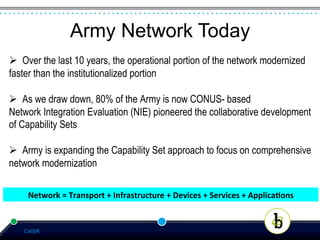
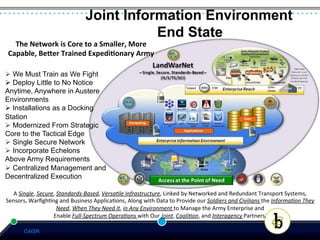
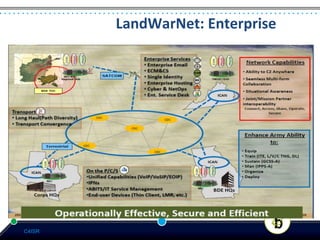
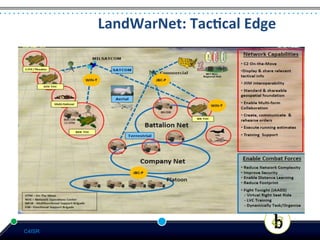
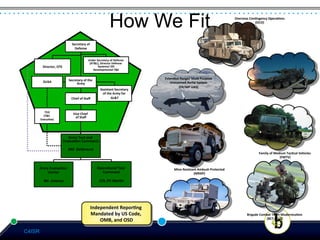
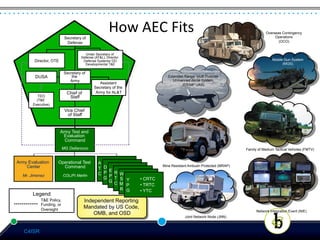
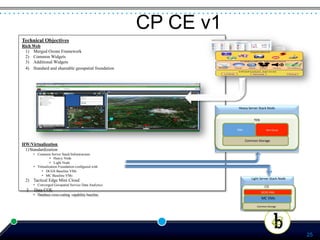
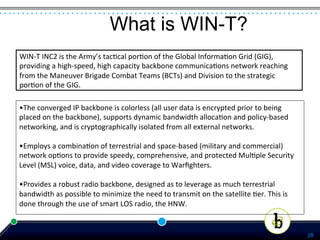
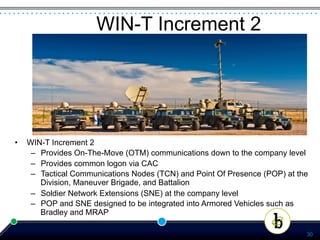
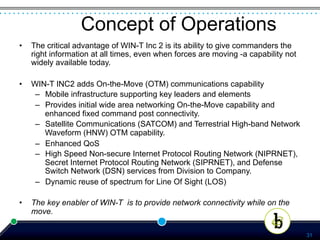
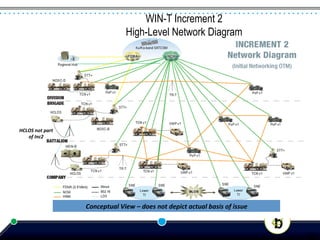
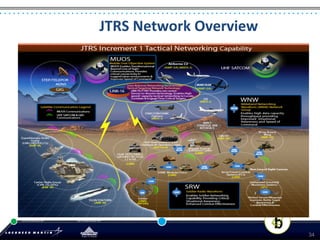
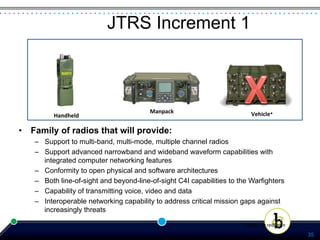
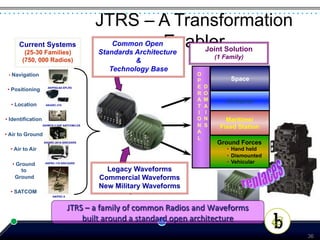
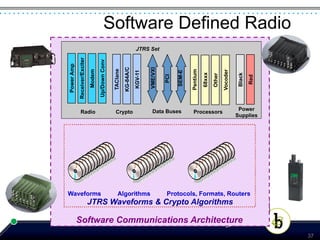
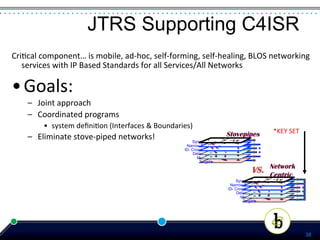
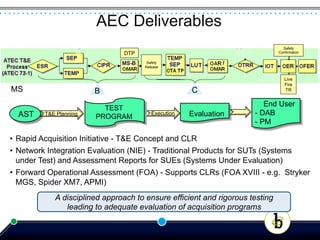
The document presents an agenda for a panel discussion on the integration of command, control, communications, computer, intelligence, surveillance, and reconnaissance (C4ISR) systems within the Army, highlighting key modernization objectives and challenges. It emphasizes the necessity for network modernization to maintain military superiority while addressing the evolving technological landscape. The document outlines the roles of various Army testing and evaluation commands and the specific programs under evaluation, such as the tactical portion of the Global Information Grid and the Joint Tactical Radio Systems.