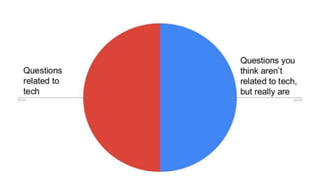
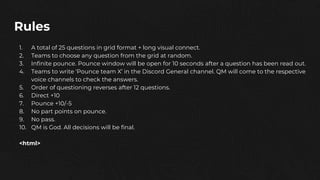
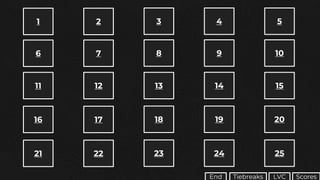
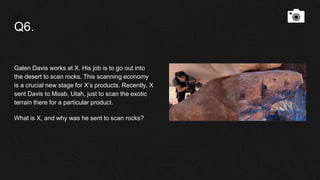
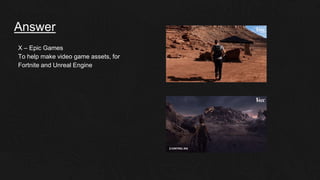
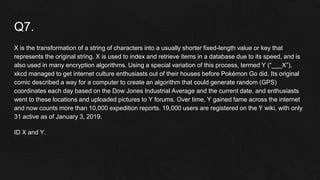
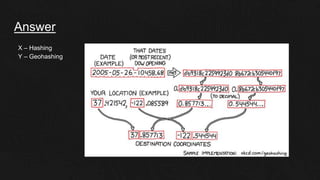
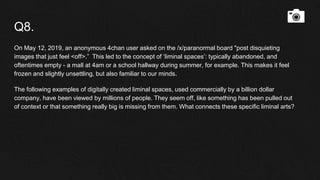
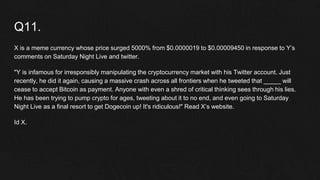
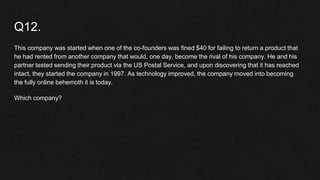
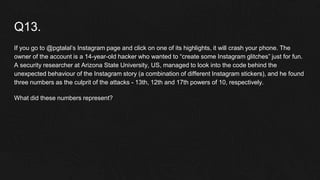
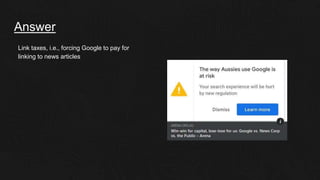
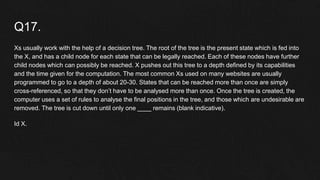
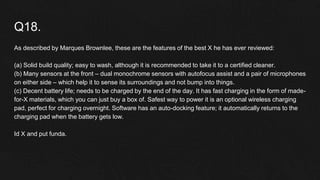
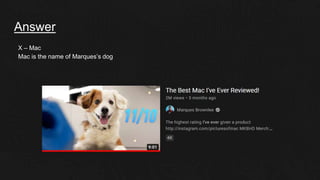
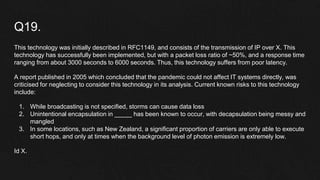
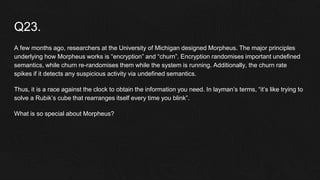
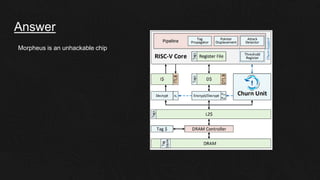
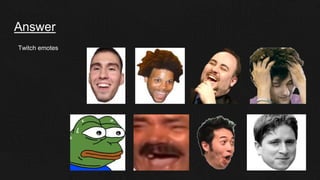
The document provides rules for the AlphaBit'21 Q?Bit finals trivia competition. It consists of 25 questions in a grid format, plus a long visual connect question. Teams can choose any question and have 10 seconds to "pounce" or attempt to answer before the other team. The order of questioning reverses after 12 questions. Correct answers receive +10 points, while incorrect pounce answers receive -5 points. There is no passing or part points for pounces. The question master's decisions are final. It also lists categories for a long visual connect and tiebreaker questions.