The document discusses Augeas, a configuration management tool designed to edit configuration files programmatically while handling various file formats in their native forms. It outlines how to disable 'permitrootlogin' in SSH configuration using commands, introduces the augtool and augmatch utilities for managing and viewing configuration files, and provides examples of their usage. Additionally, it highlights opportunities for contributions to improve documentation and expand language bindings.

![Disable PermitRootLogin in sshd_config
$ sed -r 's/PermitRootLogin yes/PermitRootLogin no/'
$ sed -r 's/(PermitRootLogin[ t]+)yes/1no/'](https://image.slidesharecdn.com/augeas-180206160502/85/Augeas-5-320.jpg)
![Disable PermitRootLogin in sshd_config
$ sed -r 's/PermitRootLogin yes/PermitRootLogin no/'
$ sed -r 's/(PermitRootLogin[ t]+)yes/1no/'
$ sed -r 's/(PermitRootLogin[ t]+)[a-z]+/1no/'](https://image.slidesharecdn.com/augeas-180206160502/85/Augeas-6-320.jpg)
![Disable PermitRootLogin in sshd_config
$ sed -r 's/PermitRootLogin yes/PermitRootLogin no/'
$ sed -r 's/(PermitRootLogin[ t]+)yes/1no/'
$ sed -r 's/(PermitRootLogin[ t]+)[a-z]+/1no/'
$ grep PermitRootLogin /etc/ssh/sshd_config
# PermitRootLogin no](https://image.slidesharecdn.com/augeas-180206160502/85/Augeas-7-320.jpg)

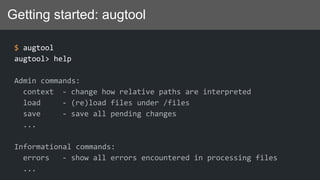
![Getting started: augtool
$ augtool --help
Usage: augtool [OPTIONS] [COMMAND]
-b, --backup preserve originals of modified files with
extension '.augsave'
-r, --root ROOT use ROOT as the root of the filesystem
-t, --transform XFM add a file transform
-l, --load-file FILE load individual FILE in the tree
-f, --file FILE read commands from FILE
-L, --noload do not load any files into the tree on
startup
-A, --noautoload do not autoload modules from the search path](https://image.slidesharecdn.com/augeas-180206160502/85/Augeas-21-320.jpg)
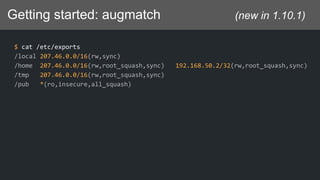
![Getting started: augmatch (new in 1.10.1)
$ docker pull lutter/augmatch
$ docker run -ti lutter/augmatch
/ # augmatch --help
Usage: augmatch [OPTIONS] FILE
Print the contents of a file as parsed by augeas.
Options:
-l, --lens LENS use LENS to transform the file
-m, --match EXPR start printing where nodes match EXPR
-e, --exact print only exact matches
...](https://image.slidesharecdn.com/augeas-180206160502/85/Augeas-22-320.jpg)

![Getting started: augmatch (new in 1.10.1)
$ augmatch /etc/exports
dir[1] = /local
dir[1]/client = 207.46.0.0/16
dir[1]/client/option[1] = rw
dir[1]/client/option[2] = sync
dir[2] = /home
dir[2]/client[1] = 207.46.0.0/16
dir[2]/client[1]/option[1] = rw
dir[2]/client[1]/option[2] = root_squash
dir[2]/client[1]/option[3] = sync
dir[2]/client[2] = 192.168.50.2/32
dir[2]/client[2]/option[1] = rw
dir[2]/client[2]/option[2] = root_squash
...](https://image.slidesharecdn.com/augeas-180206160502/85/Augeas-24-320.jpg)
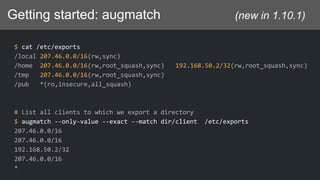
![Getting started: augmatch (new in 1.10.1)
$ cat /etc/exports
/local 207.46.0.0/16(rw,sync)
/home 207.46.0.0/16(rw,root_squash,sync) 192.168.50.2/32(rw,root_squash,sync)
/tmp 207.46.0.0/16(rw,root_squash,sync)
/pub *(ro,insecure,all_squash)
# List all clients to which we export the /home directory
$ augmatch -eom 'dir["/home"]/client ' /etc/exports
207.46.0.0/16
192.168.50.2/32](https://image.slidesharecdn.com/augeas-180206160502/85/Augeas-28-320.jpg)
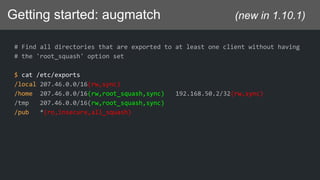
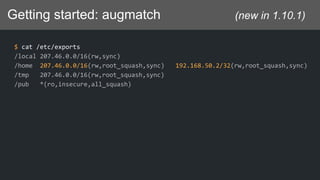
![Getting started: augmatch (new in 1.10.1)
# Find all directories that are exported to at least one client without having
# the 'root_squash' option set
$ cat /etc/exports
/local 207.46.0.0/16(rw,sync)
/home 207.46.0.0/16(rw,root_squash,sync) 192.168.50.2/32(rw,sync)
/tmp 207.46.0.0/16(rw,root_squash,sync)
/pub *(ro,insecure,all_squash)
$ augmatch -eom 'dir[client[not(option = "root_squash")]]' /etc/exports
/local
/home
/pub](https://image.slidesharecdn.com/augeas-180206160502/85/Augeas-30-320.jpg)
![Getting started: augmatch (new in 1.10.1)
# How match dir[client[not(option = "root_squash")]] works
$ augmatch /etc/exports
dir[1] = /local
dir[1]/client = 207.46.0.0/16
dir[1]/client/option[1] = rw
dir[1]/client/option[2] = sync
dir[2] = /home
dir[2]/client[1] = 207.46.0.0/16
dir[2]/client[1]/option[1] = rw
dir[2]/client[1]/option[2] = root_squash
dir[2]/client[1]/option[3] = sync
...](https://image.slidesharecdn.com/augeas-180206160502/85/Augeas-31-320.jpg)
![Idempotent change
$ augtool print /files/etc/exports/dir["/home"]/client[1]
/files/etc/exports/dir[2]/client[1] = "207.46.0.0/16"
/files/etc/exports/dir[2]/client[1]/option[1] = "rw"
/files/etc/exports/dir[2]/client[1]/option[2] = "root_squash"
/files/etc/exports/dir[2]/client[1]/option[3] = "sync"](https://image.slidesharecdn.com/augeas-180206160502/85/Augeas-34-320.jpg)
![Idempotent change
def ensure_client(dir, client, opts)
Augeas::open(nil, nil, Augeas::NO_MODL_AUTOLOAD) do |aug|
aug.transform(lens: "Exports.lns", incl: "/etc/exports")
aug.context("/files/etc/exports")
aug.load
aug.set("/scratch/client", client)
options.each {|opt| aug.set("/scratch/client/option[last()+1]", opt)}
if aug.match("dir['#{dir}']").empty?
aug.set("dir[last()+1]", dir)
end
...
aug.mv("/scratch", "dir['#{dir}']/client['#{client}]")
aug.save
end
end](https://image.slidesharecdn.com/augeas-180206160502/85/Augeas-35-320.jpg)
![Idempotent change
def ensure_client(dir, client, opts)
Augeas::open(nil, nil, Augeas::NO_MODL_AUTOLOAD) do |aug|
aug.transform(lens: "Exports.lns", incl: "/etc/exports")
aug.context("/files/etc/exports")
aug.load
aug.set("/scratch/client", client)
options.each {|opt| aug.set("/scratch/client/option[last()+1]", opt)}
if aug.match("dir['#{dir}']").empty?
aug.set("dir[last()+1]", dir)
end
...
aug.mv("/scratch", "dir['#{dir}']/client['#{client}]")
aug.save
end
end](https://image.slidesharecdn.com/augeas-180206160502/85/Augeas-36-320.jpg)
![Idempotent change
def ensure_client(dir, client, opts)
Augeas::open(nil, nil, Augeas::NO_MODL_AUTOLOAD) do |aug|
aug.transform(lens: "Exports.lns", incl: "/etc/exports")
aug.context("/files/etc/exports")
aug.load
aug.set("/scratch/client", client)
options.each {|opt| aug.set("/scratch/client/option[last()+1]", opt)}
if aug.match("dir['#{dir}']").empty?
aug.set("dir[last()+1]", dir)
end
...
aug.mv("/scratch", "dir['#{dir}']/client['#{client}]")
aug.save
end
end](https://image.slidesharecdn.com/augeas-180206160502/85/Augeas-37-320.jpg)