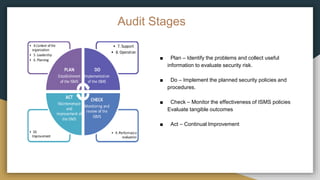
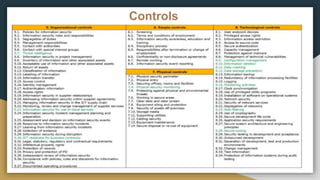
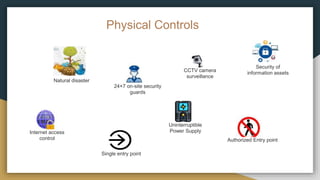
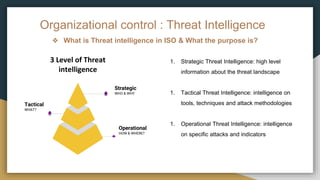
The document discusses ISO 27001 certification, which establishes requirements for an information security management system (ISMS). It outlines the various clauses of ISO 27001:2022 such as leadership, planning, support, operation, performance evaluation, and improvement. The presentation also covers topics like audit stages, organizational controls, physical controls, and the purpose of threat intelligence as it relates to ISO standards.