Computer forensics [pdf library]
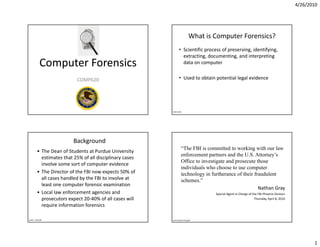
- 1. 4/26/2010 What is Computer Forensics? • Scientific process of preserving, identifying, extracting, documenting, and interpreting t ti d ti di t ti Computer Forensics data on computer COMP620 • Used to obtain potential legal evidence Sara Jones Background “The FBI is committed to working with our law • The Dean of Students at Purdue University enforcement partners and the U.S. Attorney’s estimates that 25% of all disciplinary cases Office to investigate and prosecute those involve some sort of computer evidence i l f id individuals who choose to use computer • The Director of the FBI now expects 50% of technology in furtherance of their fraudulent all cases handled by the FBI to involve at schemes.” least one computer forensic examination Nathan Gray • Local law enforcement agencies and Local law enforcement agencies and Special Agent in Charge of the FBI‐Phoenix Division prosecutors expect 20‐40% of all cases will Thursday, April 8, 2010 require information forensics Scott L. Ksander www.cybercrime.gov 1
- 2. 4/26/2010 Computers in Crime Computers Role in Crime • Computer as Target of the incident • A computer can hold data of a crime – Get to instructor’s test preparation – Access someone else’s homework – child pornography child pornography – Access/Change a grade • The computer could be stolen property – Access financial information – “Denial of Service” • The computer could hold evidence of a crime • Computer as Tool of the incident – spreadsheet of drug transactions – Word processing used to create plagiarized work – E‐mail sent as threat or harassment • A computer can be the instrument of a crime A computer can be the instrument of a crime – Printing used to create counterfeit material Printing used to create counterfeit material – hacking • Computer as Incidental to the incident – E‐mail/file access used to establish date/timelines – distribute copyrighted videos – Stored names and addresses of contacts or others potentially involved in the incident www.cybercrime.gov Scott L. Ksander Forensic Use Law Enforcement Computer forensics is used for • Computer forensics is often used to gather • L Law enforcement f evidence to prosecute a crime id t t i • Enforce employee policies • Computer forensics professionals must be • To gather evidence against an employee that careful to follow the legal requirements for an organization wishes to terminate handling evidence • R Recover data in the event of a hardware or d t i th t f h d • The evidence can be dismissed if it cannot be The evidence can be dismissed if it cannot be software failure shown that it was not tampered, either accidently or intentionally • Understand how a system works Wikipedia 2
- 3. 4/26/2010 Preparing an Investigation Preparing an Investigation (continued) • Role of computer forensics professional: • Follow an accepted procedure to prepare a case gather evidence to prove a suspect committed th id t t itt d • The U S Department of Justice has a document The U.S. Department of Justice has a document a crime or violated a company policy you can download that reviews proper • Collect evidence that can be offered in court acquisition of electronic evidence or at a corporate inquiry http://www.cybercrime.gov/ssmanual/index.html – Investigate the suspect’s computer Investigate the suspect s computer • Chain of custody Chain of custody – Preserve the evidence on a different computer – Route the evidence takes from the time you find it until the case is closed or goes to court Guide to Computer Forensics and Investigations, 2e Guide to Computer Forensics and Investigations, 2e Chain of Custody The Process • Protects integrity of the evidence • The primary activities of a computer forensics • Effective process of documenting the specialist are investigative in nature. complete journey of the evidence during the • Th i The investigative process encompasses ti ti life of the case – Identification • Allows you to answer the following questions: – Preservation – Who collected it? – Collection – Examination – How & where? How & where? – Analysis – Who took possession of it? – Presentation – How was it stored & protected in storage? – Decision – Who took it out of storage & why? Scott L. Ksander Scott L. Ksander 3
- 4. 4/26/2010 Computer Forensic Activities The 3 As Activities commonly include: The basic methodology consists of the 3 As: • the secure collection of computer data p • the identification of suspect data • the examination of suspect data to determine • Acquire the evidence without altering or details such as origin and content damaging the original • the presentation of computer‐based • Authenticate the image information information • Analyze the data without modifying it • the application of a country's laws to computer practice Scott L. Ksander Scott L. Ksander General Types of Digital Forensics 5 Rules of Evidence • Network Analysis • Admissible – Communication analysis – Log analysis – Must be able to be used in court or elsewhere – Path tracing • Authentic • Media Analysis – Disk imaging – Evidence relates to incident in relevant way – Content analysis • Complete (no tunnel vision) – Slack space analysis – Exculpatory evidence for alternative suspects – Steganography • Code Analysis Code Analysis • Reliable – Reverse engineering – No question about authenticity & veracity – Malicious code review • Believable – Exploit Review – Clear, easy to understand, and believable by a jury Scott L. Ksander Scott L. Ksander 4
- 5. 4/26/2010 General Evidence Dos & Don’ts Creating Disk Images 1. Minimize Handling/Corruption of Original Data • Care must be taken not to change the evidence. 2. Account for Any Changes and Keep Detailed Logs of Your Actions • Most media are “magnetic based” and the data is volatile: 3. Comply with the Five Rules of Evidence – Registers & Cache 4. Do Not Exceed Your Knowledge – Process tables, ARP Cache, Kernel stats 5. Follow Your Local Security Policy and Obtain Written Permission – Contents of system memory 6. Capture as Accurate an Image of the System as Possible – Temporary File systems 7. Be Prepared to Testify – Data on the disk 8. Ensure Your Actions are Repeatable • Examining a live file system changes the state of the evidence 9. Work Fast • The computer/media is the “crime scene” 10. Proceed From Volatile to Persistent Evidence • Protecting the crime scene is paramount as once evidence is 11. Don't Run Any Programs on the Affected System contaminated it cannot be decontaminated. 12. Document Document Document!!!! • Really only one chance to do it right! Scott L. Ksander Source: AusCERT 2003 (www.auscert.org) Scott L. Ksander Why Create a Duplicate Image? Bitstream vs. Backups • A file copy does not recover all data areas of • Forensic Copies (Bitstream) are bit for bit the device for examination copies capturing all the data on the copied media including hidden and residual data (e.g., media including hidden and residual data (e g • Working from a duplicate image free space, swap, residue, deleted files etc.) – Preserves the original evidence • Often the “smoking gun” is found in the – Prevents inadvertent alteration of original residual data. evidence during examination • Logical vs. physical image – Allows recreation of the duplicate image if Allows recreation of the duplicate image if necessary Scott L. Ksander Scott L. Ksander 5
- 6. 4/26/2010 Make Two Copies Computer Forensics Certification • Make 2 copies of the original media – 1 copy becomes the working copy – 1 copy is a library/control copy py y py There are several professional groups and – Verify the integrity of the copies to the original companies that offer forensic certification i th t ff f i tifi ti • The working copy is used for the analysis • International Association of Computer • The library copy is stored for disclosure purposes or in Investigative Specialist (IACIS) offers the the event that the working copy becomes corrupted • If performing a drive to drive imaging (not an image Certified Electronic Evidence Collection file) use clean media to copy to file) use clean media to copy to p ( ) Specialist Certification (CEECS) and Certified – Shrink wrapped new drives Forensic Computer examiner (CFCE) – Next best, zero another drive • Global Information Assurance Certification Certified Forensic Analyst Scott L. Ksander References • Scott L. Ksander, “Computer Forensics in the Campus Environment , Environment”, www.purdue.edu/securepurdue/docs/ComputerForensics.ppt • Thomas Course Technology, “Guide to Computer Forensics and Investigations, 2e”, euclid.barry.edu/~zuniga/courses/cs300/ch02.ppt • Sara Jones, “Computer Forensics”, www.middlesexcc.edu/faculty/Steven.../Computer_%20Forensics.ppt • www.cybercrime.gov 6