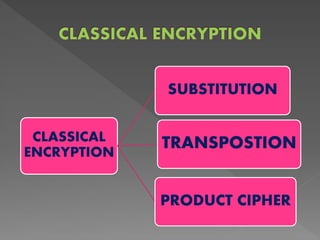
1. There are two basic building blocks of encryption techniques: substitution and transposition.
2. Substitution involves replacing plaintext symbols like letters, numbers or bits with ciphertext symbols. Transposition rearranges the order of letters in the plaintext without changing them.
3. A product cipher combines both substitution and transposition ciphers, subjecting the output of one cipher to another encryption for greater security.