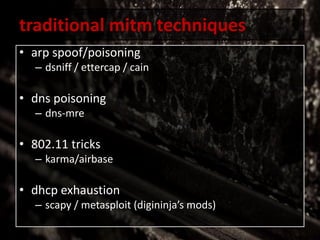
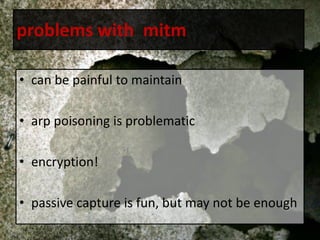
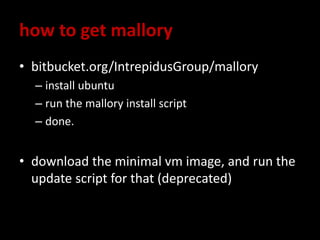
The document discusses the challenges and techniques of man-in-the-middle (MITM) attacks, highlighting tools like ARP spoofing, DNS poisoning, and the limitations of current methods due to encryption. It introduces 'Mallory,' a TCP MITM proxy that allows for packet manipulation and stream editing, with notes on installation and recent improvements to its GUI and functionality. However, it also addresses common problems users face, such as confusion in the rules and protocol configurations.


![[stop]
• @rossja
• algorythm@gmail.com](https://image.slidesharecdn.com/aliceandbobareeffd-170117171010/85/Alice-and-Bob-are-Eff-d-26-320.jpg)