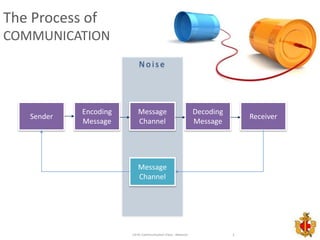
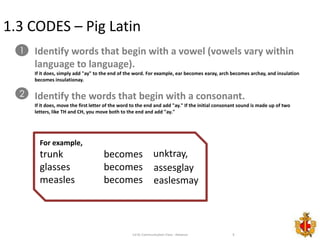
The document discusses various methods of encoding and concealing messages, including codes, ciphers, and space codes. It describes book codes, Pig Latin, Turkish Irish codes, Caesar and keyboard ciphers, date shift ciphers, combining multiple ciphers, and techniques for concealing messages by rearranging spaces. The goal is to teach effective yet difficult to break communication methods.