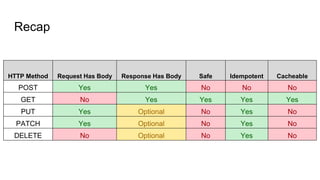
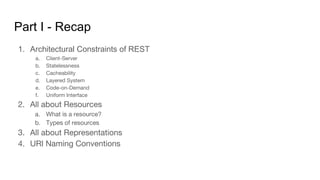
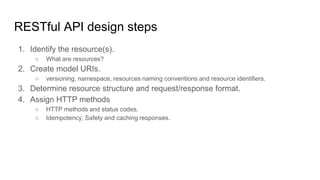
The document explores RESTful API design, detailing architectural constraints, resource identification, URI naming conventions, and request/response formats. It emphasizes the importance of versioning, organization through namespaces, and best practices for URI formatting, while also breaking down HTTP methods and status codes used in API interactions. An example application outlines resources and CRUD operations to demonstrate these principles in action.












![PATCH
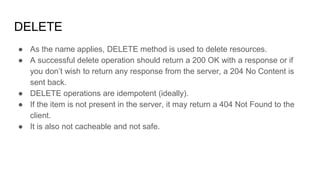
● It is used to partially update a resource.
● It cannot create a resource as it sends partial information only.
● PATCH applies a delta rather than updating the given resource entirely.
● A typical PATCH request is an array of partial modifications to the given resource.
● The array contains a request to update a particular portion of a given resource in the
following format.
[{ “op”: “replace”, “path”: “/email”, “value”: “new.email@example.org” }]
● op is operation, it can be remove, add, replace, move and copy.
● It includes the path to the field that you are changing and the value that needs to be
changed.
● Similar to PUT, PATCH requests are also idempotent, not safe and not cacheable.
JSON Patch standard -
https://tools.ietf.org/html/rfc6902](https://image.slidesharecdn.com/restdeepdivepartii-210204170131/85/A-Deep-Dive-into-RESTful-API-Design-Part-2-24-320.jpg)