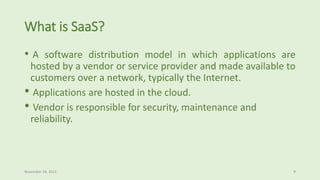
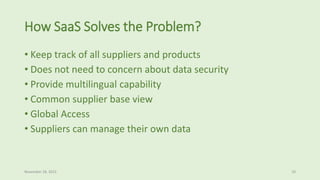
The document presents a case study on the successful implementation of Software-as-a-Service (SaaS) for General Electric and H.B. Fuller, focusing on their need for a centralized, user-friendly system to manage supplier interactions, data security, and compliance. It outlines the benefits of SaaS, such as lower costs, scalability, and global access, as well as risks associated with its use, including data security and vendor reliability. Ultimately, the implementation of SaaS led to improved service standards, enhanced management capabilities, and opportunities for expansion.