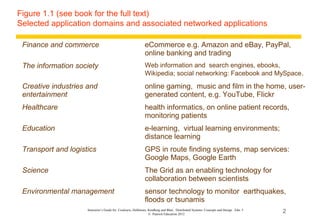
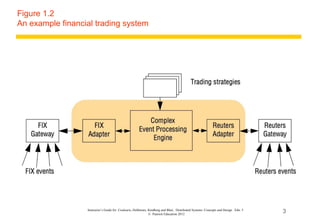
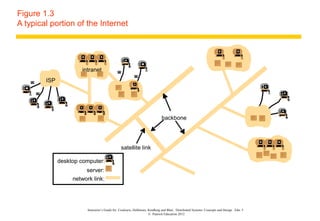
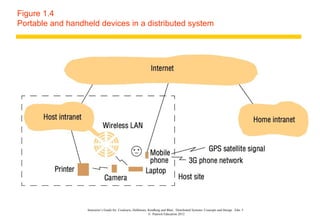
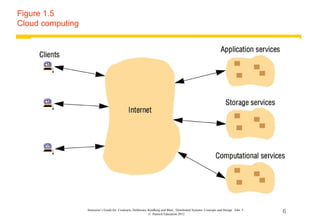
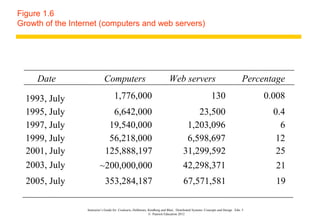
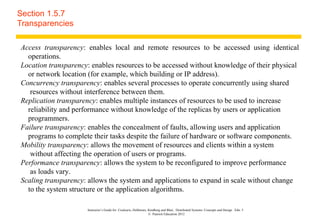
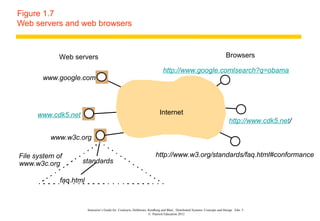
This document contains slides summarizing key concepts from Chapter 1 of the textbook "Distributed Systems: Concepts and Design" by Coulouris, Dollimore, Kindberg and Blair. The slides highlight common application domains for distributed systems like finance, healthcare, education and more. Examples of distributed systems are shown like a financial trading system and portions of the internet. The slides also cover concepts like transparency in distributed systems and how web servers and browsers interact over the internet.