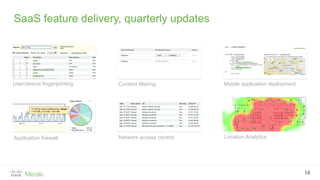
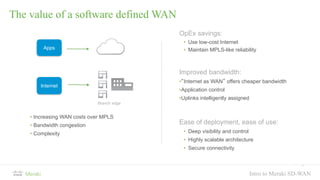
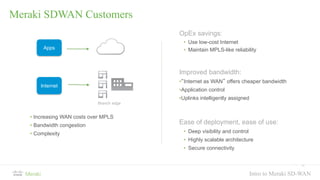
Cisco Meraki provides a complete cloud-managed networking solution including wireless, switching, security, communications, endpoint management, and security cameras. With over 140,000 customers and 2 million devices online, Meraki simplifies IT using an integrated hardware, software, and cloud services approach. The solution is managed through a centralized cloud-based dashboard that provides turnkey installation, management, security, and scalability benefits.