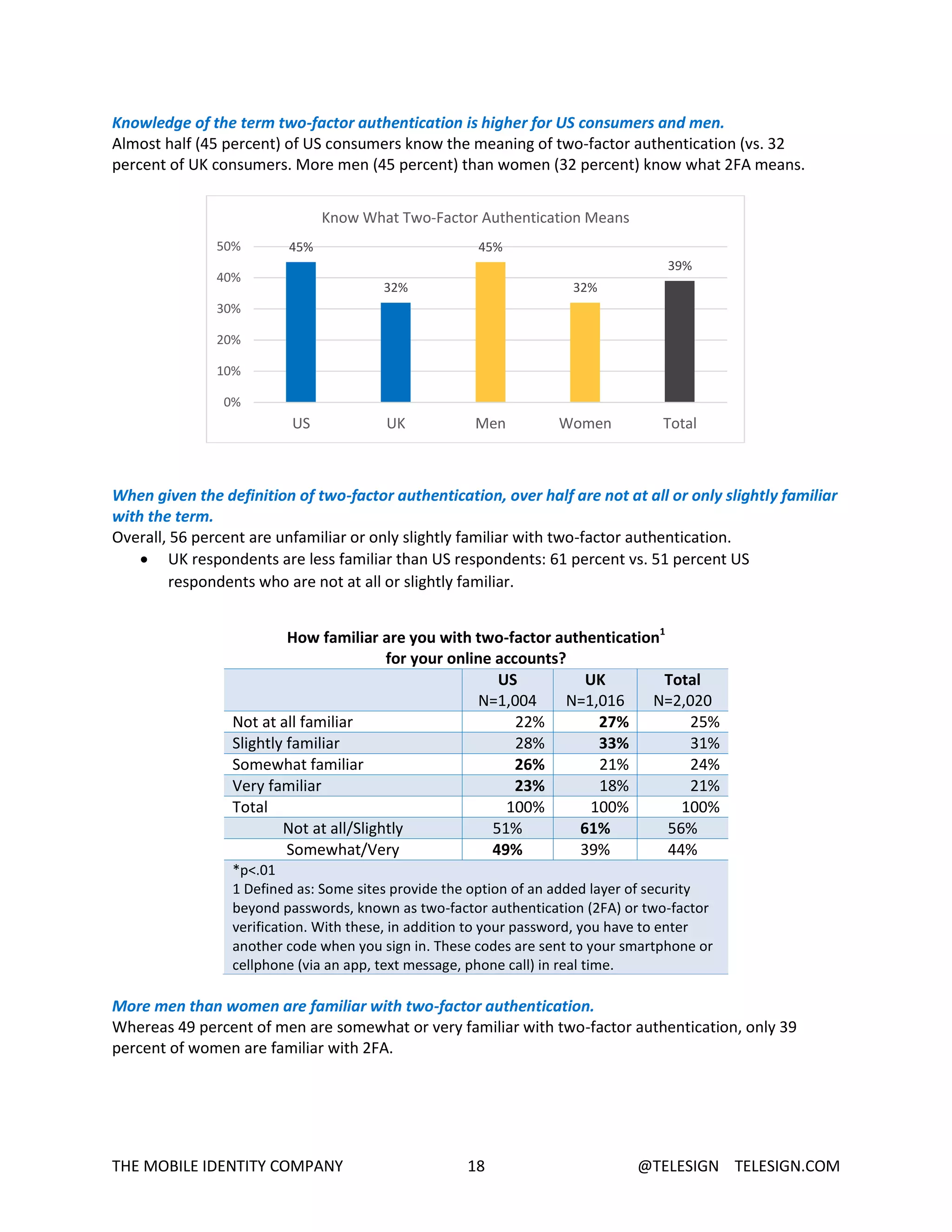
The document is a summary report of a study on consumer digital security concerns and practices. Some of the key findings include:
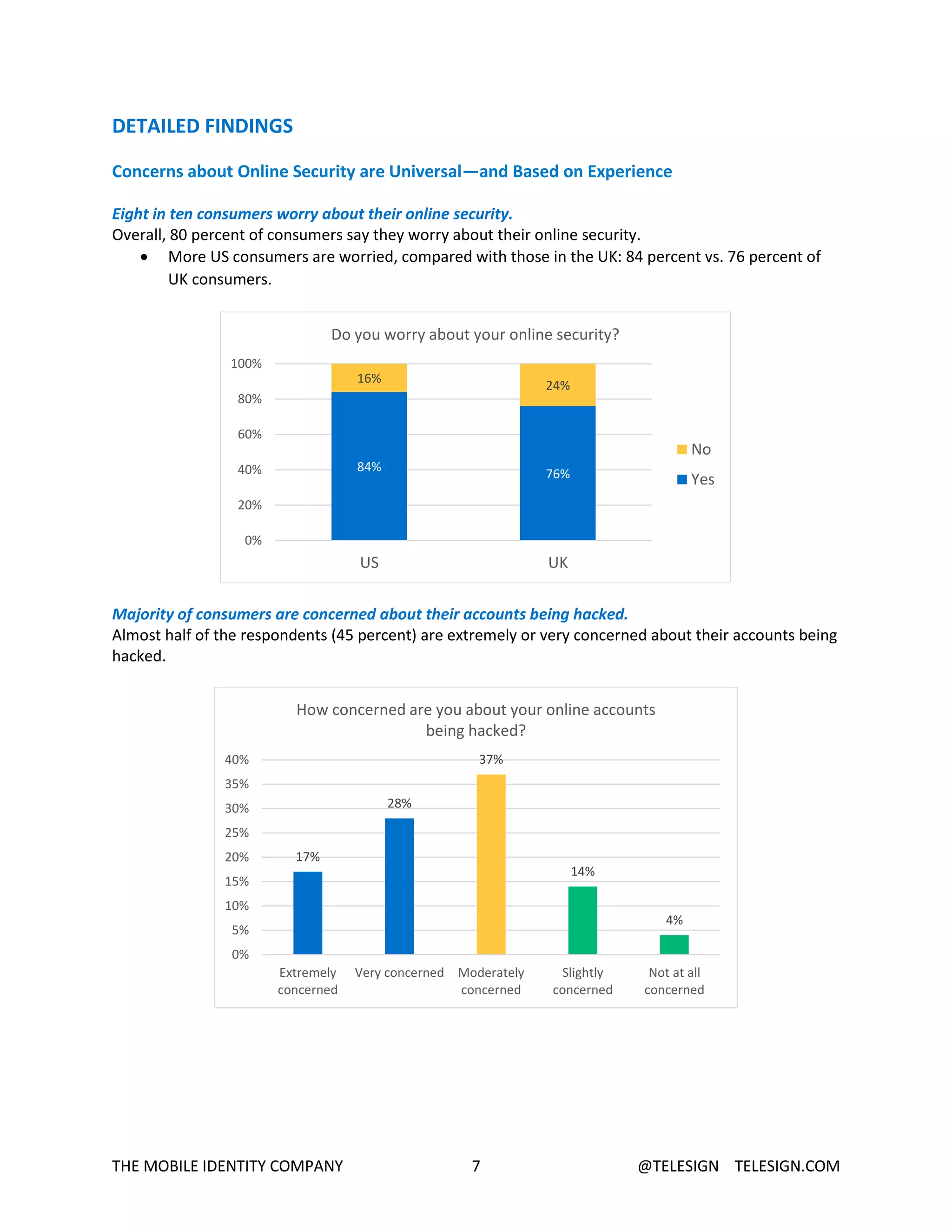
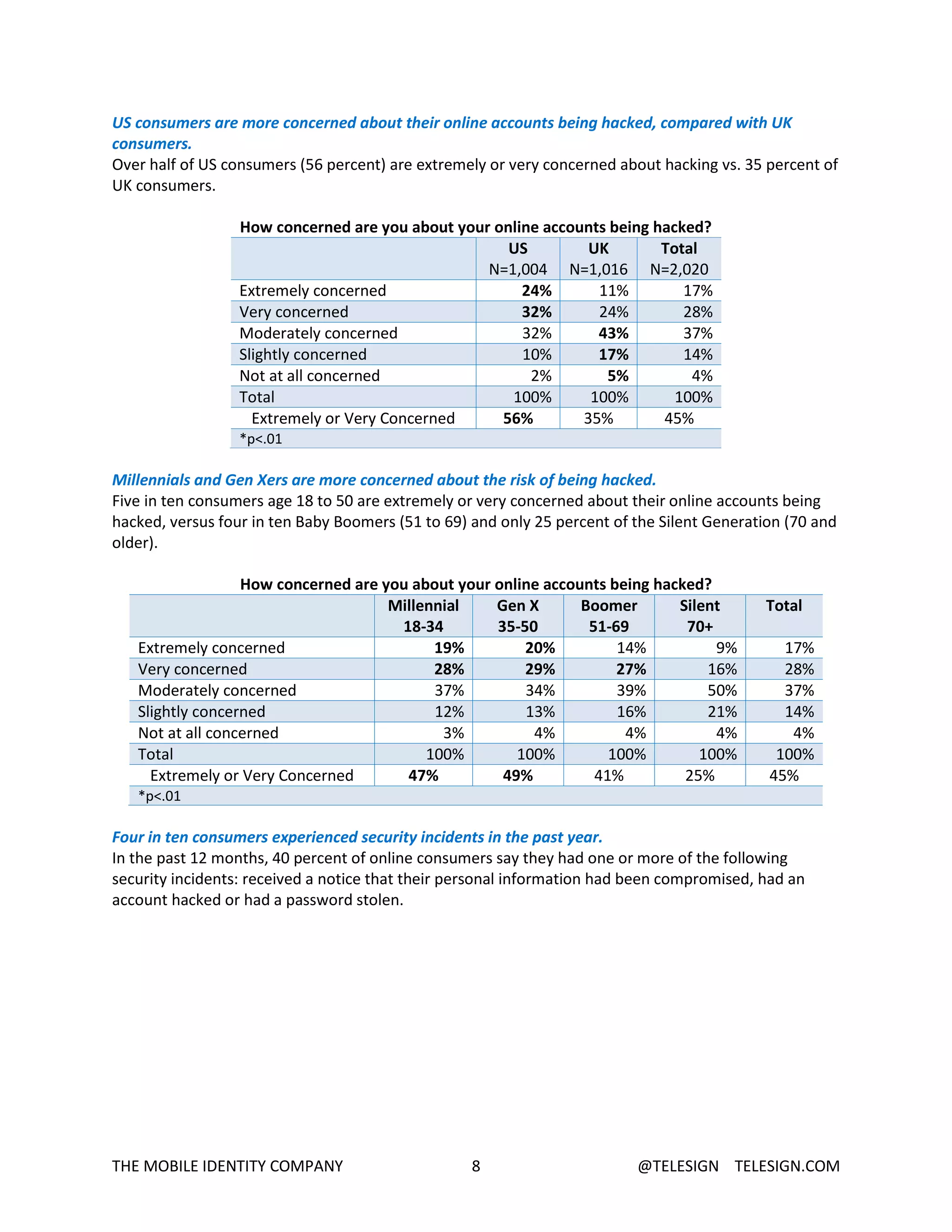
- 80% of consumers worry about online security and 45% are very or extremely concerned about their accounts being hacked.
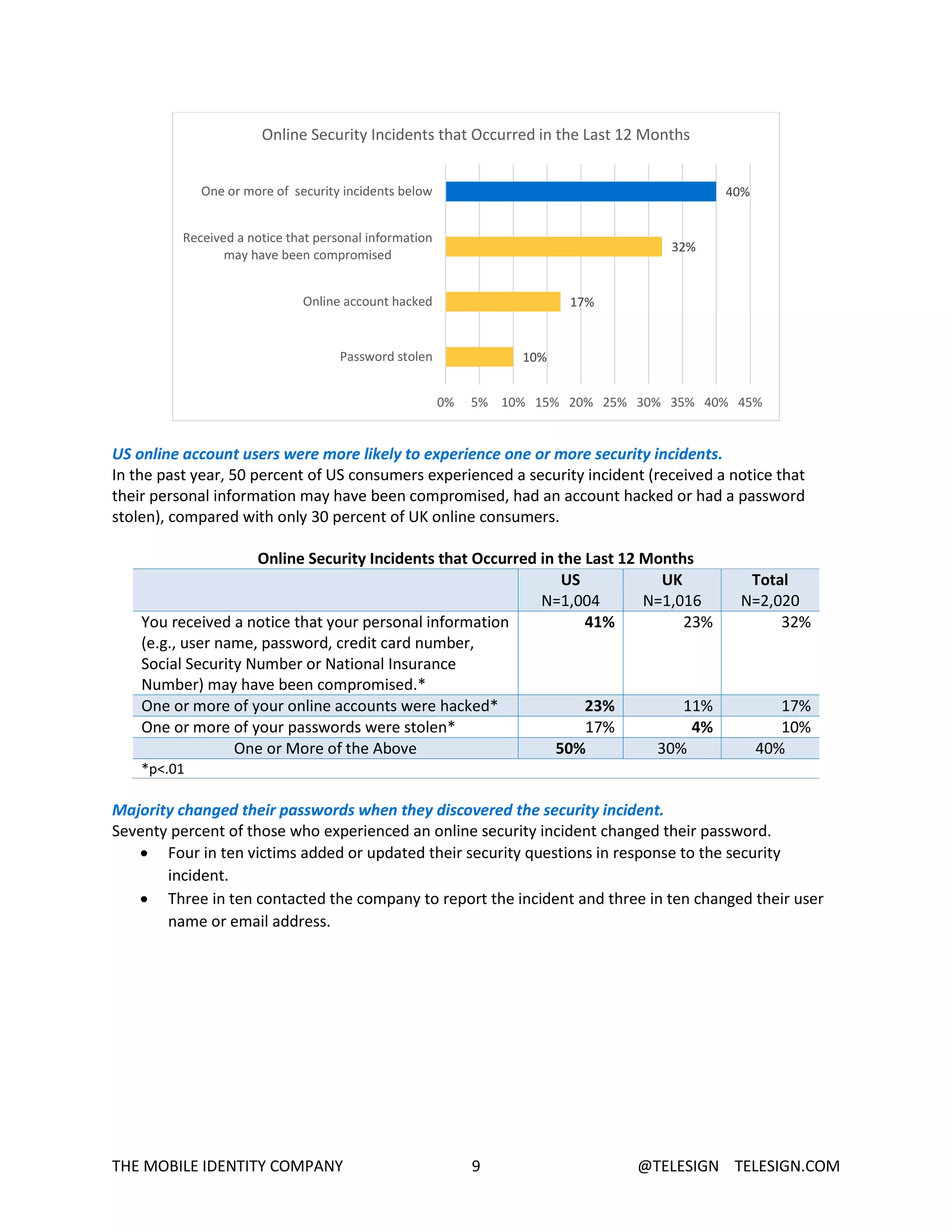
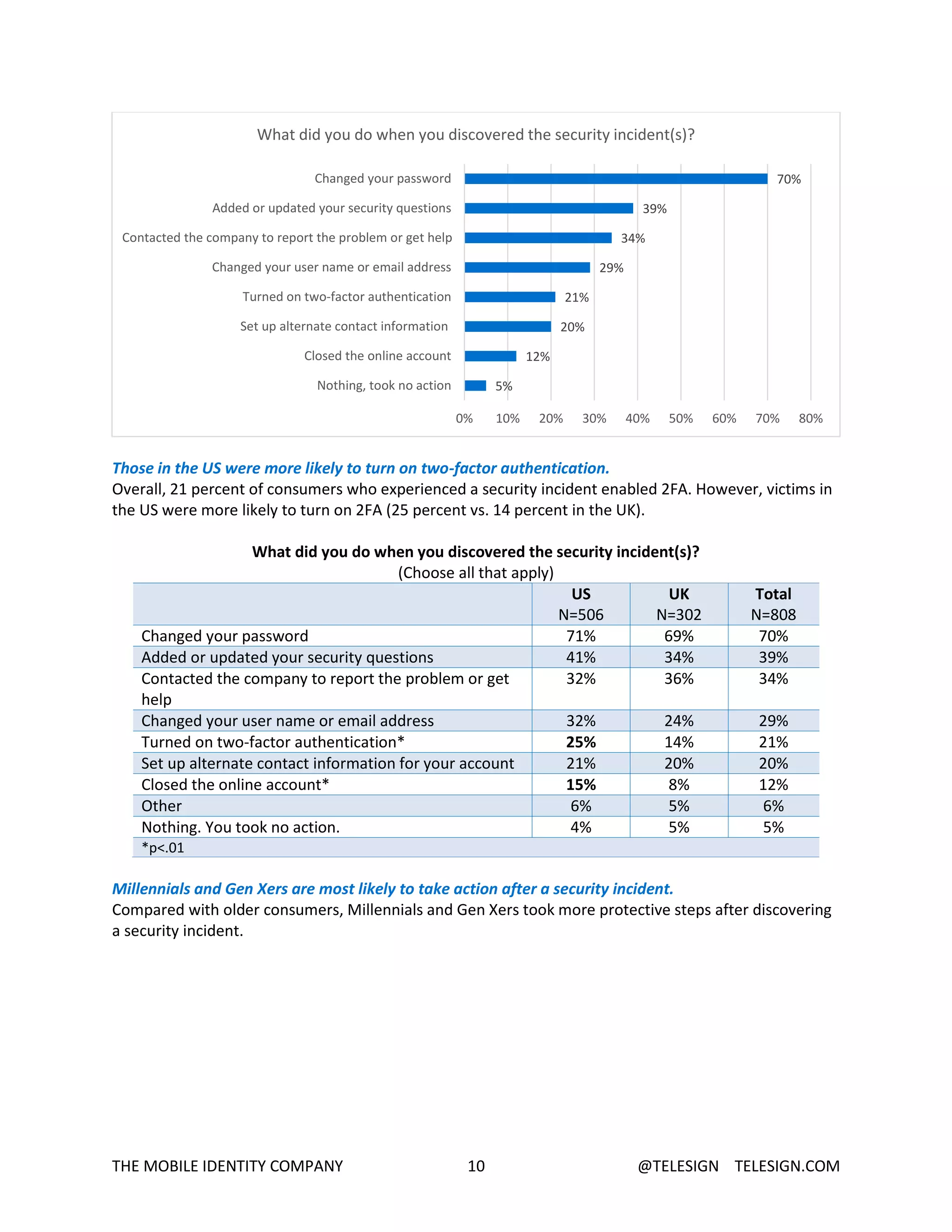
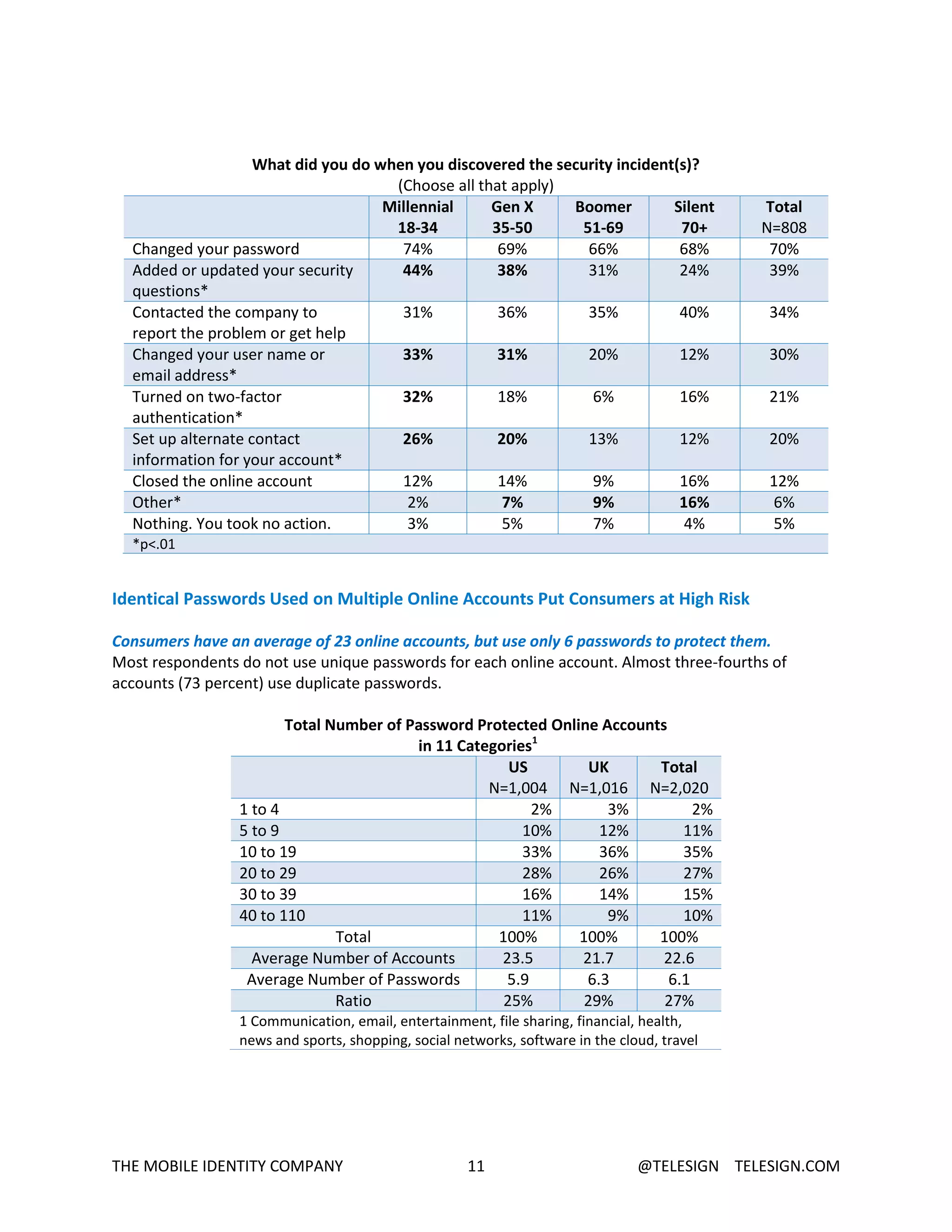
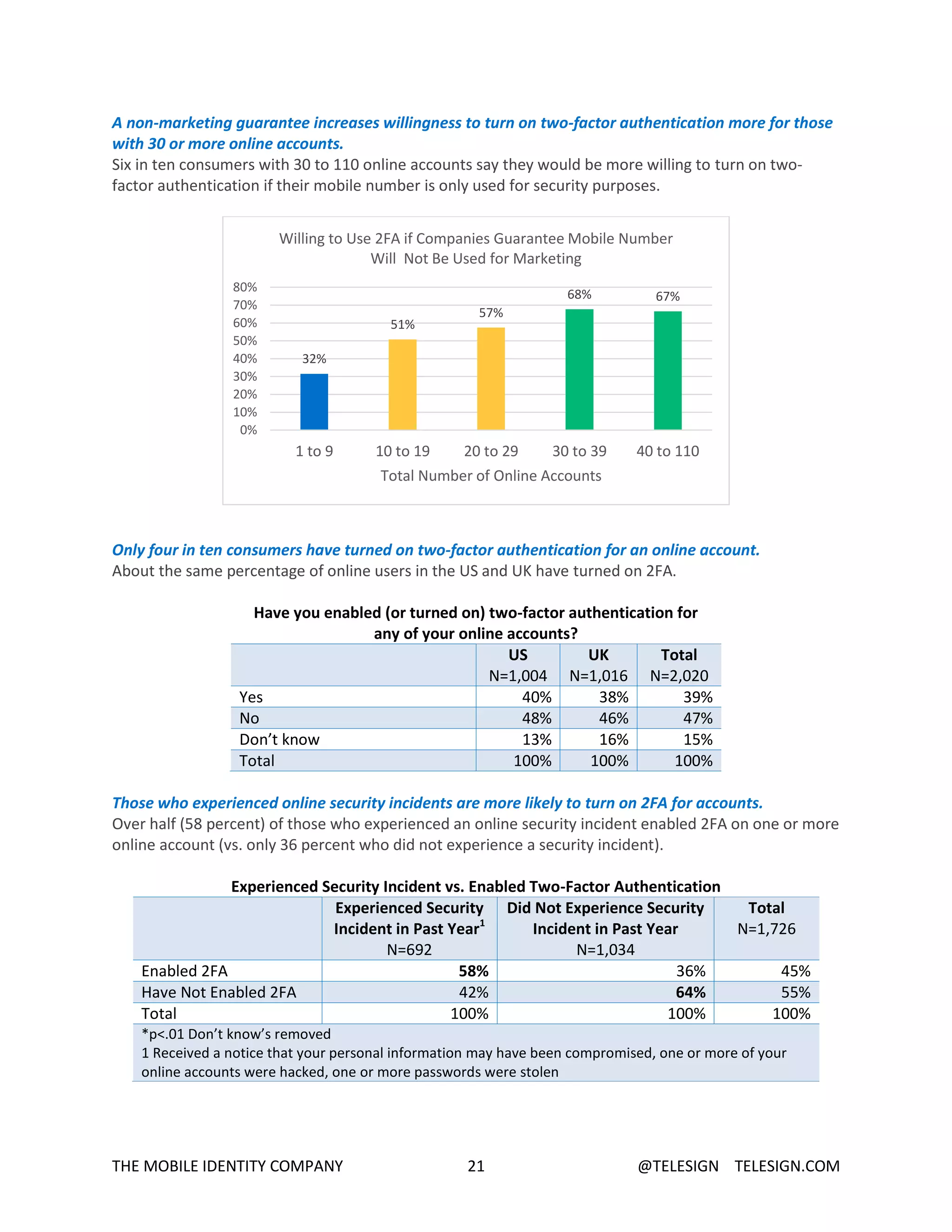
- In the past year, 40% of consumers experienced a security incident like a data breach or hacked account.
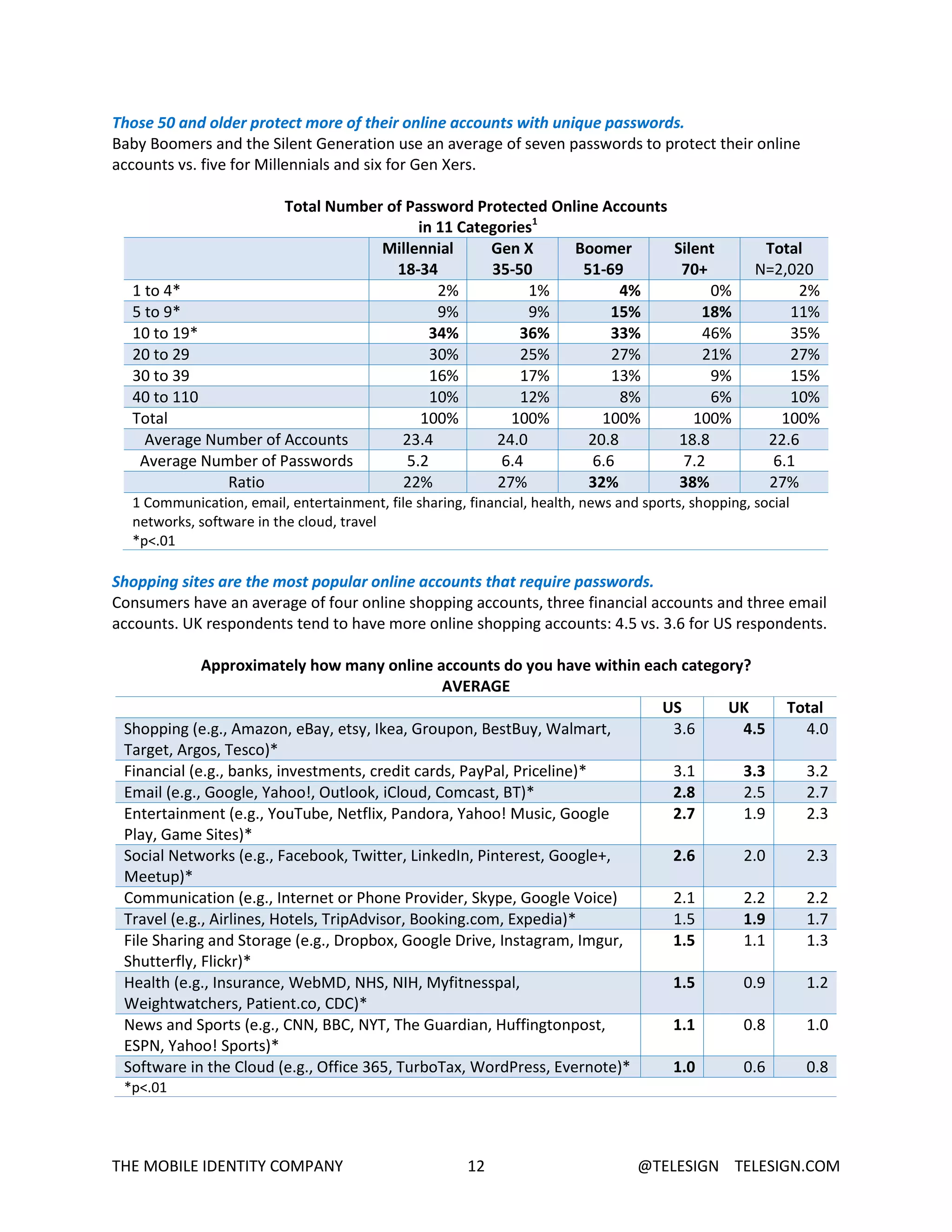
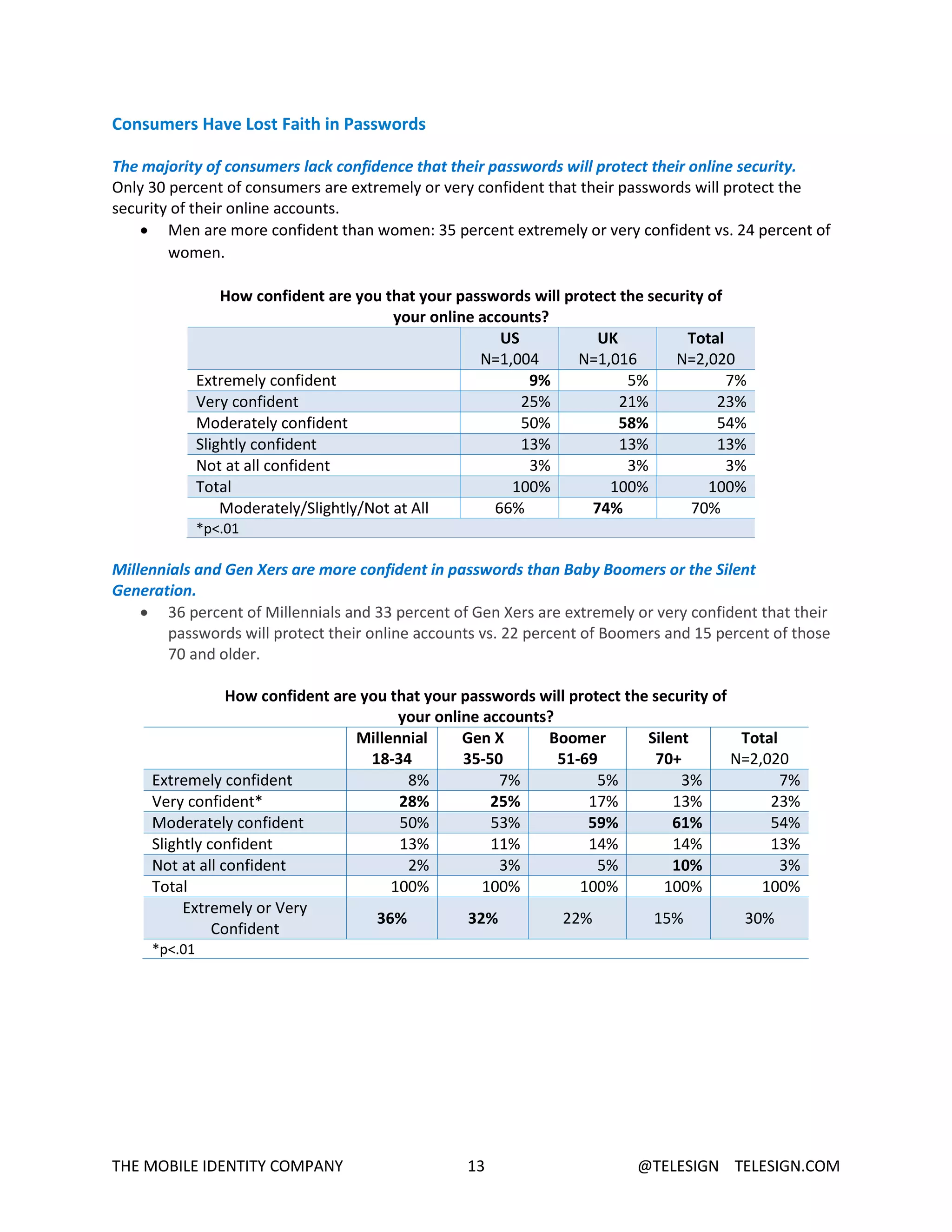
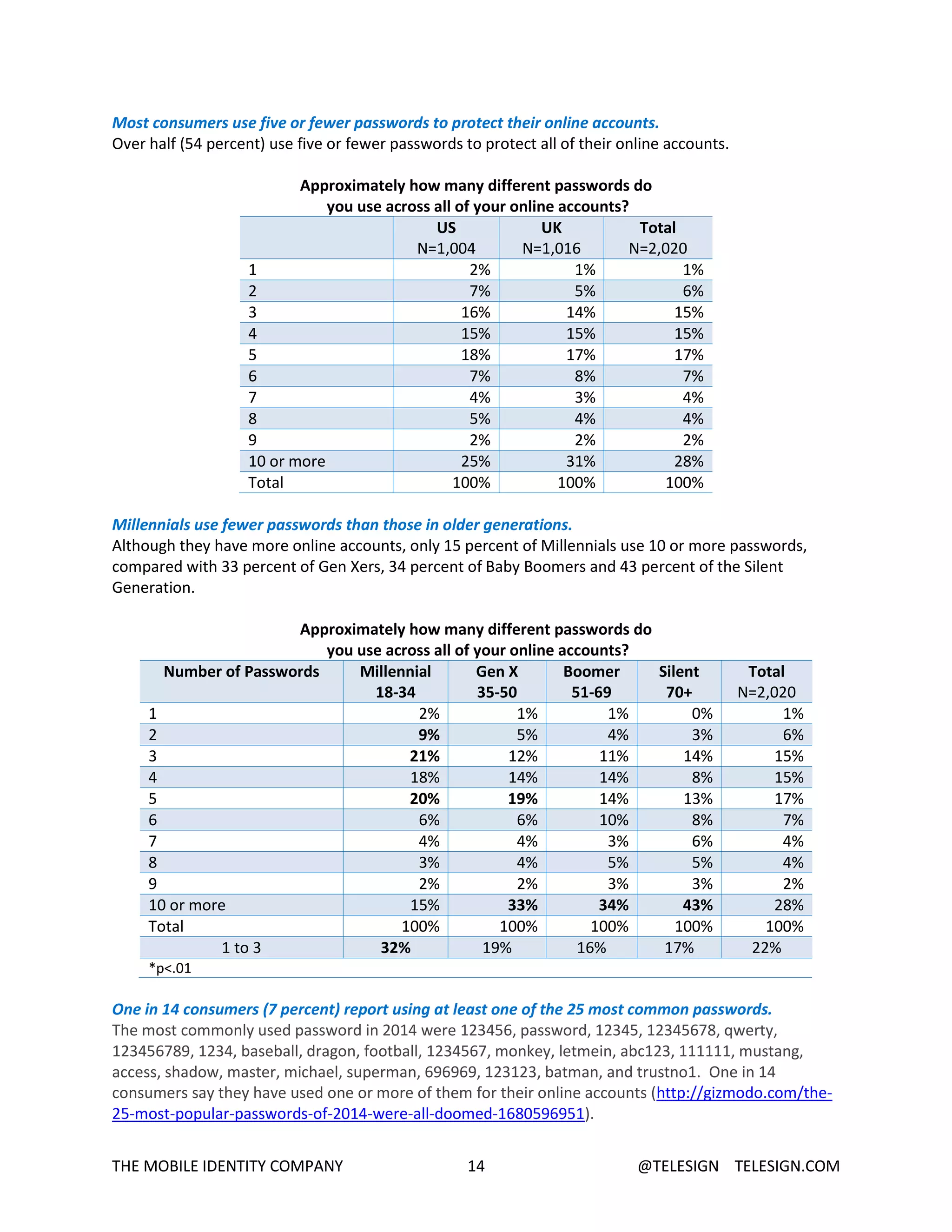
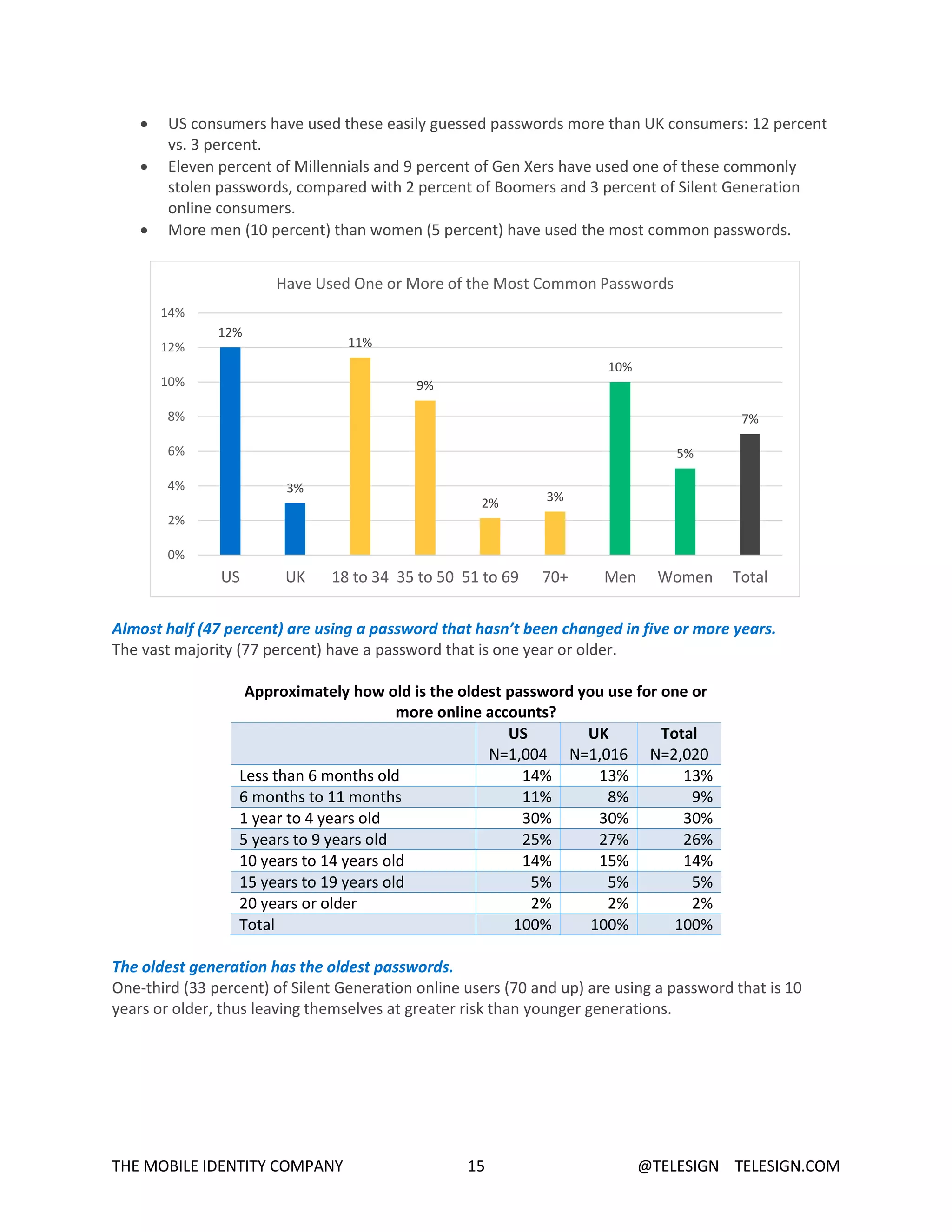
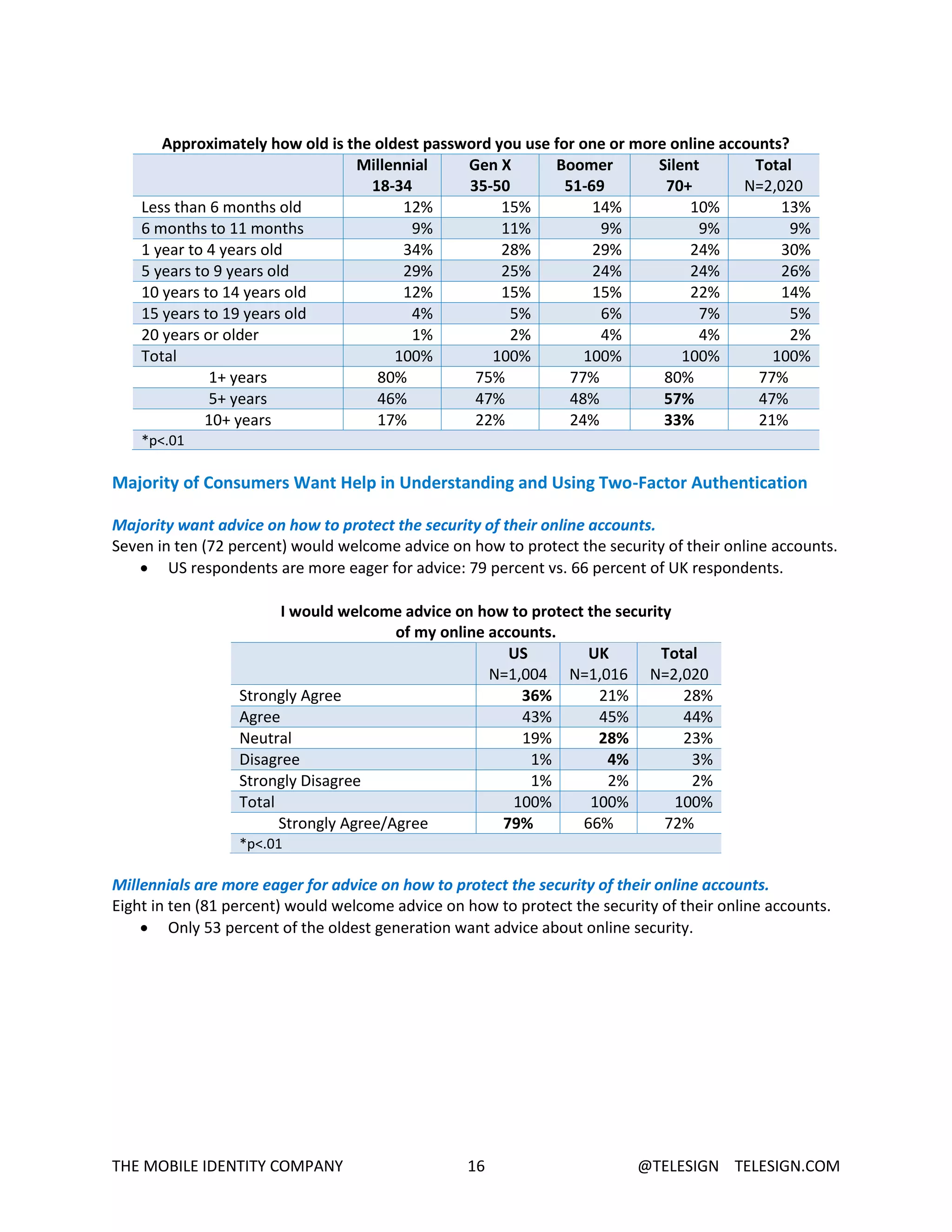
- Consumers have little confidence in passwords and tend to reuse the same few passwords across many accounts, putting their security at high risk.
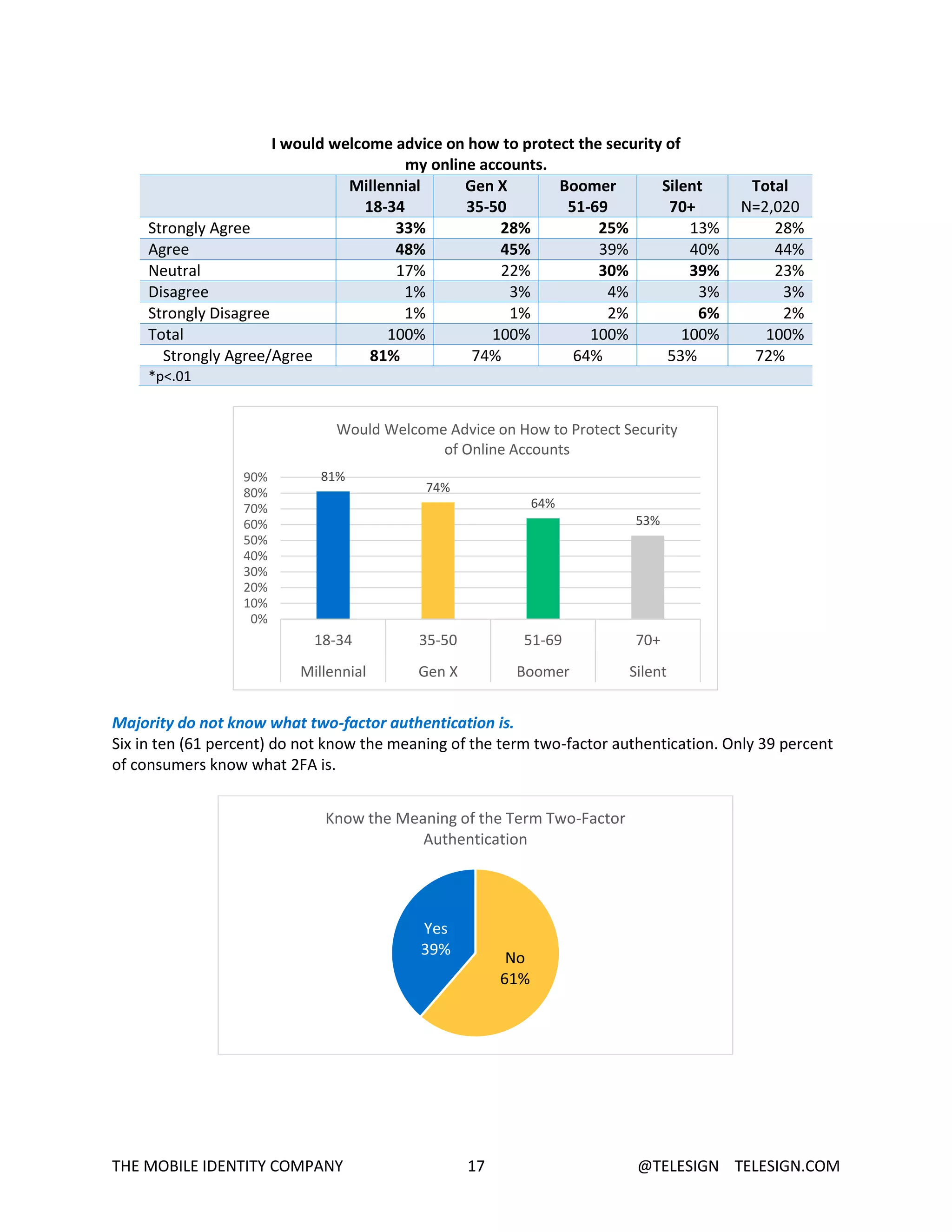
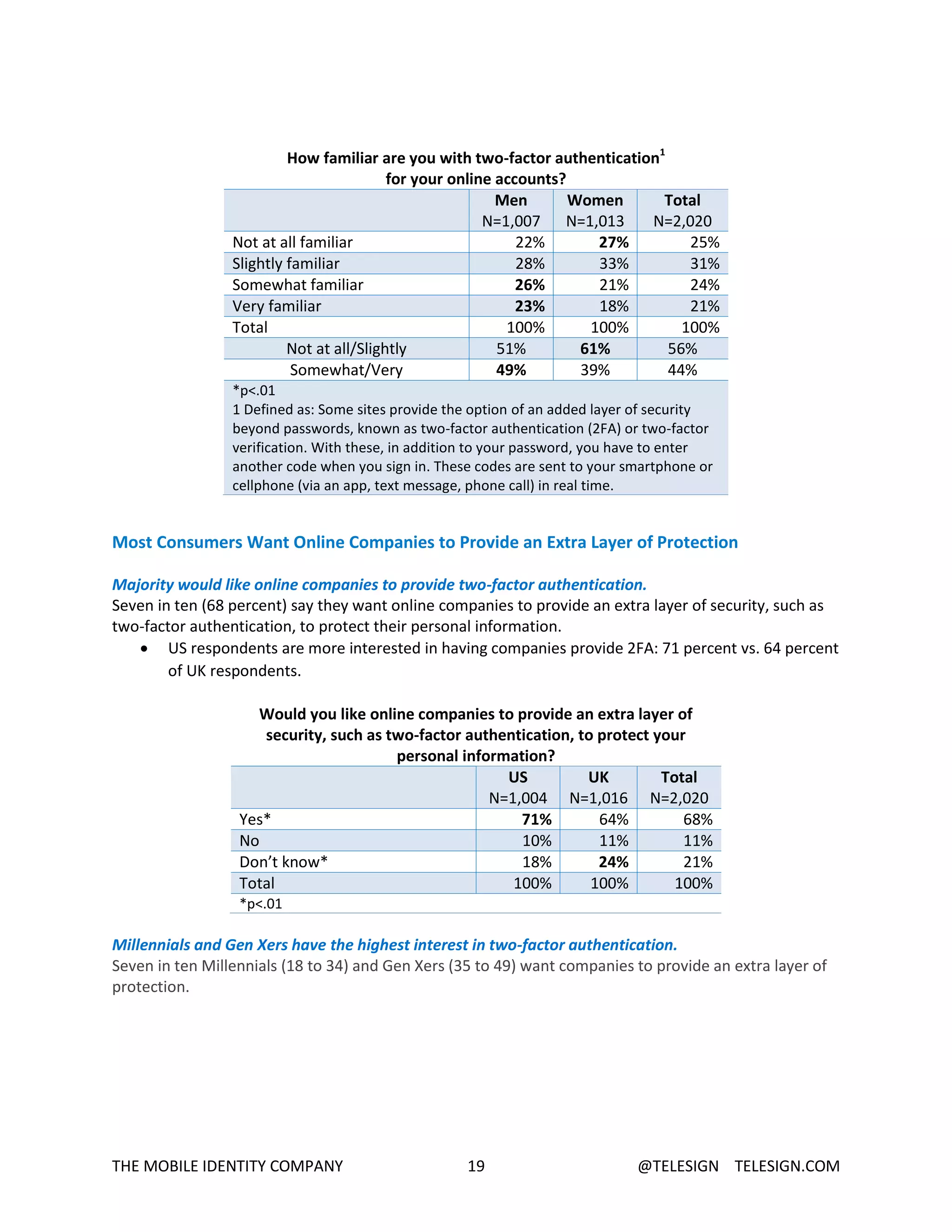
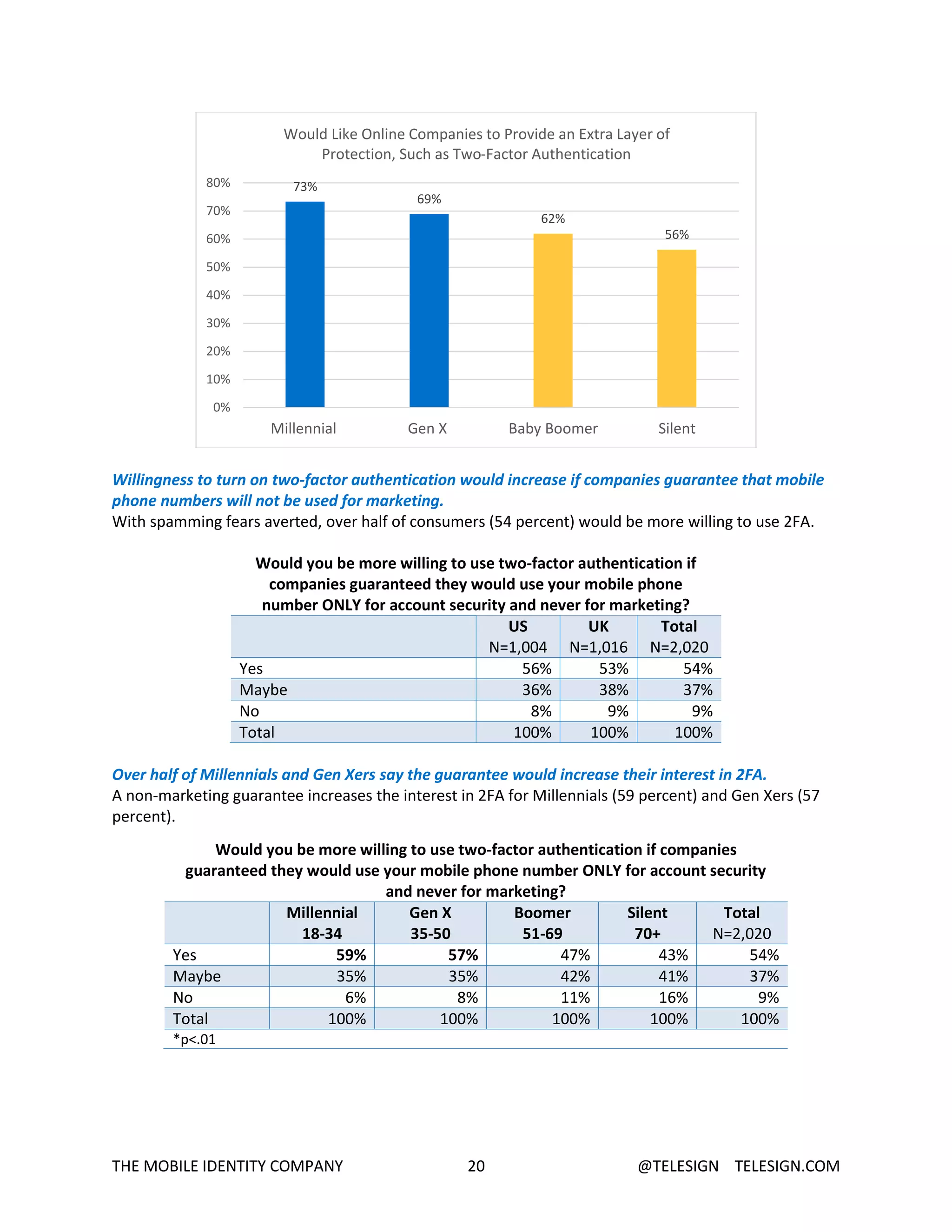
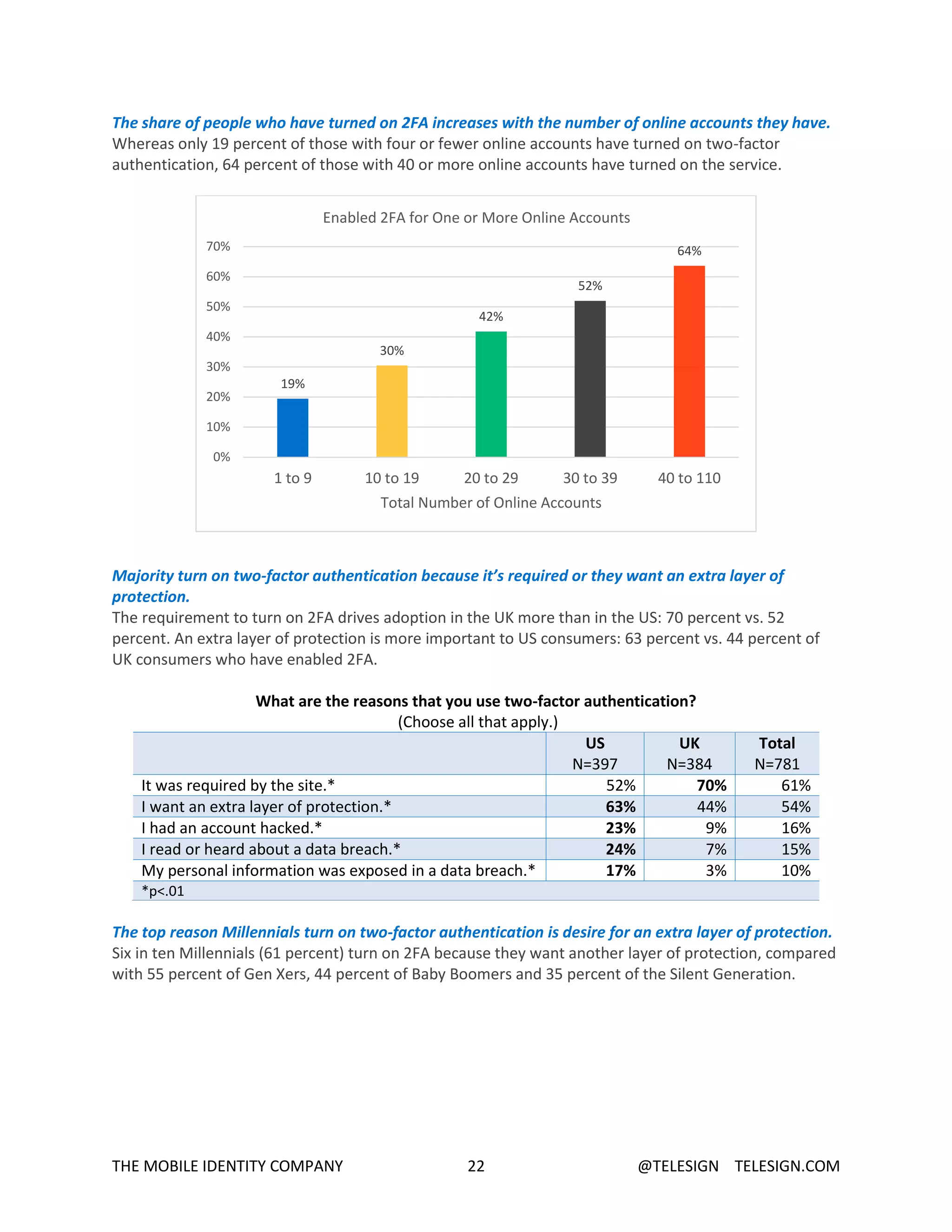
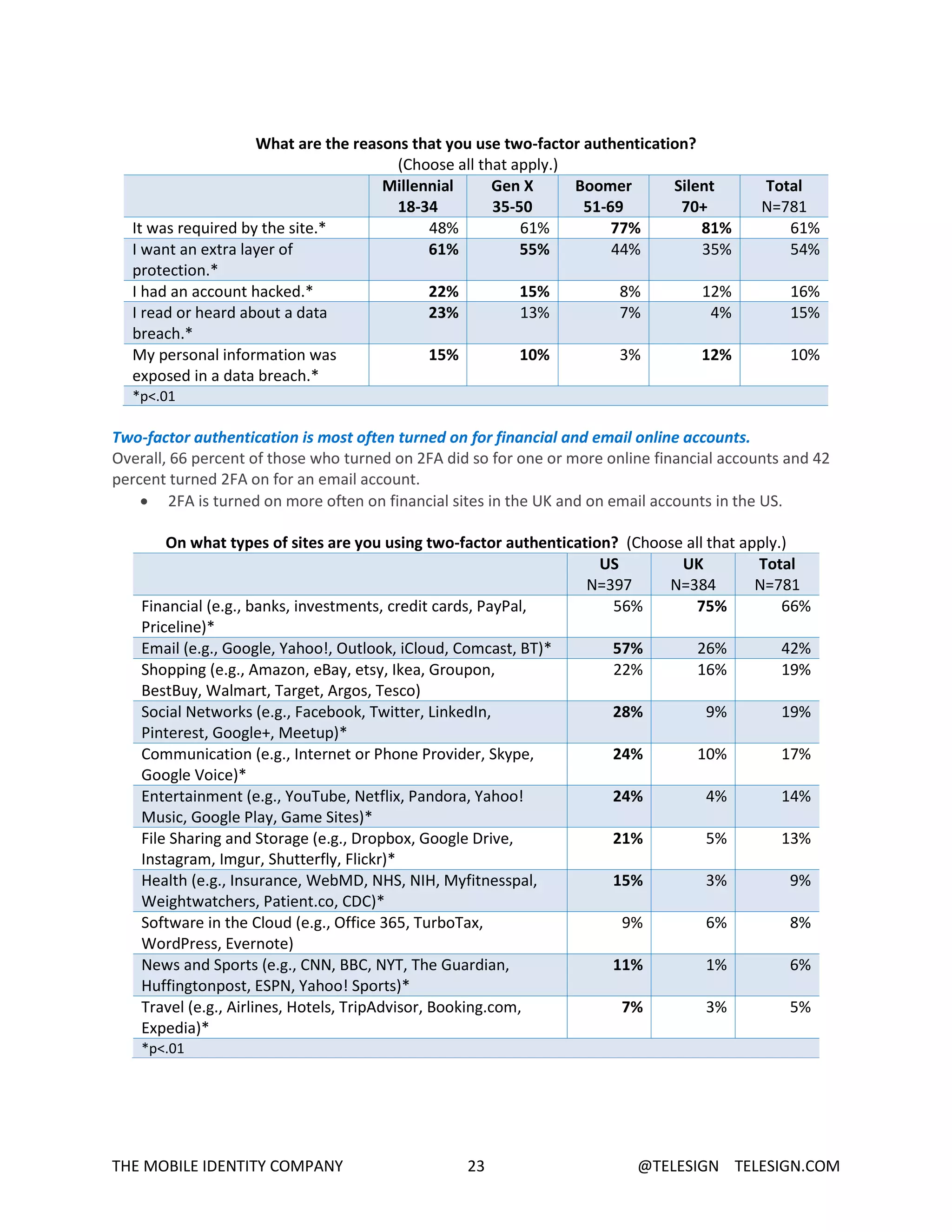
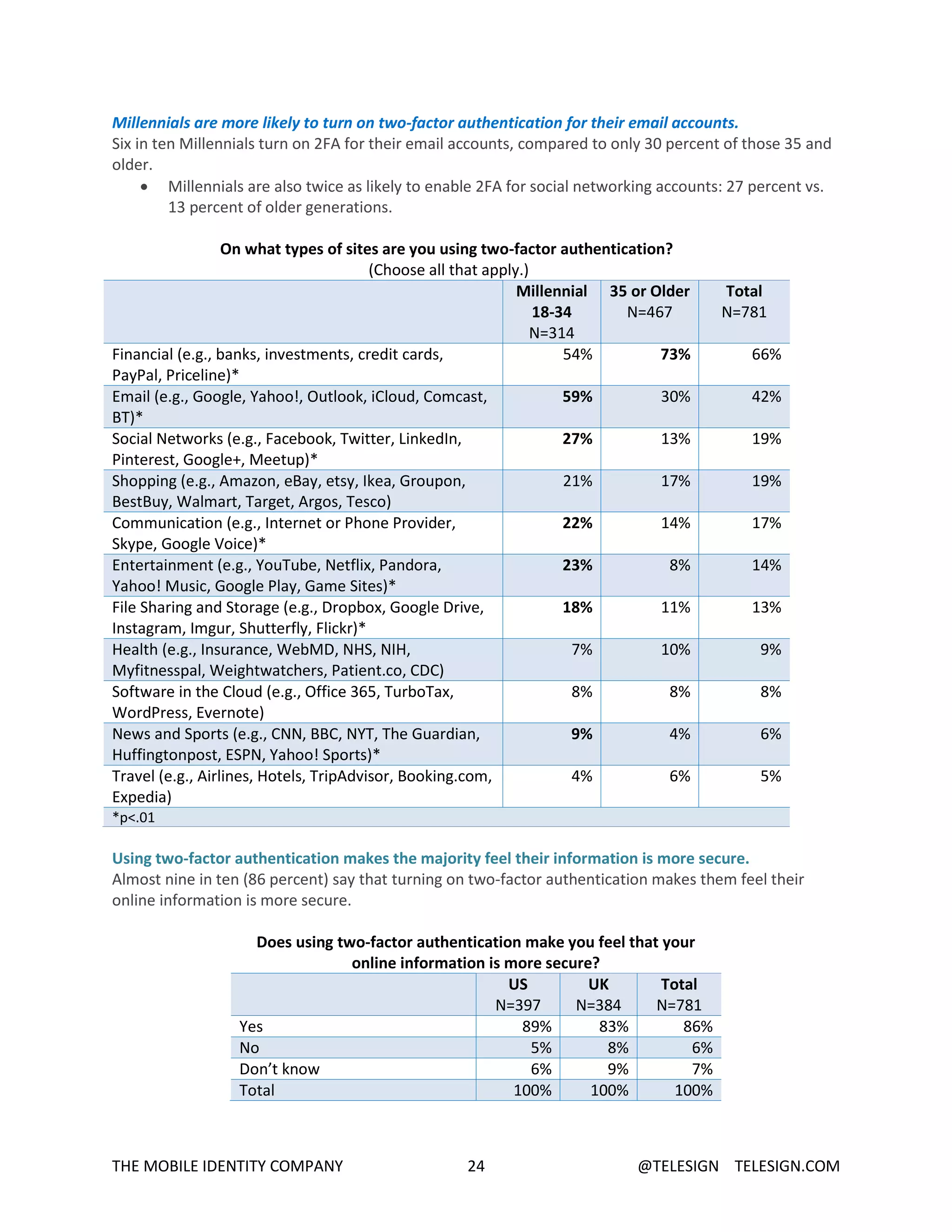
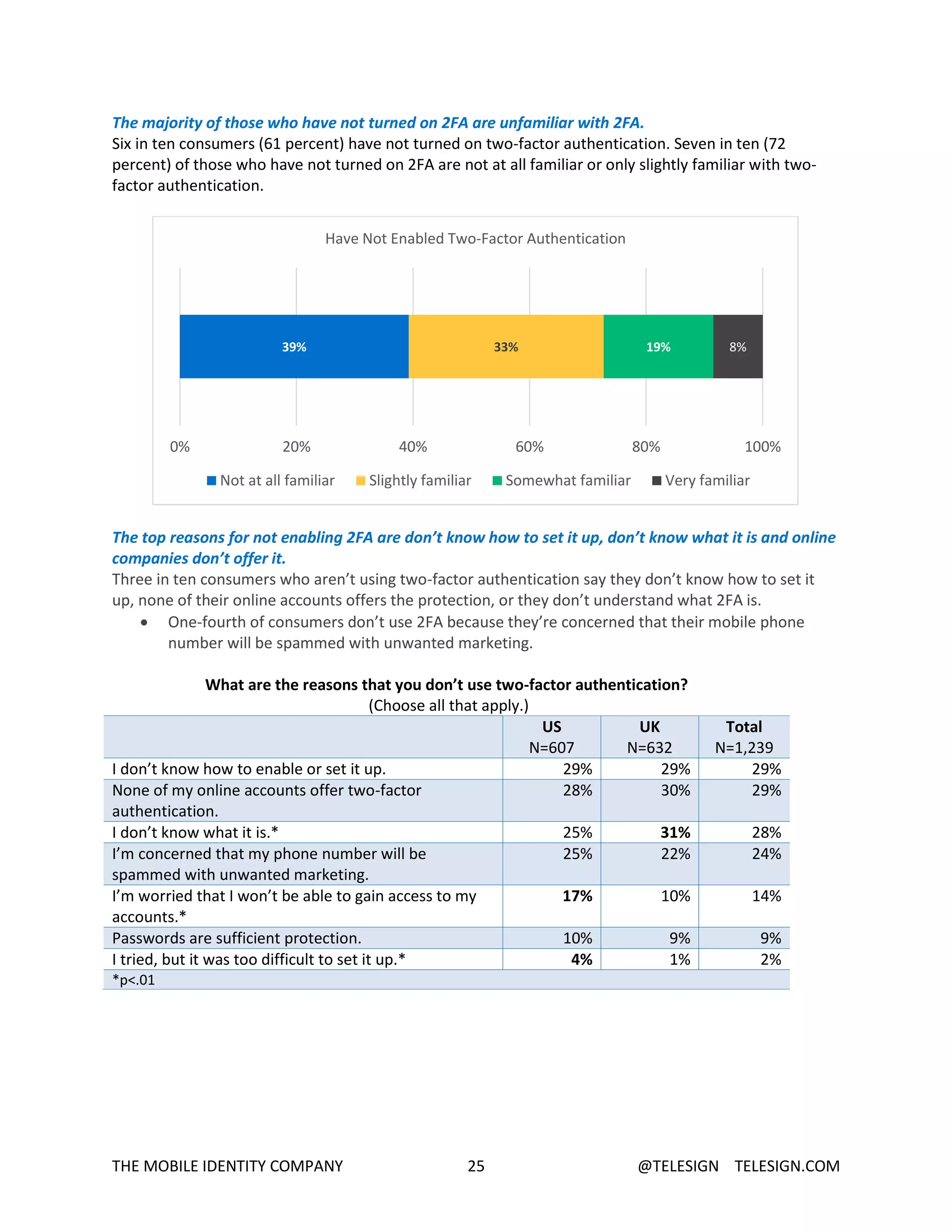
- While two-factor authentication provides stronger security, 61% of consumers have not enabled it due to lack of awareness, understanding, or companies not offering it.
- Consumers want help protecting