued transformation to the cloud, mobile and internet of things (IoT), and the increased demand for open business balanced by user data security found in initiatives such as GDPR, Open Banking and PSD2. In this session, you will learn about key requirements and design principles required for modern IAM systems, and how to effectively drive digital transformation, address user data security regulations and ensure you successfully manage your company’s transformation to the cloud.
Webinar: Three Steps to Transform Your Mobile App into a Security Factor

It’s your job to secure customer interactions with your brand. Enabling multi-factor authentication (MFA) for your customers can secure their data, even if their credentials get compromised elsewhere. You may be asking yourself, “doesn’t MFA add friction and detract from their customer experience?”
Join Pamela Dingle, Principal Technical Architect for Ping Identity, as she outlines three easy steps to transform your own mobile application into a second factor that is both secure and convenient. You will learn how to achieve transaction approvals, strong device-based mobile app authentication, and many other use cases from your own mobile app, with minimal impact on your existing authentication infrastructure.
Stay tuned for the webinar replay. To learn more, download the 'Multi-factor Authentication for Customers' white paper: http://www.bit.ly/2tusUA0
Webinar: Deep Diving Into the KuppingerCole IDaaS Leadership Compass 

While enterprises move to the cloud, they are pressured to keep security in mind without hindering user productivity with a cumbersome sign-on process. One solution that delivers both a secure and seamless experience for users with one-click access to SaaS applications is single sign-on (SSO). Many enterprises cannot simply rip and replace, so finding a solution provider that creates a hybrid environment between cloud and existing on-premise infrastructures is vital.
The 2017 KuppingerCole Leadership Compass is the industry leading recourse that deep dives into this market, rating identity-as-a-service (IDaaS) solution providers in areas like SSO cloud services for users including employees, business partners and customers.
Get the report: http://www.ow.ly/Rhht30eLbbD
Join Ping Identity’s Product Marketing Manager, Alex Babar, as he looks at the KuppingerCole Leadership Compass for IDaaS and at the capabilities they consider. He will also review Ping Identity product features focusing on core factors that led KuppingerCole to name Ping a leader in their Leadership Compass, such as outbound federation and single sign-on, authentication support, and access management.
Get the replay: http://bit.ly/2eK0I66
GDPR & Customer IAM: The Real Winners Won’t Stop At Compliance

Listen to the on-demand recorded webinar here: http://bit.ly/2synQpD.
In the recording you will learn how customer identity and access management (Customer IAM) solutions can help you meet GDPR requirements out of the box, while also providing a single, unified customer profile, and enabling secure, seamless and personalized customer experiences across all channels and applications.
Note, this is a recorded webinar which took place on 27 June, 2017. For more information on GDPR and how Ping's leading Customer IAM solution can turn a compliance challenge into an opportunity for your organization, visit www.pingidentity.com/GDPR.
Gartner IAM London 2017 Session - Security, Standards & User Experience: The ...

Ping Identity Principal Technical Architect, Pam Dingle’s slides on how organisations can meet PSD2 and Open Banking Standard requirements while delivering excellent customer experiences in today’s challenging digital business environments. Using software that’s based on the OAuth family of standards, organisations are protecting RESTful APIs, combining a critical blend of intuitive user interactions, highly scalable certification of clients and interoperability.
A Modern Identity Architecture for the Digital Enterprise: http://bit.ly/2lPNiCM
More from Ping Identity (20)
Hybrid IAM: Fuelling Agility in the Cloud Transformation Journey | Gartner IA...

Hybrid IAM: Fuelling Agility in the Cloud Transformation Journey | Gartner IA...
LES ATTITUDES DES CONSOMMATEURS À L’ÈRE DES CYBERATTAQUES

LES ATTITUDES DES CONSOMMATEURS À L’ÈRE DES CYBERATTAQUES
WIE TICKEN VERBRAUCHER IM ZEITALTER DER DATENSCHUTZVERLETZUNGEN?

WIE TICKEN VERBRAUCHER IM ZEITALTER DER DATENSCHUTZVERLETZUNGEN?
Standard Based API Security, Access Control and AI Based Attack - API Days Pa...

Standard Based API Security, Access Control and AI Based Attack - API Days Pa...
ATTITUDES DES CONSOMMATEURS A L’ERE DES PIRATAGES LE CONFLIT DE GENERATIONS

ATTITUDES DES CONSOMMATEURS A L’ERE DES PIRATAGES LE CONFLIT DE GENERATIONS
WIE TICKEN VERBRAUCHER IM ZEITALTER DER DATENSCHUTZVERLETZUNGEN? ALLES EINE F...

WIE TICKEN VERBRAUCHER IM ZEITALTER DER DATENSCHUTZVERLETZUNGEN? ALLES EINE F...
Fishing for a CIAM Platform? 11 Question to Ask Before You Buy

Fishing for a CIAM Platform? 11 Question to Ask Before You Buy
Criteria for Effective Modern IAM Strategies (Gartner IAM 2018)

Criteria for Effective Modern IAM Strategies (Gartner IAM 2018)
Webinar: Three Steps to Transform Your Mobile App into a Security Factor

Webinar: Three Steps to Transform Your Mobile App into a Security Factor
Webinar: Deep Diving Into the KuppingerCole IDaaS Leadership Compass 

Webinar: Deep Diving Into the KuppingerCole IDaaS Leadership Compass
GDPR & Customer IAM: The Real Winners Won’t Stop At Compliance

GDPR & Customer IAM: The Real Winners Won’t Stop At Compliance
Gartner IAM London 2017 Session - Security, Standards & User Experience: The ...

Gartner IAM London 2017 Session - Security, Standards & User Experience: The ...
Recently uploaded
Elizabeth Buie - Older adults: Are we really designing for our future selves?

Elizabeth Buie - Older adults: Are we really designing for our future selves?
The Metaverse and AI: how can decision-makers harness the Metaverse for their...

The Metaverse is popularized in science fiction, and now it is becoming closer to being a part of our daily lives through the use of social media and shopping companies. How can businesses survive in a world where Artificial Intelligence is becoming the present as well as the future of technology, and how does the Metaverse fit into business strategy when futurist ideas are developing into reality at accelerated rates? How do we do this when our data isn't up to scratch? How can we move towards success with our data so we are set up for the Metaverse when it arrives?
How can you help your company evolve, adapt, and succeed using Artificial Intelligence and the Metaverse to stay ahead of the competition? What are the potential issues, complications, and benefits that these technologies could bring to us and our organizations? In this session, Jen Stirrup will explain how to start thinking about these technologies as an organisation.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
By Design, not by Accident - Agile Venture Bolzano 2024

As presented at the Agile Venture Bolzano, 4.06.2024
Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf

Monitoring and observability aren’t traditionally found in software curriculums and many of us cobble this knowledge together from whatever vendor or ecosystem we were first introduced to and whatever is a part of your current company’s observability stack.
While the dev and ops silo continues to crumble….many organizations still relegate monitoring & observability as the purview of ops, infra and SRE teams. This is a mistake - achieving a highly observable system requires collaboration up and down the stack.
I, a former op, would like to extend an invitation to all application developers to join the observability party will share these foundational concepts to build on:
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
zkStudyClub - Reef: Fast Succinct Non-Interactive Zero-Knowledge Regex Proofs

This paper presents Reef, a system for generating publicly verifiable succinct non-interactive zero-knowledge proofs that a committed document matches or does not match a regular expression. We describe applications such as proving the strength of passwords, the provenance of email despite redactions, the validity of oblivious DNS queries, and the existence of mutations in DNA. Reef supports the Perl Compatible Regular Expression syntax, including wildcards, alternation, ranges, capture groups, Kleene star, negations, and lookarounds. Reef introduces a new type of automata, Skipping Alternating Finite Automata (SAFA), that skips irrelevant parts of a document when producing proofs without undermining soundness, and instantiates SAFA with a lookup argument. Our experimental evaluation confirms that Reef can generate proofs for documents with 32M characters; the proofs are small and cheap to verify (under a second).
Paper: https://eprint.iacr.org/2023/1886
PHP Frameworks: I want to break free (IPC Berlin 2024)

In this presentation, we examine the challenges and limitations of relying too heavily on PHP frameworks in web development. We discuss the history of PHP and its frameworks to understand how this dependence has evolved. The focus will be on providing concrete tips and strategies to reduce reliance on these frameworks, based on real-world examples and practical considerations. The goal is to equip developers with the skills and knowledge to create more flexible and future-proof web applications. We'll explore the importance of maintaining autonomy in a rapidly changing tech landscape and how to make informed decisions in PHP development.
This talk is aimed at encouraging a more independent approach to using PHP frameworks, moving towards a more flexible and future-proof approach to PHP development.
Essentials of Automations: The Art of Triggers and Actions in FME

In this second installment of our Essentials of Automations webinar series, we’ll explore the landscape of triggers and actions, guiding you through the nuances of authoring and adapting workspaces for seamless automations. Gain an understanding of the full spectrum of triggers and actions available in FME, empowering you to enhance your workspaces for efficient automation.
We’ll kick things off by showcasing the most commonly used event-based triggers, introducing you to various automation workflows like manual triggers, schedules, directory watchers, and more. Plus, see how these elements play out in real scenarios.
Whether you’re tweaking your current setup or building from the ground up, this session will arm you with the tools and insights needed to transform your FME usage into a powerhouse of productivity. Join us to discover effective strategies that simplify complex processes, enhancing your productivity and transforming your data management practices with FME. Let’s turn complexity into clarity and make your workspaces work wonders!
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
UiPath Community Day Dubai: AI at Work..

Welcome to the first live UiPath Community Day Dubai! Join us for this unique occasion to meet our local and global UiPath Community and leaders. You will get a full view of the MEA region's automation landscape and the AI Powered automation technology capabilities of UiPath. Also, hosted by our local partners Marc Ellis, you will enjoy a half-day packed with industry insights and automation peers networking.
📕 Curious on our agenda? Wait no more!
10:00 Welcome note - UiPath Community in Dubai
Lovely Sinha, UiPath Community Chapter Leader, UiPath MVPx3, Hyper-automation Consultant, First Abu Dhabi Bank
10:20 A UiPath cross-region MEA overview
Ashraf El Zarka, VP and Managing Director MEA, UiPath
10:35: Customer Success Journey
Deepthi Deepak, Head of Intelligent Automation CoE, First Abu Dhabi Bank
11:15 The UiPath approach to GenAI with our three principles: improve accuracy, supercharge productivity, and automate more
Boris Krumrey, Global VP, Automation Innovation, UiPath
12:15 To discover how Marc Ellis leverages tech-driven solutions in recruitment and managed services.
Brendan Lingam, Director of Sales and Business Development, Marc Ellis
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
Quantum Computing: Current Landscape and the Future Role of APIs

The current state of quantum computing and the role of APIs to take it mainstream.
Recently uploaded (20)
Elizabeth Buie - Older adults: Are we really designing for our future selves?

Elizabeth Buie - Older adults: Are we really designing for our future selves?
The Metaverse and AI: how can decision-makers harness the Metaverse for their...

The Metaverse and AI: how can decision-makers harness the Metaverse for their...
Monitoring Java Application Security with JDK Tools and JFR Events

Monitoring Java Application Security with JDK Tools and JFR Events
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
By Design, not by Accident - Agile Venture Bolzano 2024

By Design, not by Accident - Agile Venture Bolzano 2024
Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf

Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
zkStudyClub - Reef: Fast Succinct Non-Interactive Zero-Knowledge Regex Proofs

zkStudyClub - Reef: Fast Succinct Non-Interactive Zero-Knowledge Regex Proofs
Assure Contact Center Experiences for Your Customers With ThousandEyes

Assure Contact Center Experiences for Your Customers With ThousandEyes
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
PHP Frameworks: I want to break free (IPC Berlin 2024)

PHP Frameworks: I want to break free (IPC Berlin 2024)
Essentials of Automations: The Art of Triggers and Actions in FME

Essentials of Automations: The Art of Triggers and Actions in FME
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
Free Complete Python - A step towards Data Science

Free Complete Python - A step towards Data Science
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
Quantum Computing: Current Landscape and the Future Role of APIs

Quantum Computing: Current Landscape and the Future Role of APIs
Consumer Attitudes in a Post-breach Era: The Geographical Gap
- 1. CONSUMER ATTITUDES IN A POST-BREACH ERA THE GEOGRAPHICAL GAP OVER-SHARERS Americans are more likely to share their social security number with online brands. % that regularly share SSN/National Security # % ‘confident’ or ‘very confident’ in providers % have been victim of a data breach % experienced a financial loss % unwilling to pay extra % no longer use Facebook Connect % that spend money on subscriptions % willing to pay more than $0 Consumers in the United States, France, Germany and the United Kingdom display different security preferences and behaviors. Our recent survey revealed where each country stands out from the others. Data based on a MarketCube survey commissioned by Ping Identity. 3,264 consumers in the United States, France, Germany and the United Kingdom were surveyed in May 2018. Copyright ©2018 Ping Identity Corporation. All rights reserved. Ping Identity, PingFederate, PingOne, PingAccess, PingID, their respective product marks, the Ping Identity trademark logo, and IDENTIFY are trademarks, or servicemarks of Ping Identity Corporation. All other product and service names mentioned are the trademarks of their respective companies. 16% 34% 9% 6% 4% 62% BIG SPENDERS — ON SERVICES... More Americans spend money on online services and apps (e.g., Spotify, Netflix). ...AND SECURITY Americans are the most willing to pay to ensure that their personal information is never breached. LEAST LIKELY TO BE BREACHED... UK residents are less likely to have experienced a breach than the other countries. ...BUT BREACHES ARE COSTLY Of those who experienced a breach, many in the UK experienced a financial loss. UNWILLING TO PAY MORE FOR SECURITY People in the UK are the least willing to pay more to online services/apps for added security to protect their personal information. TRUST IS LOW The French are the least confident in online service and app providers’ ability to protect personal information. ABANDONING FACEBOOK CONNECT Following Cambridge Analytica, more Germans are choosing not to use Facebook Connect to login to online services and apps. 64% 54% 46% 40% 53% 49% 47% 42% 48% 48% 42% 41% 39% 50% 15% 27% 21% 17% 42% 24% 38% 43% 64% 61% 52% 48% UNITED KINGDOM FRANCE UNITED STATES GERMANY
