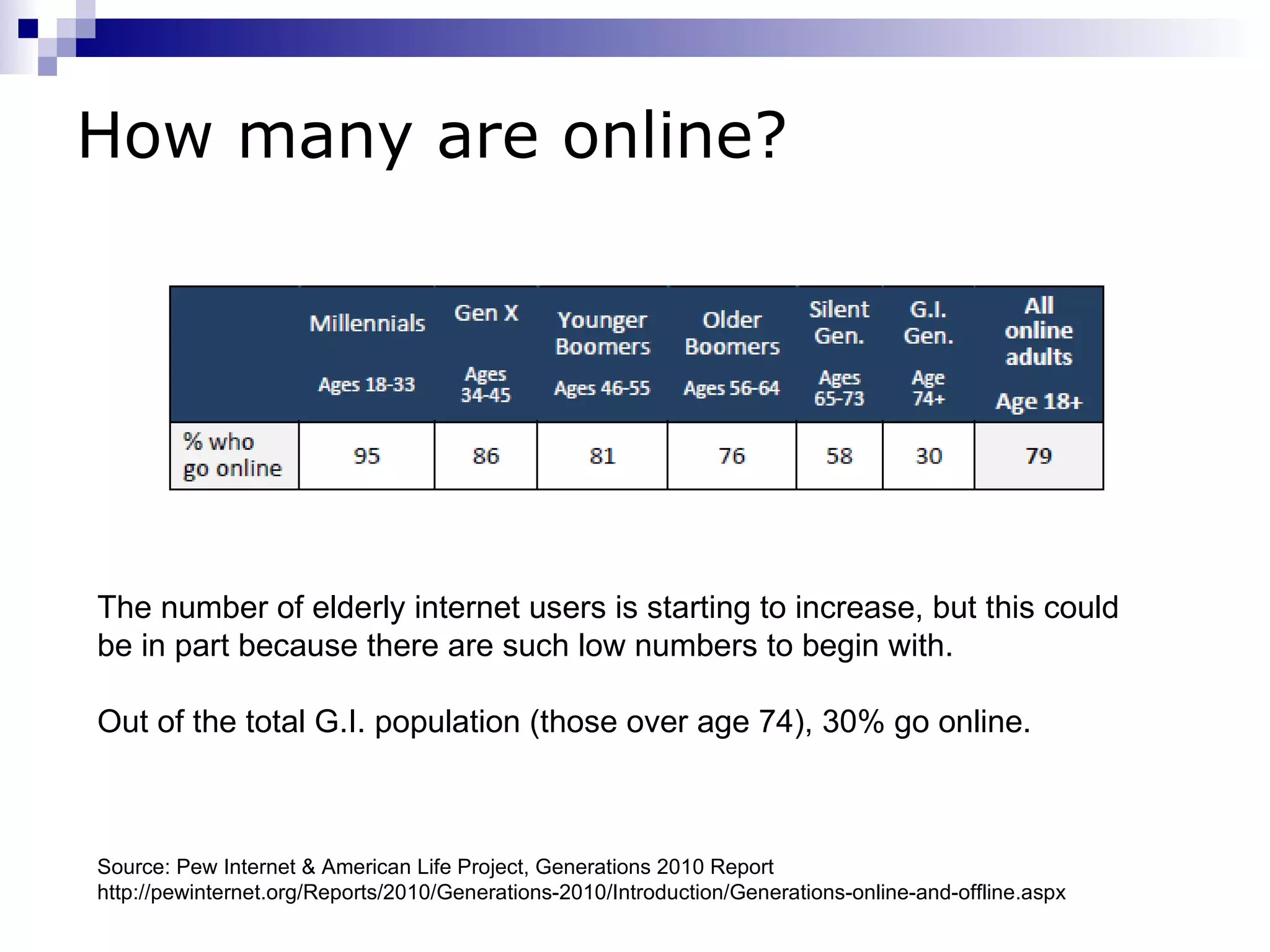
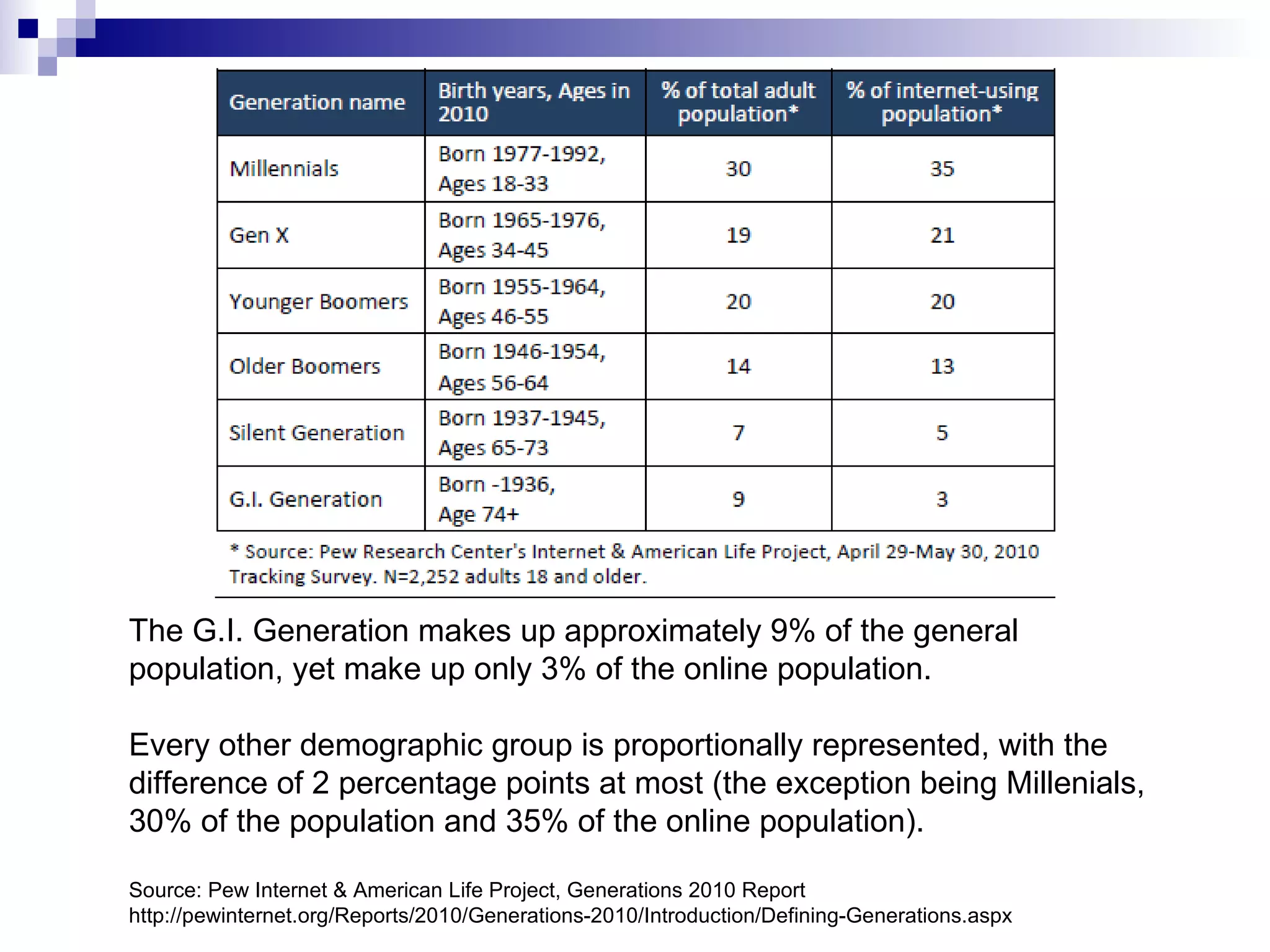
1) Only 30% of those over age 74 ("G.I. Generation") go online, much lower than other age groups which are proportionally represented.
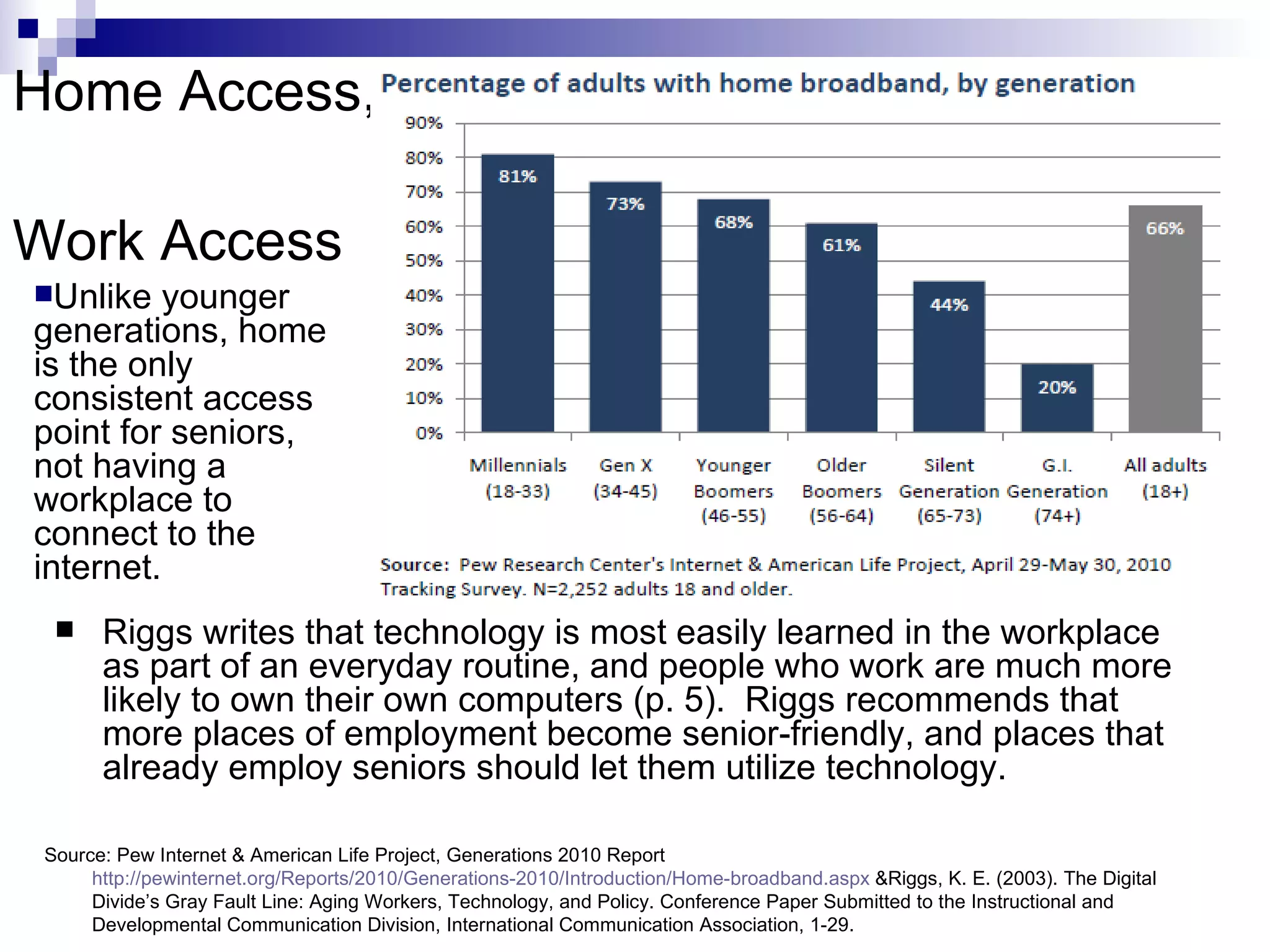
2) Unlike younger generations, seniors only have consistent home internet access and do not access the internet at work.
3) Senior internet use focuses more on research and checking email than social media or other online activities. However, social media use is rising among those 65+ to stay connected to others.