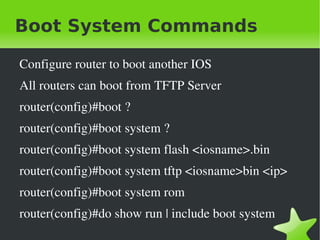
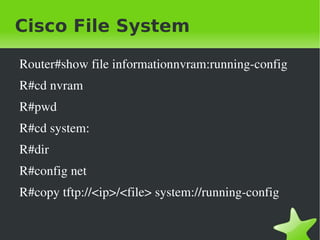
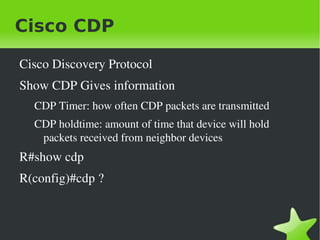
This document provides instructions and commands for booting, backing up, restoring, and upgrading Cisco IOS, managing the Cisco file system, backing up and restoring the router configuration, using Cisco Discovery Protocol to gather neighbor and interface information, using Telnet to connect to remote devices, troubleshooting network connectivity issues, and using debugging commands. It also discusses using host tables or DNS to resolve hostnames when connecting to devices.












![Build Host Table
Ip host <hostname> [tcpport#] <ipaddress>
Default Telnet Port is 23
R(config)#ip host R1 <ip>
R(config)#do show hosts
R#R1
Trying to connect to my telnet... WoW!](https://image.slidesharecdn.com/cisco-ios-cont-120412100527-phpapp01/85/Cisco-ios-cont-17-320.jpg)