The document provides instructions to configure basic settings on a Cisco router and switch including hostname, enable password, login banner, IP addresses, default gateway, and remote access using telnet. The configurations assign IP addresses to interfaces, set passwords to restrict access to privileged modes, and enable remote management of the devices on the network.







![CCNA Routing & Switching v3 LAB Guide
11
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
6. Enter Virtual Terminal lines and give a password ashish@123#, to login remotely
BUET(config)#line vty 0 4
BUET(config-line)#password ashish@123#
BUET(config-line)#login
BUET(config-line)#exit
BUET(config)#
7. Configure IP Address Router's on Interface
Enter global configuration mode
BUET# config terminal
Enter configuration commands, one per line. End with CNTL/Z.
BUET(config)#
Enter FastEthernet 0/0 interface configuration mode :
BUET(config)#interface fastEthernet 0/0
BUET(config-if)#
Enter IP address and subnet mask:
BUET(config-if)#ip address 192.168.10.1 255.255.255.0
By default, all interfaces on a Cisco router are “Administratively Down”. To bring an interface up, issue
the no shutdown command.
BUET(config-if)#no shutdown
BUET(config-if)#exit
BUET(config)#
8. Save Configuration
BUET#write memory
Building configuration...
[OK]
BUET#
DU#write memory
Building configuration...
[OK]
you can also save configuration using
BUET# copy running-config start-up config
But be sure about the command, cannot be reversed as:
copy start-up config running-config](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-11-320.jpg)



![CCNA Routing & Switching v3 LAB Guide
15
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
Switch(config)#hostname ASHISH-SW
ASHISH-SW(config)#ip domain-name ashish.com
Step 4 :Generate the RSA Keys
ASHISH-SW(config)#crypto key generate rsa
The name for the keys will be: ASHISH-SW.ashish.com
Choose the size of the key modulus in the range of 360 to 2048 for your
General Purpose Keys. Choosing a key modulus greater than 512 may take
a few minutes.
How many bits in the modulus [512]: 2048
% Generating 2048 bit RSA keys, keys will be non-exportable...[OK]
ASHISH-SW(config)#
Key sizes of 1024 or smaller should be avoided. Larger key sizes take longer time to calculate
and enhance more security
Step 5: SSH version 1 is the default version. So change it to version 2
ASHISH-SW(config)#ip ssh version 2
Step 6 : Setup the Line VTY configurations
ASHISH-SW(config)#line vty 0 4
ASHISH-SW(config-line)#transport input ssh
ASHISH-SW(config-line)#login local
Step 7: Create the username password
ASHISH-SW(config)#username ashish privilege 15 password cisco123
Step 8: Create enable password
ASHISH-SW(config)#enable secret cisco123
Step 9: create console password
ASHISH-SW(config)#line console 0
ASHISH-SW(config-line)#logging synchronous
ASHISH-SW(config-line)#login local
Step 10: Verify SSH
C:>ssh -l ashish 192.168.10.10
Password:
ASHISH-SW#conf t](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-15-320.jpg)
![CCNA Routing & Switching v3 LAB Guide
16
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
ASHISH-SW(config)#
Enable SSH on Router (same as before)
Router>en
Router#conf t
Router(config)#hostname Venus
Venus(config)#interface fastEthernet 0/0
Venus(config-if)#ip address 192.168.10.1 255.255.255.0
Venus(config-if)#no shutdown
Venus(config-if)#exit
Venus(config)#ip domain-name cisco.com
Venus(config)#username ashish privilege 15 password cisco123
Venus(config)#crypto key generate rsa
The name for the keys will be: Venus.cisco.com
Choose the size of the key modulus in the range of 360 to 2048 for your
General Purpose Keys. Choosing a key modulus greater than 512 may take
a few minutes.
How many bits in the modulus [512]: 2048
% Generating 2048 bit RSA keys, keys will be non-exportable...[OK]
Venus(config)#
*Mar 1 0:34:31.790: %SSH-5-ENABLED: SSH 1.99 has been enabled
Venus(config)#ip ssh version 2
Venus(config)#enable secret cisco
Venus(config)#line console 0
Venus(config-line)#logging synchronous
Venus(config-line)#login local
Venus(config-line)#exit
Venus(config)#line vty 0 4
Venus(config-line)#transport input ssh
Venus(config-line)#login local](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-16-320.jpg)

![CCNA Routing & Switching v3 LAB Guide
18
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
Configure tftp server (In your physical Lab you can download tftp server in your PC then
configure it. And rest of the configurations are same)
Verify configuration file is saved in NVRAM
Denver#show startup-config
DU#show startup-config
Now backup configuration file to tftp server (From Switch)
Denver#copy startup-config tftp
Address or name of remote host []? 192.168.10.4 (TFTP Server IP)
Destination filename [Denver-confg]? (Press Enter to save it as default name)
Writing startup-config...!!](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-18-320.jpg)
![CCNA Routing & Switching v3 LAB Guide
19
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
[OK - 653 bytes]
653 bytes copied in 0.012 secs (54416 bytes/sec)
Denver#
Now backup configuration file to tftp server (From Router)
DU#copy startup-config tftp:
Address or name of remote host []? 192.168.10.4
Destination filename [DU-confg]?
Writing startup-config...!!
[OK - 1178 bytes]
1178 bytes copied in 0.032 secs (36812 bytes/sec)
DU#
Erase startup-configuration file and reboot or reload the router and switch
DU#erase startup-config
Erasing the nvram filesystem will remove all configuration files! Continue?
[confirm]
[OK]
Erase of nvram: complete
%SYS-7-NV_BLOCK_INIT: Initialized the geometry of nvram
DU#
DU#reload
Proceed with reload? [confirm]
Denver#erase startup-config
Erasing the nvram filesystem will remove all configuration files! Continue?
[confirm]
[OK]
Erase of nvram: complete
%SYS-7-NV_BLOCK_INIT: Initialized the geometry of nvram
BUET#
Denver #reload
Proceed with reload? [confirm]
Configure IP address to router and switch
Router#conf t
Enter configuration commands, one per line. End with CNTL/Z.
Router(config)#interface fastEthernet 0/0
Router(config-if)#ip address 192.168.10.1 255.255.255.0
Router(config-if)#no shutdown
Router(config-if)#exit](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-19-320.jpg)
![CCNA Routing & Switching v3 LAB Guide
20
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
Switch#conf t
Enter configuration commands, one per line. End with CNTL/Z.
Switch(config)#interface vlan 1
Switch(config-if)#ip address 192.168.10.10 255.255.255.0
Switch(config-if)#no shutdown
Switch(config-if)#exit
Switch(config)#ip default-gateway 192.168.10.1
Now restore configuration from tftp server to switch and router
Switch#copy tftp running-config
Address or name of remote host []? 192.168.10.4 (TFTP Server IP)
Source filename []? Denver-confg (Backup file name on tftp server)
Destination filename [running-config]? (Press enter)
Denver#write
Building configuration...
[OK]
Denver#
Router#copy tftp running-config
Address or name of remote host []? 192.168.10.4 (TFTP Server IP)
Source filename []? DU-confg (Backup file name on tftp server)
Destination filename [running-config]? (Press enter)
Now save the configuration to NVRAM
Switch# write memory
Router# write memory
============================================================================
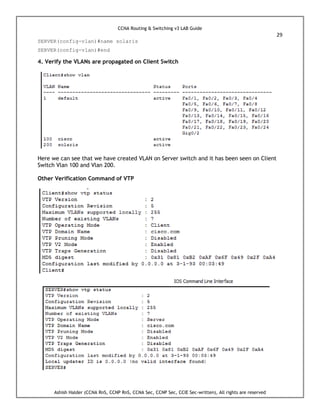
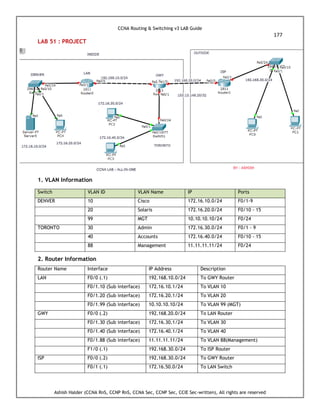
LAB 5: Configure VLAN, Access and Trunk Port
The design of layer-2 switched network is a flat network. Each and every device on the
Network can see the transmission of every broadcast packet even if it does not need to
receive the data. But we can create multiple/ separate broadcast domain logically in a L2
switch. This is possible with VLAN technology. VLAN means Virtual LAN.](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-20-320.jpg)

















![CCNA Routing & Switching v3 LAB Guide
41
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
BUET(config)#interface fastEthernet 0/23
BUET(config-if)#switchport mode access
BUET(config-if)#switchport access vlan 199
BUET(config-if)#exit
BUET(config)#interface vlan 199
BUET(config-if)#ip address 192.168.20.1 255.255.255.0
BUET(config-if)#no shutdown
Telnet Configuration
BUET(config)#line vty 0 4
BUET(config-line)#password cisco123
BUET(config-line)#login
BUET(config-line)#exit
DENVER(config)#line vty 0 4
DENVER(config-line)#password cisco123
DENVER(config-line)#login
DENVER(config-line)#exit
DENVER(config)#interface fastEthernet 0/0.99
DENVER(config-subif)#encapsulation dot1Q 99
DENVER(config-subif)#ip address 192.168.10.1 255.255.255.0
DENVER(config-subif)#no shutdown
DENVER#ping 192.168.10.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.10.1, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 0/2/8 ms
DENVER#telnet 192.168.10.1
Trying 192.168.10.1 ...OpenThis Router belongs to VENUS TELECOM LTD
User Access Verification
Password:
% Password: timeout expired!
[Connection to 192.168.10.1 closed by foreign host]
==============================================================
DENVER#conf t
DENVER(config)#interface fastEthernet 0/0.199
DENVER(config-subif)#encapsulation dot1Q 199
DENVER(config-subif)#ip address 192.168.20.1 255.255.255.0](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-41-320.jpg)











![CCNA Routing & Switching v3 LAB Guide
57
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
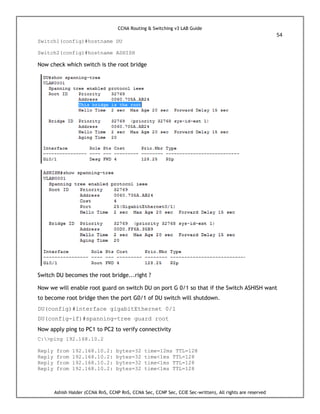
Now we will make it root bridge by using the following command:
spanning-tree vlan [list] root [primary | secondary]
Using this command will automatically lower the priority of the switch to a very significant
value in order to make sure that the switch is elected as a root switch.
ASHISH(config)#spanning-tree vlan 1 root primary
We can see that the switch is now the root bridge.
Method2 (Switch DU will be the root bridge now):
Setting the Bridge priority using the command spanning-tree vlan [list] priority
[value].
DU(config)#spanning-tree vlan 1 priority 4096
DU is now the root switch.](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-57-320.jpg)


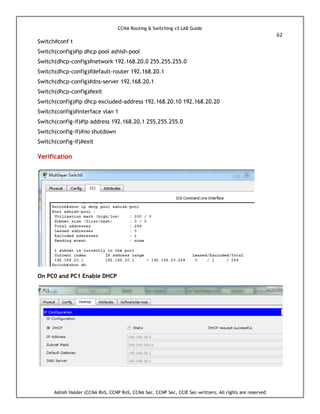



![CCNA Routing & Switching v3 LAB Guide
66
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
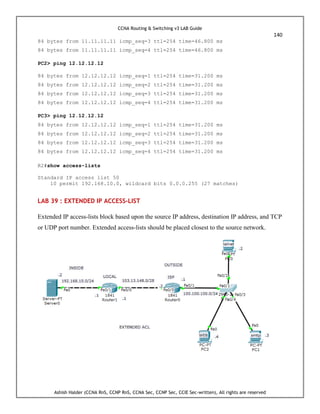
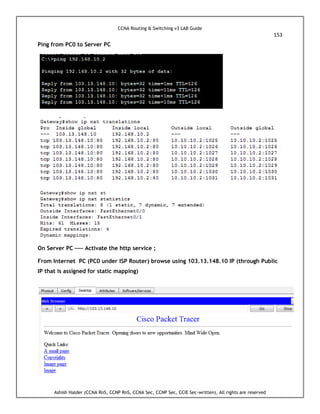
Try to Ping from PC0 to PC1
C:>ping 192.168.30.2
Pinging 192.168.30.2 with 32 bytes of data:
Reply from 192.168.10.1: Destination host unreachable.
Reply from 192.168.10.1: Destination host unreachable.
Reply from 192.168.10.1: Destination host unreachable.
Reply from 192.168.10.1: Destination host unreachable.
Thus we need routing either static or dynamic, right ?
Let us start with static routing...............
DU Router
DU(config)#ip route 192.168.30.0 255.255.255.0 192.168.20.2
BUET Router
BUET(config)#ip route 192.168.10.0 255.255.255.0 192.168.20.1
Rules of Static route
Router(config)# ip route [destination_network] [subnet_mask] [next-hop]
On point-to-point links, an exit-interface can be specified instead of a next-hop address.
Router(config)# ip route [destination_network] [subnet_mask] [Exit-Interface ]
So for the previous example instead of IP Address we can write exit-interface as follows but if
the 2 routers are connected point-to-point
DU(config)#ip route 192.168.30.0 255.255.255.0 fastEthernet 0/0
BUET(config)#ip route 192.168.10.0 255.255.255.0 fastEthernet 0/0
Now ping again,](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-66-320.jpg)
![CCNA Routing & Switching v3 LAB Guide
67
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
C:>ping 192.168.30.2
Reply from 192.168.30.2: bytes=32 time<1ms TTL=126
Reply from 192.168.30.2: bytes=32 time<1ms TTL=126
Reply from 192.168.30.2: bytes=32 time<1ms TTL=126
Reply from 192.168.30.2: bytes=32 time<1ms TTL=126
Telnet to BUET Router..............
C:>telnet 192.168.20.2
Trying 192.168.20.2 ...Open
User Access Verification
Password:
Password:
BUET>
Success...right ..
Other verification command
BUET#show ip route
Gateway of last resort is not set
S 192.168.10.0/24 [1/0] via 192.168.20.1
C 192.168.20.0/24 is directly connected, FastEthernet0/0
C 192.168.30.0/24 is directly connected, FastEthernet0/1
S ----- represent Static route
C------Directly connected route
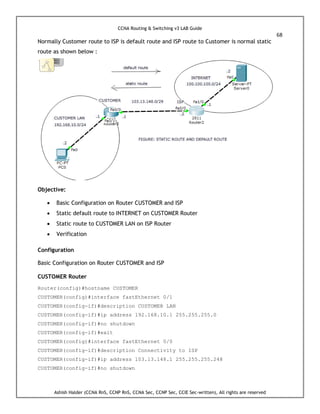
LAB 18 : Static Default Routing
It is a special type of static route. Default routing is used in stub networks. The stub network
has only one way for the traffic to go, to reach several different networks.
A DEFAULT ROUTE is sometime called Zero/Zero Route because the network and subnet we
are specifying as the destination for the traffic that it would match are all zeros.
A DEFAULT ROUTE says "for any traffic that DOES NOT match a specific route in the routing
table ,then forward that traffic to this destination (next-hop-router-IP Address)".Other
words default route is a "CATCH ALL"
On default route, both the network and subnet mask will be zero (0.0.0.0 0.0.0.0).
ip route 0.0.0.0 0.0.0.0 next-hop-router-IP address](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-67-320.jpg)






![CCNA Routing & Switching v3 LAB Guide
76
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
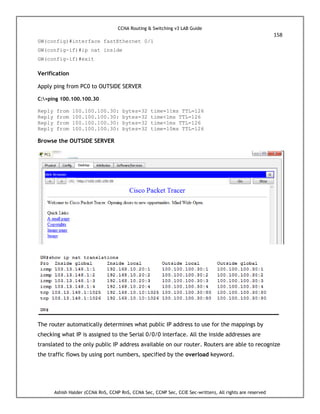
RIP send updates only to 224.0.0.9 (multicast address) Via F0/0 (103.13.148.1).....not
192.168.10.0/24
BUET#show ip route rip
103.0.0.0/29 is subnetted, 1 subnets
R 192.168.10.0/24 [120/1] via 103.13.148.1, 00:00:15, FastEthernet0/0
We can see that the network is advertised but not send any RIP updates
towards DU LAN.
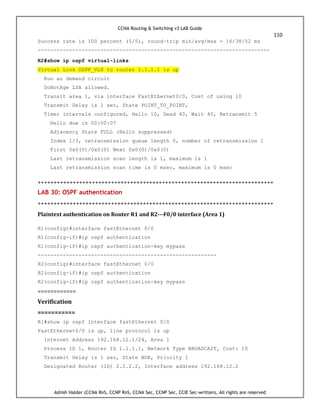
LAB 21: Configure RIP Authentication
Plain text authentication mode is the default setting in every RIPv2 packet, when
authentication is enabled. Plain text authentication should not be used when security is an
issue, because the unencrypted authentication password is sent in every RIPv2 packet. Note:
RIP version 1 (RIPv1) does not support authentication.
I have used GNS3 to configure this LAB](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-76-320.jpg)

![CCNA Routing & Switching v3 LAB Guide
78
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
Configure RIP on R2
BUET(config)#router rip
BUET(config-router)#version 2
BUET(config-router)#network 192.168.10.0
BUET(config-router)#network 192.168.30.0
BUET(config-router)#no auto-summary
BUET(config-router)#end
BUET#
Assign IP address to hosts and verify connectivity using ping command
DU#show ip route rip
R 192.168.30.0/24 [120/1] via 192.168.10.2, 00:00:26, FastEthernet0/0
DU#
R2#show ip route rip
R 192.168.20.0/24 [120/1] via 192.168.10.1, 00:00:27, FastEthernet0/0
R2#](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-78-320.jpg)











![CCNA Routing & Switching v3 LAB Guide
94
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
R1#show ip route
C 192.168.10.0/24 is directly connected, FastEthernet0/0
172.16.0.0/16 is variably subnetted, 6 subnets, 2 masks
C 172.16.4.0/24 is directly connected, Loopback4
C 172.16.0.0/24 is directly connected, Loopback0
D 172.16.0.0/16 is a summary, 00:00:30, Null0
C 172.16.1.0/24 is directly connected, Loopback1
C 172.16.2.0/24 is directly connected, Loopback2
C 172.16.3.0/24 is directly connected, Loopback3
R2#show ip route
C 192.168.10.0/24 is directly connected, FastEthernet0/0
172.16.0.0/24 is subnetted, 5 subnets
D 172.16.4.0 [90/409600] via 192.168.10.1, 00:00:07, FastEthernet0/0
D 172.16.0.0 [90/409600] via 192.168.10.1, 00:00:07, FastEthernet0/0
D 172.16.1.0 [90/409600] via 192.168.10.1, 00:00:07, FastEthernet0/0
D 172.16.2.0 [90/409600] via 192.168.10.1, 00:00:07, FastEthernet0/0
D 172.16.3.0 [90/409600] via 192.168.10.1, 00:00:07, FastEthernet0/0
Router R2 gets a number of EIGRP Route from R1, So we will now reduce the size of routing
table of R2
We will create the summary (Manual Summarization)
R1(config)#interface fastEthernet 0/0
R1(config-if)#ip summary-address eigrp 10 172.16.0.0 255.255.248.0
Verification
R2#show ip route
C 192.168.10.0/24 is directly connected, FastEthernet0/0
172.16.0.0/21 is subnetted, 1 subnets
D 172.16.0.0 [90/409600] via 192.168.10.1, 00:00:15, FastEthernet0/0
R2#show ip route eigrp
172.16.0.0/21 is subnetted, 1 subnets
D 172.16.0.0 [90/409600] via 192.168.10.1, 00:05:05, FastEthernet0/0
Now we can see that R2 Router has only one summary route......](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-94-320.jpg)












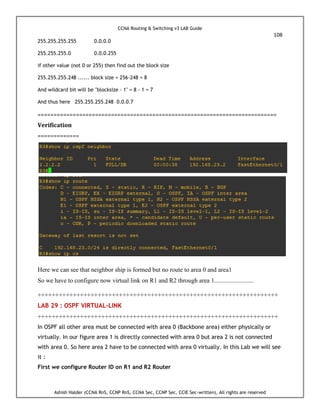
![CCNA Routing & Switching v3 LAB Guide
109
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
R1(config-router)#router-id 1.1.1.1
R1(config-router)#
R2(config-router)#router-id 2.2.2.2
Reload or use "clear ip ospf process" command, for this to take effect
R2#clear ip ospf process
Reset ALL OSPF processes? [no]: yes
We must run this command to take effect on this configuration (also called soft reset)
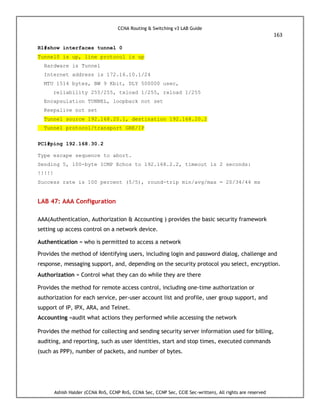
Now we will configure virtual link through area 1
R1(config)#router ospf 1
R1(config-router)#area 1 virtual-link 2.2.2.2
R2(config)#router ospf 1
R2(config-router)#area 1 virtual-link 1.1.1.1
===========
Now verify
============
Ping to any loopback IP
R3#ping 172.16.1.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 172.16.1.1, timeout is 2 seconds:
!!!!!](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-109-320.jpg)











![CCNA Routing & Switching v3 LAB Guide
130
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
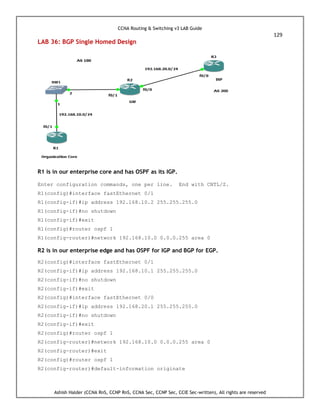
R2(config-router)#exit
R2(config)#router bgp 100
R2(config-router)#neighbor 192.168.20.2 remote-as 200
R2(config-router)#network 1.1.1.0 mask 255.255.255.0
R2(config-router)#exit
R2(config)#ip route 1.1.1.0 255.255.255.0 null 0
R2 is in the service provider edge. R2 has a couple of static routes to advertise into BGP and is
advertising a default route to R1 which will then propagated throughout the enterprise core.
R3(config)#interface fastEthernet 0/0
R3(config-if)#ip address 192.168.20.2 255.255.255.0
R3(config-if)#no shutdown
R3(config)#ip route 0.0.0.0 0.0.0.0 null 0
R3(config)#ip route 2.2.2.0 255.255.255.0 null 0
R3(config)#router bgp 200
R3(config-router)#neighbor 192.168.20.1 remote-as 100
R3(config-router)#network 2.2.2.0 mask 255.255.255.0
R3(config-router)#neighbor 192.168.20.1 default-originate
R3(config-router)#exit
Verification
R3#show ip bgp summary
Neighbor V AS MsgRcvd MsgSent TblVer InQ OutQ Up/Down State/PfxRcd
192.168.20.1 4 100 23 24 3 0 0 00:19:33 1
R2#show ip route
..................<output omitted>...................
1.0.0.0/24 is subnetted, 1 subnets
S 1.1.1.0 is directly connected, Null0
2.0.0.0/24 is subnetted, 1 subnets
B 2.2.2.0 [20/0] via 192.168.20.2, 00:17:59 ** BGP learned route **
C 192.168.10.0/24 is directly connected, FastEthernet0/1
C 192.168.20.0/24 is directly connected, FastEthernet0/0
B* 0.0.0.0/0 [20/0] via 192.168.20.2, 00:20:18 ** default route from BGP
because of the default originate command in R3 **
R2#show ip bgp
-------------------<output omitted>.........................
Network Next Hop Metric LocPrf Weight Path](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-130-320.jpg)
![CCNA Routing & Switching v3 LAB Guide
131
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
*> 0.0.0.0 192.168.20.2 0 0 200 i
*> 1.1.1.0/24 0.0.0.0 0 32768 i
*> 2.2.2.0/24 192.168.20.2 0 0 200 i
R1#show ip ospf neighbor
Neighbor ID Pri State Dead Time Address Interface
192.168.20.1 1 FULL/BDR 00:00:31 192.168.10.1 FastEthernet0/1
R1#show ip route
------------------<outputs are omitted>--------------
Gateway of last resort is 192.168.10.1 to network 0.0.0.0
C 192.168.10.0/24 is directly connected, FastEthernet0/1
O*E2 0.0.0.0/0 [110/1] via 192.168.10.1, 00:06:16, FastEthernet0/1
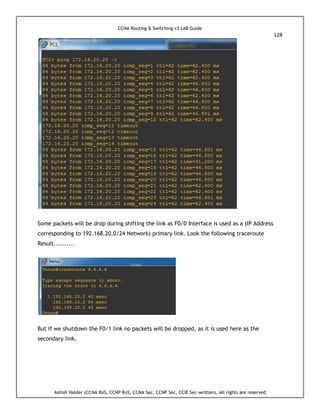
Here we can see R2 is BGP (Single homed) with R3 advertising a /24 (1.1.1.0/24) and R2 is
advertising a default to the enterprise core (R1).
Explaination
default-information originate, the router is going to Redistribute a default route it got from
another Router (OSPF)
neighbor x.x.x.x default-originate (BGP)
If you want to advertise default route to a specific peer, this is the method for that
requirement.
Add ‘neighbor x.x.x.x default-originate’ under router bgp <ASN>
It does not even check for the existence of a default route in the IP routing table
The ‘default-information originate’ command should not be configured with the
‘neighbor x.x.x.x default-originate’ command on the same router
The Null interface is typically used for preventing routing loops.
Also prevent DoS Aattack. An example of where this traffic to unused IP addresses might come
from could be denial of service attacks, scanning of IP blocks to find vulnerable hosts, etc
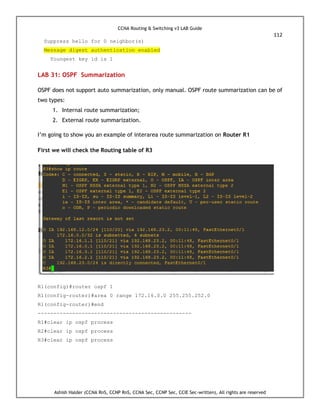
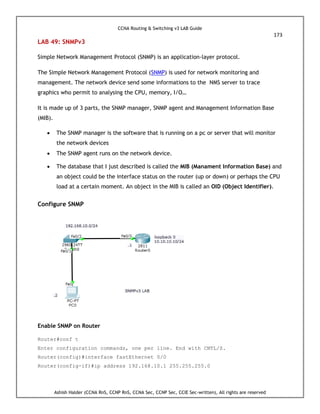
LAB 37 : HSRP (Hot Standby Router Protocol) Configuration
HSRP provides layer 3 redundancy in our network through active and standby router
assignment, interface tracking, and load balancing. A group of physical routers, acting as a
single virtual router, advertise a single IP address and MAC address into our network. By
tracking interfaces and managing multiple groups, we can optimize speed as well as add](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-131-320.jpg)





















































![CCNA Routing & Switching v3 LAB Guide
194
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
DU#show ipv6 interface fastEthernet 0/0
FastEthernet0/0 is up, line protocol is up
IPv6 is enabled, link-local address is FE80::2E0:8FFF:FED5:BD01
No Virtual link-local address(es):
Global unicast address(es):
2001:BB9:AABB:1234:2E0:8FFF:FED5:BD01, subnet is 2001:BB9:AABB:1234::/64
[EUI]
Joined group address(es):
DU#show ipv6 route
IPv6 Routing Table - 3 entries
Codes: C - Connected, L - Local, S - Static, R - RIP, B - BGP
U - Per-user Static route, M - MIPv6
I1 - ISIS L1, I2 - ISIS L2, IA - ISIS interarea, IS - ISIS summary
O - OSPF intra, OI - OSPF inter, OE1 - OSPF ext 1, OE2 - OSPF ext 2
ON1 - OSPF NSSA ext 1, ON2 - OSPF NSSA ext 2
D - EIGRP, EX - EIGRP external
C 2001:BB9:AABB:1234::/64 [0/0]
via ::, FastEthernet0/0
L 2001:BB9:AABB:1234:2E0:8FFF:FED5:BD01/128 [0/0]
via ::, FastEthernet0/0
L FF00::/8 [0/0]
via ::, Null0
DU#
BUET#show ipv6 interface fastEthernet 0/0
FastEthernet0/0 is up, line protocol is up
IPv6 is enabled, link-local address is FE80::202:4AFF:FEA8:2D01
No Virtual link-local address(es):
Global unicast address(es):
2001:BB9:AABB:1234:202:4AFF:FEA8:2D01, subnet is 2001:BB9:AABB:1234::/64
[EUI]
Joined group address(es):
FF02::1
FF02::2
FF02::1:FFA8:2D01
Ping from BUET to DU](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-194-320.jpg)

![CCNA Routing & Switching v3 LAB Guide
196
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
Ashish(config-if)#exit
Ashish(config)#interface fastEthernet 0/0
Ashish(config-if)#ipv6 enable
Ashish(config-if)#no shutdown
Ashish(config-if)#end
Ashish#show ipv6 interface brief
FastEthernet0/0 [up/up]
FE80::202:17FF:FE09:E901 (IP Address - link local Address, getting by ipv6 enable command)
FastEthernet0/1 [administratively down/down]
Loopback1 [up/up]
FE80::210:11FF:FE65:7A37
2001::1
Vlan1 [administratively down/down]
APECE#ping ipv6 FE80::202:17FF:FE09:E901
Output Interface: fastethernet0/0
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to FE80::202:17FF:FE09:E901, timeout is 2
seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 0/0/1 ms
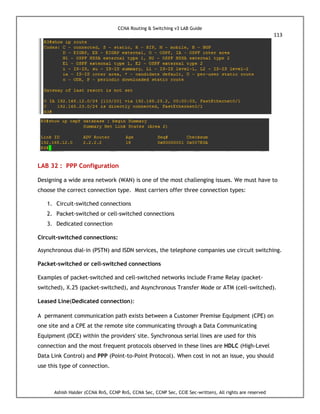
LAB 53 : Configure IPv6 Static Route](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-196-320.jpg)
![CCNA Routing & Switching v3 LAB Guide
197
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
The configuration and syntax are same as IPv4 Static routing, Just we will find some minor
differences than that of IPv4.
DU Router
Router>en
Router#conf t
Enter configuration commands, one per line. End with CNTL/Z.
Router(config)#hostname DU
DU(config)#ipv6 unicast-routing
DU(config)#interface fastEthernet 0/0
DU(config-if)#ipv6 address 2001:AD8:23:45::1/64
DU(config-if)#no shutdown
DU(config-if)#exit
BUET Router
Router>en
Router#conf t
Enter configuration commands, one per line. End with CNTL/Z.
Router(config)#hostname BUET
BUET(config)#ipv6 unicast-routing
BUET(config)#interface fastEthernet 0/0
BUET(config-if)#ipv6 address 2001:AD8:23:45::2/64
BUET(config-if)#no shutdown
BUET(config-if)#exit
BUET#conf t
Enter configuration commands, one per line. End with CNTL/Z.
BUET(config)#interface fastEthernet 0/1
BUET(config-if)#ipv6 address 2001:BD55:1234:DC4::1/64
BUET(config-if)#no shutdown
BUET(config-if)#end
BUET#
Veirfication
BUET#show ipv6 interface brief
FastEthernet0/0 [up/up]
FE80::260:3EFF:FEAE:5901
2001:AD8:23:45::2](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-197-320.jpg)
![CCNA Routing & Switching v3 LAB Guide
198
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
FastEthernet0/1 [administratively down/down]
Vlan1 [administratively down/down]
BUET#
Verify Connectivity using ping
DU#ping ipv6 2001:AD8:23:45::2
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 2001:AD8:23:45::2, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 0/0/2 ms
DU#
Assign IPv6 Address to host
Ping to Router BUET from host
C:>ping 2001:BD55:1234:DC4::1
Reply from 2001:BD55:1234:DC4::1: bytes=32 time=1ms TTL=255
Reply from 2001:BD55:1234:DC4::1: bytes=32 time<1ms TTL=255
Reply from 2001:BD55:1234:DC4::1: bytes=32 time<1ms TTL=255
Reply from 2001:BD55:1234:DC4::1: bytes=32 time<1ms TTL=255
Now ping to Router DU
C:>ping 2001:AD8:23:45::1
Request timed out.
Request timed out.
Request timed out.
Request timed out.](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-198-320.jpg)


![CCNA Routing & Switching v3 LAB Guide
201
Ashish Halder (CCNA RnS, CCNP RnS, CCNA Sec, CCNP Sec, CCIE Sec-written), All rights are reserved
Sending 5, 100-byte ICMP Echos to 2001:BD55:1234:DC4::2, timeout is 2
seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 0/0/1 ms
DU#show ipv6 route
IPv6 Routing Table - 4 entries
Codes: C - Connected, L - Local, S - Static, R - RIP, B - BGP
U - Per-user Static route, M - MIPv6
I1 - ISIS L1, I2 - ISIS L2, IA - ISIS interarea, IS - ISIS summary
O - OSPF intra, OI - OSPF inter, OE1 - OSPF ext 1, OE2 - OSPF ext 2
ON1 - OSPF NSSA ext 1, ON2 - OSPF NSSA ext 2
D - EIGRP, EX - EIGRP external
C 2001:AD8:23:45::/64 [0/0]
via ::, FastEthernet0/0
L 2001:AD8:23:45::1/128 [0/0]
via ::, FastEthernet0/0
R 2001:BD55:1234:DC4::/64 [120/2]
via FE80::260:3EFF:FEAE:5901, FastEthernet0/0
L FF00::/8 [0/0]
via ::, Null0
DU#
*** Don’t forget to enable IPv6 unicast routing otherwise no routing protocol will work for IPv6.
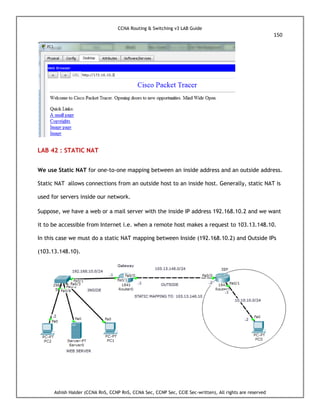
LAB 55 : Dual-Stack Example
Hosts and network devices run both IPv4 and IPv6 at the same time.
Router#conf t
Enter configuration commands, one per line. End with CNTL/Z.
Router(config)#ipv6 unicast-routing](https://image.slidesharecdn.com/ccna-lab-guide-v3last-addition4-220531101129-45c72f51/85/CCNA-LAB-GUIDE-V3_LAST-ADDITION-4-pdf-201-320.jpg)