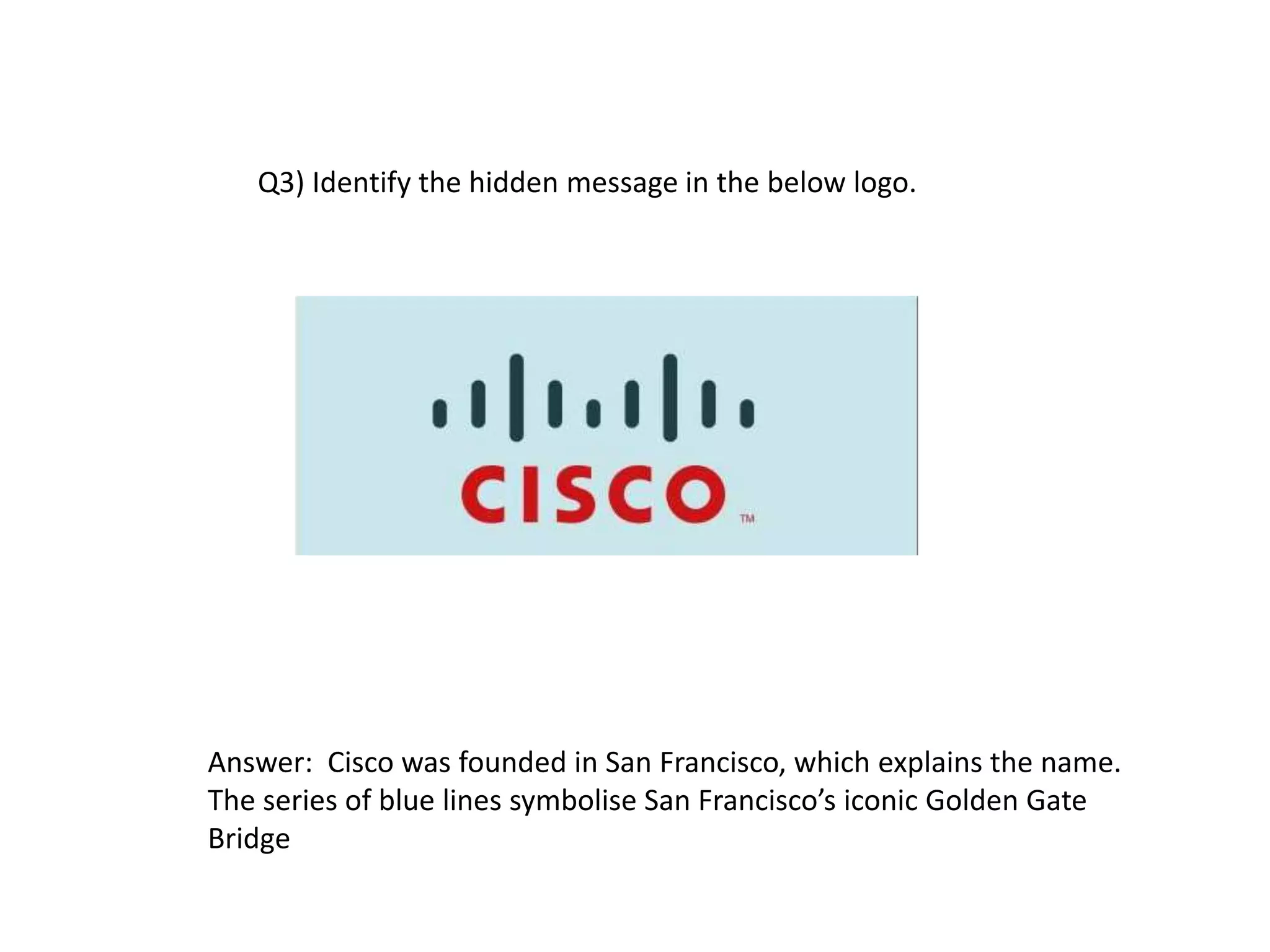
The document contains a technical quiz with multiple choice questions testing knowledge of coding, programming languages like C and Java, computer hardware, operating systems, and other technical topics. There are sections on coding, visual identification, rapid fire, and buzzer round questions. The quiz contains over 40 questions testing a range of foundational and advanced computing concepts.
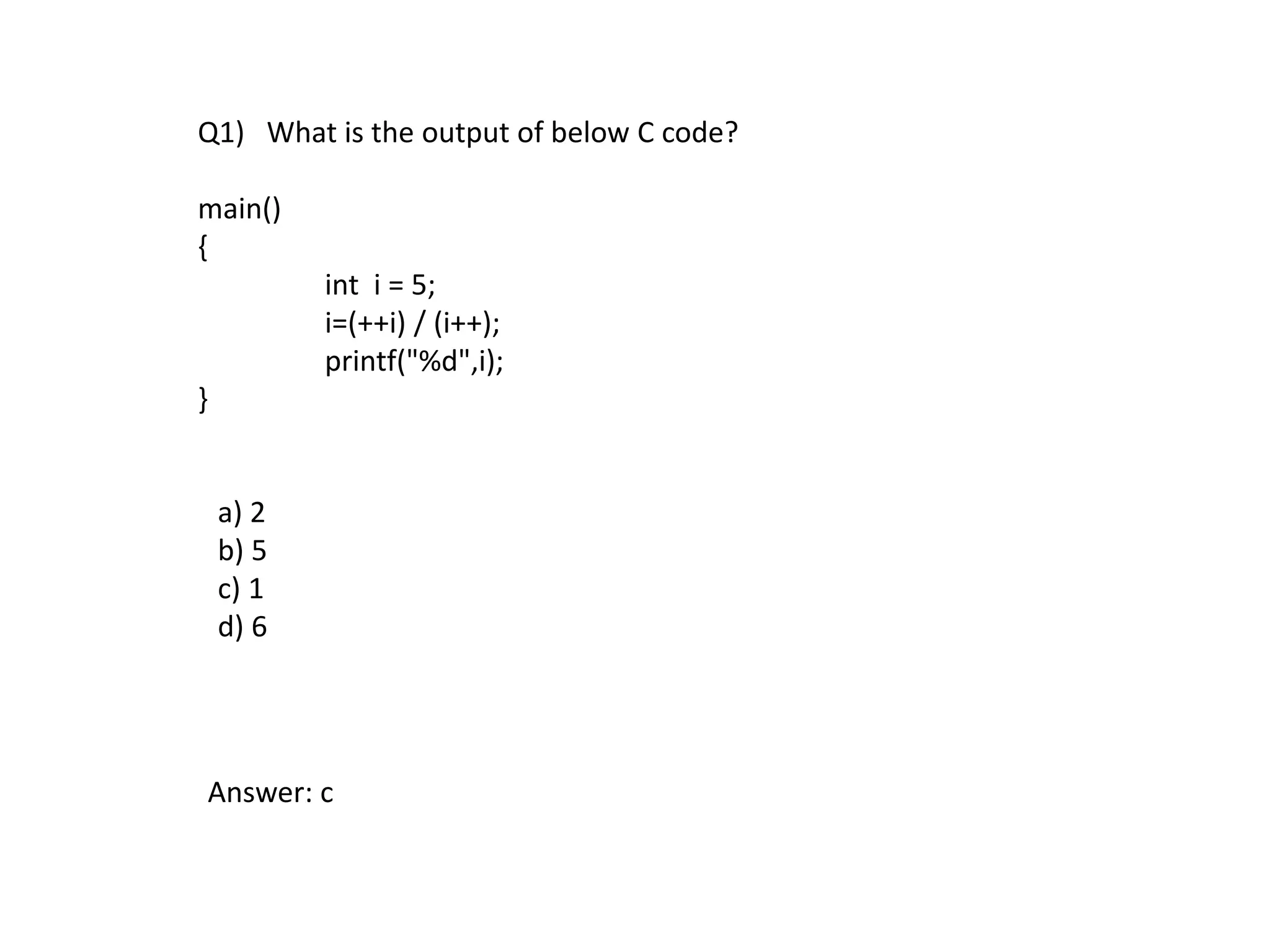
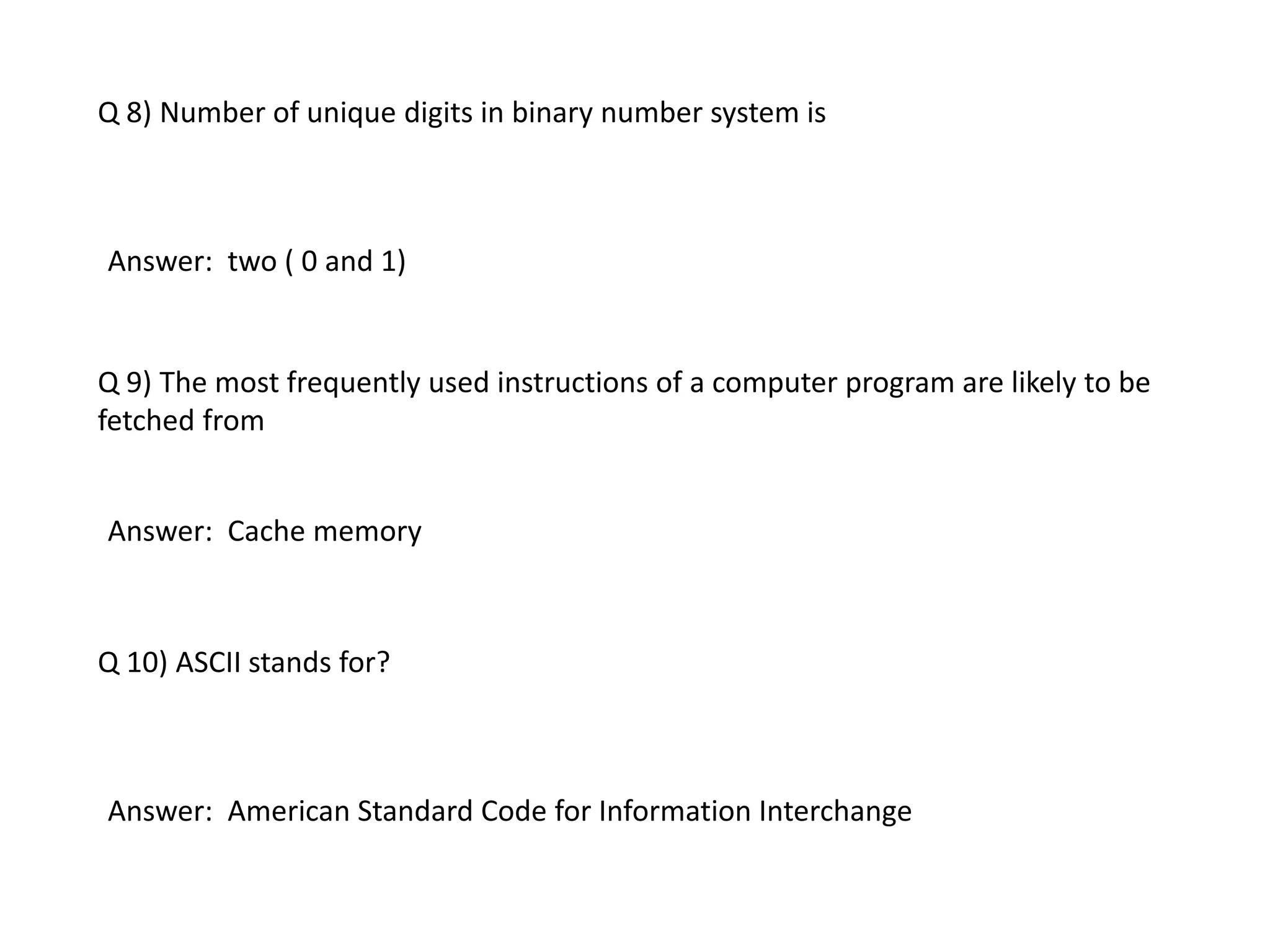
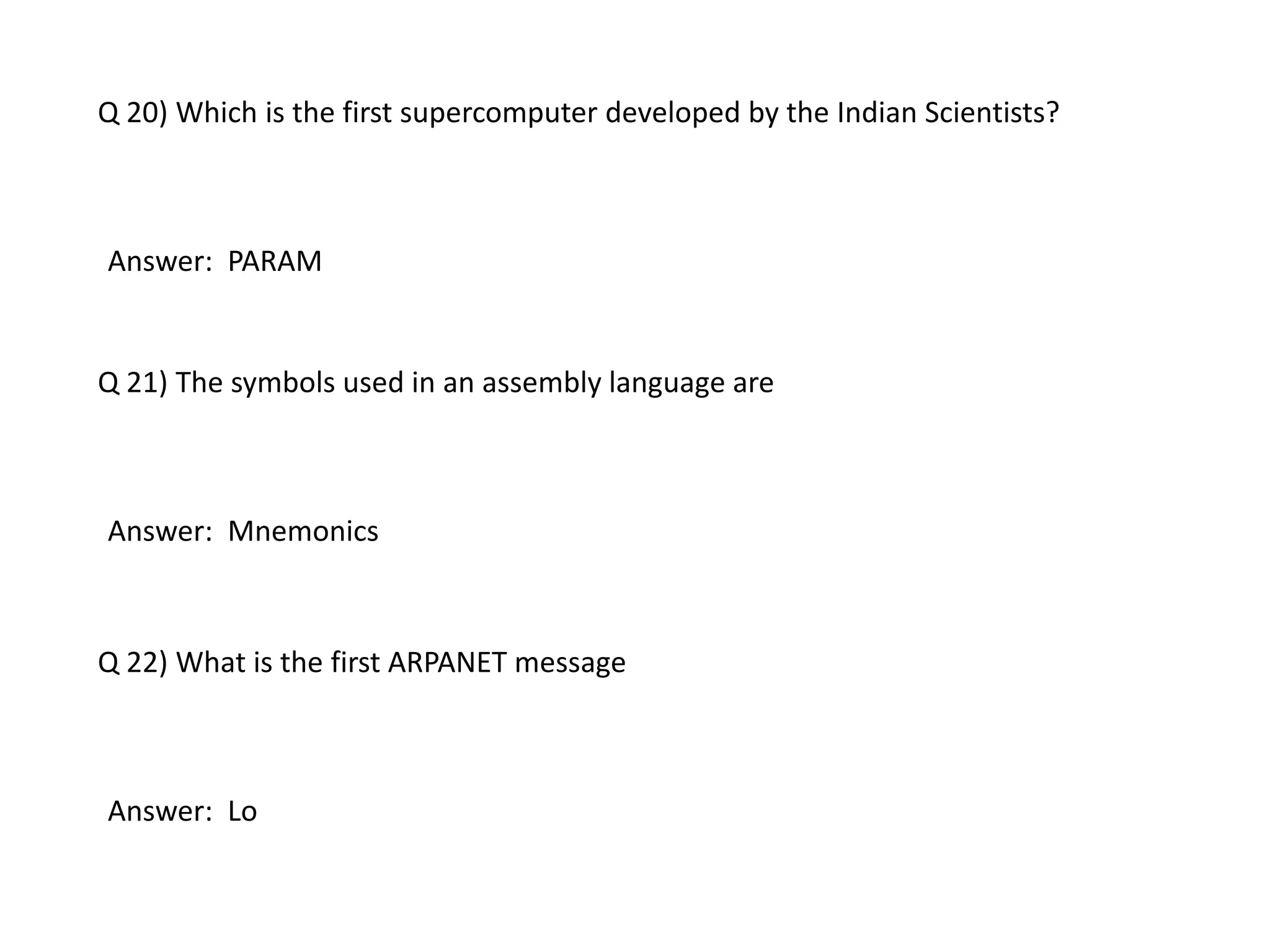
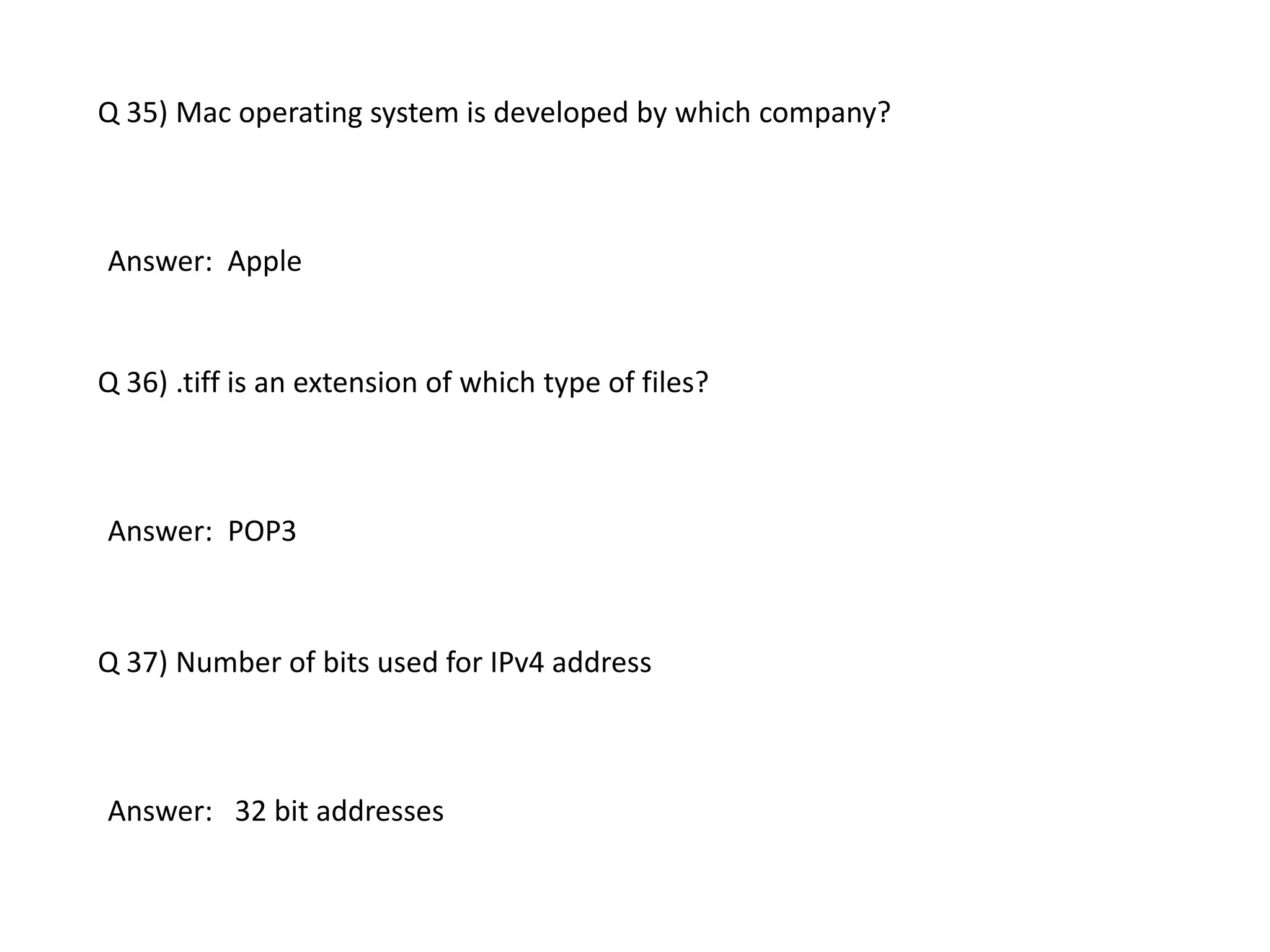
![Q2) What is the output of below code?
main()
{
int h =5;
static char wer[] = "No Substitute for hard work";
printf("%-10.*s",h,wer);
}
a) No su
b)No Su
c) No Sub
d) error message
Answer: b](https://image.slidesharecdn.com/technicalquiz1-160131060143/75/Computer-ScienceTechnical-quiz-4-2048.jpg)
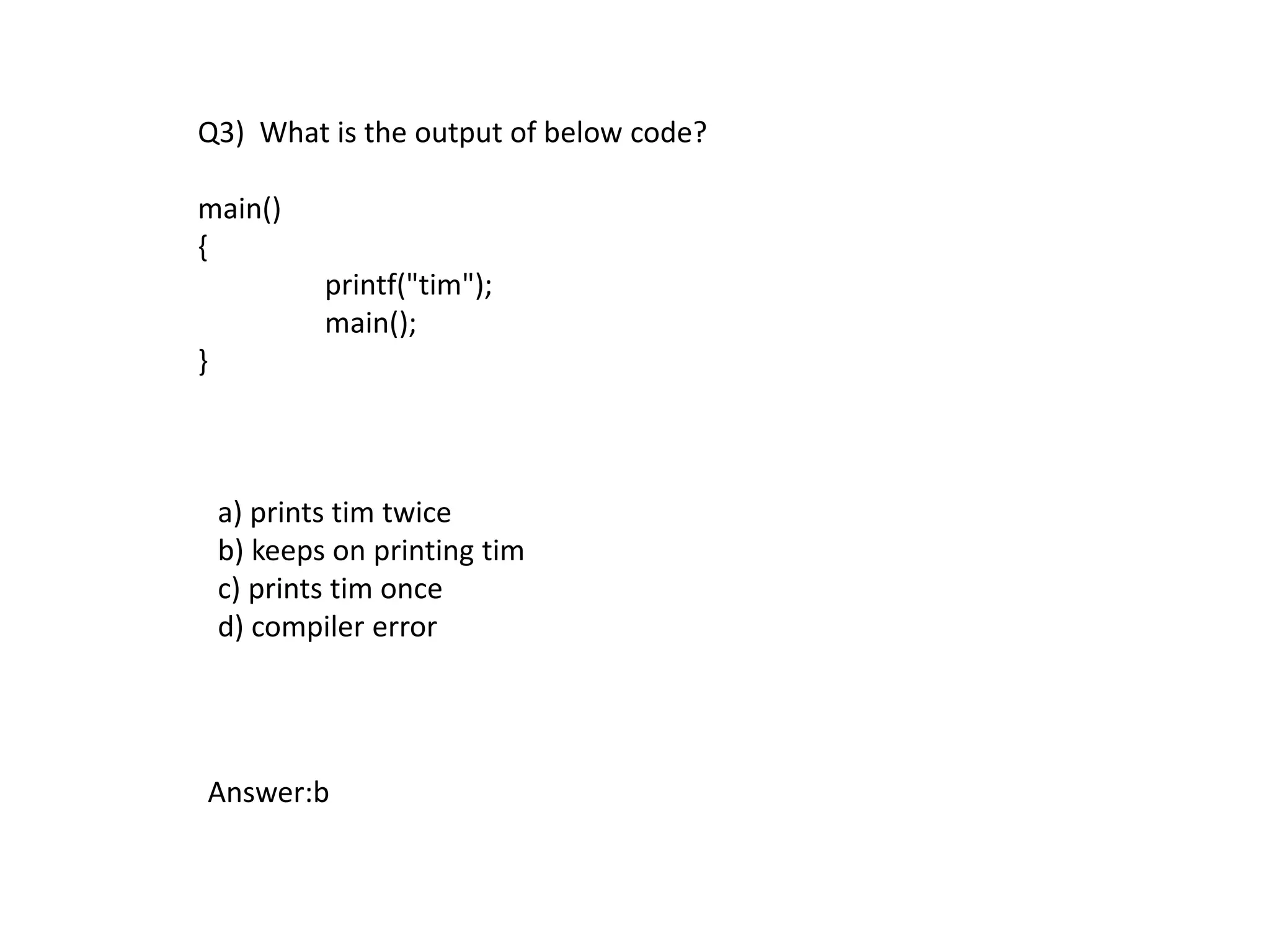
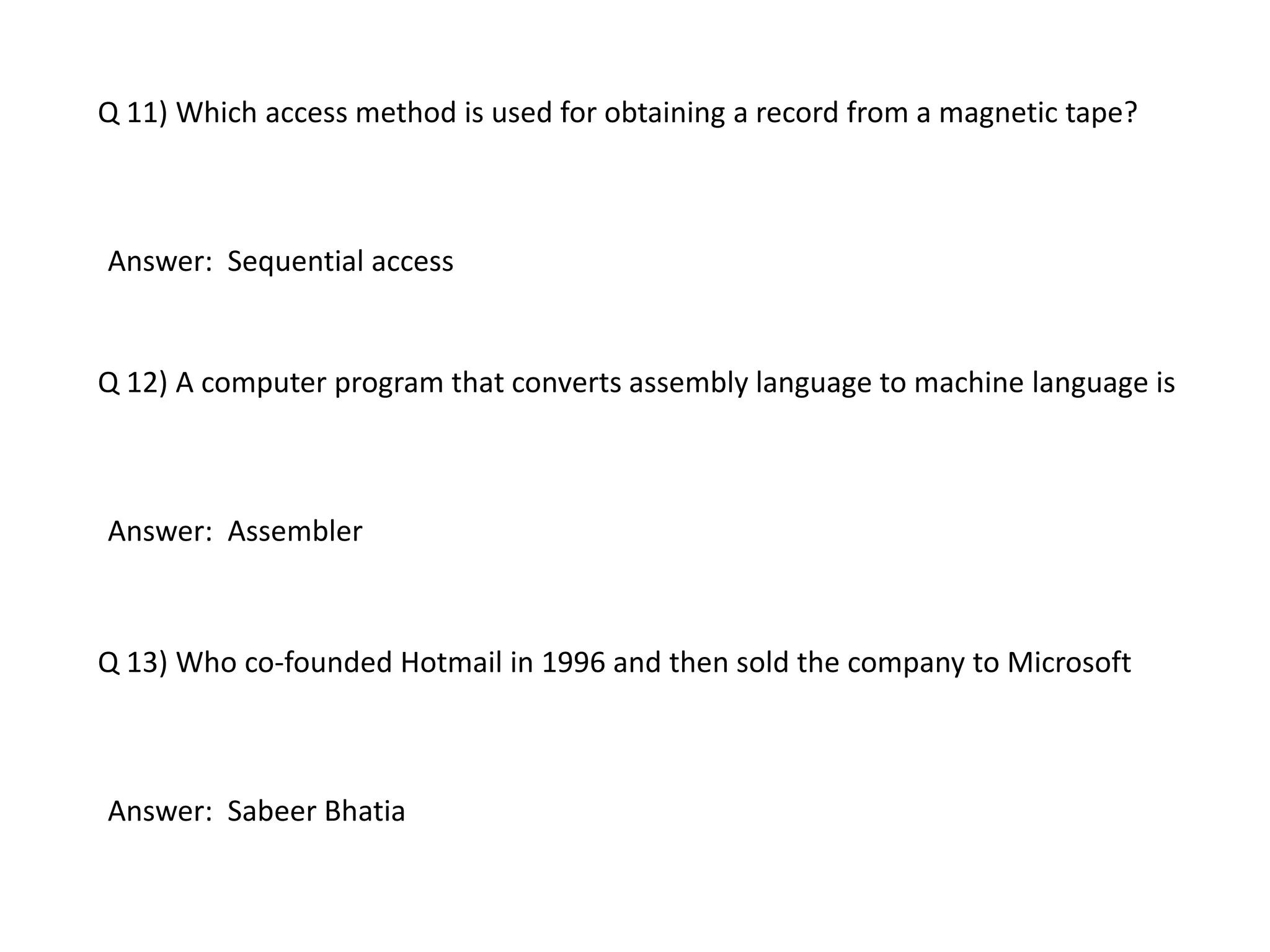
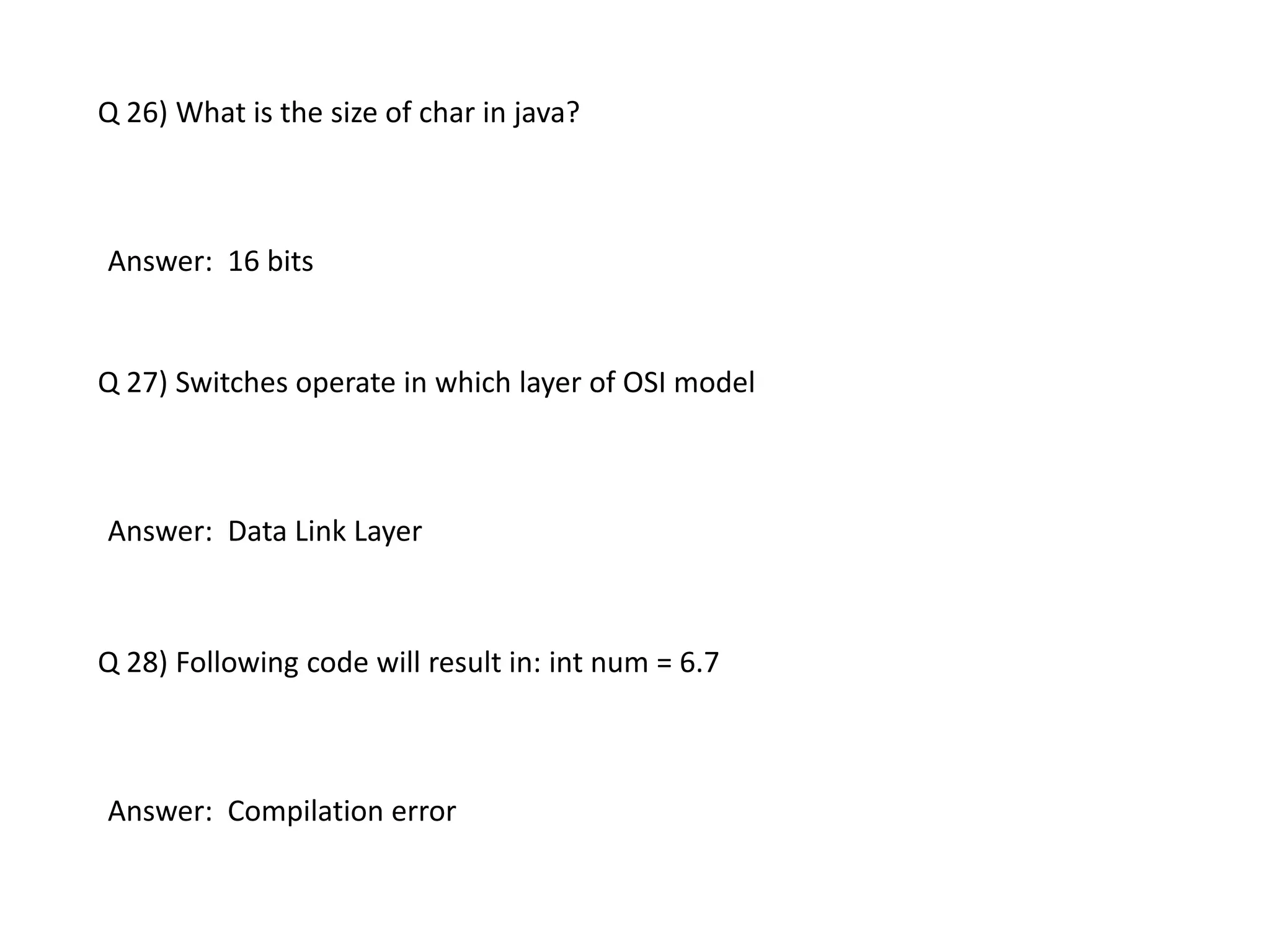
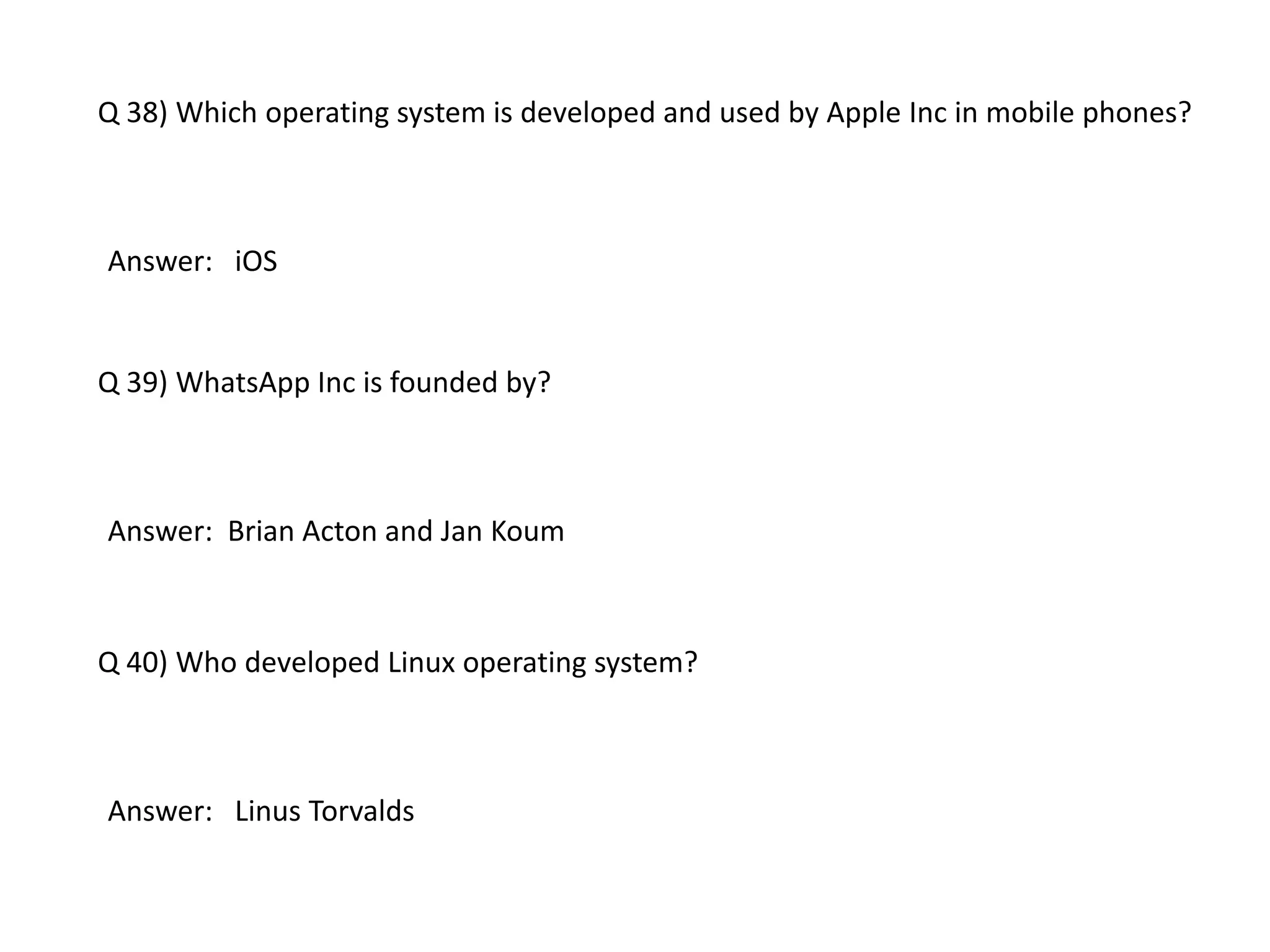
![Q6) What is the output of below code in JAVA?
class S
{
int x = 0;
S()
{
x++;
}
public static void main(String args[])
{
S s = new S();
System.out.println(s.x);
}
}
(a) 0
(b) 1
(c) compiler error
(d) Garbage value
Answer: b](https://image.slidesharecdn.com/technicalquiz1-160131060143/75/Computer-ScienceTechnical-quiz-8-2048.jpg)
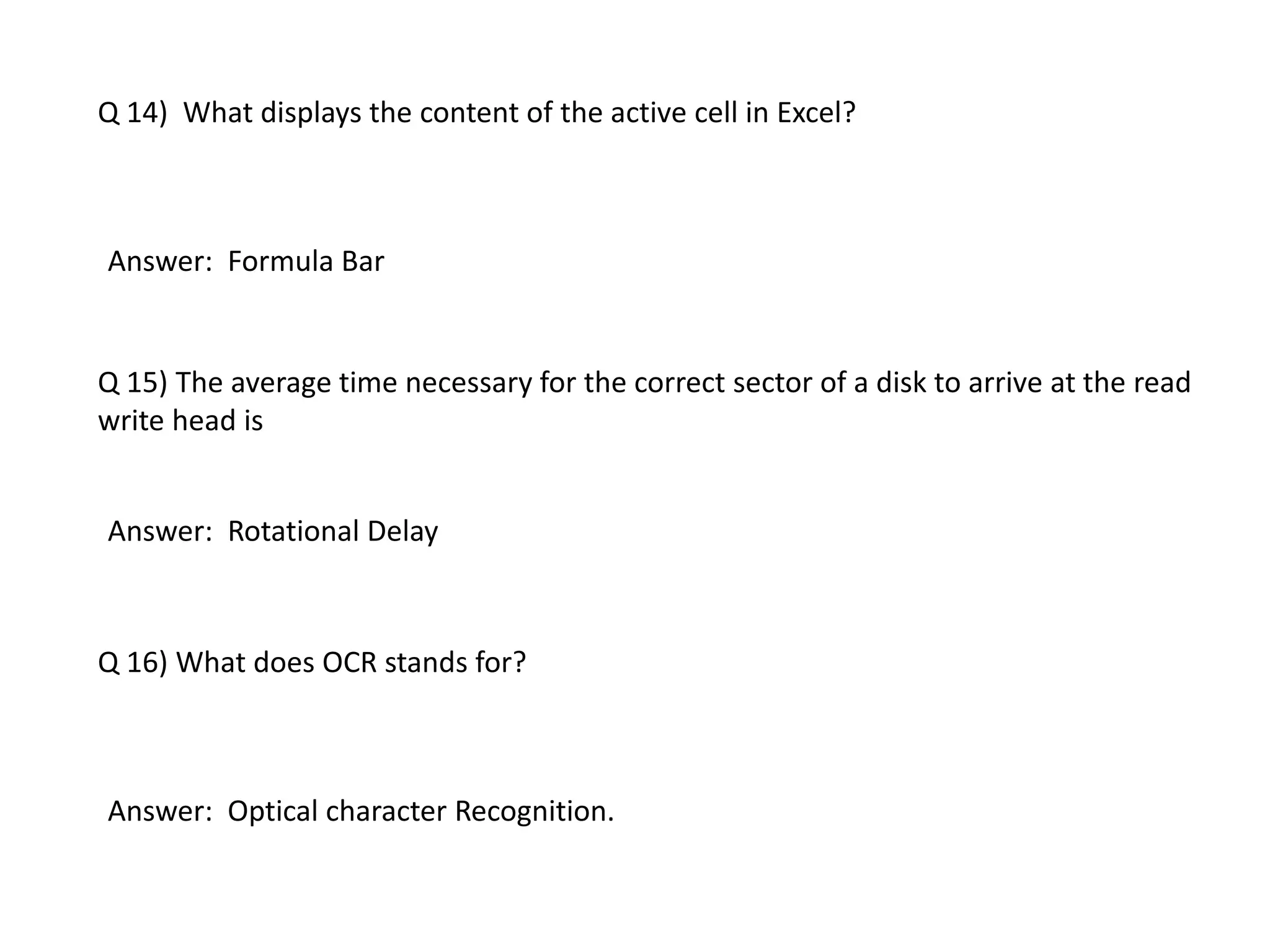
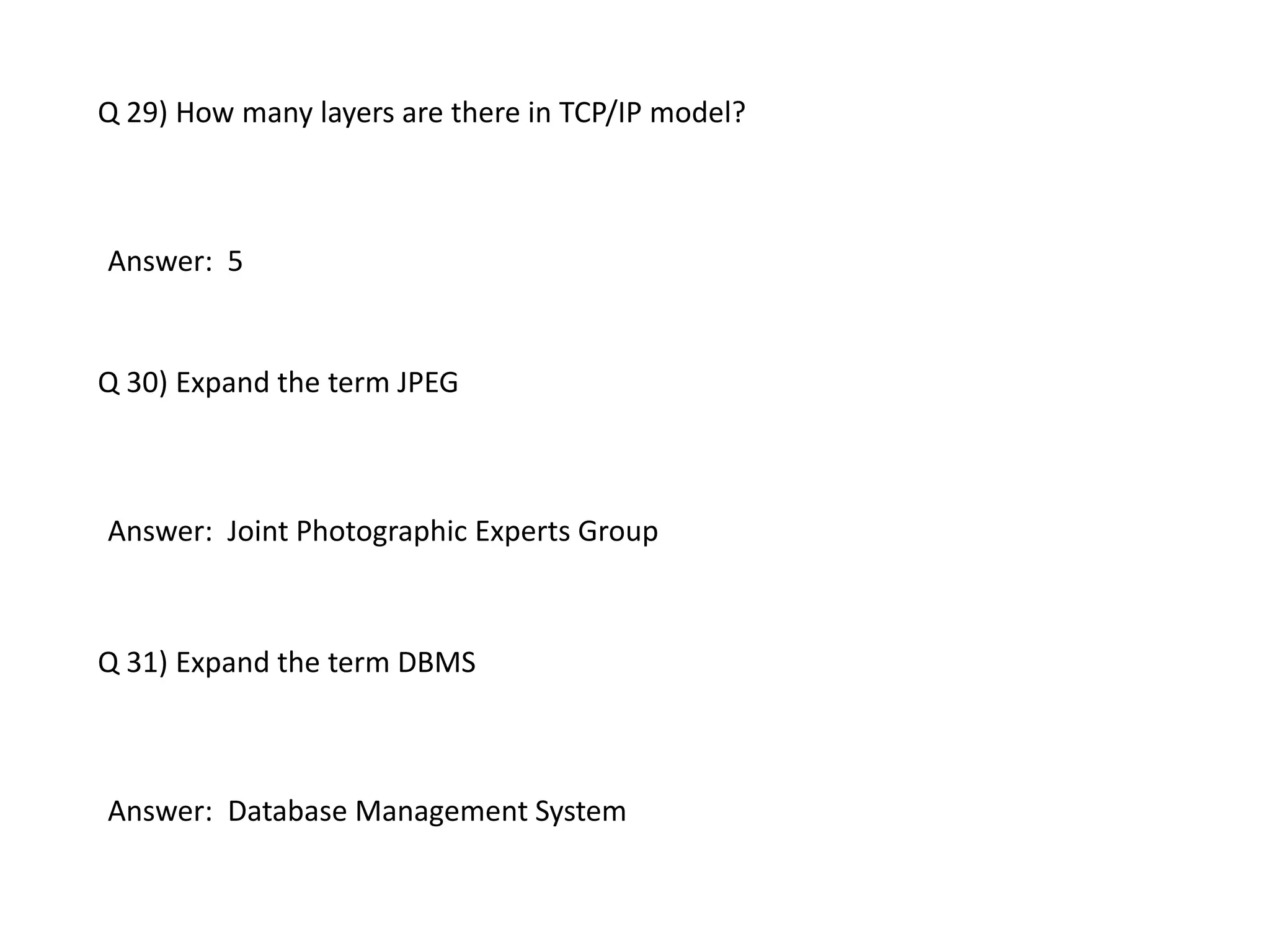
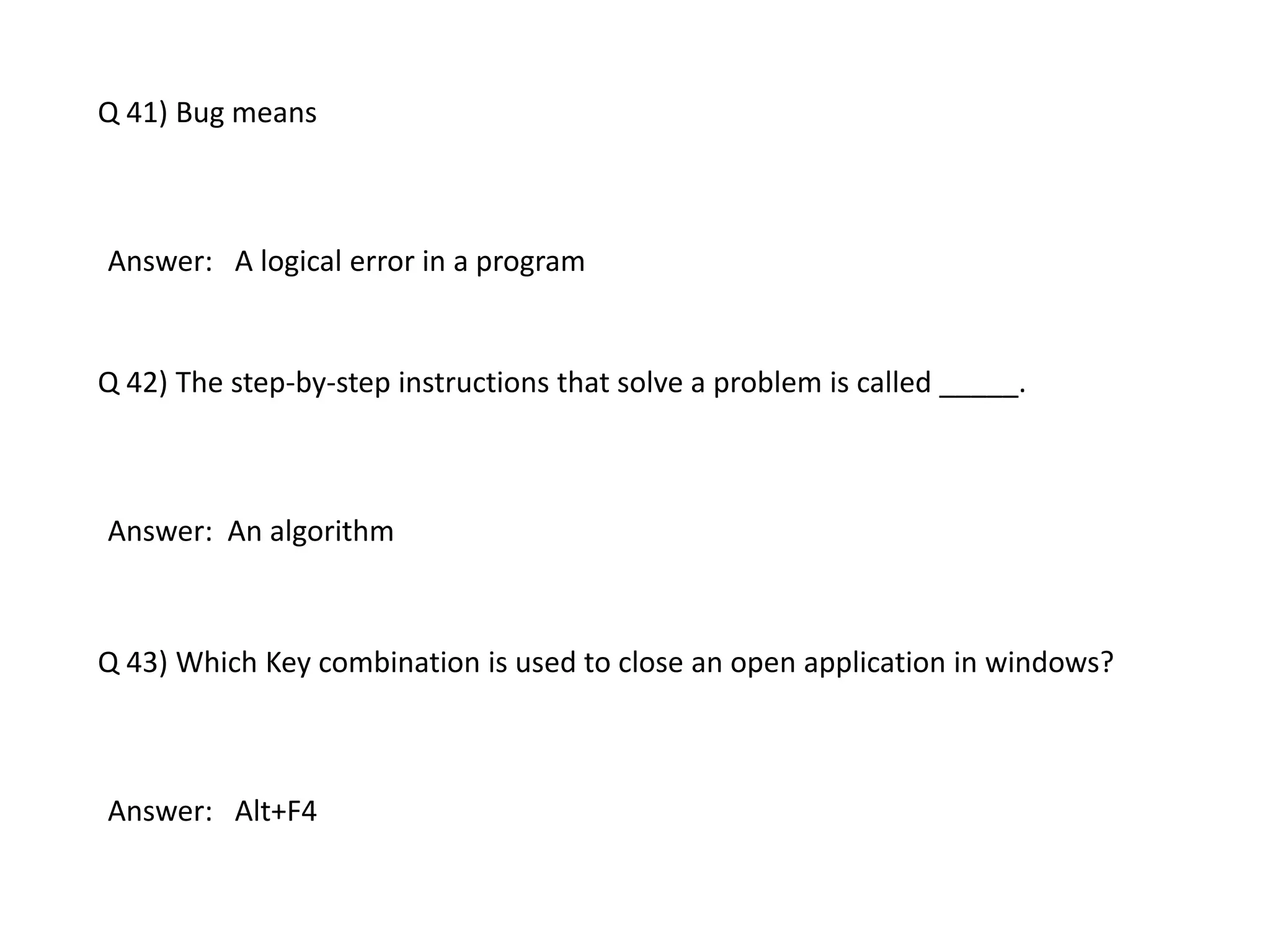
![Q7) What is the output of below code snippet in JAVA?
char word[]={'a','b','c','d','e'};
for(int i =0; i<4; i+=2)
System.out.println(word[i]);
(a) ace
(b) ac
(c) ab
(d) abe
Answer: b](https://image.slidesharecdn.com/technicalquiz1-160131060143/75/Computer-ScienceTechnical-quiz-9-2048.jpg)
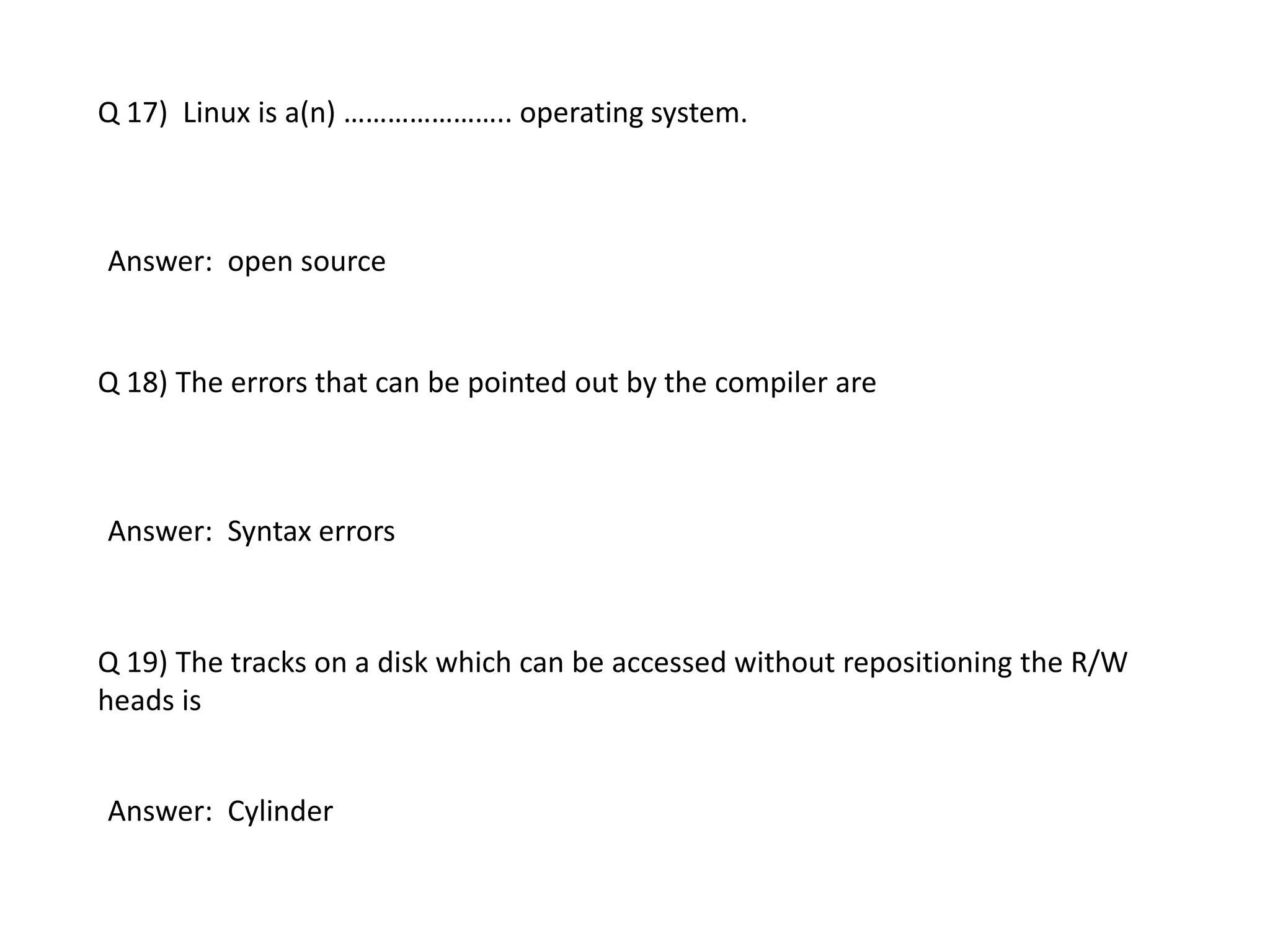
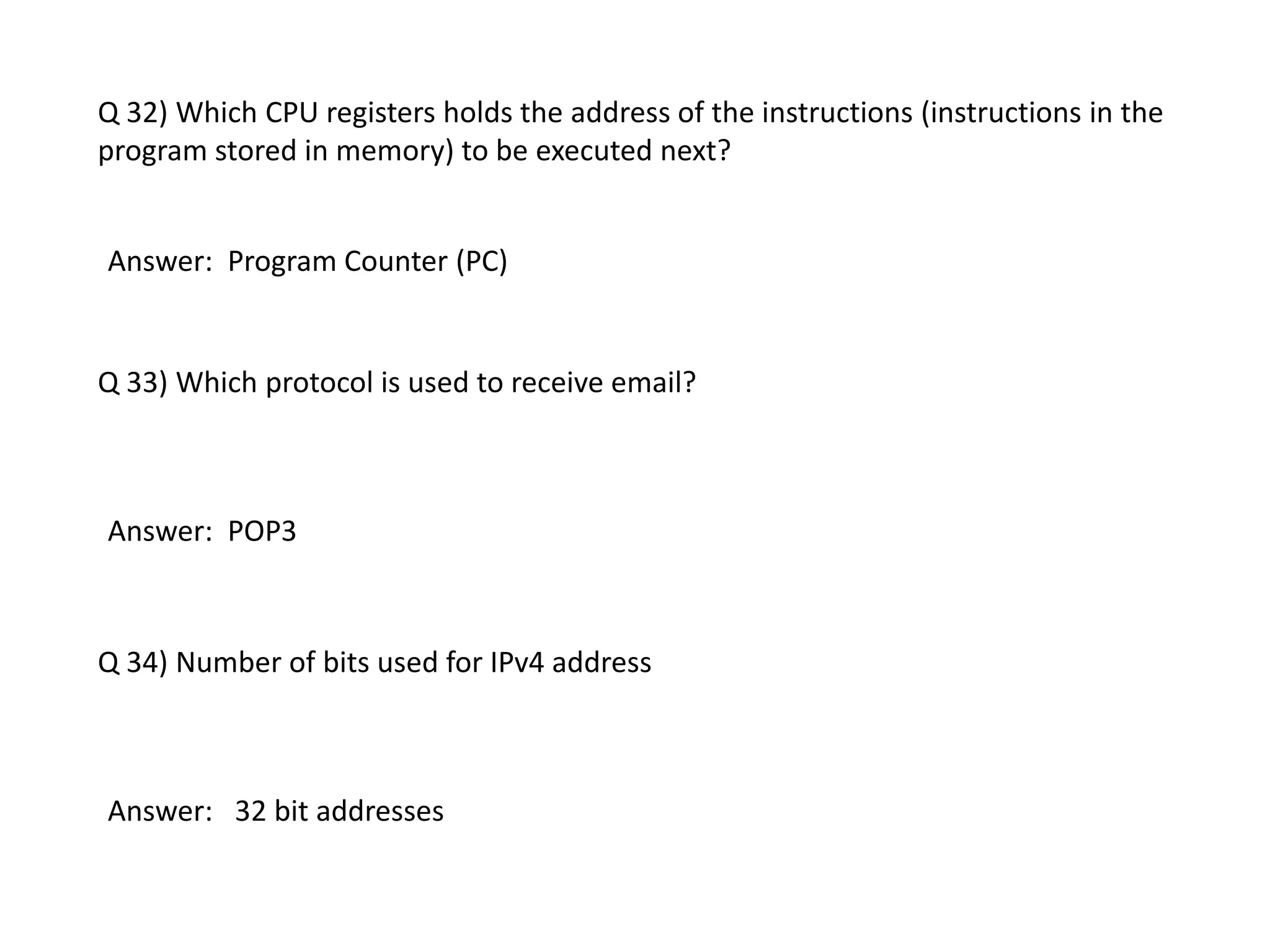
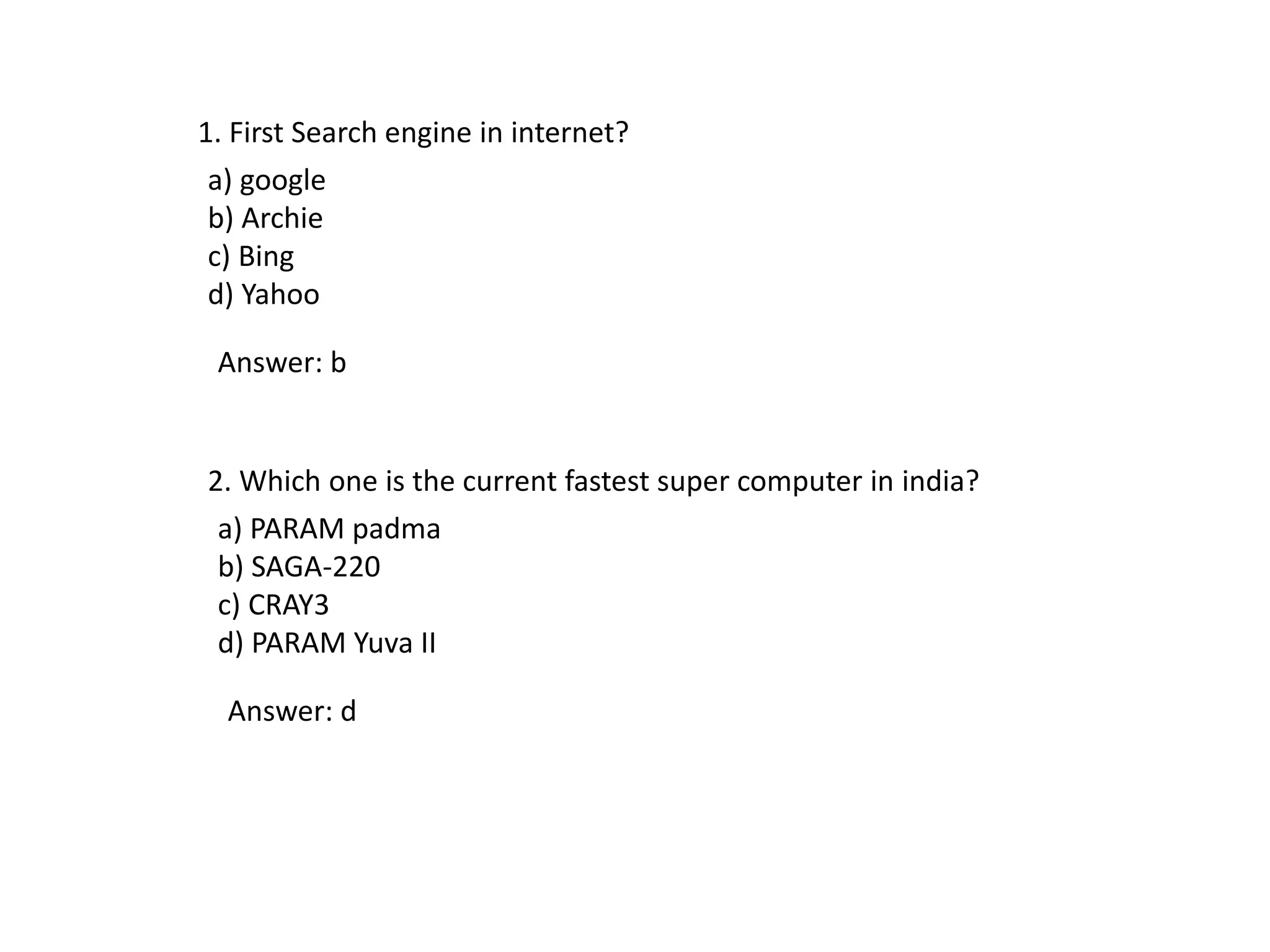
![Q8) What is the output of below code snippet in JAVA?
public static void main(String args[])
{
System.out.println(this);
}
(a) 0
(b) 1
(c) compiler error
(d) Garbage Value
Answer: c](https://image.slidesharecdn.com/technicalquiz1-160131060143/75/Computer-ScienceTechnical-quiz-10-2048.jpg)