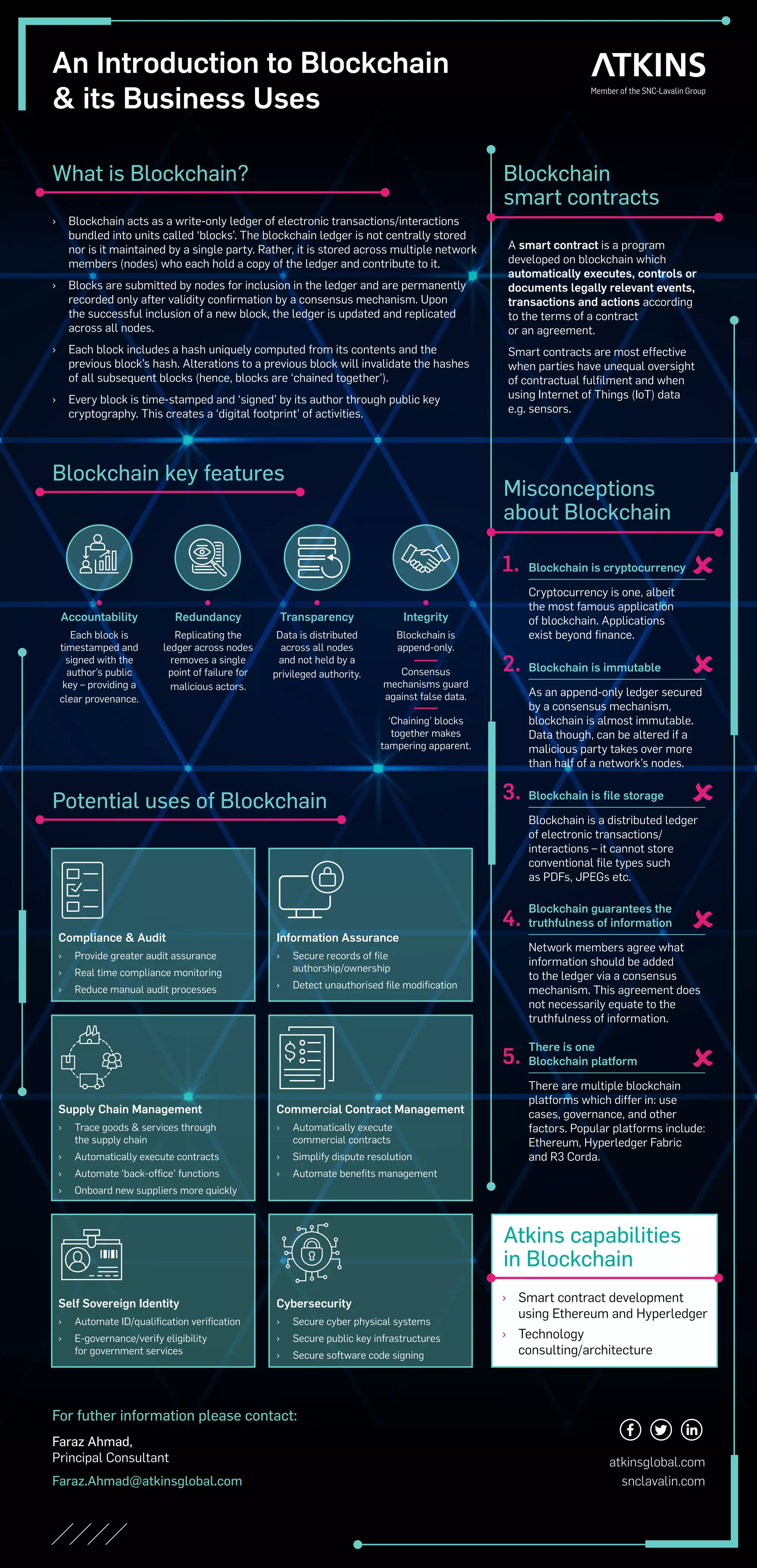
The document provides an overview of blockchain technology and its business applications, focusing on smart contracts, which automatically execute agreements based on pre-defined conditions. It discusses key features of blockchain, such as accountability, redundancy, transparency, and integrity, while addressing common misconceptions about the technology. Additionally, it outlines potential uses for blockchain in areas like compliance, supply chain management, and cybersecurity.