The document summarizes key concepts about the network layer:
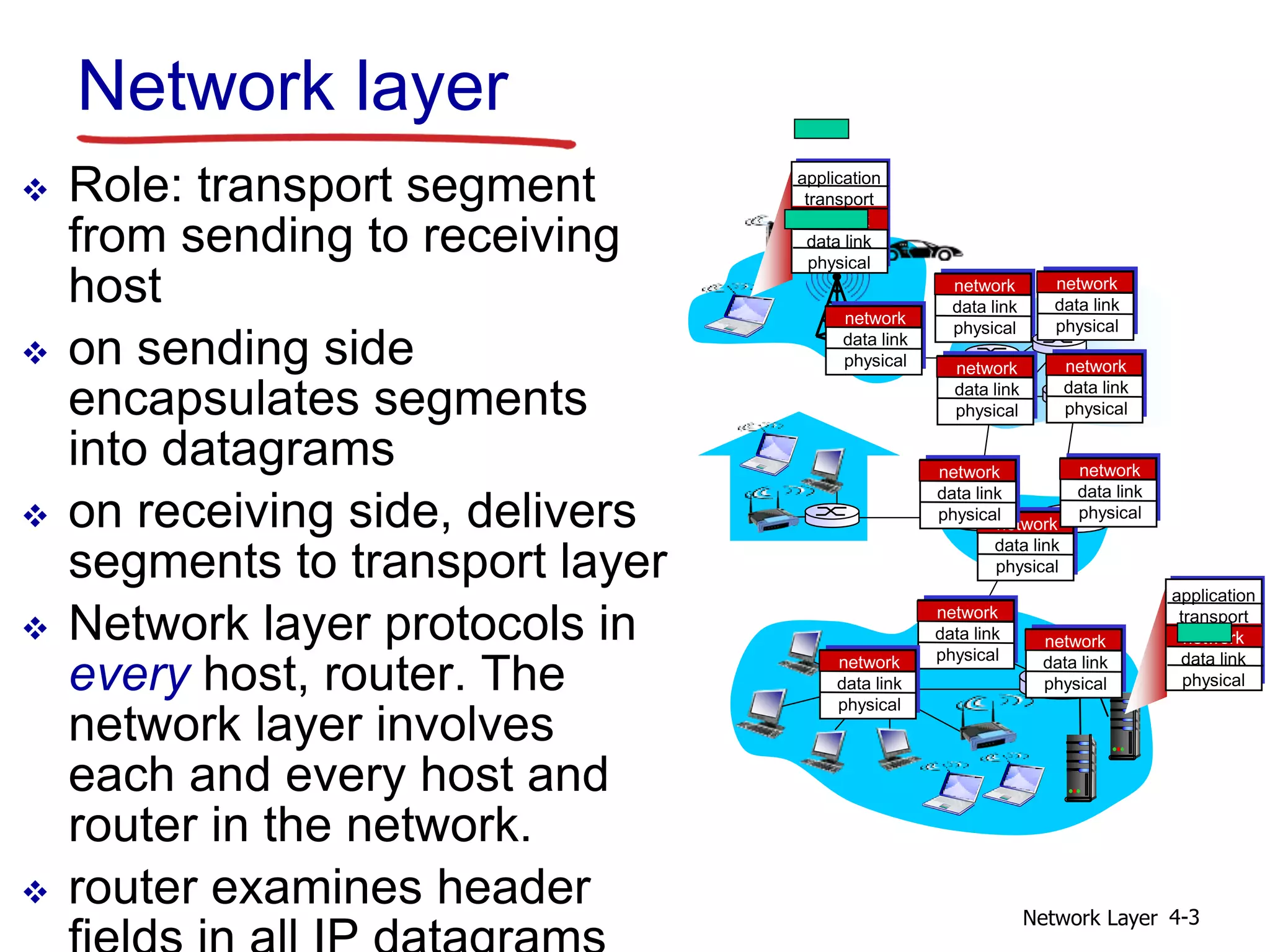
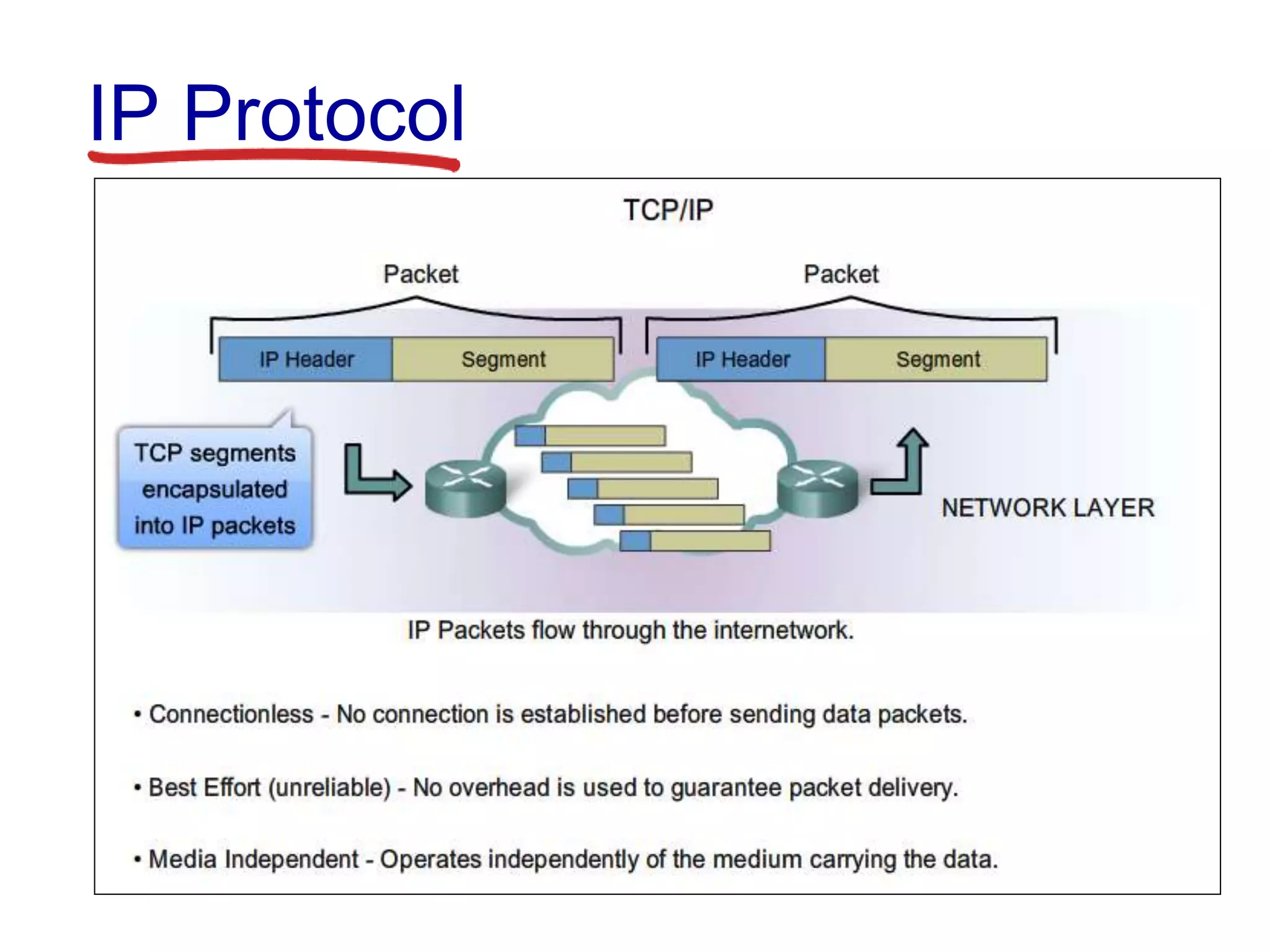
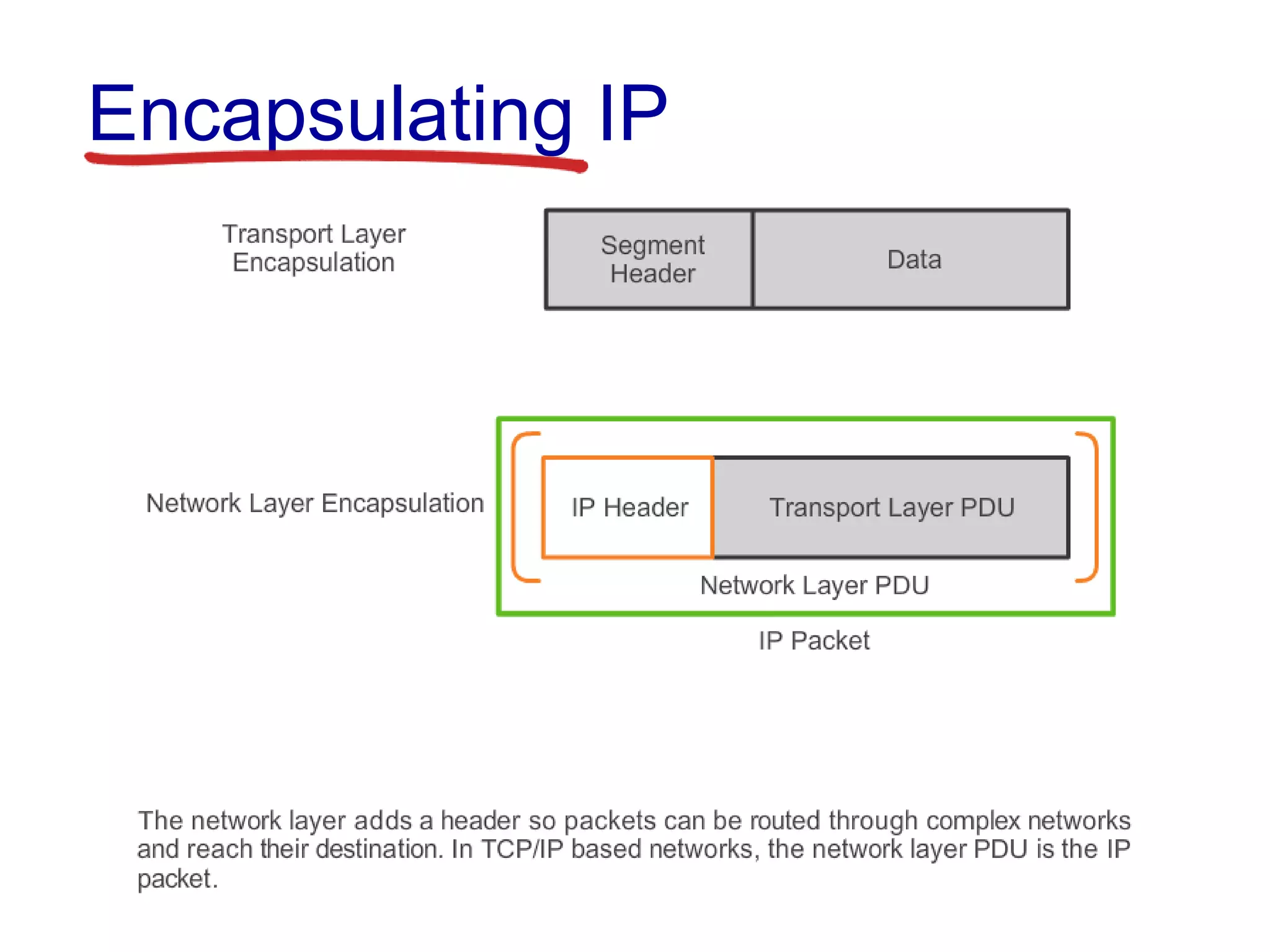
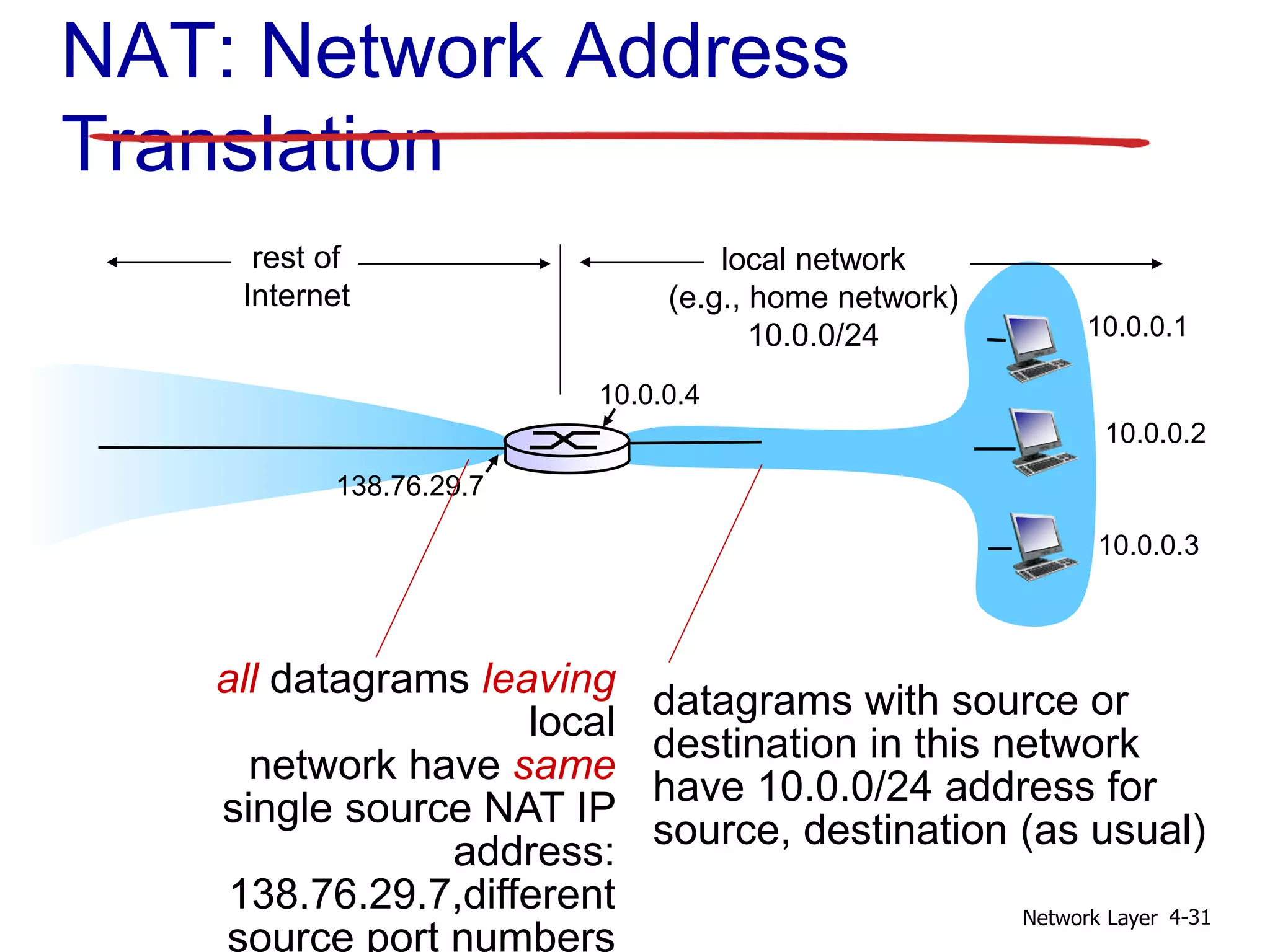
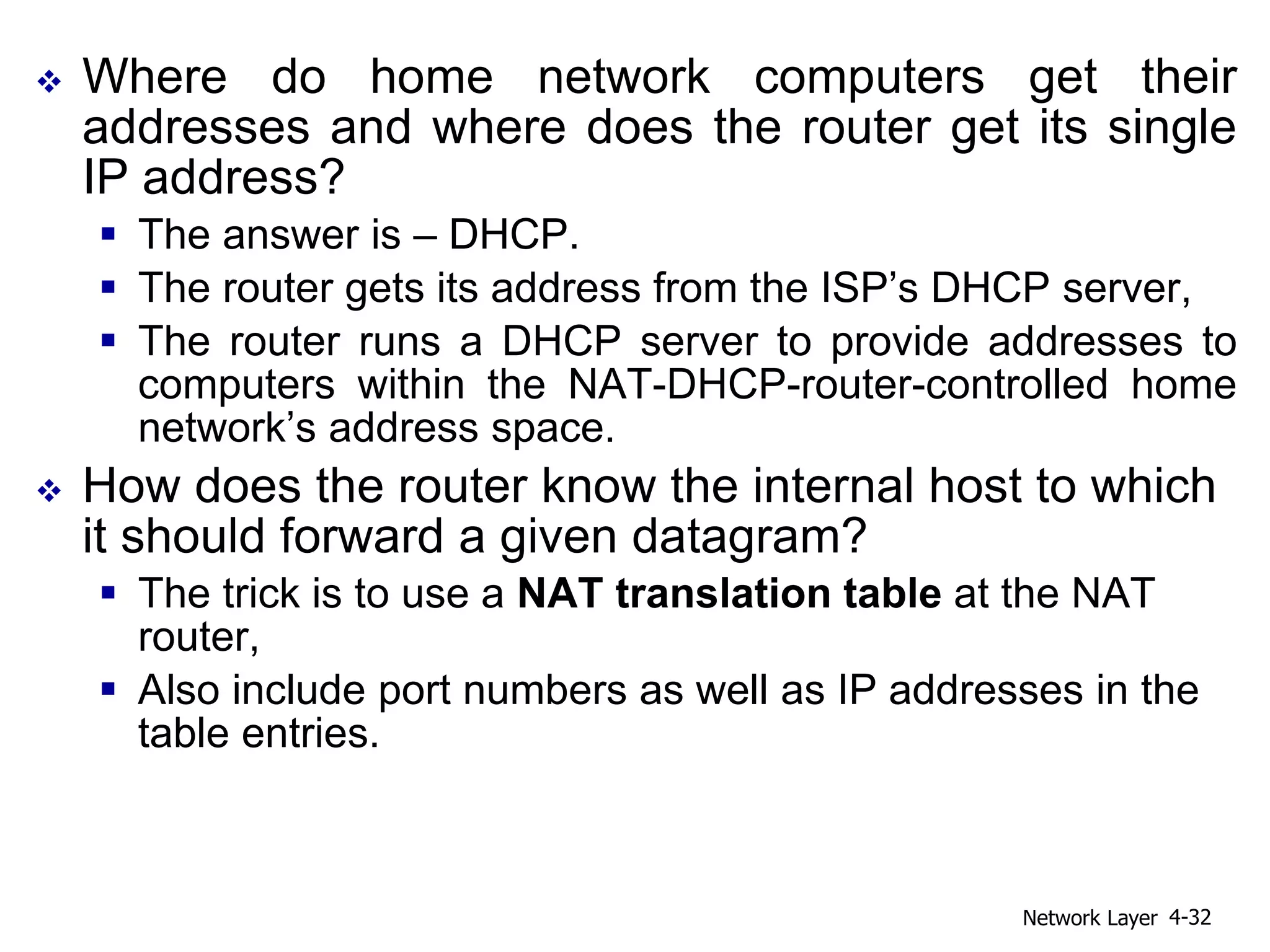
1) The network layer is responsible for transporting data segments from sending to receiving hosts by encapsulating segments into datagrams. Routers examine header fields to forward datagrams.
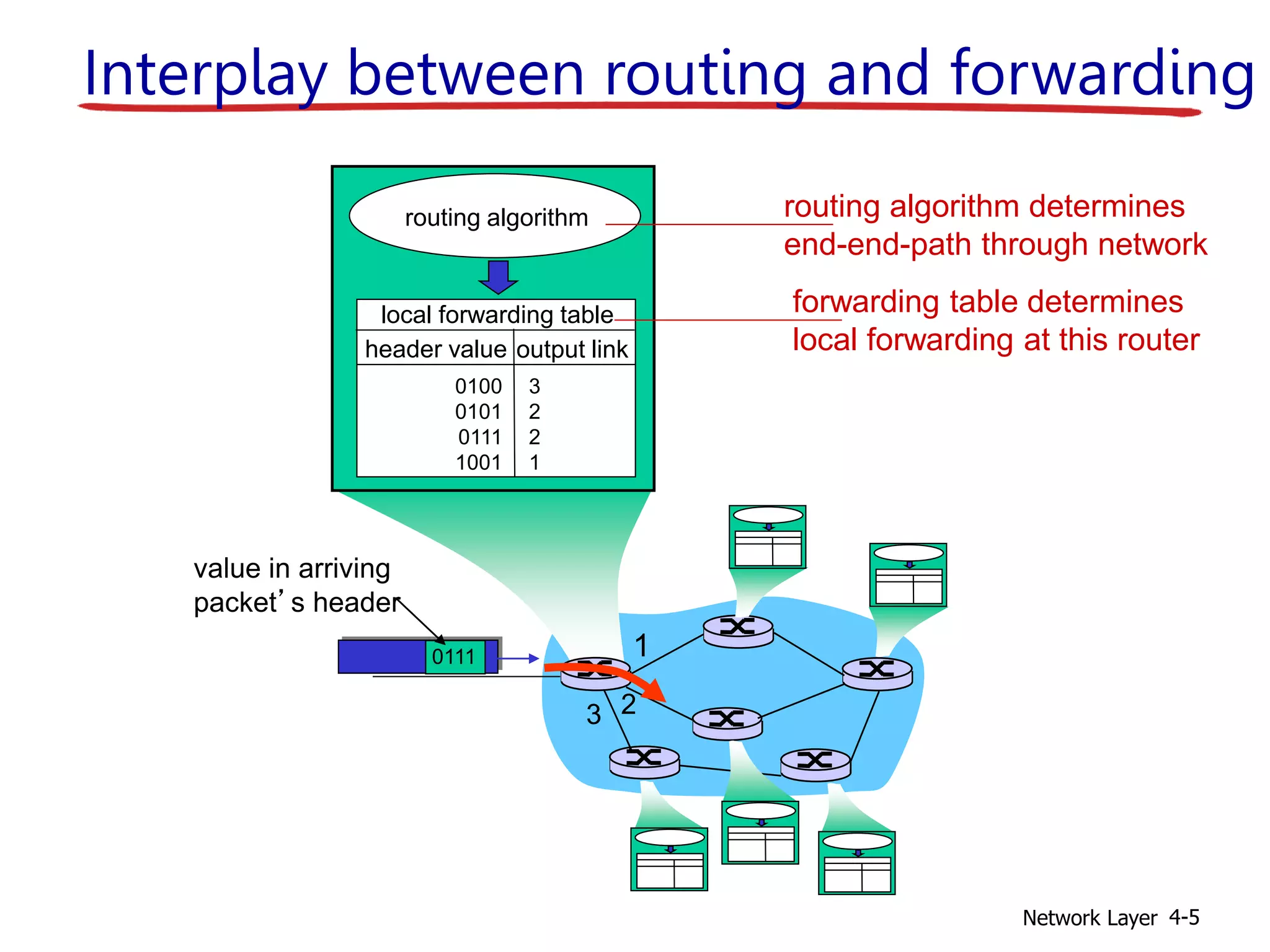
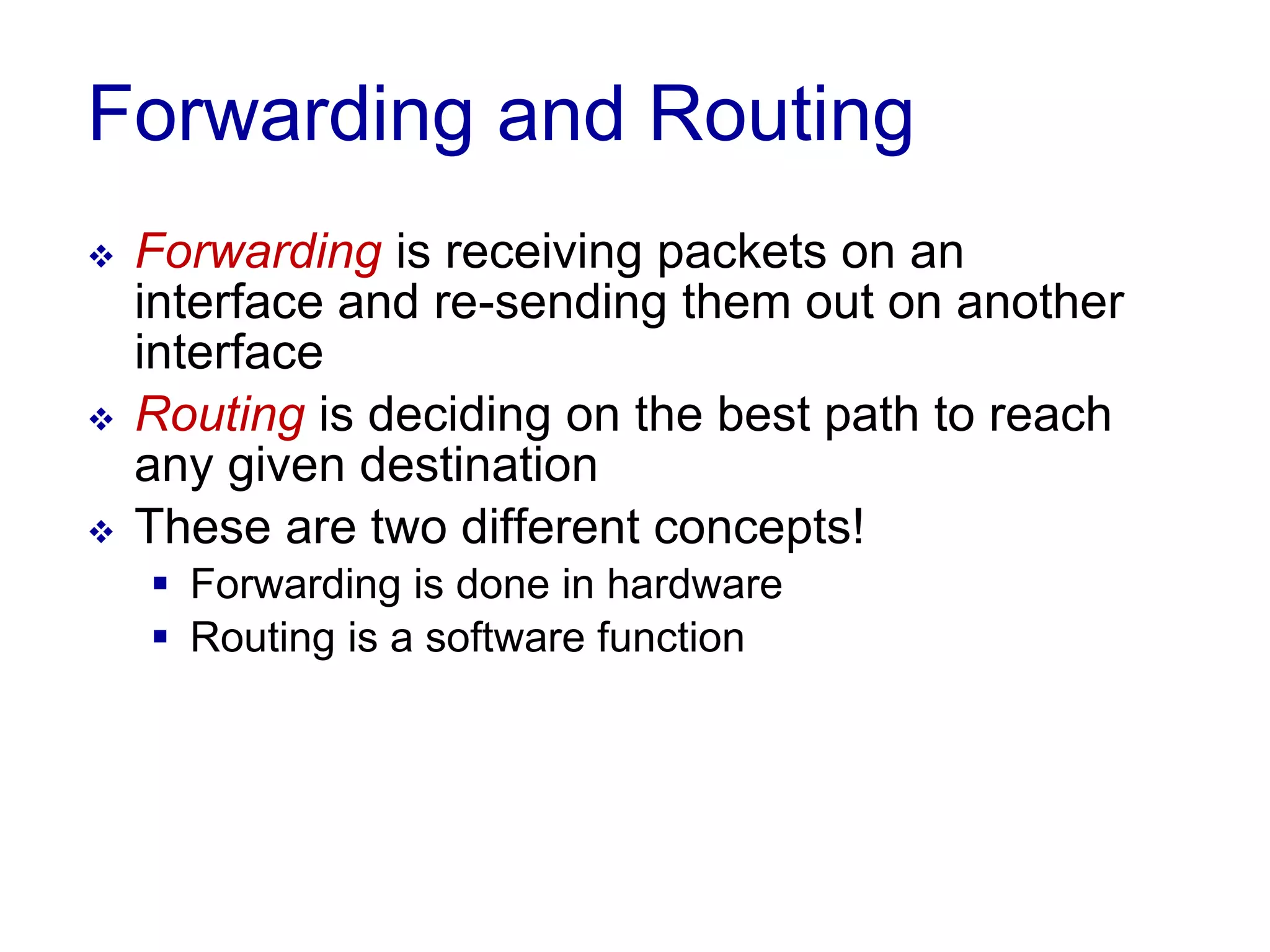
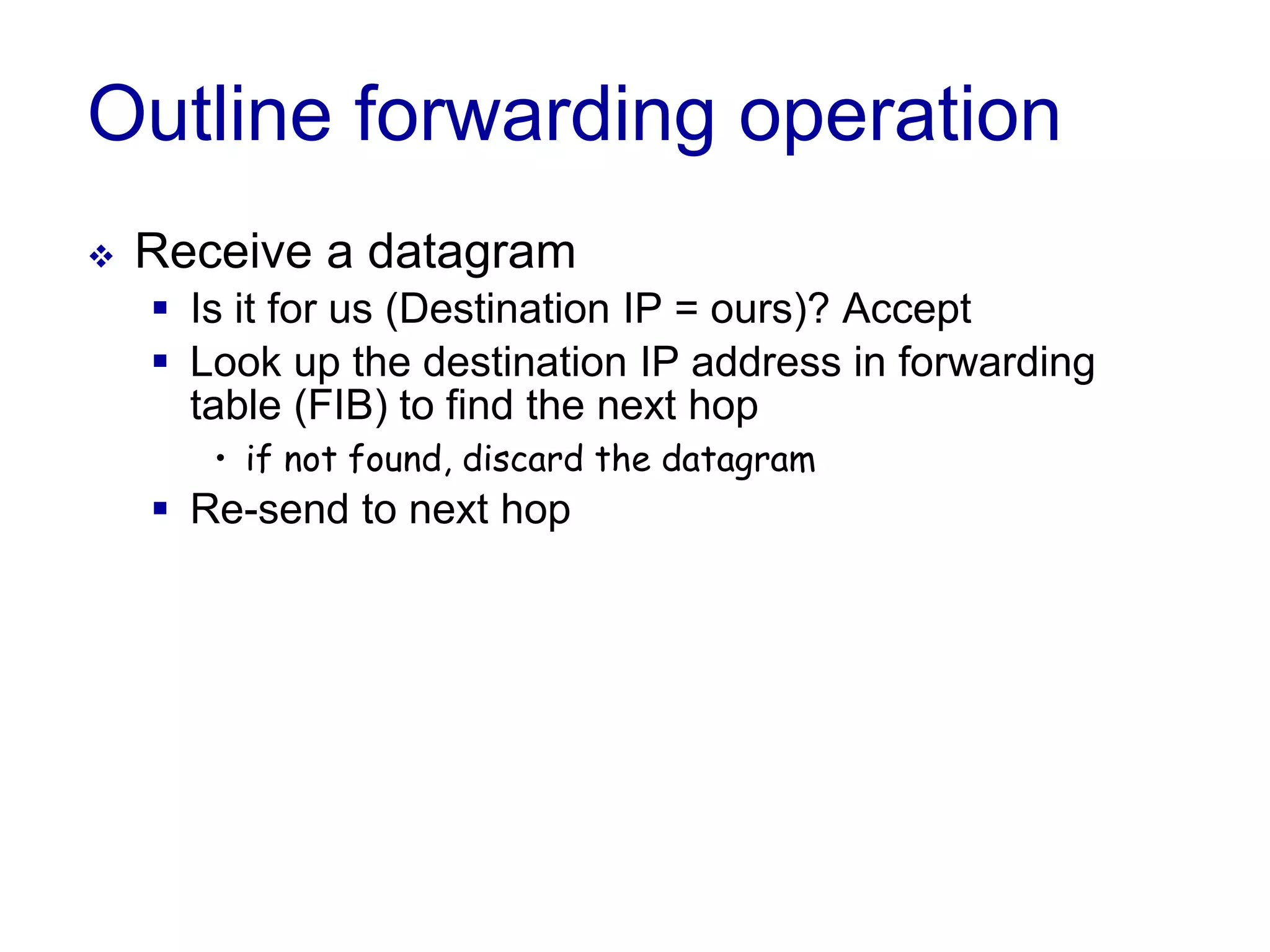
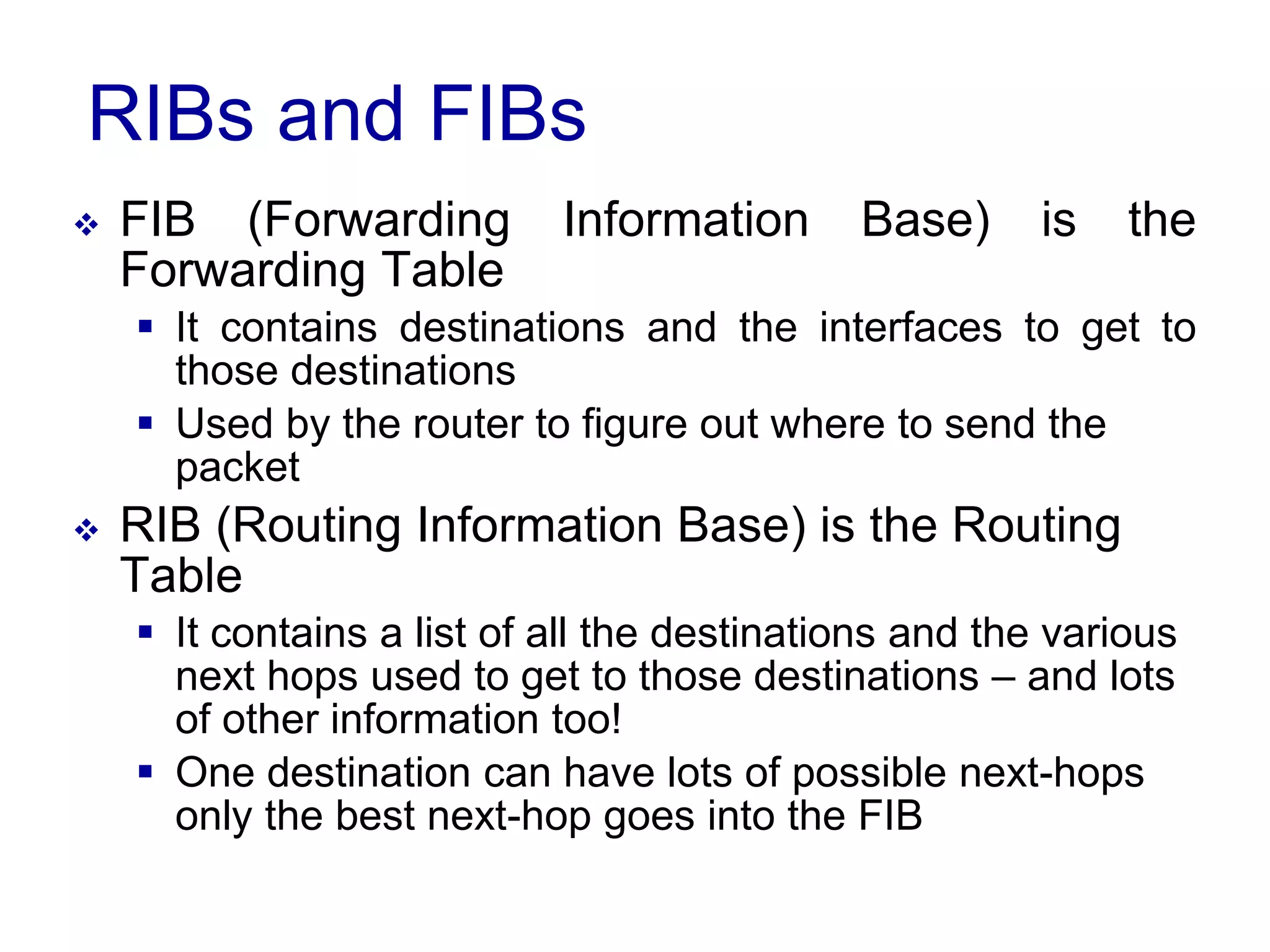
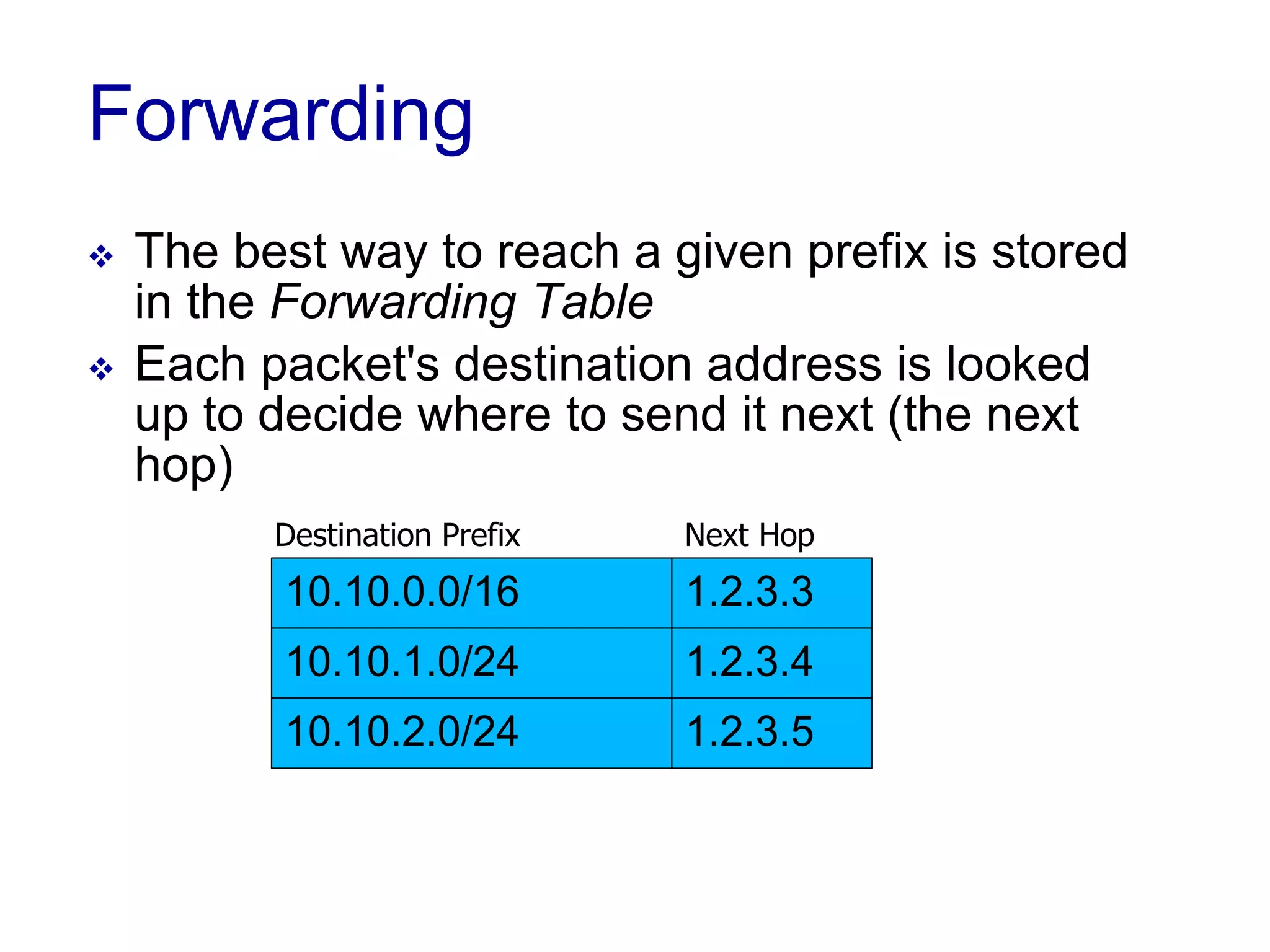
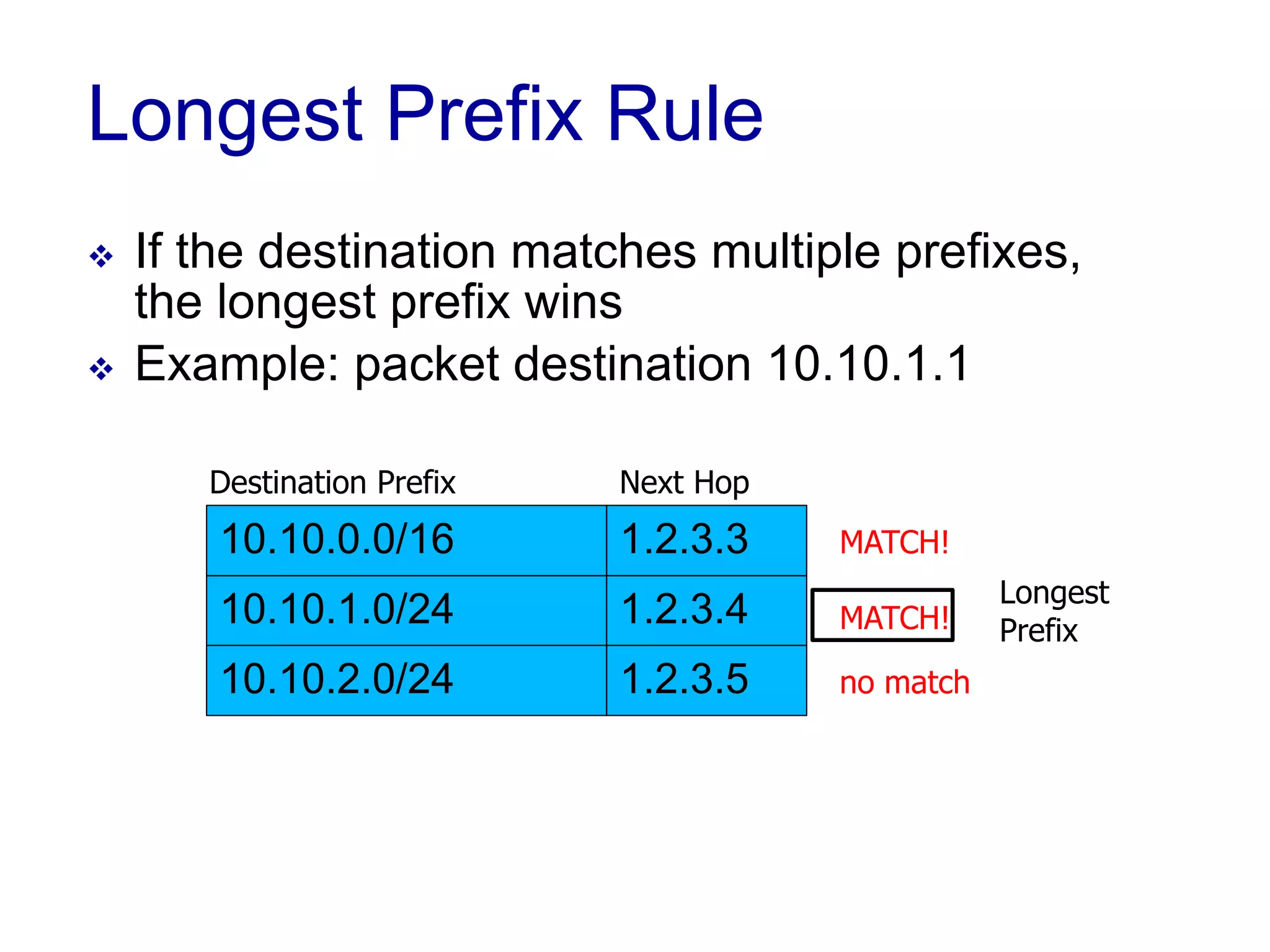
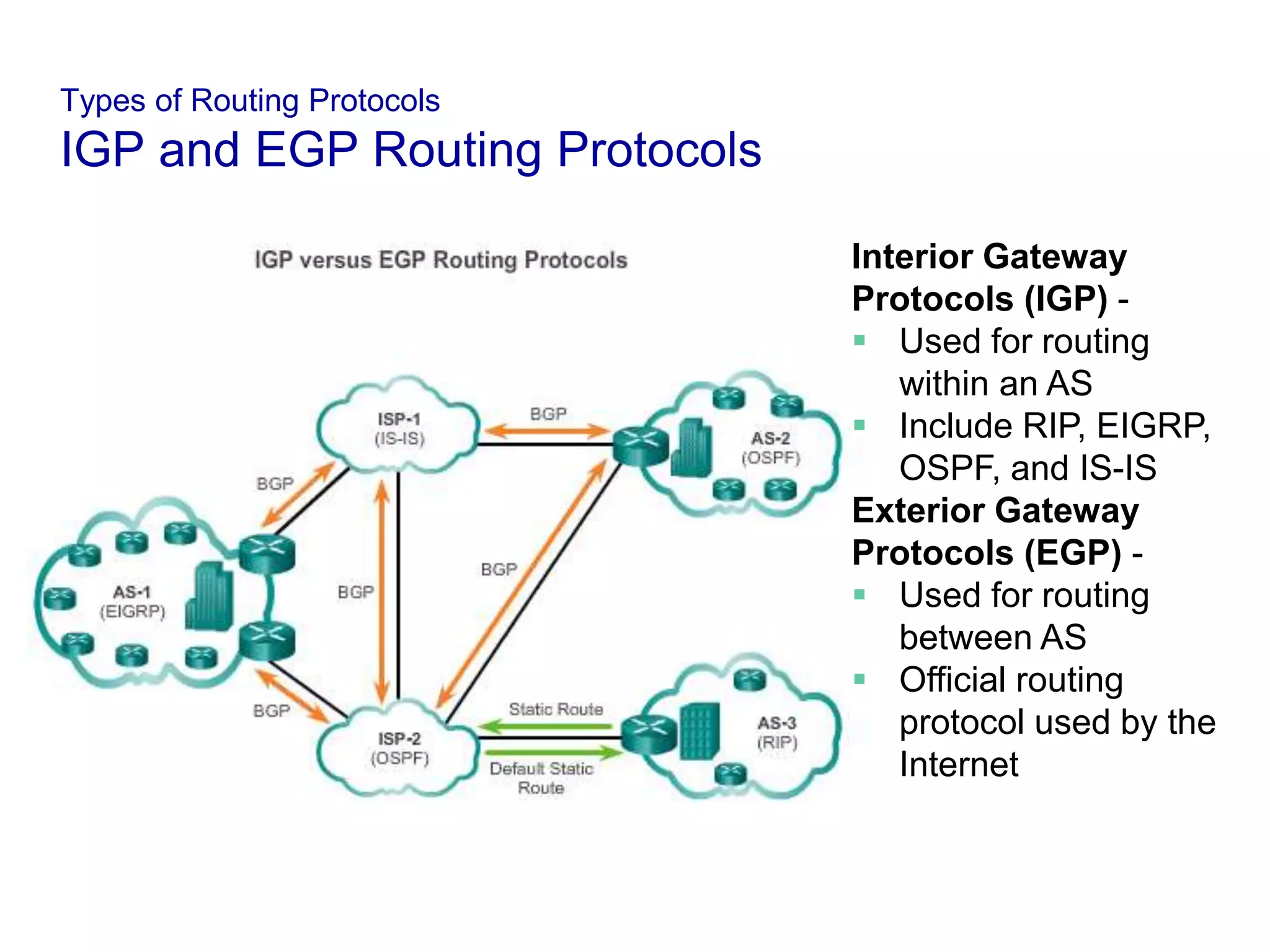
2) The network layer provides three key functions - forwarding, routing, and call setup. Forwarding moves packets through routers, routing determines the path between source and destination, and call setup establishes connections before data flows.
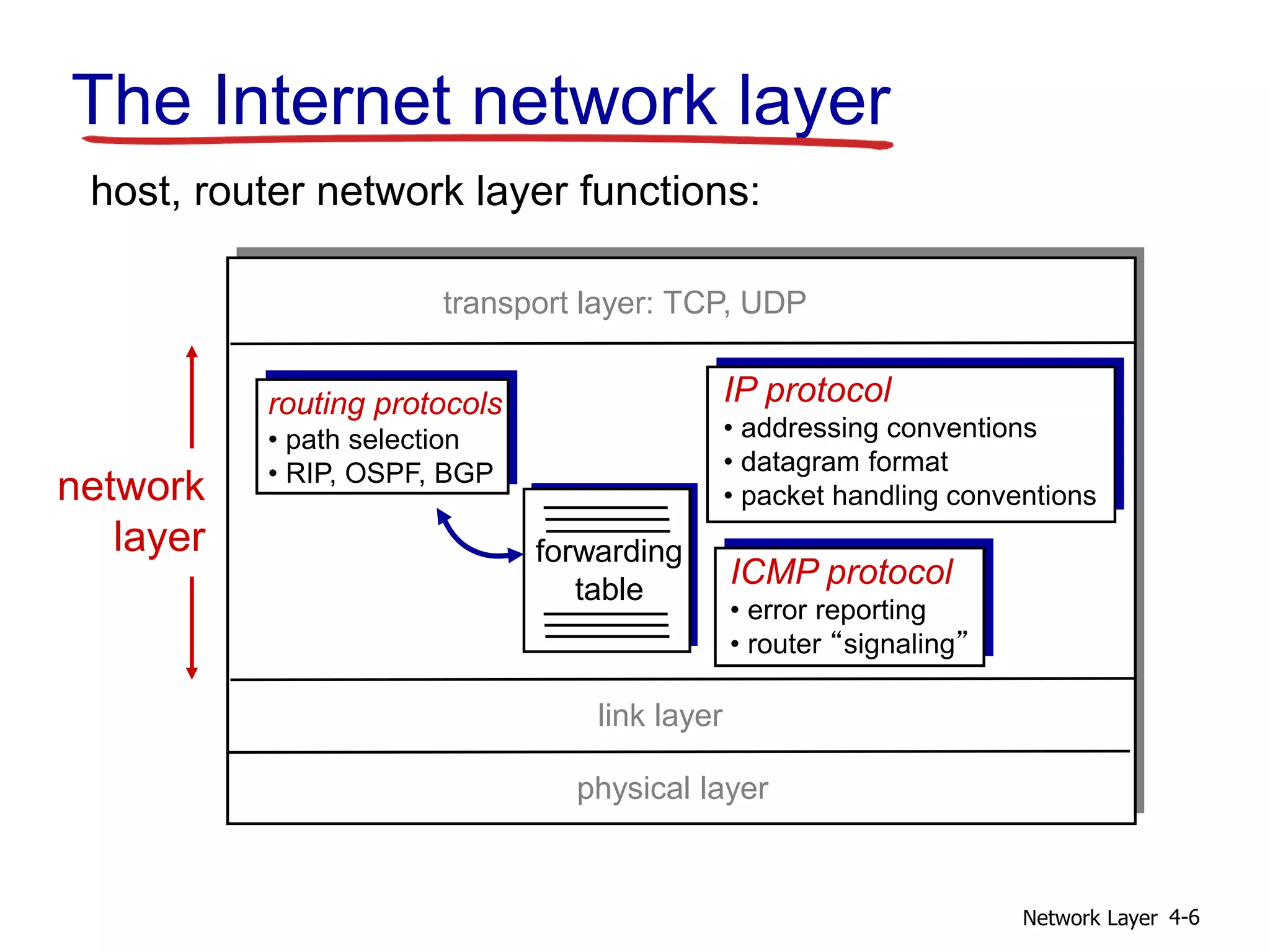
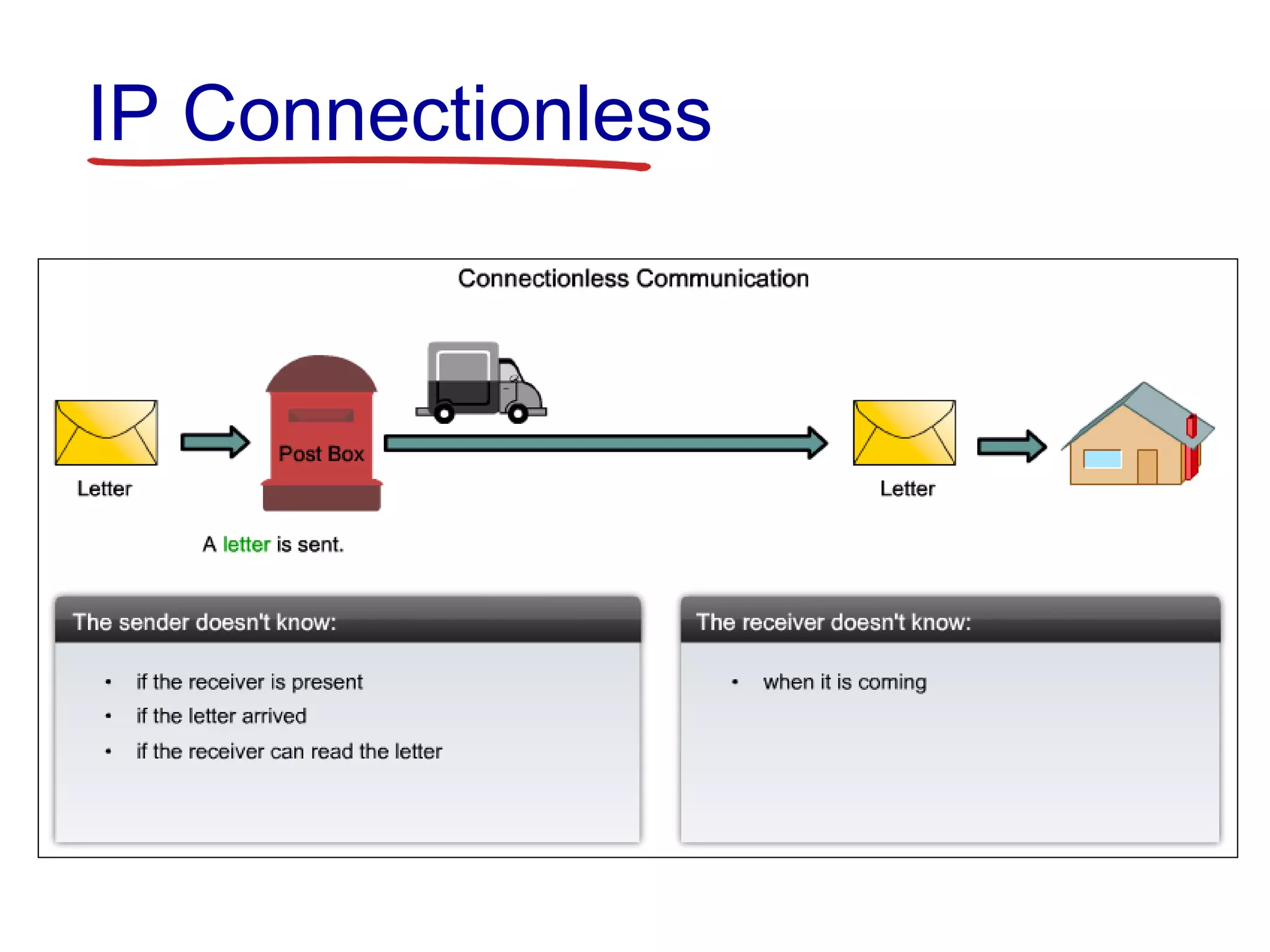
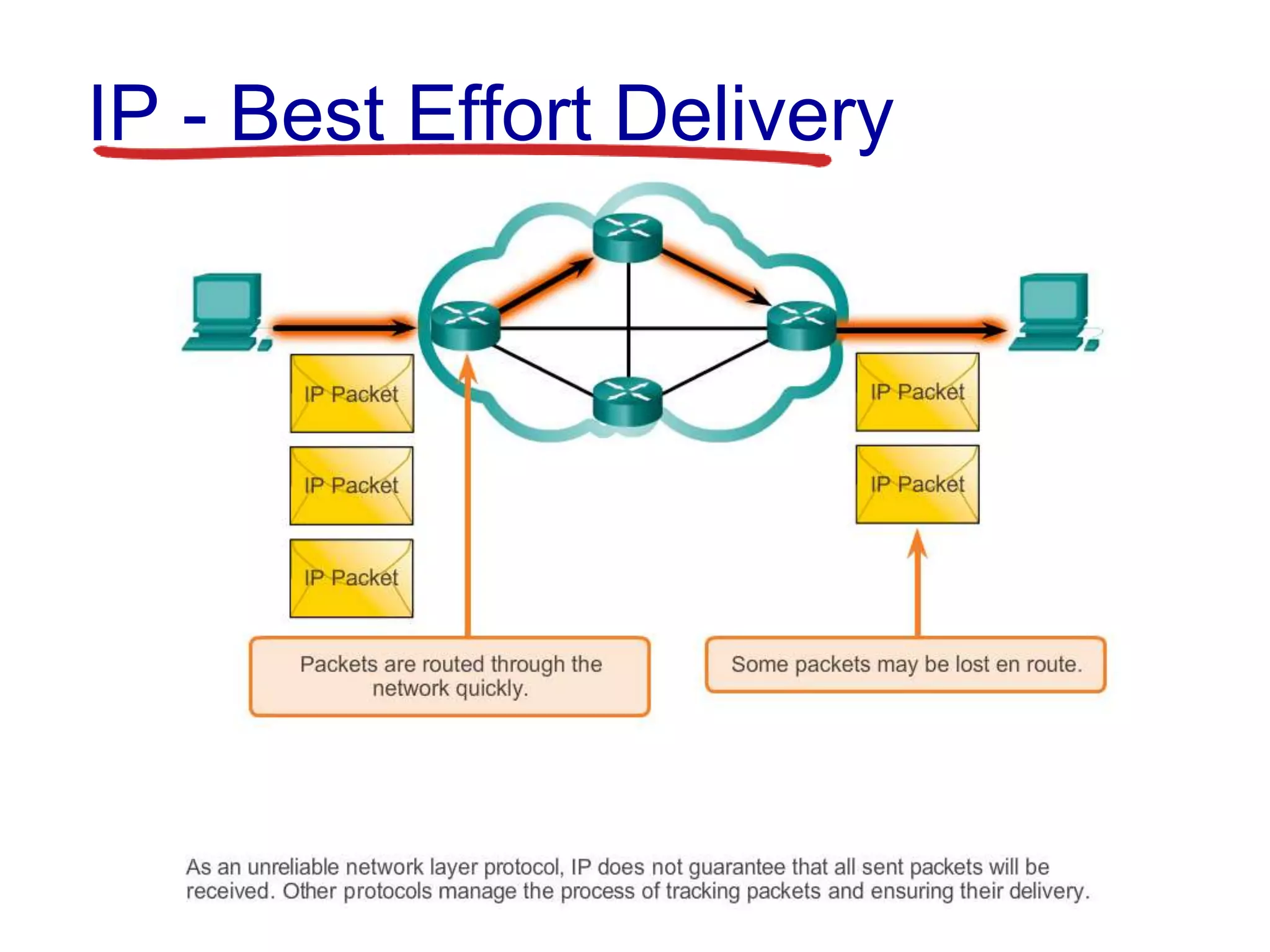
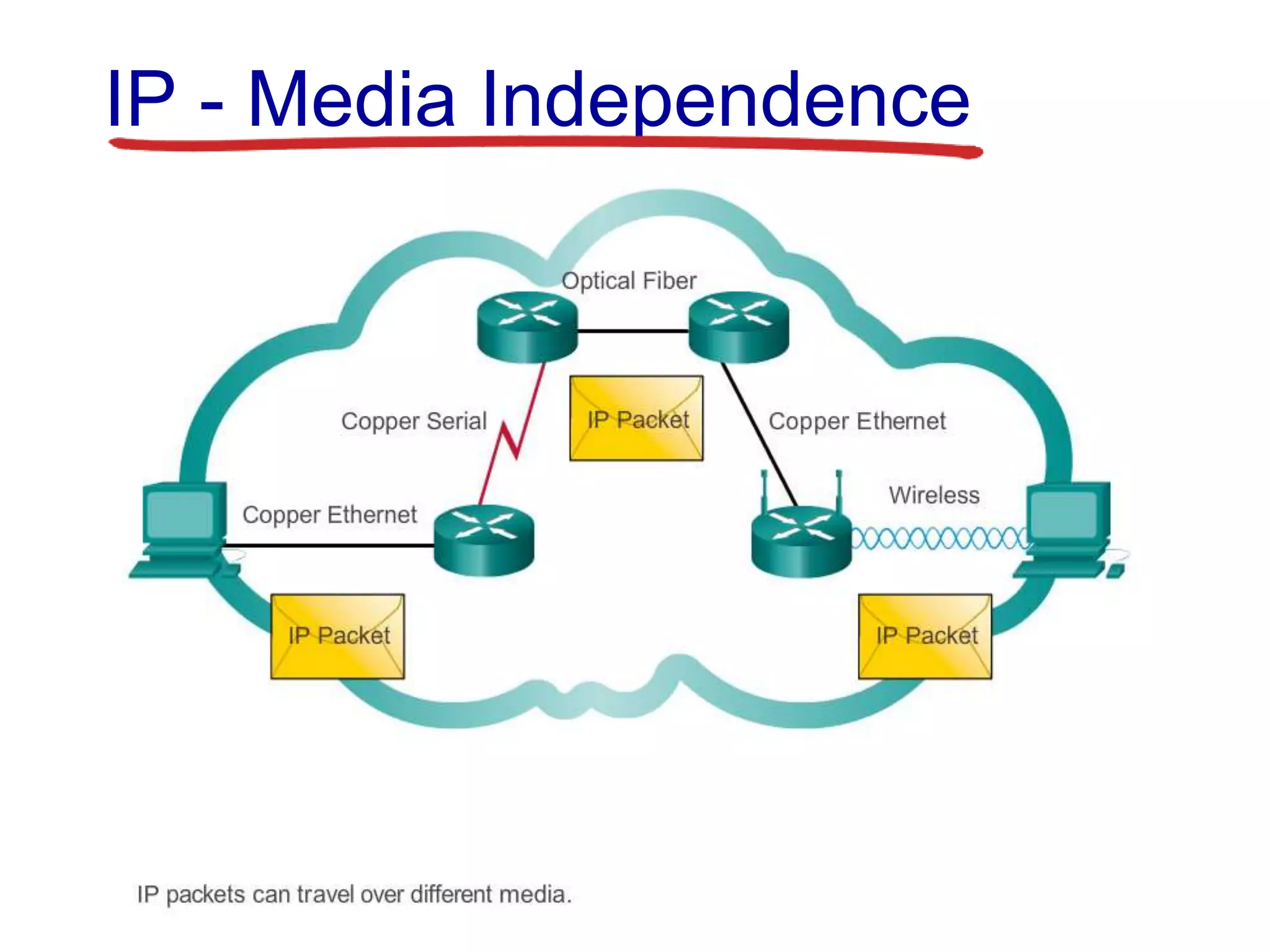
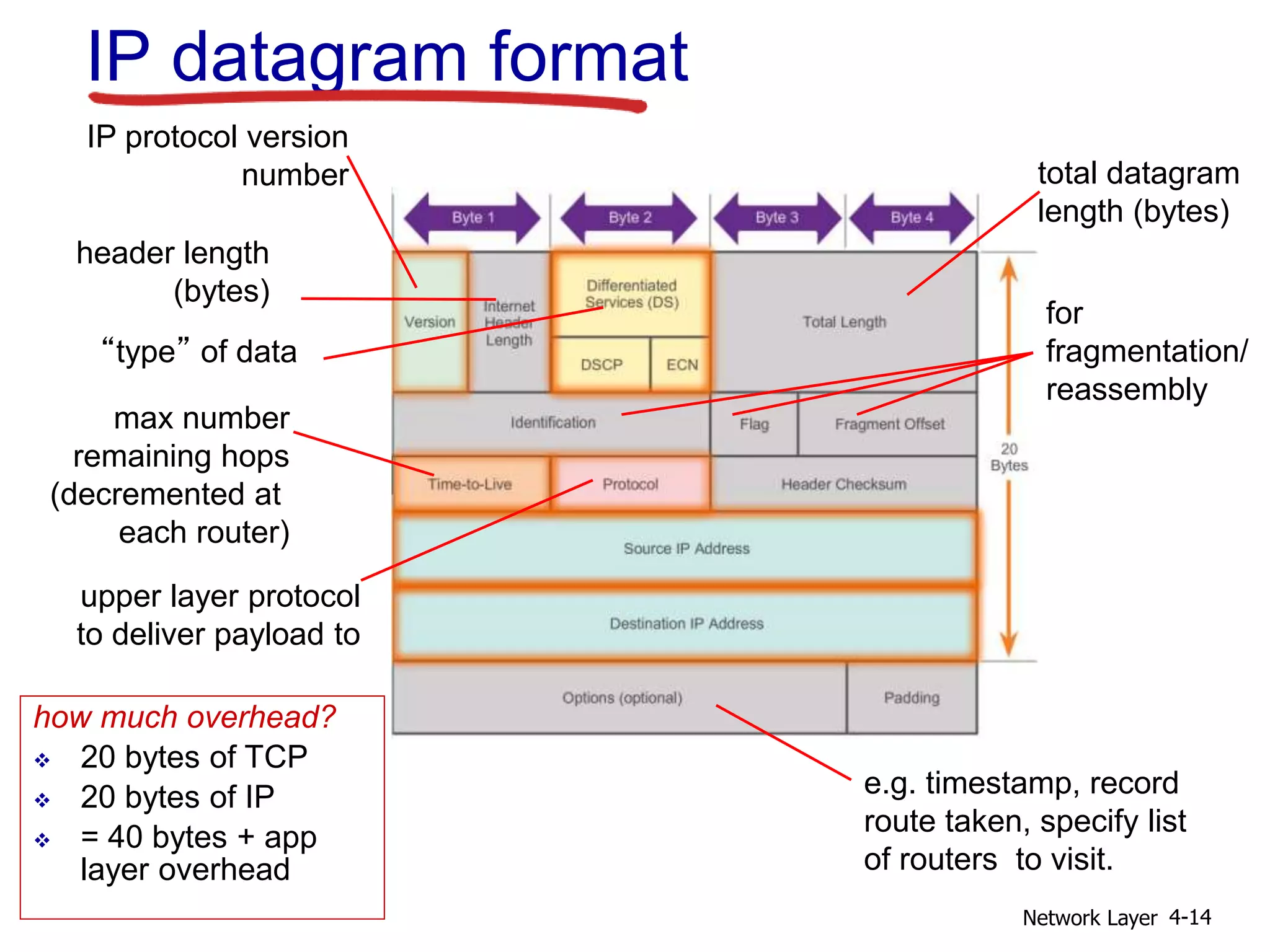
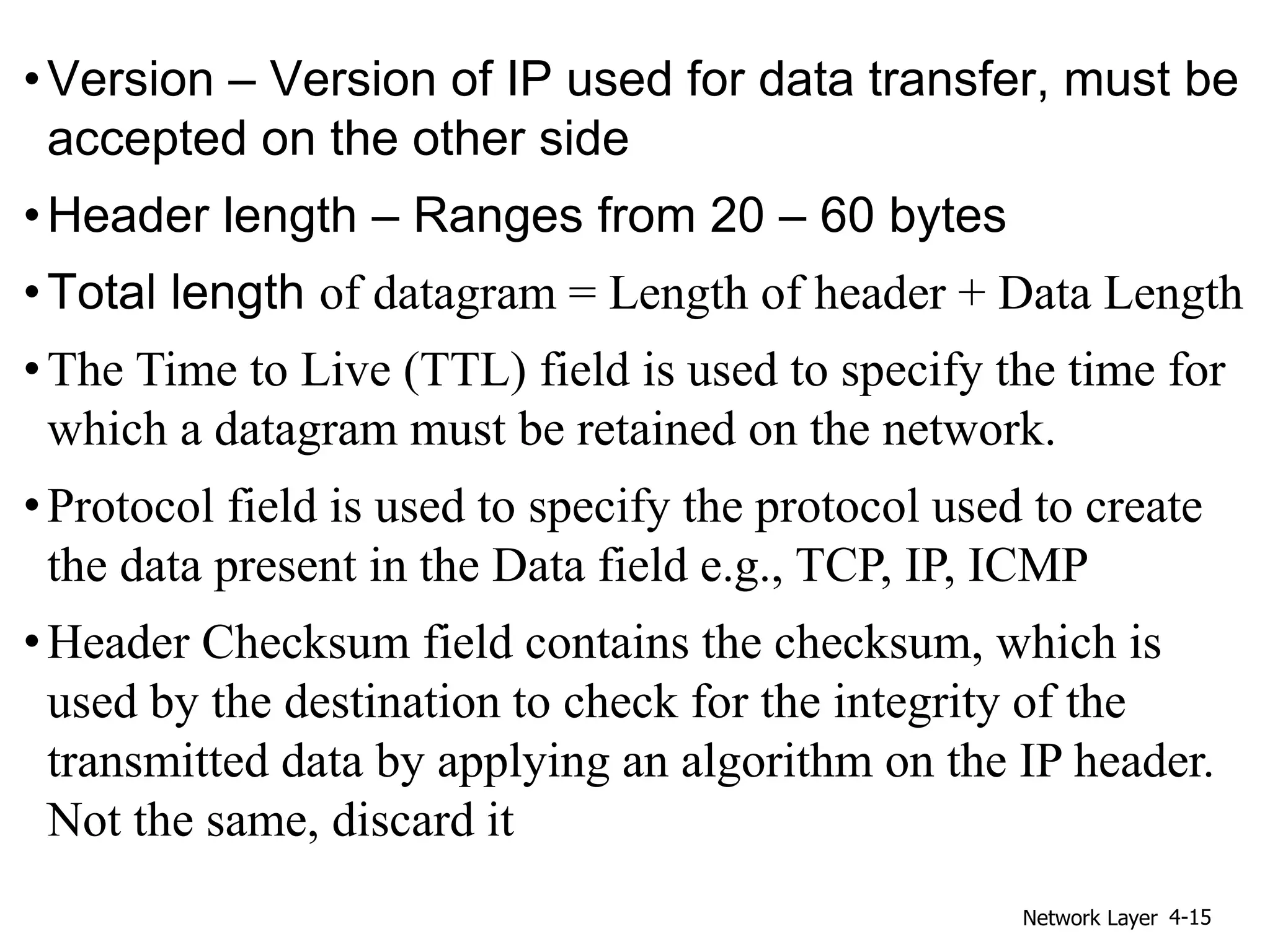
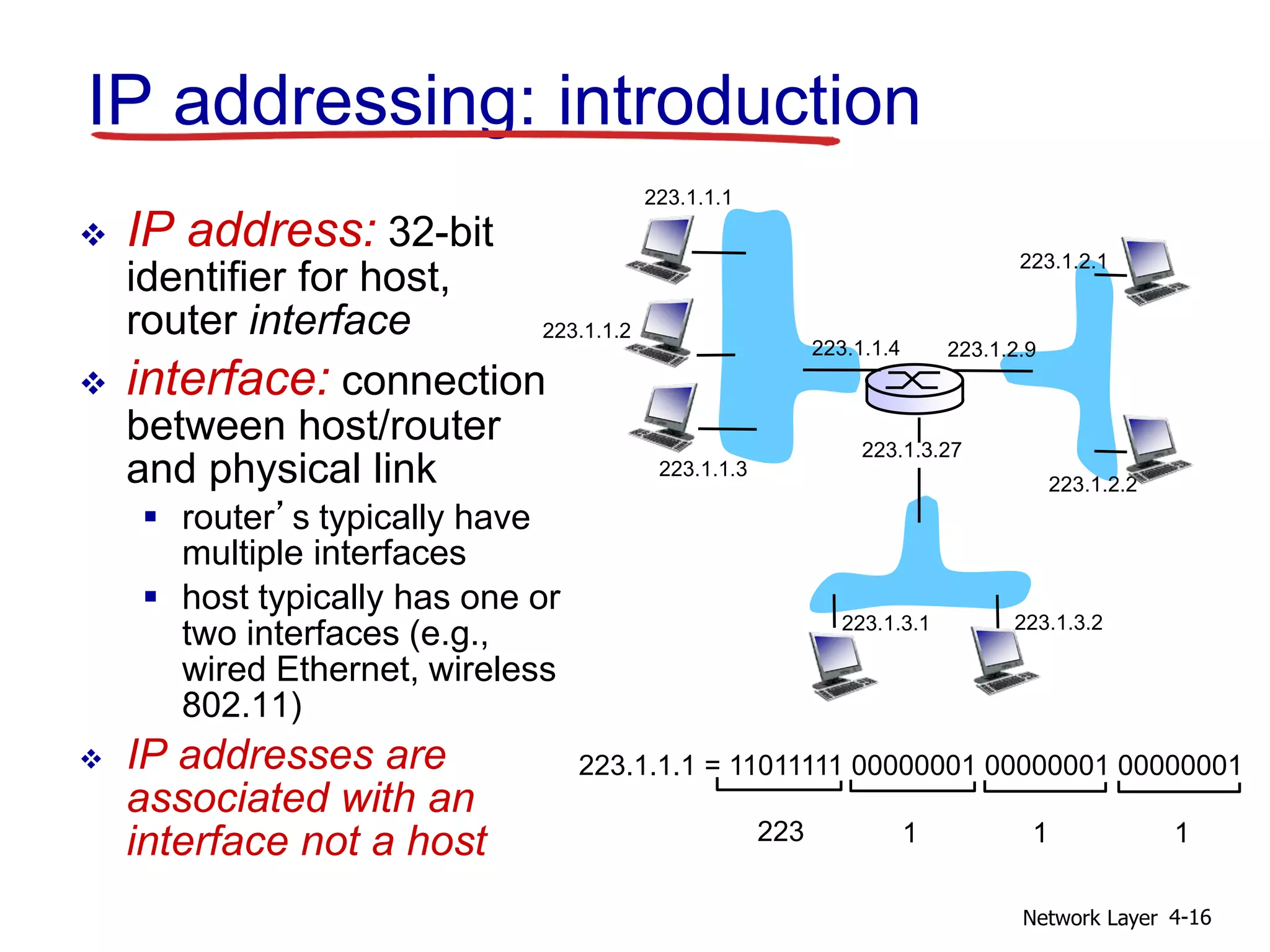
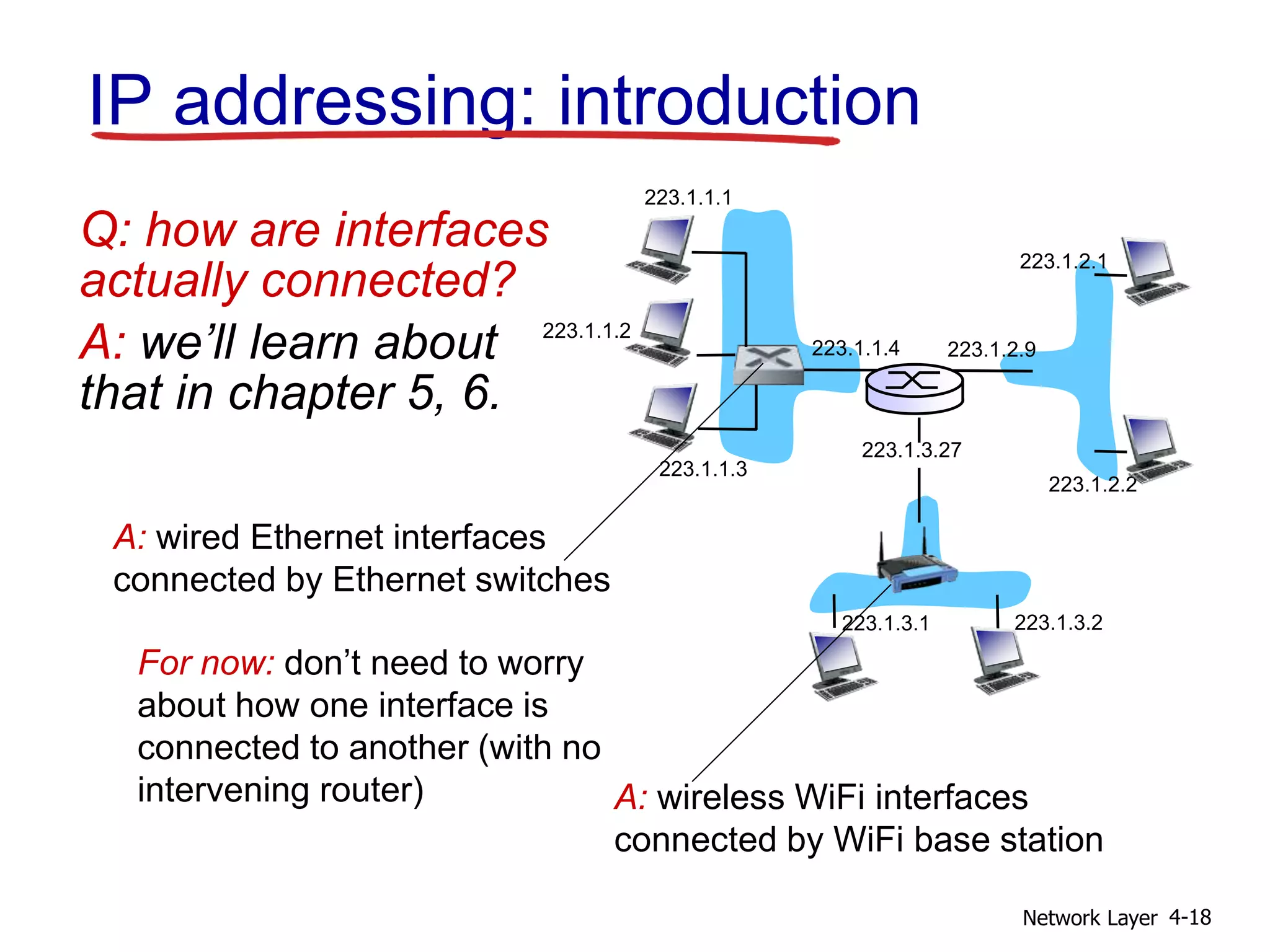
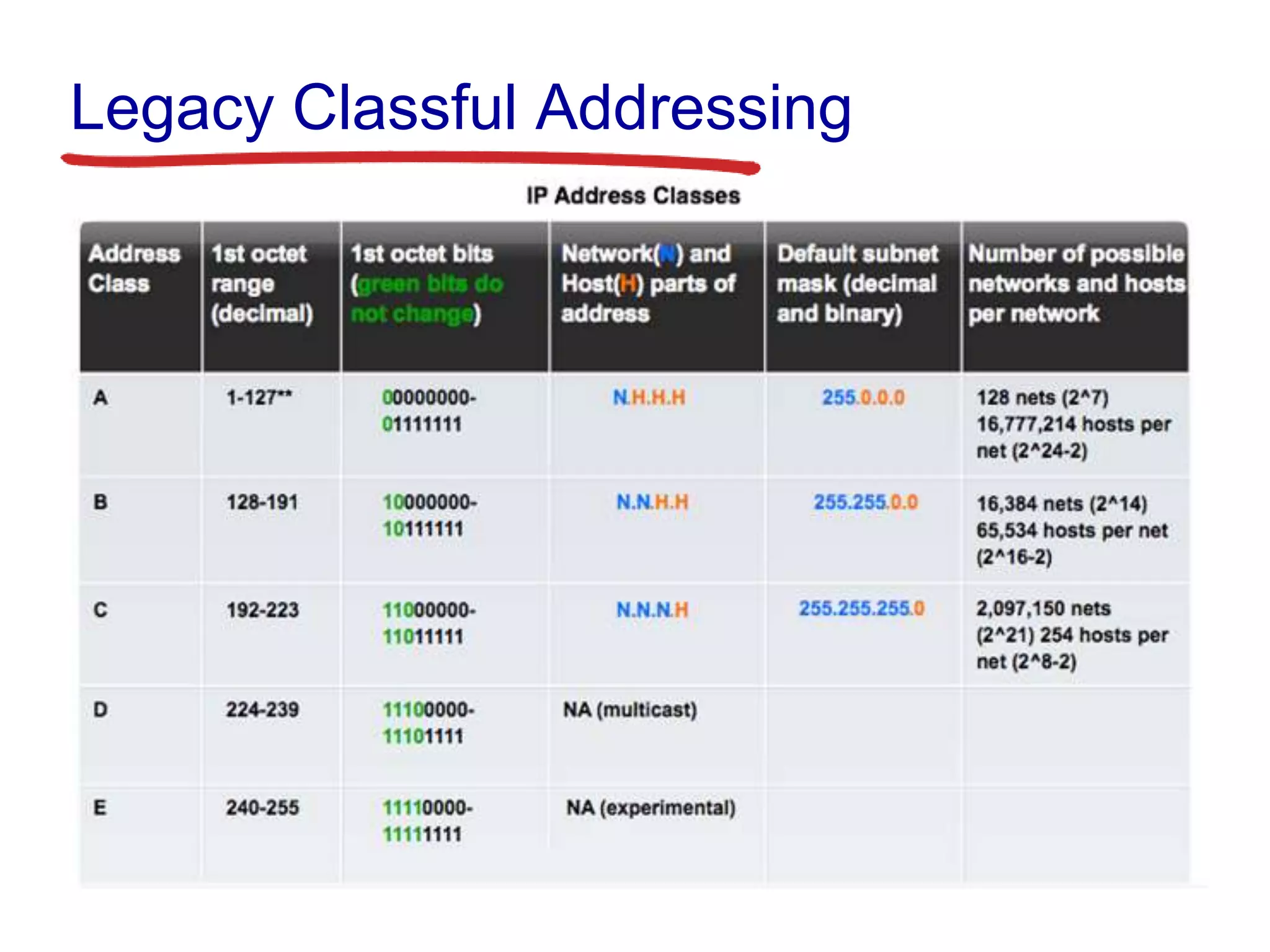
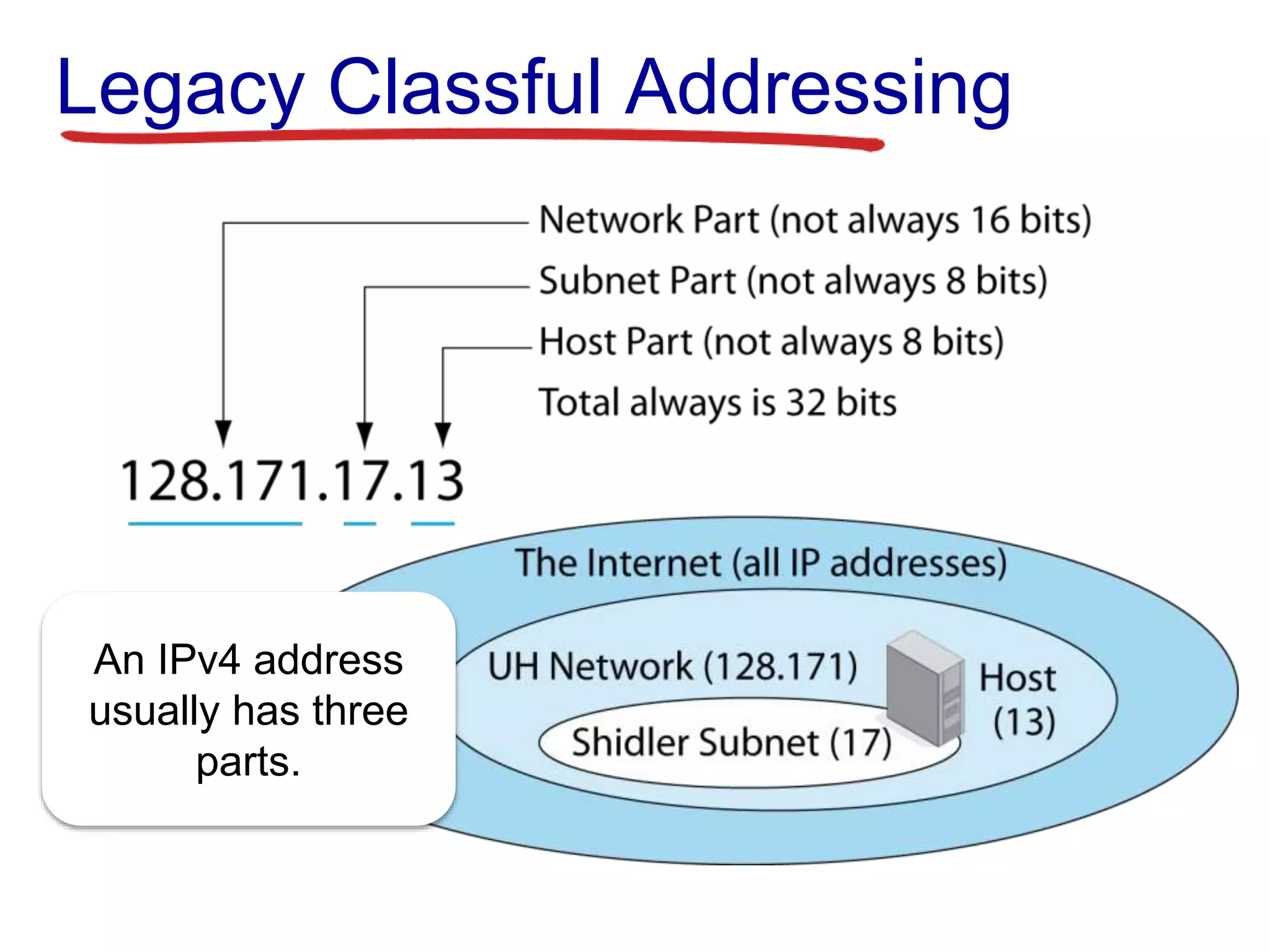
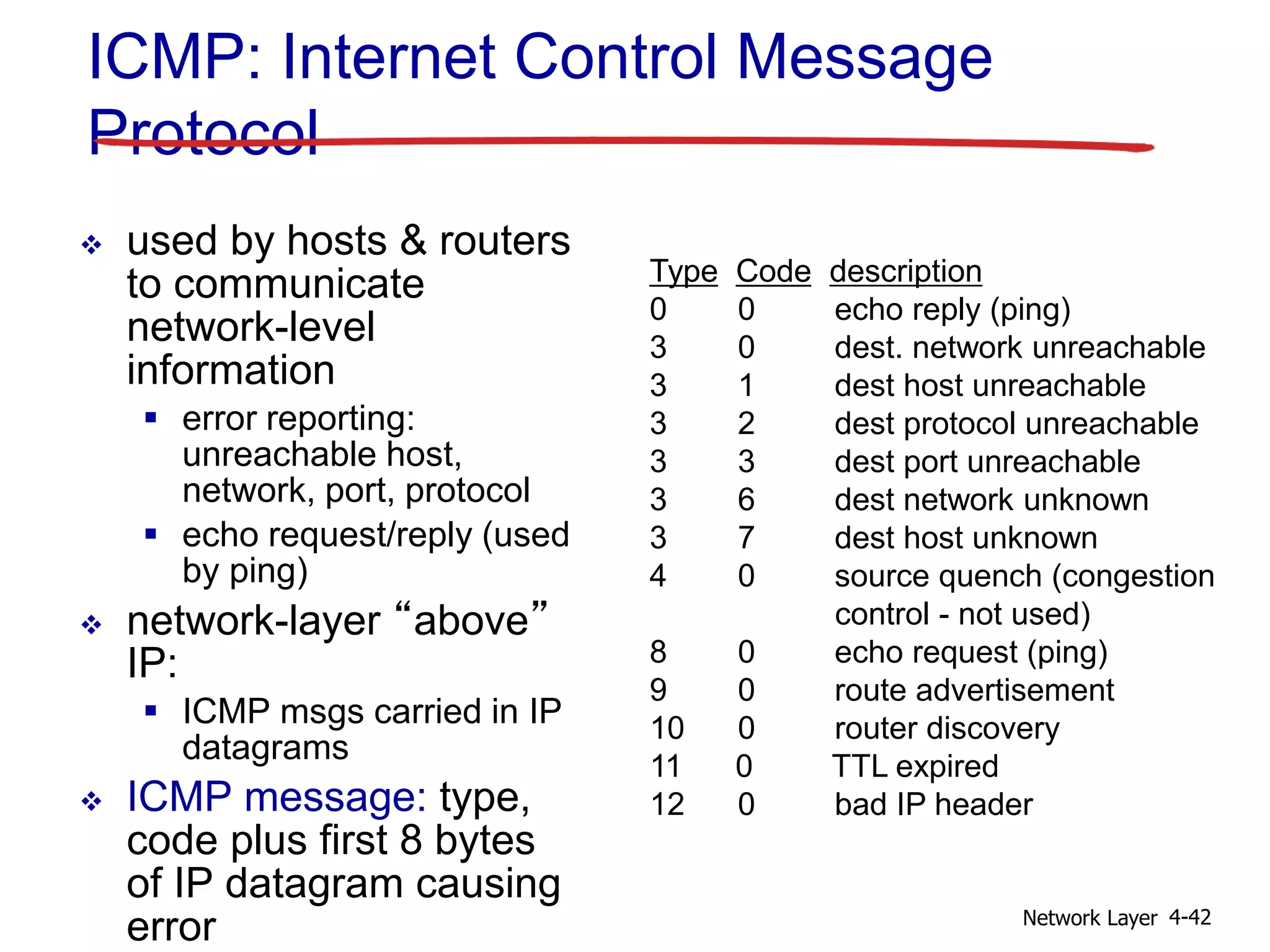
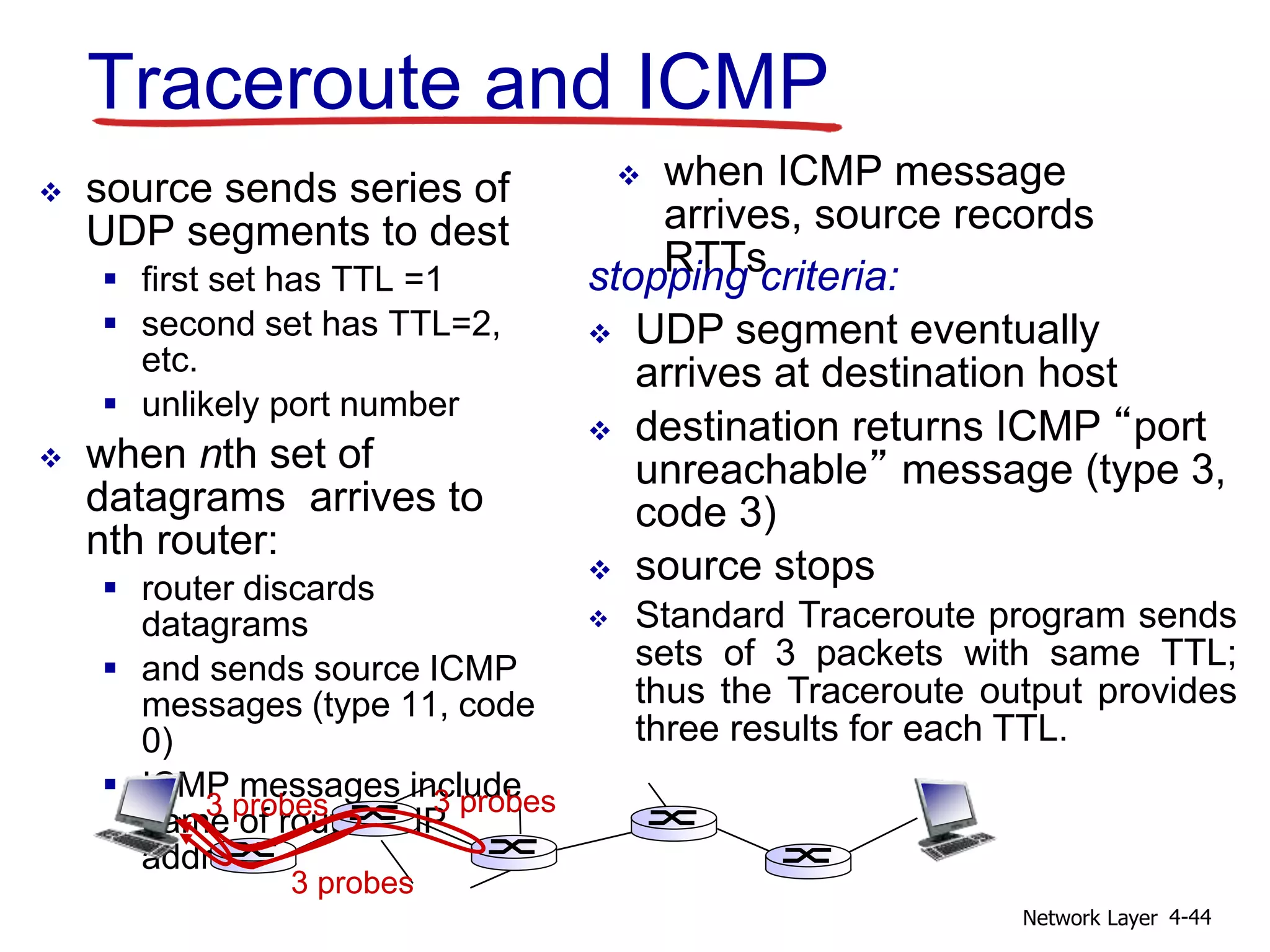
3) The Internet's network layer uses IP to define addressing and datagram format. Routing protocols determine paths and ICMP reports errors. This allows connectionless and best-effort delivery across media.