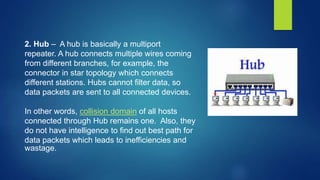
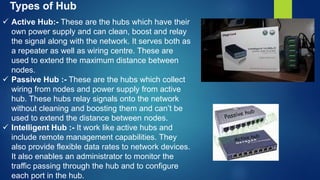
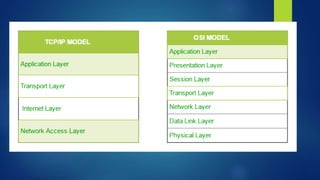
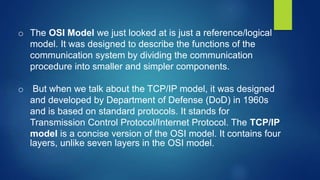
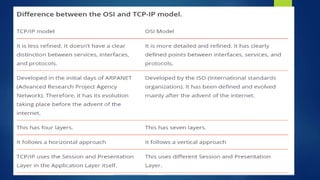
Computer networking involves connecting computing devices together to share data. It uses both hardware and software. There are different types of computer networks classified by their geographic reach, such as local area networks (LANs) within a single building and wide area networks (WANs) spanning cities or countries. Basic network designs are client-server, with centralized server computers accessed by client devices, and peer-to-peer where all devices have equal functions. Common network devices include switches, hubs, routers, gateways, and bridges which help direct data traffic and establish connections within and between networks. TCP/IP is a fundamental communications protocol used to connect devices on the internet and private networks.