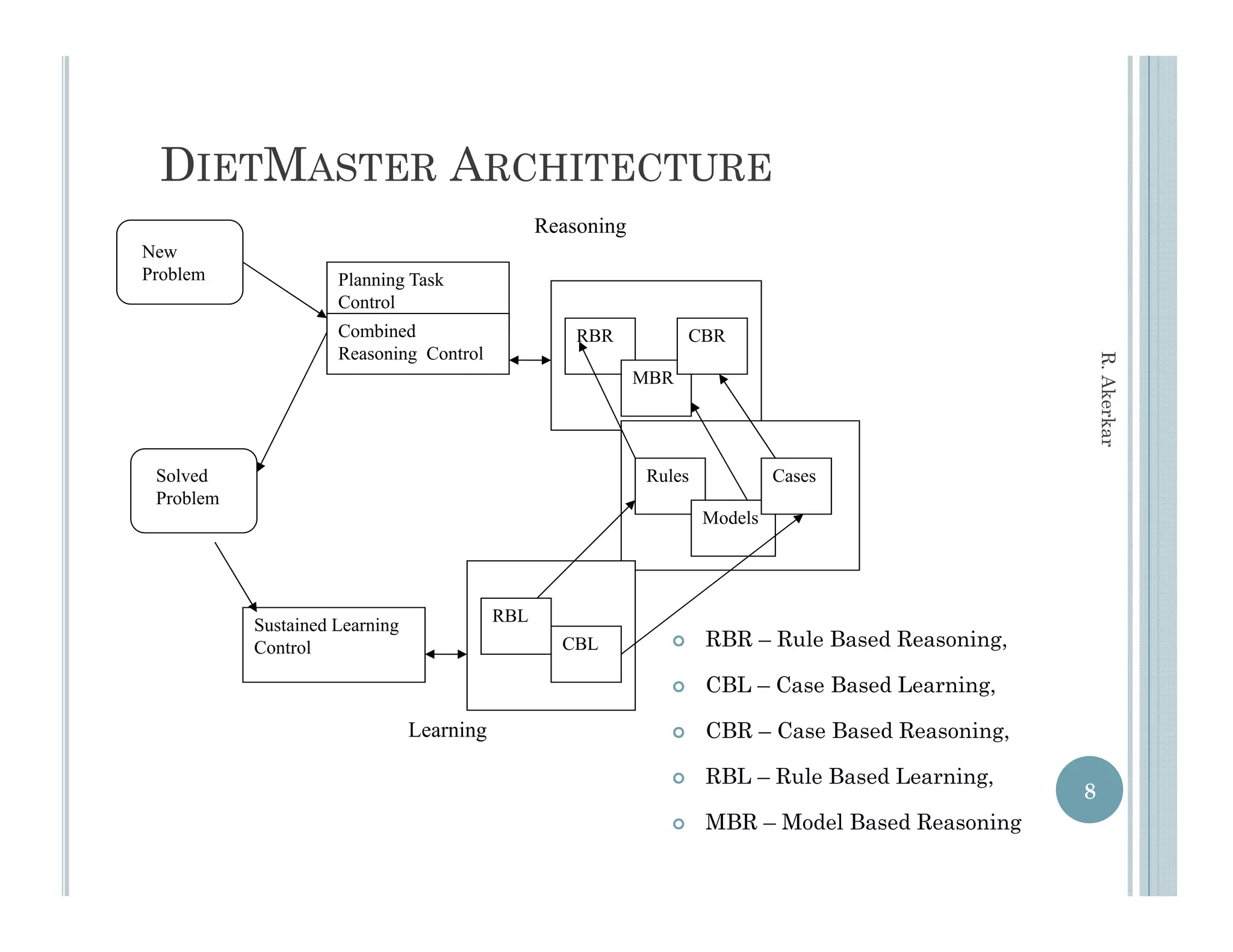
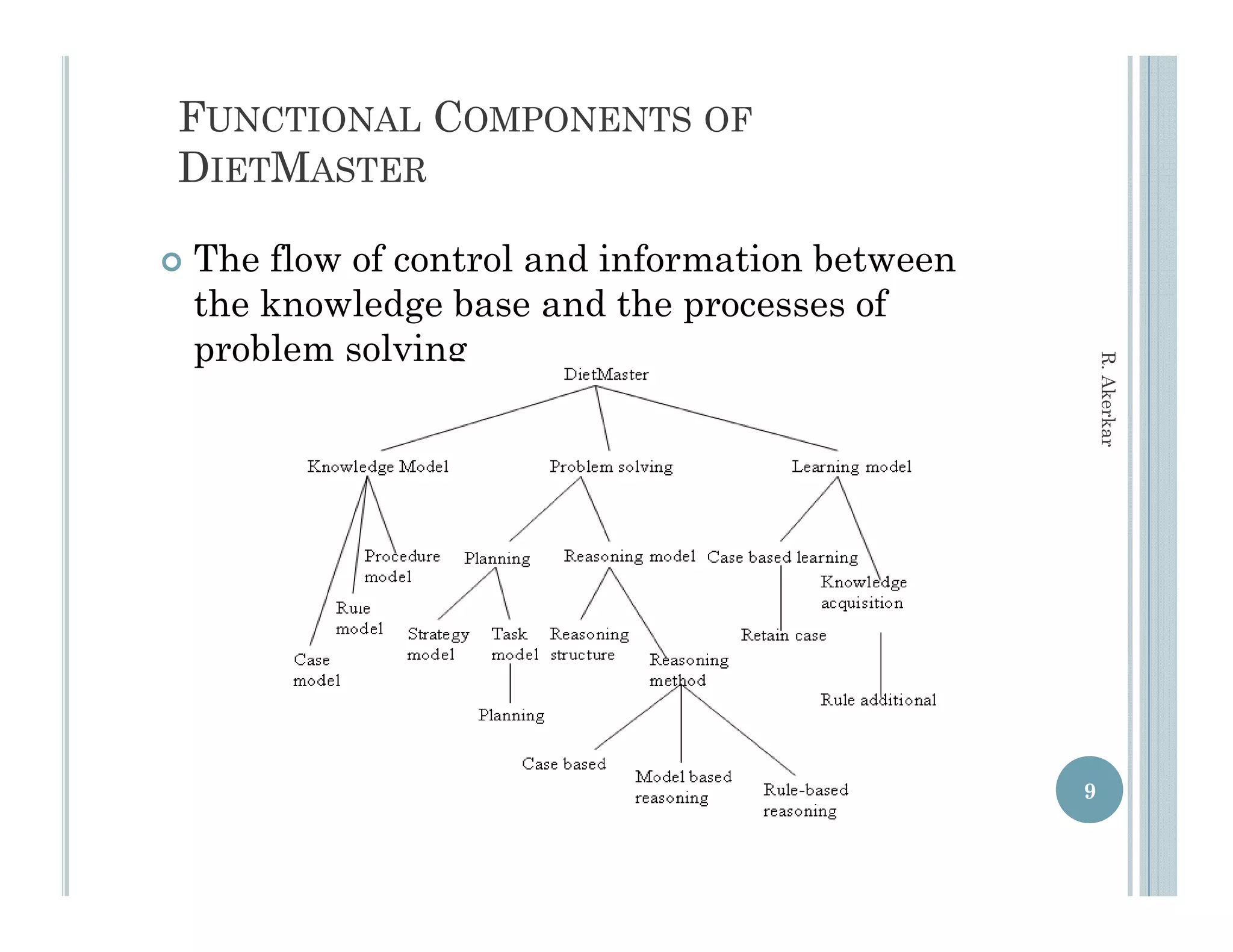
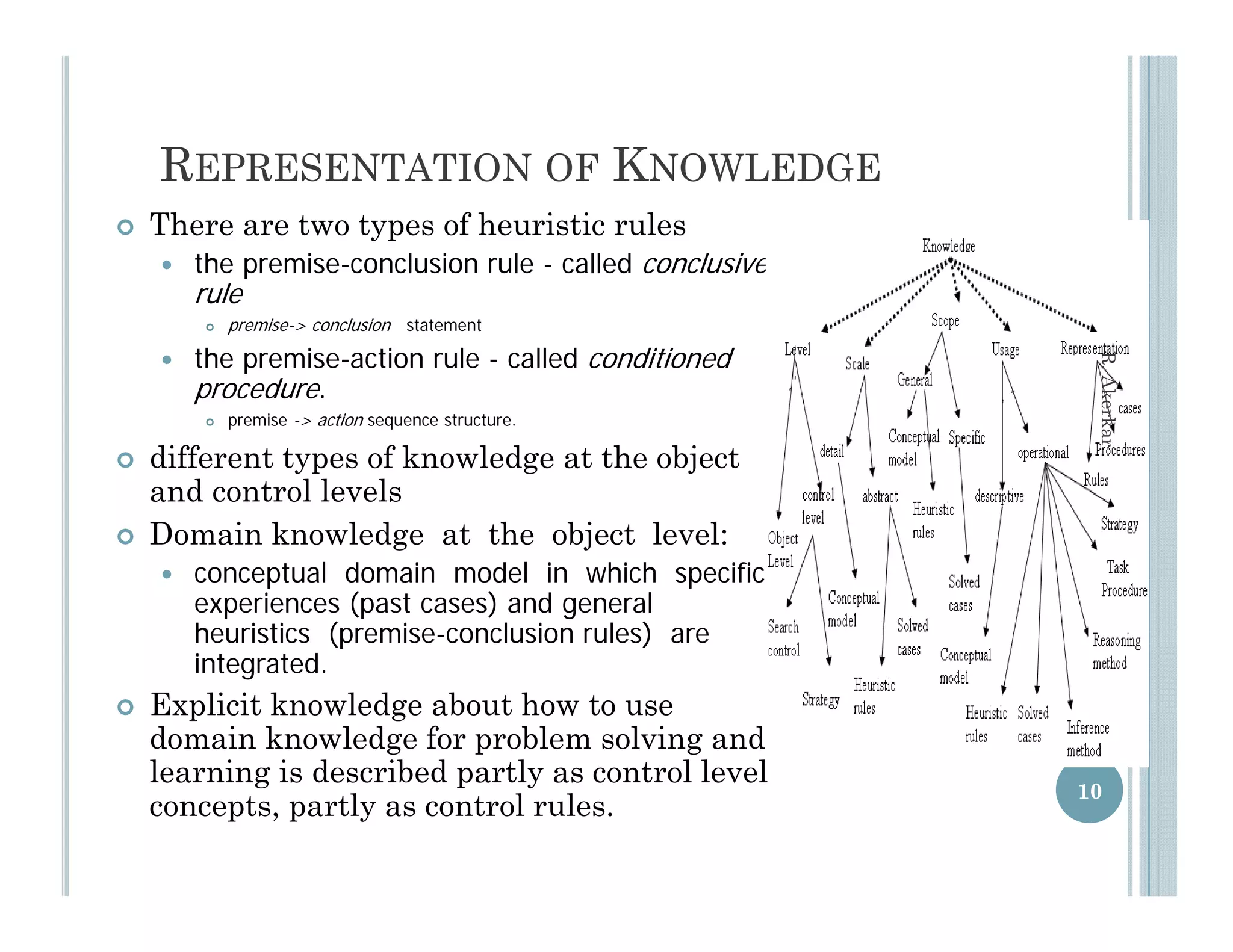
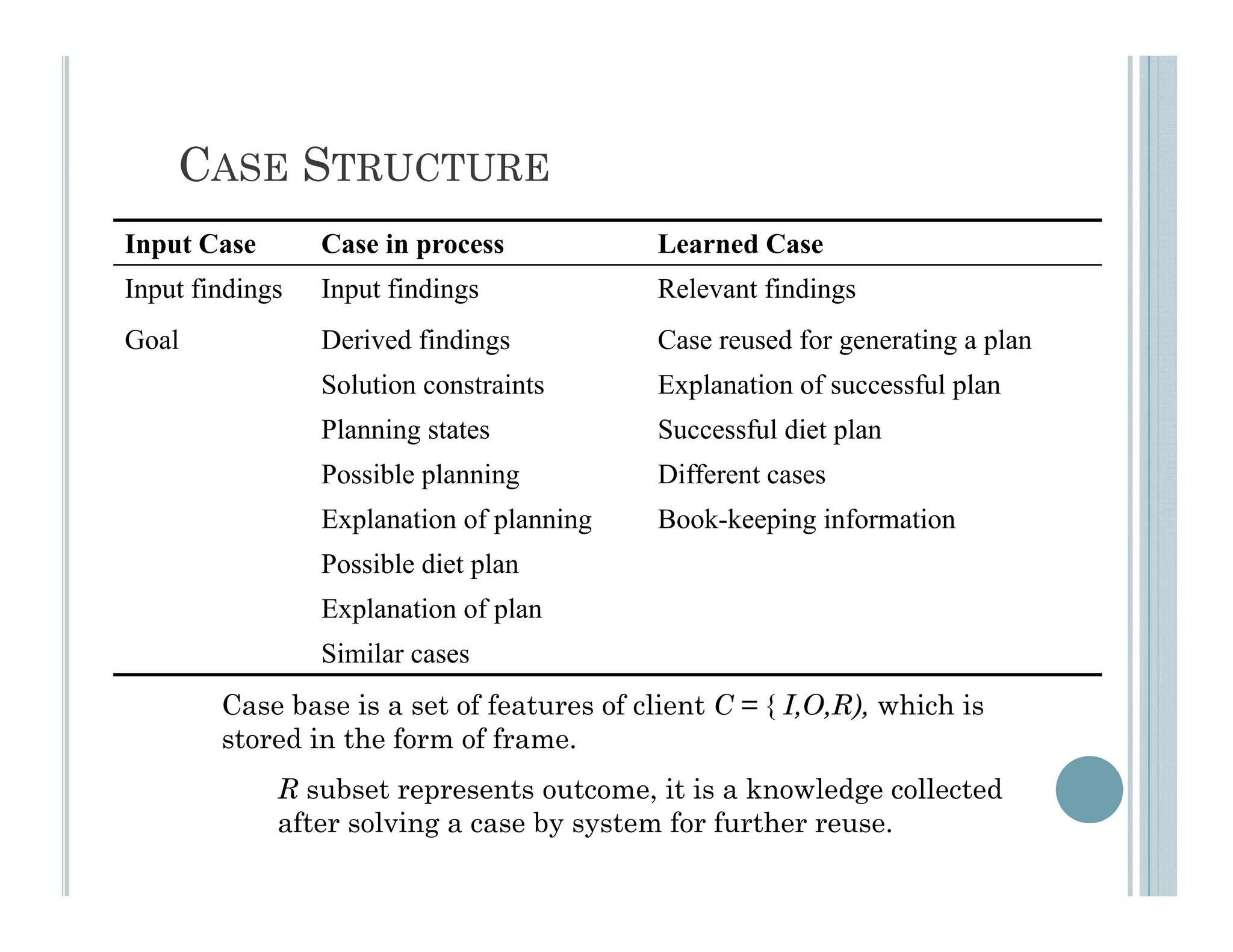
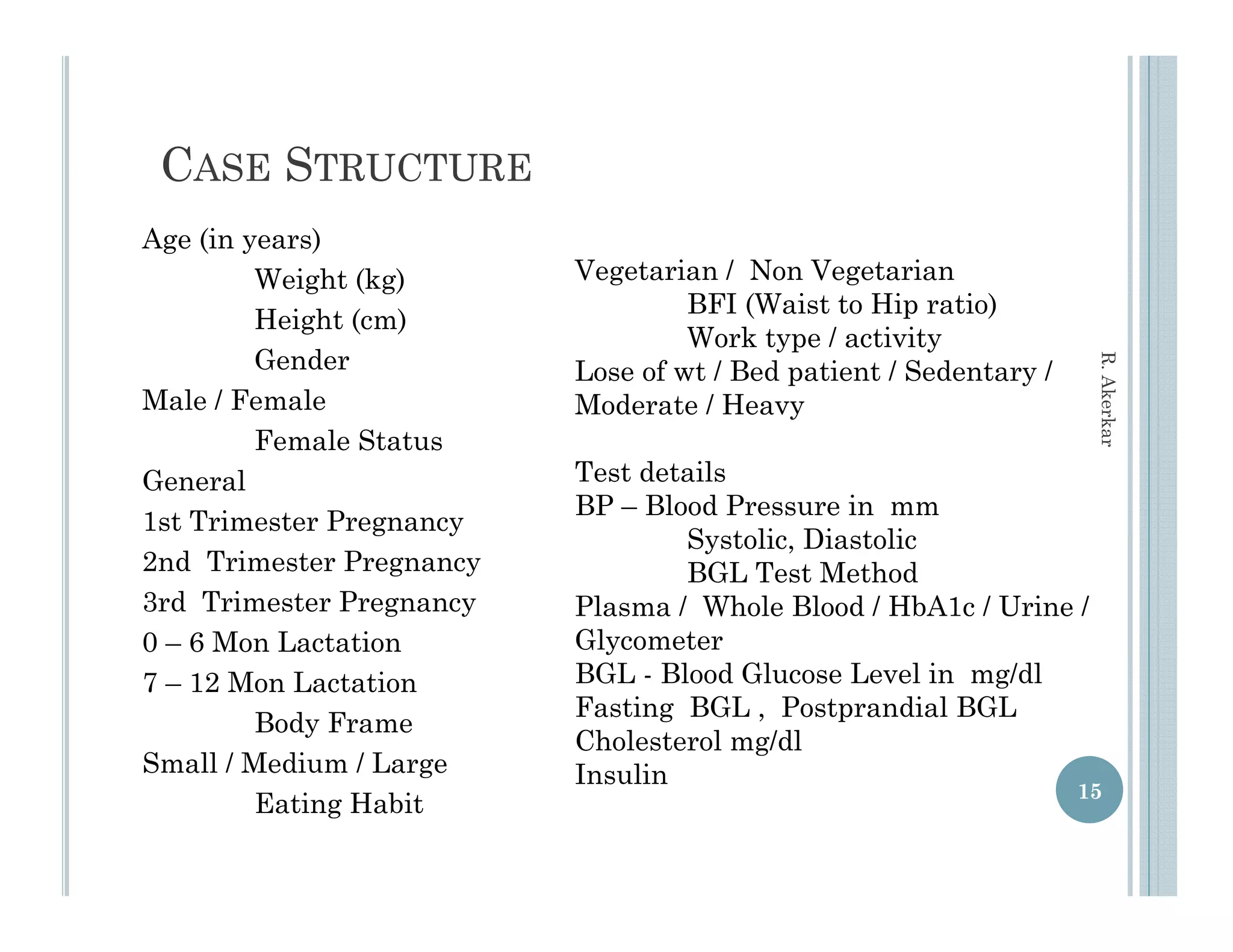
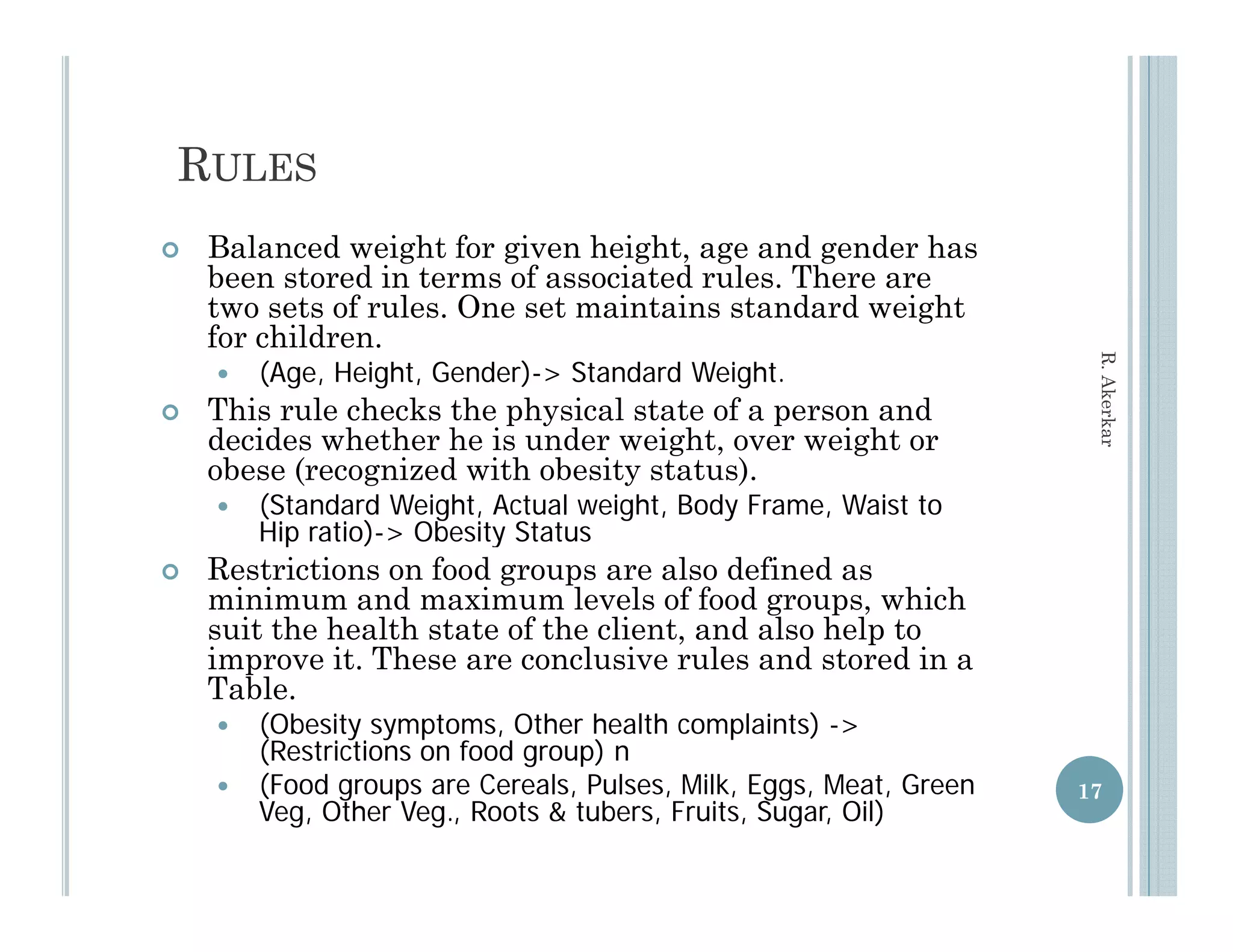
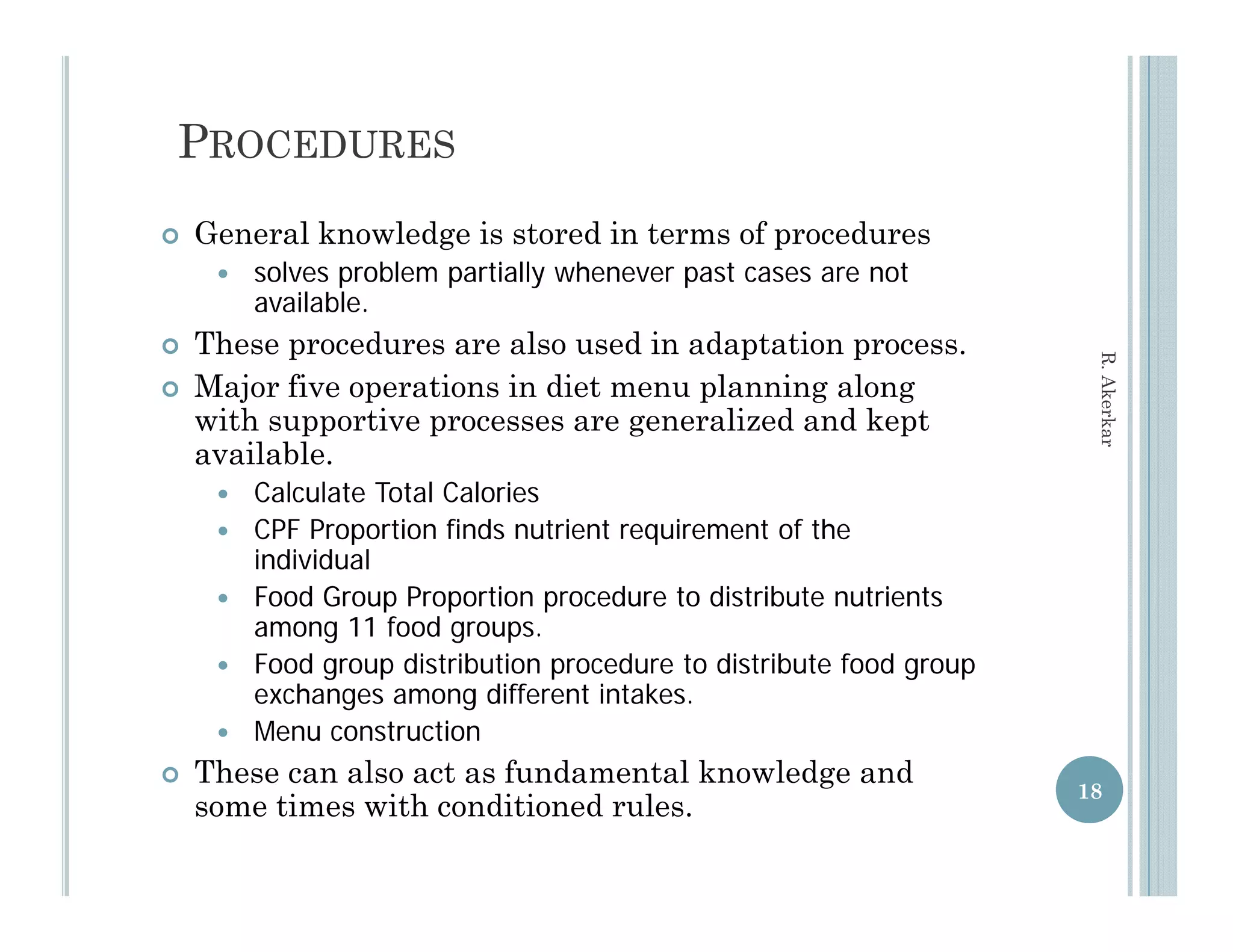
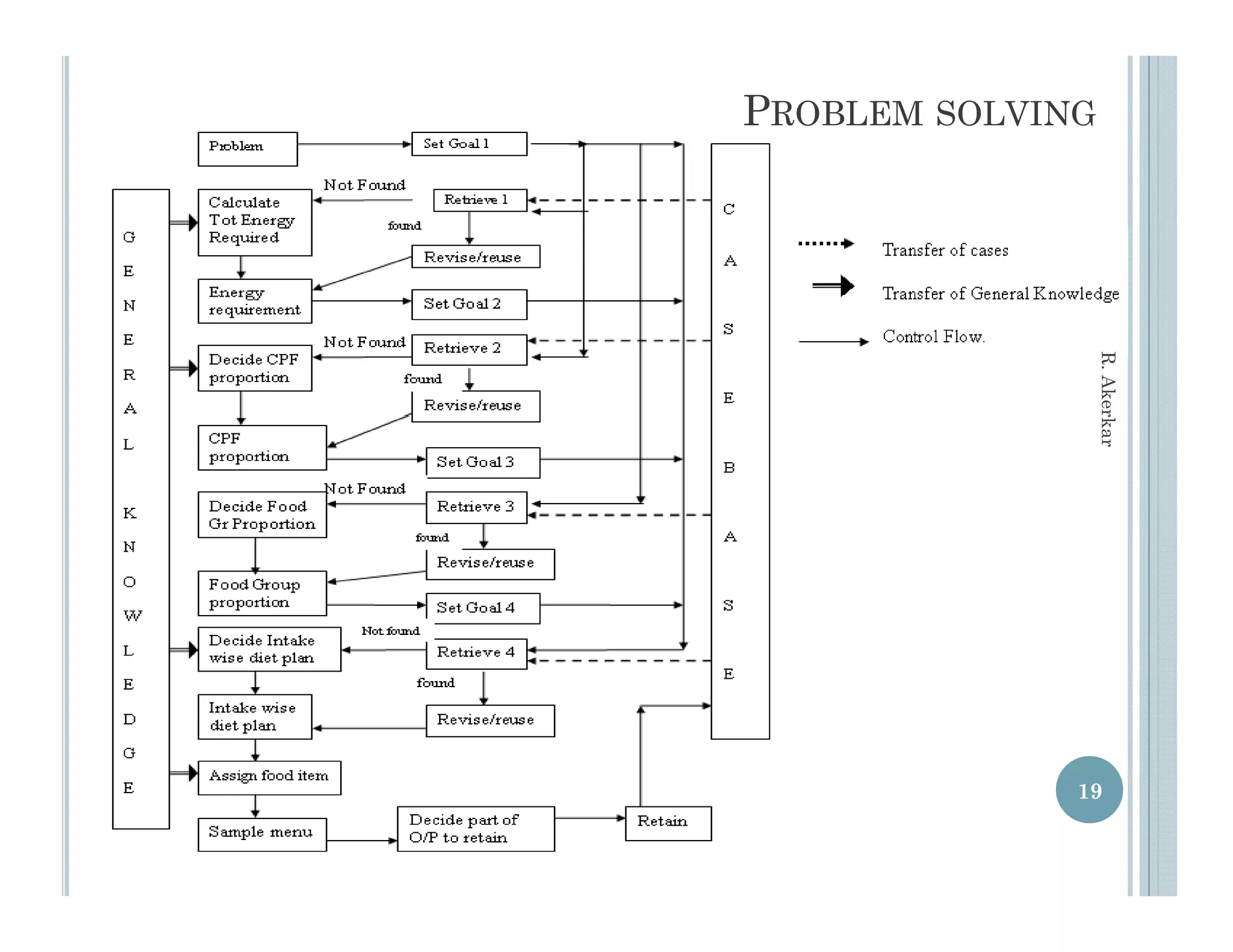
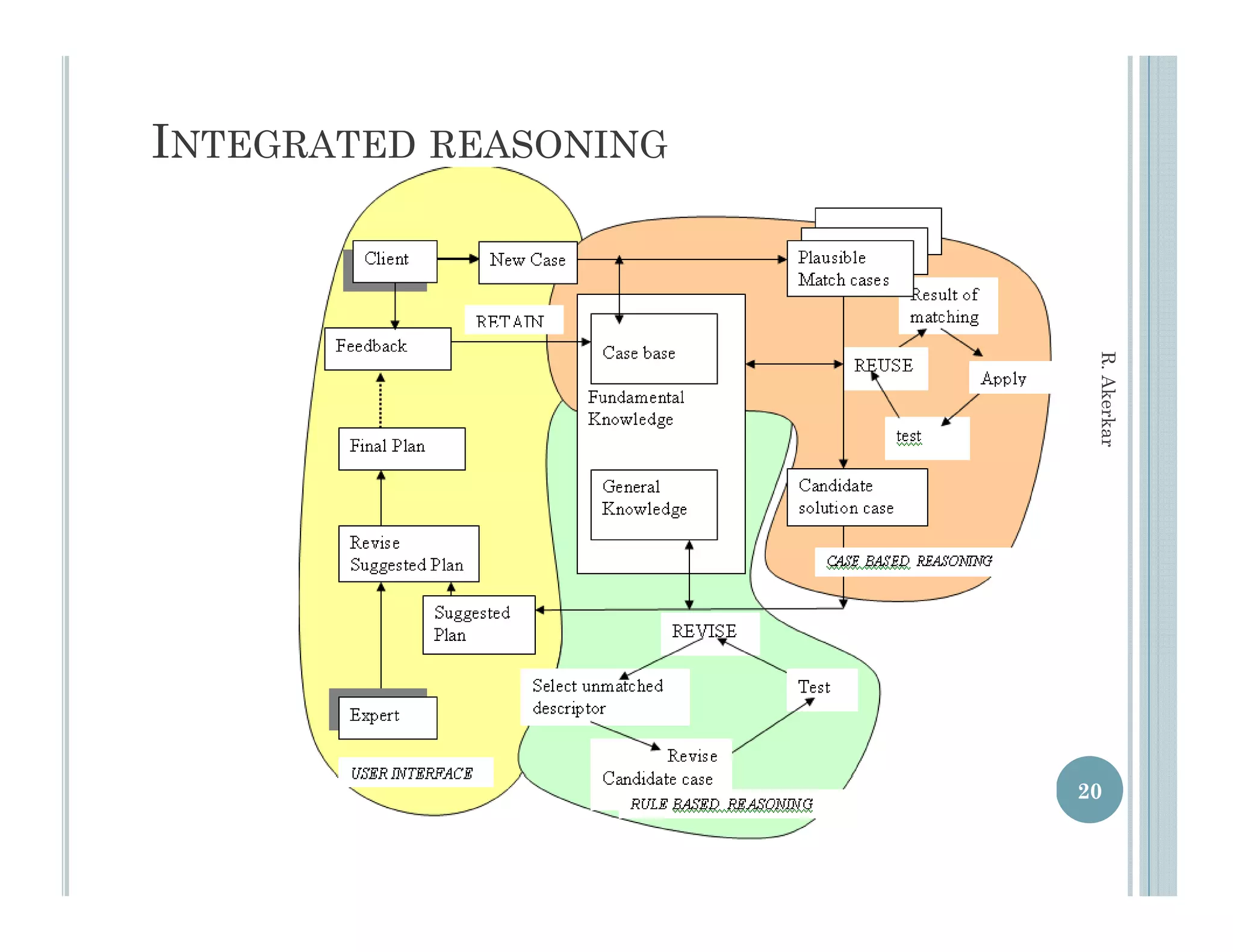
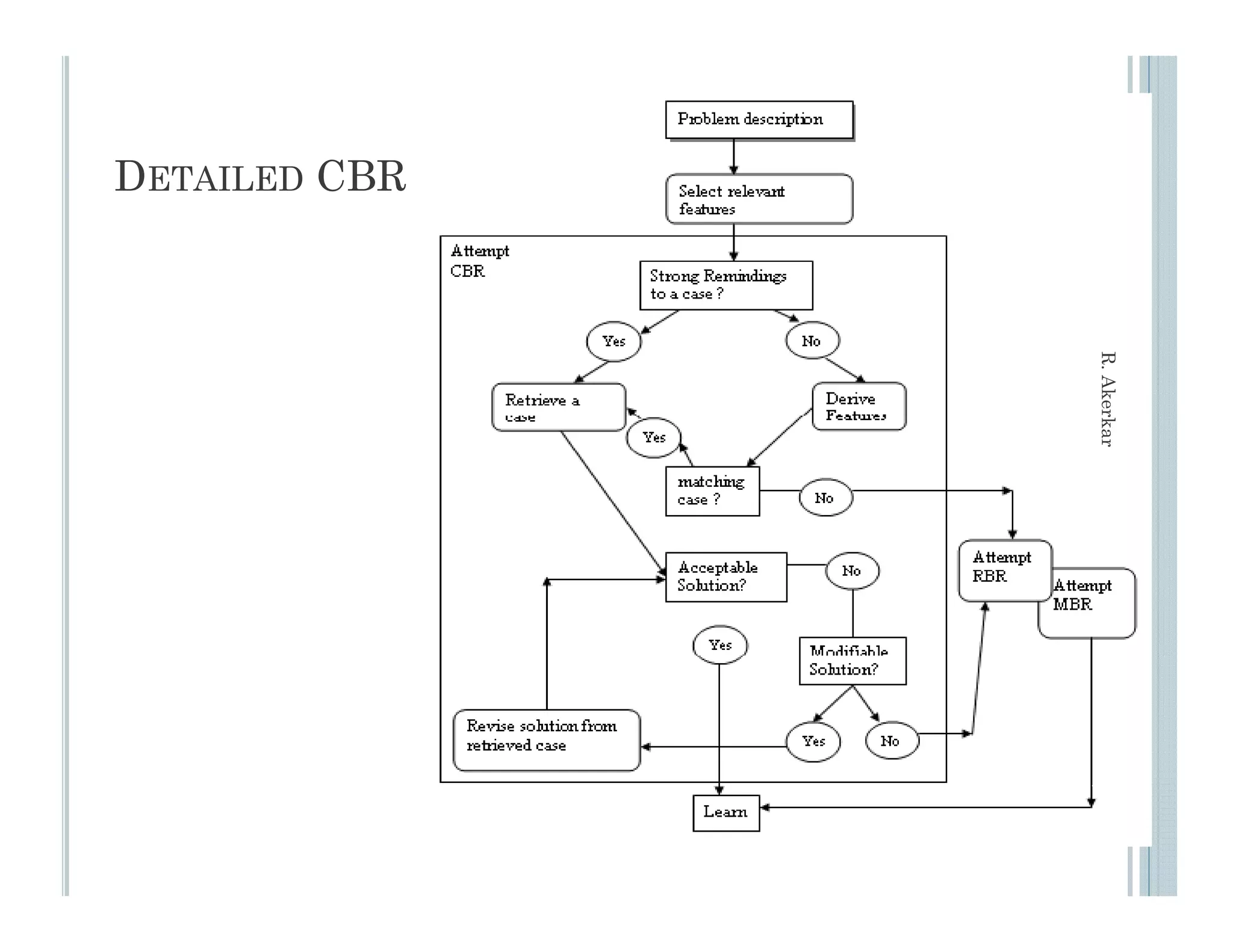
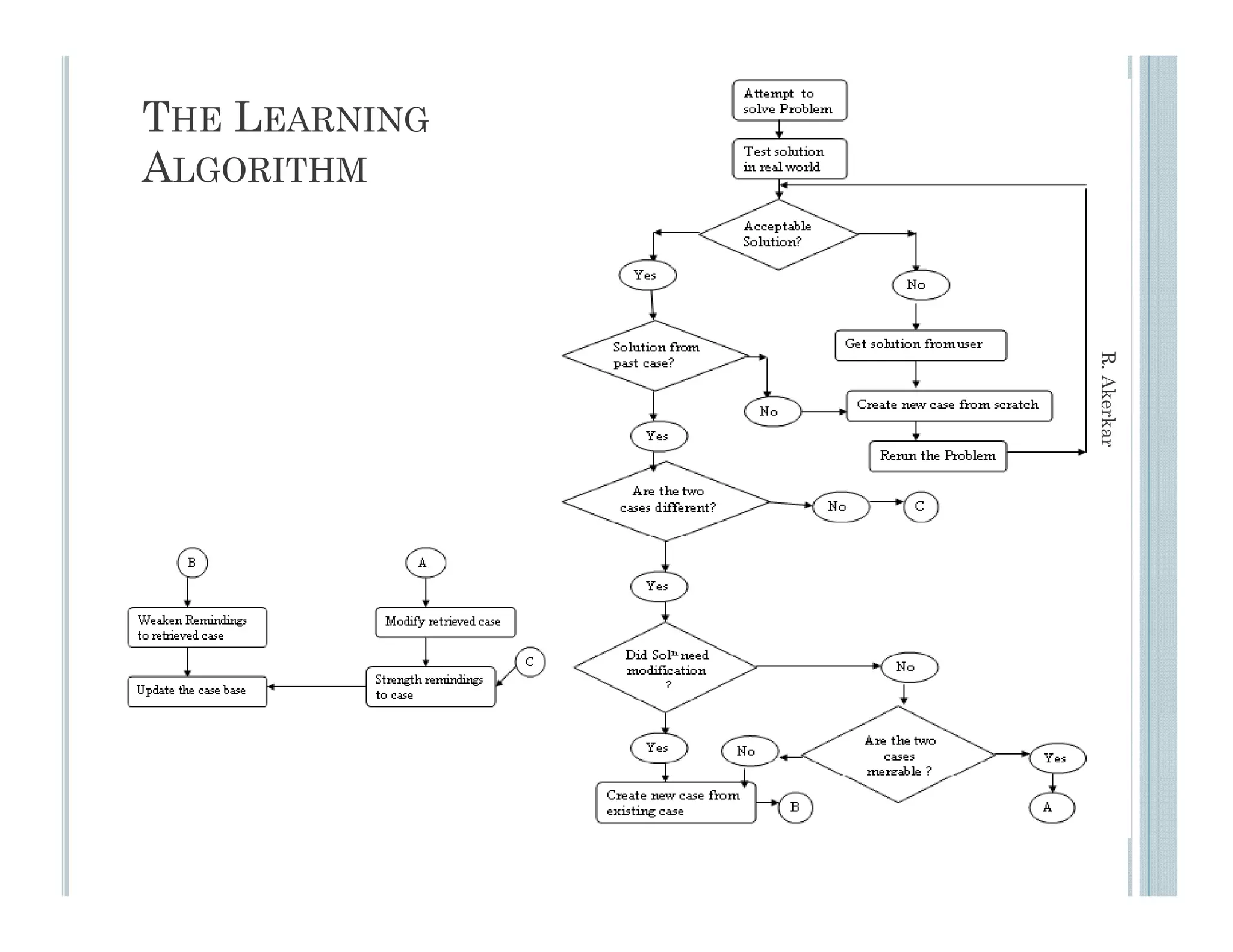
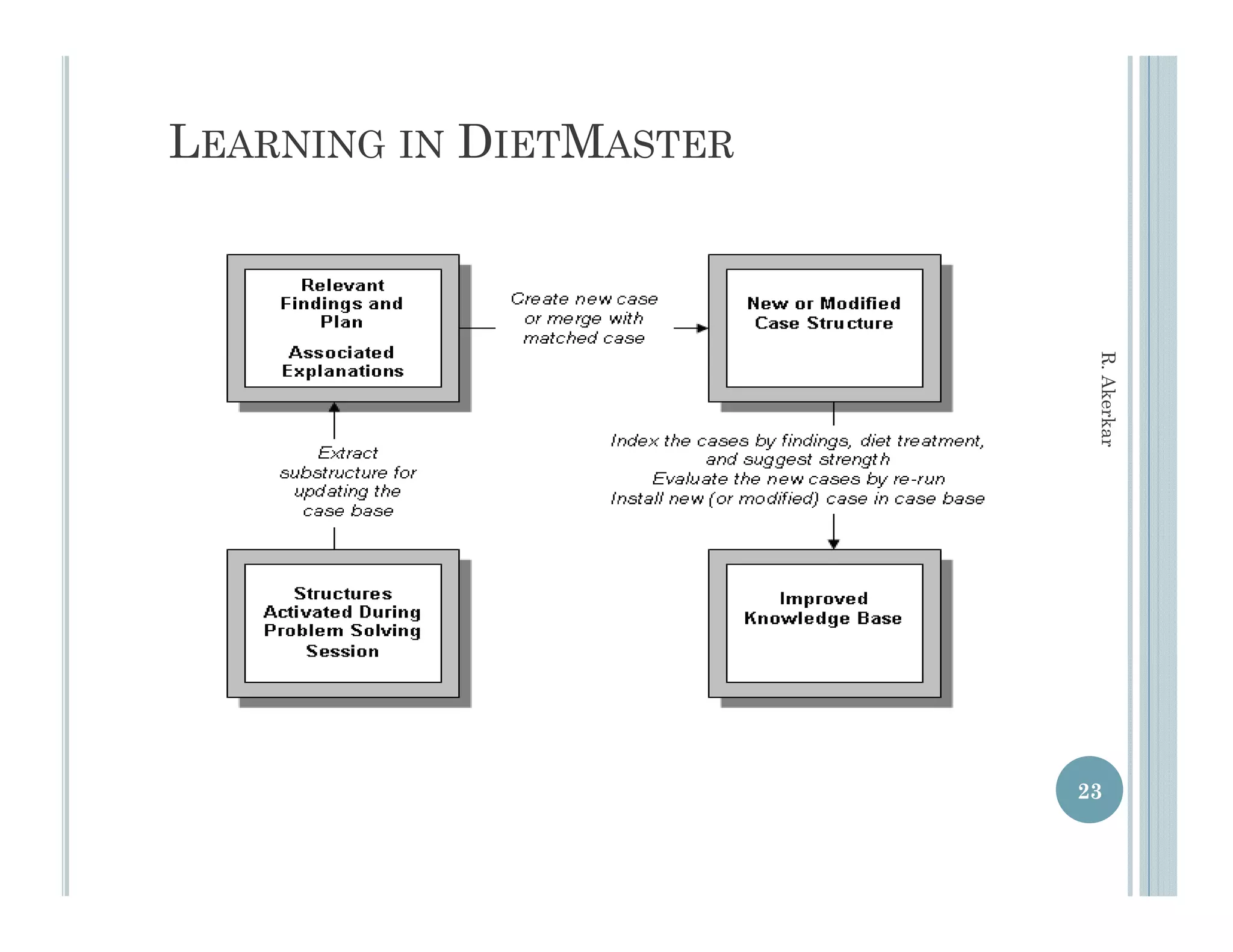
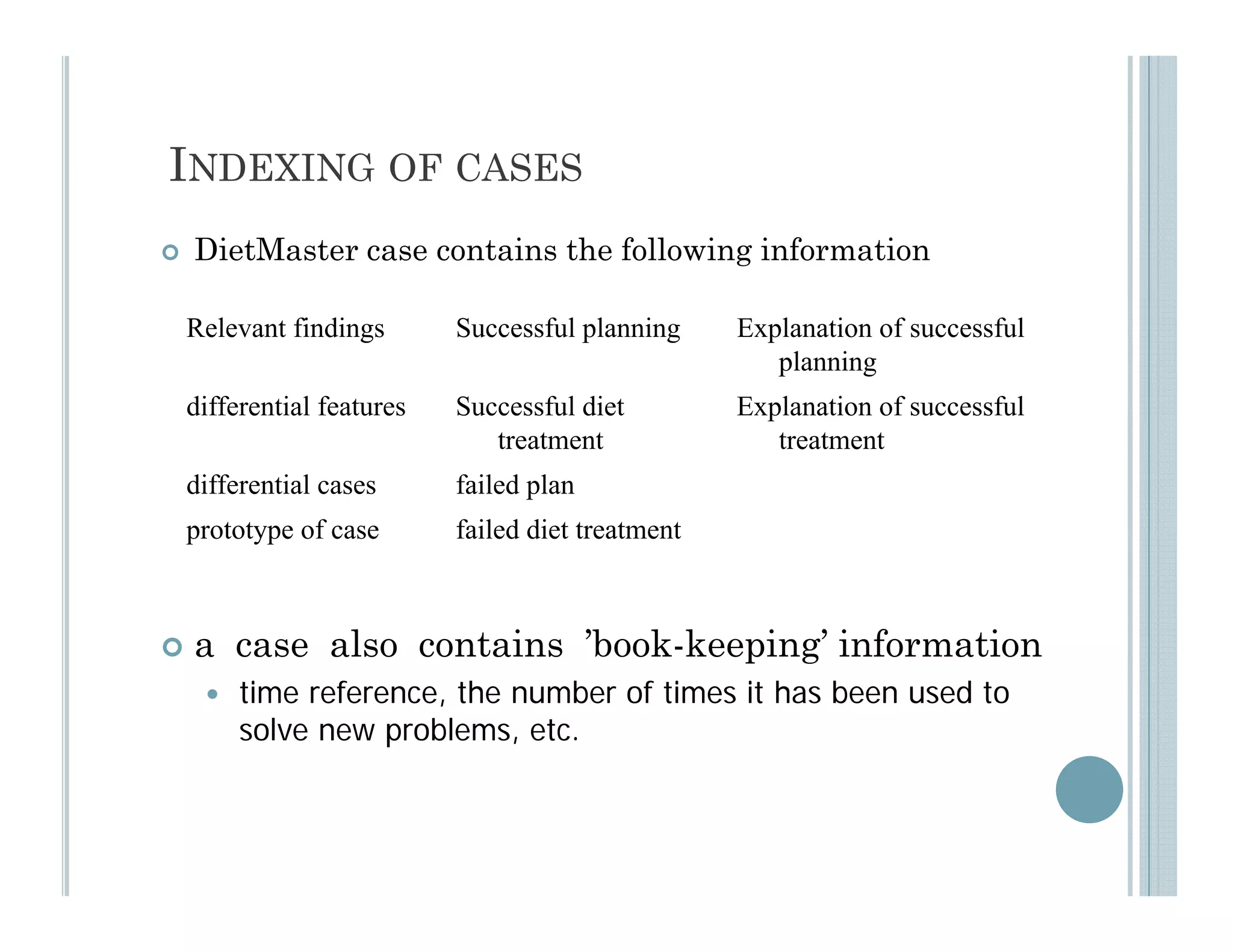
This document discusses using case-based reasoning for diet menu planning. It provides an overview of related work using CBR for domains like psychiatry and Alzheimer's care. It then describes DietMaster, a knowledge-intensive CBR system for diet menu planning that uses domain knowledge from experts. DietMaster's architecture and functional components are explained, including its representation of knowledge through rules and cases. Finally, the structures for input cases, cases in process, and output/learned cases are defined.