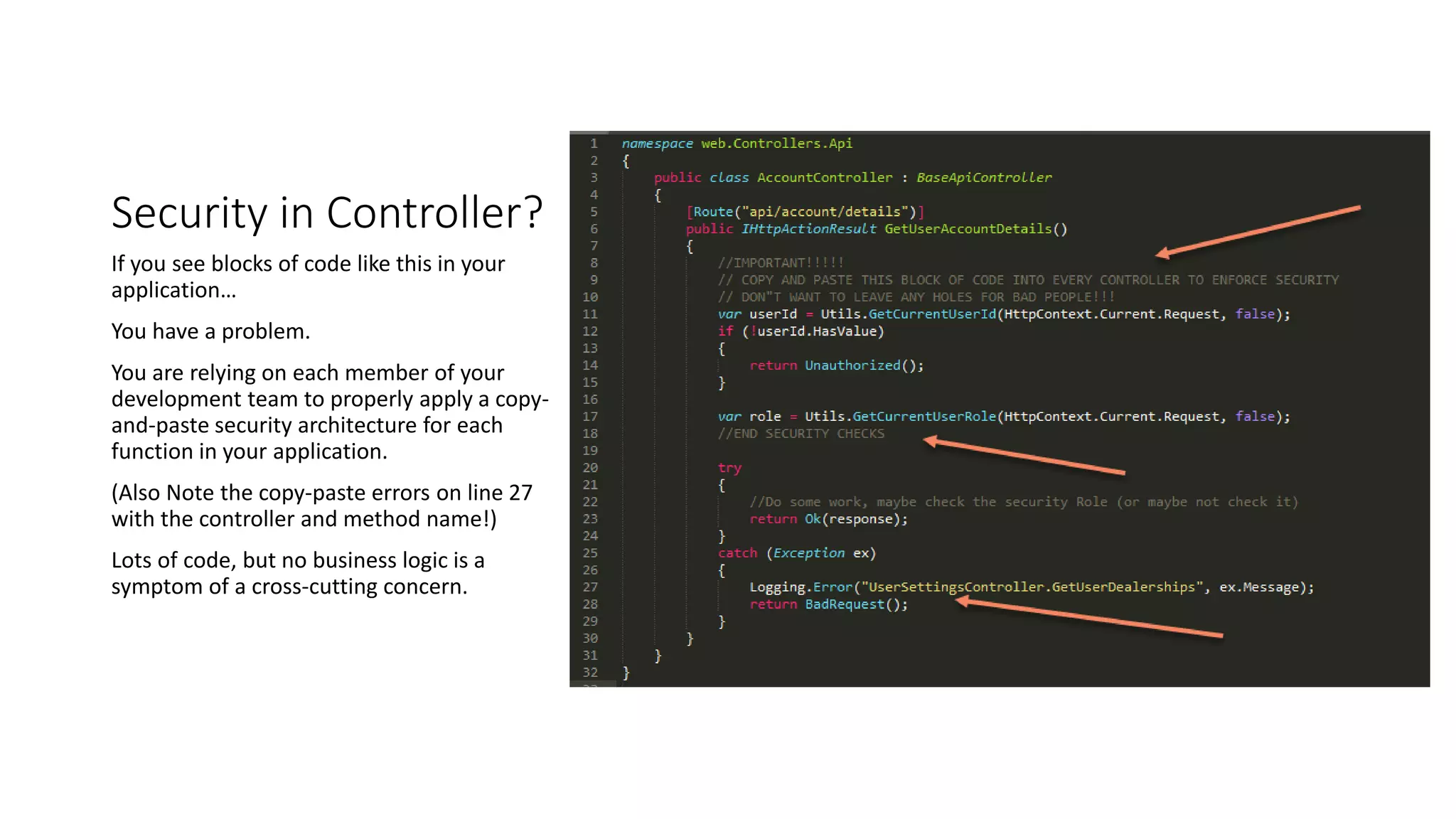
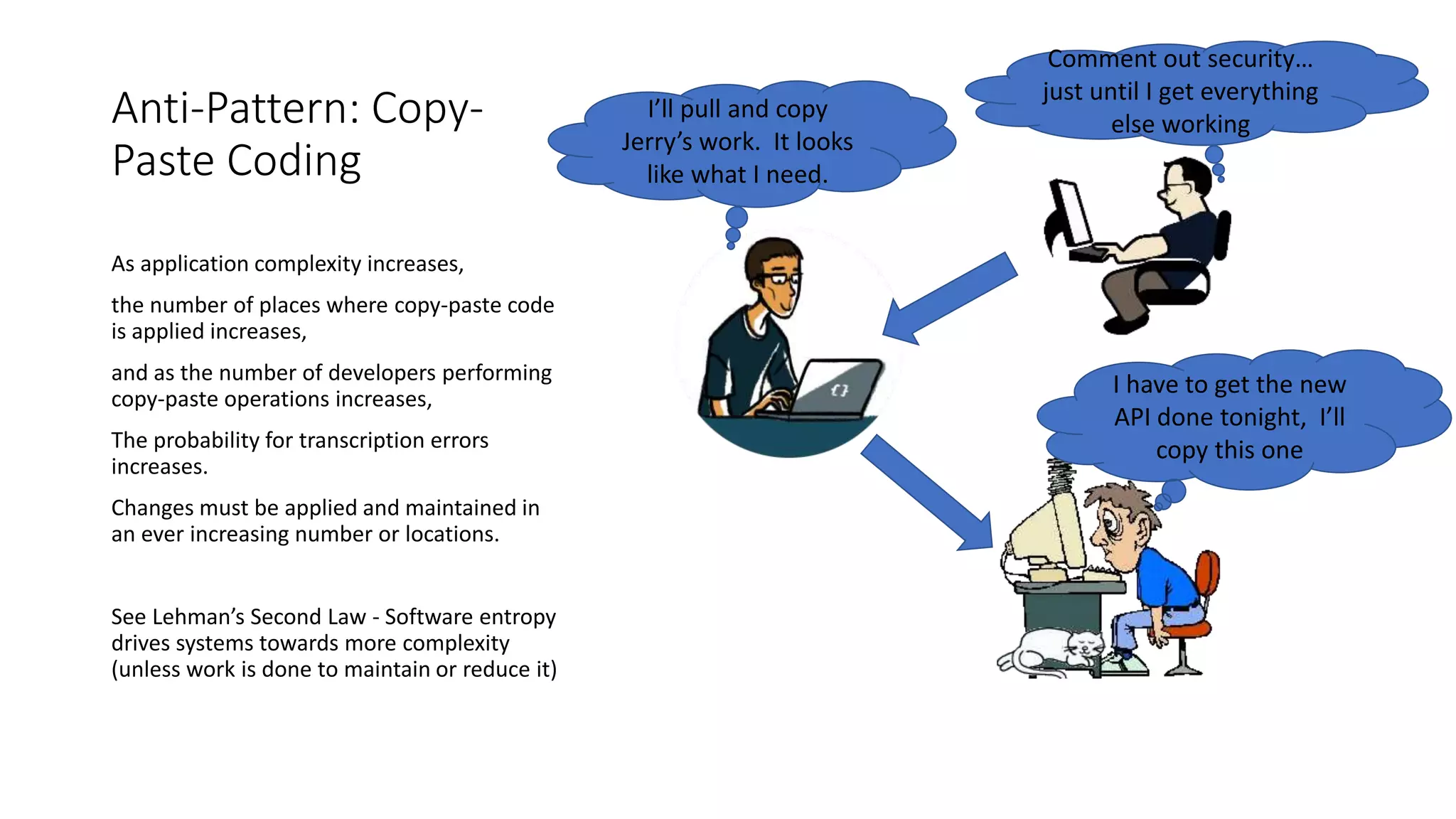
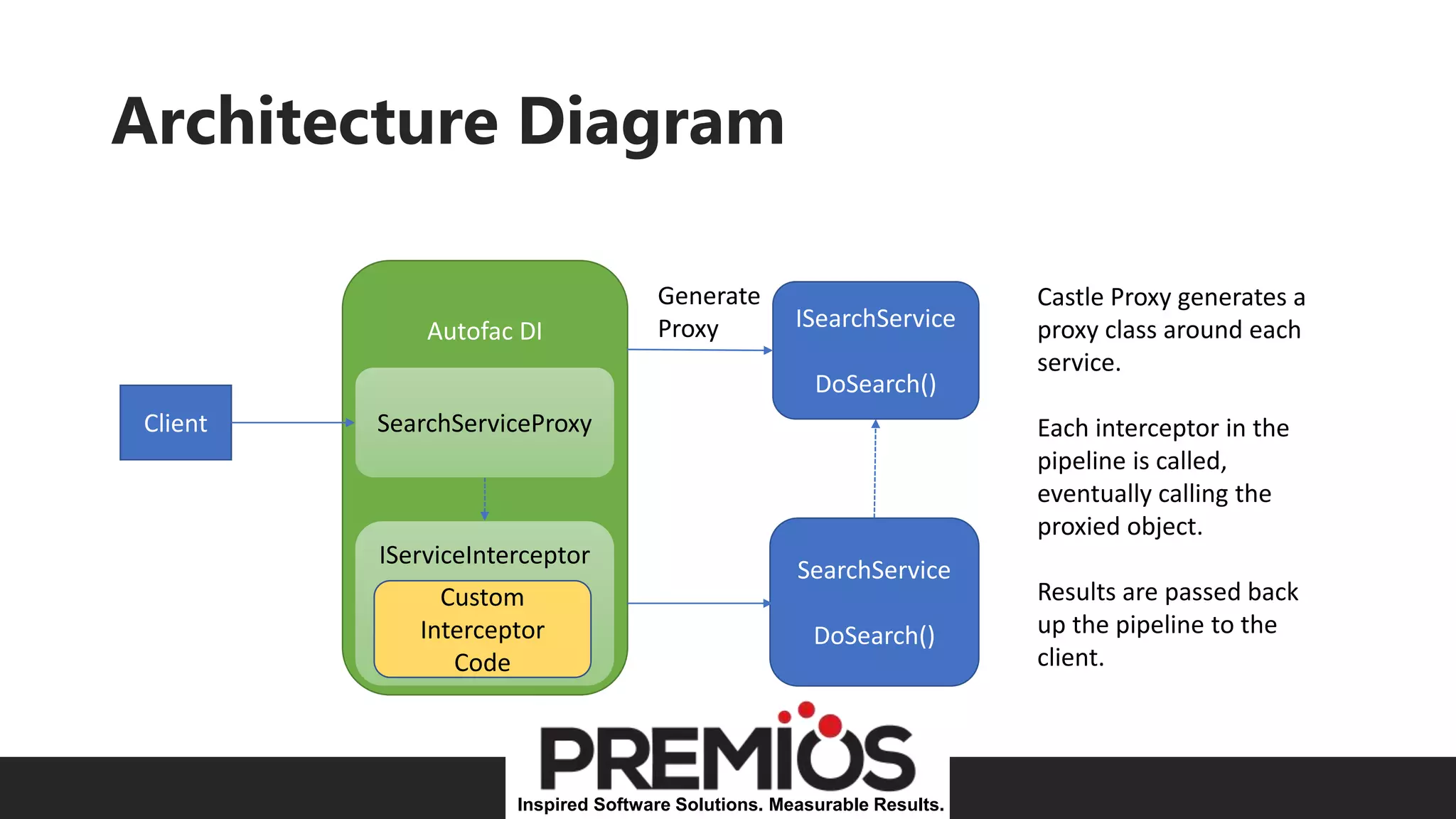
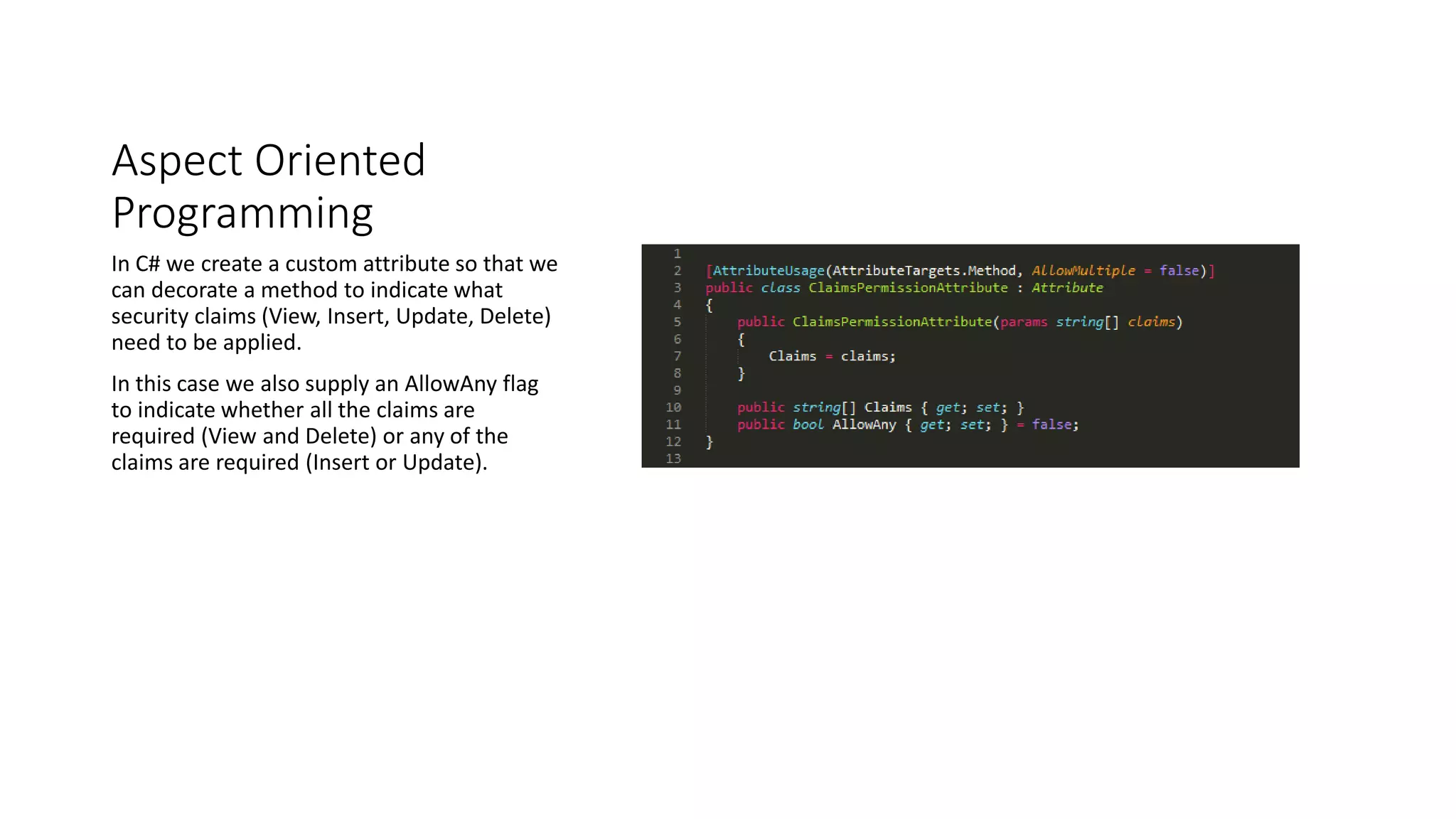
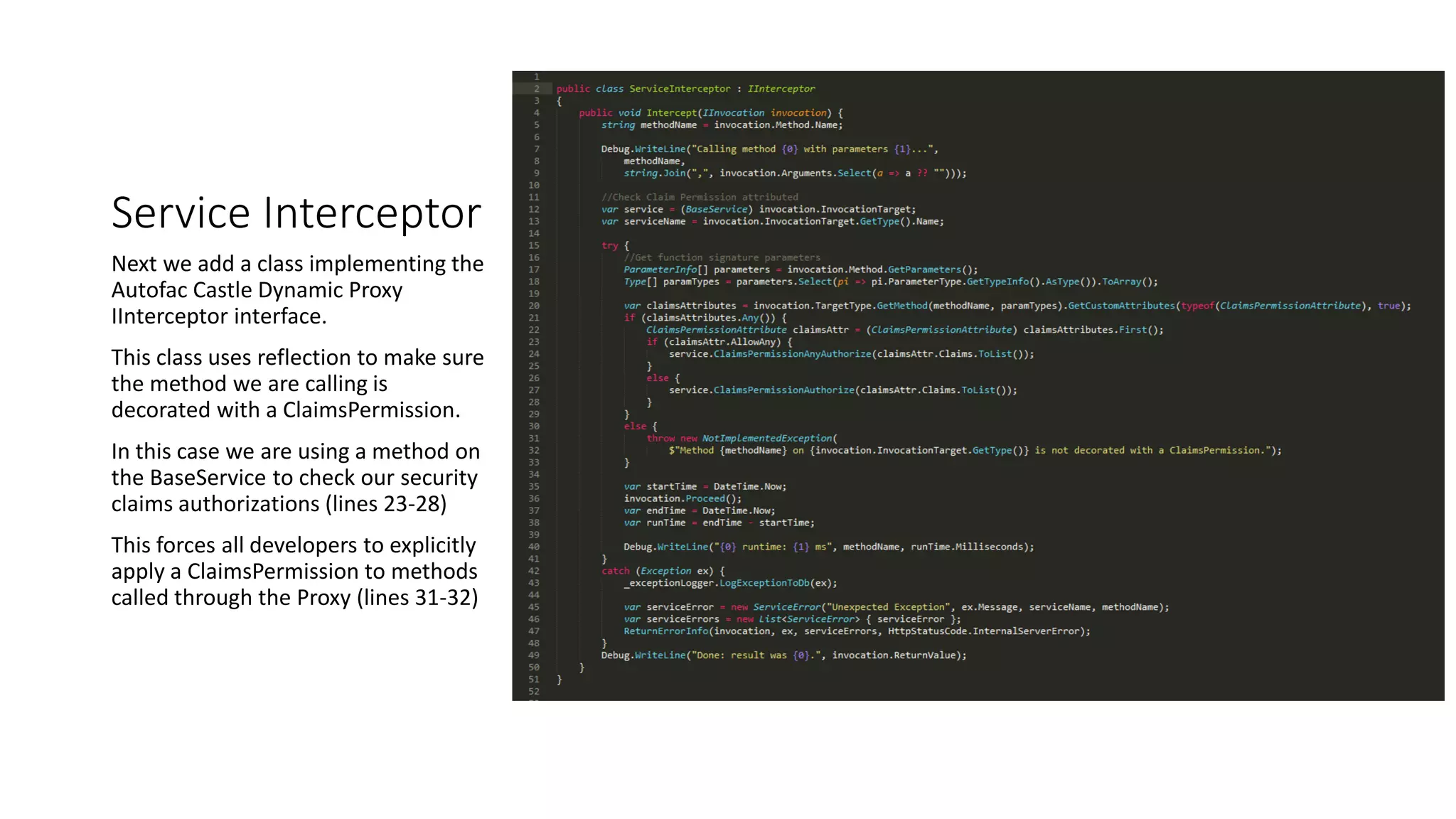
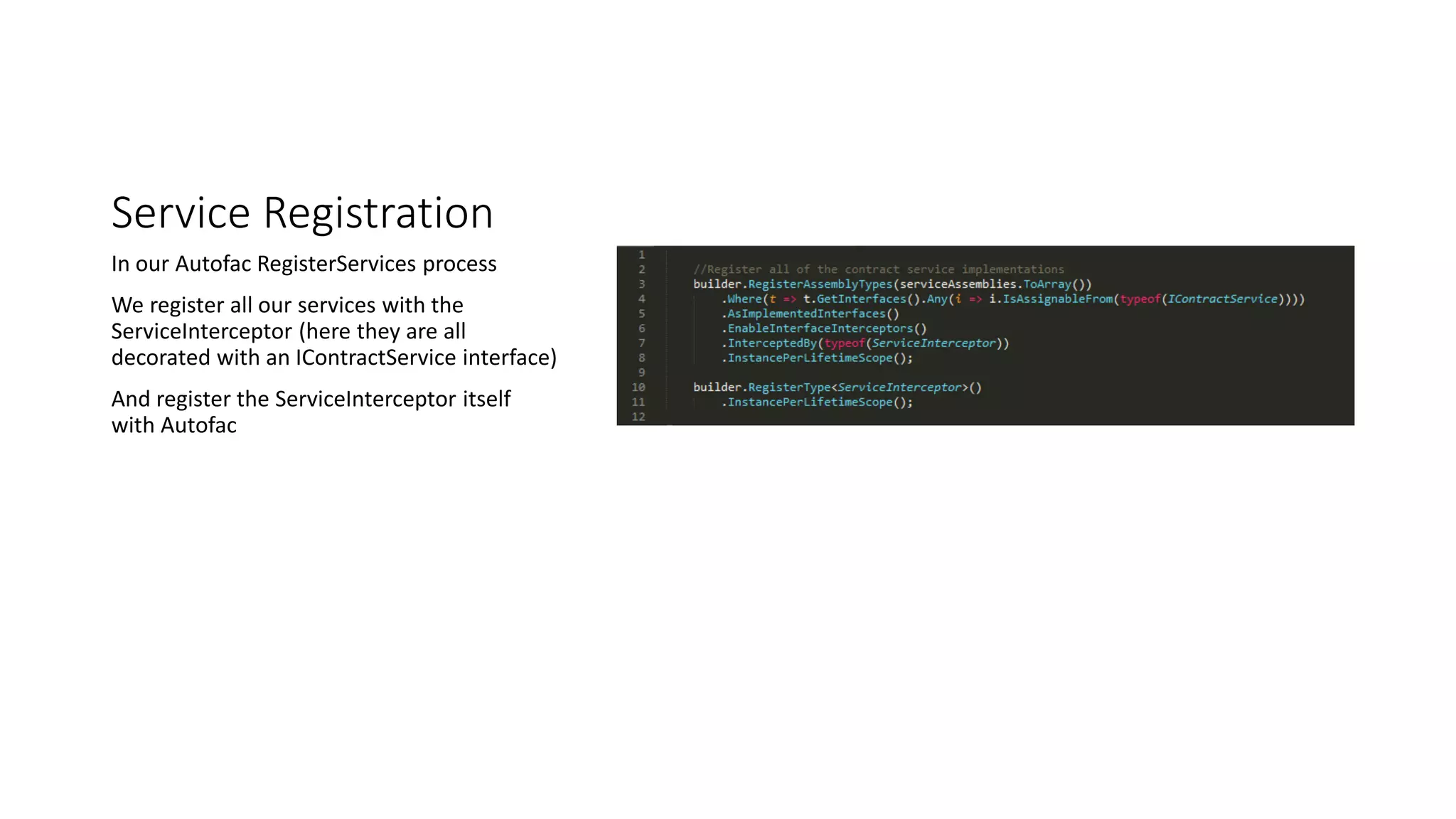
The document discusses architecting C# for managing cross-cutting concerns like security and logging through method interception using Castle Dynamic Proxy. It emphasizes the importance of architectural guidelines to reduce complexity and ensure compliance while avoiding common pitfalls like copy-paste coding. The use of aspect-oriented programming and method interception is proposed as a solution to enforce security and other concerns uniformly across an application.