This document contains a summary of 10 experiments conducted using Prolog. Each experiment includes the aim, logic, theory, and conclusion. The experiments cover topics like supports relationships between objects, defining family relationships, solving problems like the monkey banana problem and Tower of Hanoi, implementing search algorithms like depth-first search and breadth-first search, checking graph properties, checking if elements are in a list, and an example of an expert system mini-project.







![12
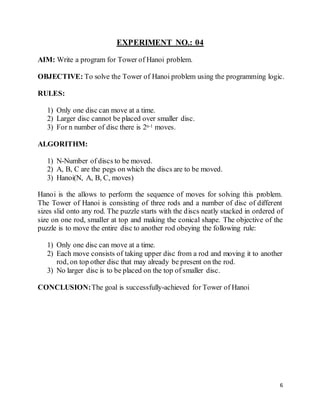
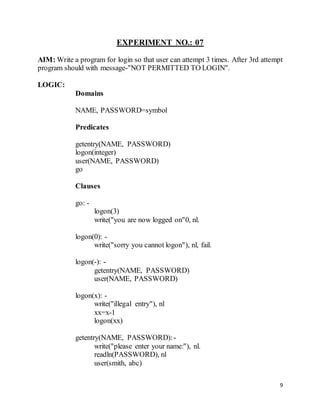
EXPERIMENT NO.:09
AIM: Write to see all element are present in the list or not.
OBJECTIVE:To study the conceptof list using PROLOG.
THEORY:
Link list is a sequence of the nodes. Each node has two part viz. node data and
pointer field. Pointer field points to the next node in the list. The last node's pointer
field contains NULL indicating that pointing to nothing. If first node pointer
consist field consist NULL it means that the link list consists of a single node.
LOGIC:
Domains
List=symbol*
Predicates
list(symbol, list)
Clauses
list(x, [H|-]): -
x=H
write("Element “, x," is present in the list"), nl
list(x, [-|T])
list(x, T),
list(x, T)
list(x, |]): write(x, "is not in the list"), fail.
CONCLUSION:Goal is successfulfor above mentioned aim.](https://image.slidesharecdn.com/artificialintelligencelabfile-160517204829/85/Artificial-Intelligence-Lab-File-13-320.jpg)
