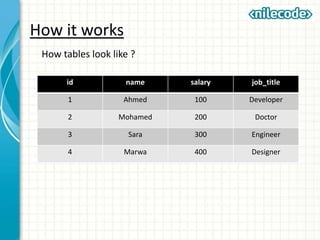
The document provides an outline of key concepts for database programming with MySQL. It discusses MySQL data types, the data definition language (DDL) for defining databases and tables, the data manipulation language (DML) for querying and manipulating data using SQL statements like SELECT, INSERT, UPDATE, DELETE. It also covers MySQL clauses like WHERE, ORDER BY, LIMIT, and joins for retrieving data from multiple tables. The document demonstrates how to connect to and query a MySQL database using PHP with examples of prepared statements. It proposes a course project and assignment to apply the concepts by building a basic application.


![Data Types
Size Name Range Example
1 TINYINT
-128 TO 127
[0 to 255 if UNSIGNED]
10
2 SMALLINT
-32,768 to 32,767
[0 to 65,535]
30000
3 MEDIUMINT
-8,388,608 to 8,388,607
[0 to 16,777,215]
8000000
4 INT
-/+2.147E+9
[0 to 4.294E+9]
80000000
8 BIGINT
-/+9.223E+18
[0 to 18.45E+18]
80000000000
4 FLOAT p=0-24 4.333333
8 DOUBLE
Min=+/-2.225E-308
Max=+/-1.798E+308
.000000000000000000
003
arbitrary
DECIMAL[(M,[D])]
Stored as string
Max Range = DOUBLE range33333.4444
M CHAR(M)
M=0-255 Characters, FIXED.
Right padded with spaces.
Hello There
M VARCHAR(M)
M=0-65,535 Characters
M=0-255 <v5.0.3
Hello There](https://image.slidesharecdn.com/class8-databaseprogramming-150930071128-lva1-app6891/85/Class-8-Database-Programming-6-320.jpg)
![Data Types
Size Name Range Example
arbitrary TINYTEXT 0-255 Characters Hello There
arbitrary TEXT 0-65,535 Char's Hello There
arbitrary MEDIUMTEXT 0-16,777,215 Char's Hello There
arbitrary LONGTEXT 0-4,294,967,295 Char's Hello There
arbitrary BINARY[(M)] M=0-255 bytes, FIXED.
arbitrary VARBINARY(M)
0-65,535 bytes
M=0-255 <v5.0.3
arbitrary TINYBLOB 0-255 bytes
arbitrary BLOB 0-65,535 bytes
arbitrary MEDIUMBLOB 0-16,777,215 bytes
arbitrary LONGBLOB 0-4,294,967,295 bytes
3 DATE
"1000-01-01" - "9999-12-
31"
2010-01-01
8 DATETIME
"1000-01-01 00:00:00" -
"9999-12-31 23:59:59"
2010-01-01 10:12:01
3 TIME "-838:59:59" - "838:59:59" 10:12:01
4 TIMESTAMP
19700101000000 -
2037+
19700101000000](https://image.slidesharecdn.com/class8-databaseprogramming-150930071128-lva1-app6891/85/Class-8-Database-Programming-7-320.jpg)



















![Querying a database
Here we will need to display the last name of the people
with first_name = ‘Mohamed’.
<?php
$sql = "SELECT * FROM employees WHERE first_name =
'Mohamed'";
$result = $connection->query($sql);
foreach ($result as $row) {
print $row['last_name'] . "<br/>";
}
?>](https://image.slidesharecdn.com/class8-databaseprogramming-150930071128-lva1-app6891/85/Class-8-Database-Programming-27-320.jpg)




![Exercise Solution
The other script is called “add.php” which contains :
<?php
$dsn = 'mysql:dbname=testdb;host=127.0.0.1';
$user = 'dbuser';
$password = 'dbpass';
try {
$connection = new PDO($dsn, $user, $password);
$sql = "INSERT INTO employees SET first_name = '" . $connection->quote($_POST['first_name']) . "',
last_name = '" . $connection->quote($_POST['last_name']) . "', salary = " . $connection->quote($_POST['salary'])
. ", dateofbirth = '" . $connection->quote($_POST['dateofbirth']) . "'";
$connection->query($sql);
echo "Record has been added.";
} catch (PDOException $e) {
echo 'Connection failed: ' . $e->getMessage();
}
?>](https://image.slidesharecdn.com/class8-databaseprogramming-150930071128-lva1-app6891/85/Class-8-Database-Programming-32-320.jpg)



![Prepared statements
1- Question marks:
<?php
$connection = new PDO($dsn, $user, $password);
$sql = "INSERT INTO employees SET first_name = ? , last_name = ?, salary = ?,
dateofbirth = ?";
$sth = $connection->prepare($sql);
$sth->bindParam(1, $_POST['first_name']);
$sth->bindParam(2, $_POST['last_name']);
$sth->bindParam(3, $_POST['salary']);
$sth->bindParam(4, $_POST['dateofbirth']);
$sth->execute()
?>](https://image.slidesharecdn.com/class8-databaseprogramming-150930071128-lva1-app6891/85/Class-8-Database-Programming-36-320.jpg)
![Prepared statements
2-Named parameters:
<?php
$sql = "INSERT INTO employees SET first_name = :first_name , last_name =
:last_name, salary = :salary, dateofbirth = :dateofbirth";
$sth = $connection->prepare($sql);
$sth->bindParam(':first_name', $_POST['first_name']);
$sth->bindParam(':last_name', $_POST['last_name']);
$sth->bindParam(':salary', $_POST['salary']);
$sth->bindParam(':dateofbirth', $_POST['dateofbirth']);
$sth->execute();
?>](https://image.slidesharecdn.com/class8-databaseprogramming-150930071128-lva1-app6891/85/Class-8-Database-Programming-37-320.jpg)





