The document outlines the agenda for the 8th demand seminar held by EXEM, including presentations on PostgreSQL Vacuum and MySQL locks. The PostgreSQL presentation covers the details of Vacuum including its behavior during updates, deletes, and different Vacuum commands. The MySQL presentation covers different types of locks in MySQL including global read locks, table locks, and string locks.
![Table of Agenda
© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
제 8회 수요 세미나
1. [PostgreSQL] Vacuum의 거의 모든 것 (4차)
2. [MySQL] Lock (1차)](https://image.slidesharecdn.com/8-160714105719/85/8-2-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[PostgreSQL] Vacuum의 거의 모든 것 (4차)
발표자: 연구컨텐츠팀 이근오](https://image.slidesharecdn.com/8-160714105719/85/8-3-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[PostgreSQL]
Vacuum의 거의 모든 것(4차)
Page Layout ( 1/2 )
Dump
0.](https://image.slidesharecdn.com/8-160714105719/85/8-4-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[PostgreSQL]
Vacuum의 거의 모든 것(4차)
SELECT * from heap_page_items(get_raw_page('t2', 0));
Page Layout ( 1/2 )
Dump
0.
00 7c 9f c0 00 7c 9f 80](https://image.slidesharecdn.com/8-160714105719/85/8-5-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[PostgreSQL]
Vacuum의 거의 모든 것(4차)
SELECT * from heap_page_items(get_raw_page('t2', 0));
create table t2 ( c1 char(19),c2 char(8),c3 char(8) );
insert into t2 values('A1001','A','A');
insert into t2 values('A1002','A','A');
Dump
all line pointers on a heap page
1.](https://image.slidesharecdn.com/8-160714105719/85/8-6-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[PostgreSQL]
Vacuum의 거의 모든 것(4차)
SELECT * from heap_page_items(get_raw_page('t2', 0));
update t2 set c2='B' where c1 = 'A1001' ;
Dump
2.
새로운 위치에
변경데이타 “B” 레코드를 추가.
ItemIdData 부분도 추가됨.
“A1001” 원본은 “xmax” 값을 변경](https://image.slidesharecdn.com/8-160714105719/85/8-7-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[PostgreSQL]
Vacuum의 거의 모든 것(4차)
update t2 set c2='B' where c1 = 'A1001' ;
tab.sql
2.
select xmin,xmax,ctid,* from t1;
select txid_current() ;
select xmin,xmax,ctid,* from t2;
“A1001” item 의 xmin 변경됨.](https://image.slidesharecdn.com/8-160714105719/85/8-8-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[PostgreSQL]
Vacuum의 거의 모든 것(4차)
SELECT * from heap_page_items(get_raw_page('t2', 0));
vacuum t2 ;
Dump
3.
“순서가 변경됨”
• A1002가 제일 아래로 내려감
• A1001 위치도 아래로 변경
• A1001 원래 위치의 데이터는 그대로
두고 ItemIdData만 삭제.](https://image.slidesharecdn.com/8-160714105719/85/8-9-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[PostgreSQL]
Vacuum의 거의 모든 것(4차)
vacuum t2 ;
tab.sql
3.
select xmin,xmax,ctid,* from t1;
select txid_current() ;
select xmin,xmax,ctid,* from t2;
변경안됨](https://image.slidesharecdn.com/8-160714105719/85/8-10-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[PostgreSQL]
Vacuum의 거의 모든 것(4차)
vacuum freeze t2 ;
tab.sql
4.
select xmin,xmax,ctid,* from t1;
select xmin,xmax,ctid,* from t2;
1807012522에서 변경됨](https://image.slidesharecdn.com/8-160714105719/85/8-11-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[PostgreSQL]
Vacuum의 거의 모든 것(4차)
vacuum full t2 ;
tab.sql
5.
select xmin,xmax,ctid,* from t1;
select xmin,xmax,ctid,* from t2;
136677에서 변경됨 변경안됨](https://image.slidesharecdn.com/8-160714105719/85/8-12-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[PostgreSQL]
Vacuum의 거의 모든 것(4차)
vacuum full t2 ;
Dump
5.](https://image.slidesharecdn.com/8-160714105719/85/8-13-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[PostgreSQL]
Vacuum의 거의 모든 것(4차)
autovacuum_analyze_scale_factor = 0.1
autovacuum_analyze_threshold = 50
6.
1. 1000건 insert
2. autovacuum_naptime=60s 이상 wait 후 확인 : autoanalyze OK.
3. autovacuum_analyze_scale_factor=0.1 인 100건 insert wait 후 확인 : autoanalyze NOT OK.](https://image.slidesharecdn.com/8-160714105719/85/8-14-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[PostgreSQL]
Vacuum의 거의 모든 것(4차)
autovacuum_analyze_scale_factor = 0.1
autovacuum_analyze_threshold = 50
6.
4. autovacuum_analyze_threshold=50 인 50건 insert wait 후 확인 : autoanalyze NOT OK.
5. Only 1건 insert wait 후 확인 : autoanalyze OK.
autovacuum analyze 대상 조건
변경건수(insert포함) > ( reltuples * 0.1(autovacuum_analyze_scale_factor) )
+ 50(autovacuum_analyze_scale_factor)](https://image.slidesharecdn.com/8-160714105719/85/8-15-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[PostgreSQL]
Vacuum의 거의 모든 것(4차)
autovacuum_vacuum_scale_factor = 0.2
autovacuum_vacuum_threshold = 50
7.
1. 1000건 insert wait 후 확인 : autovacuum NOT OK.
2. autovacuum_vacuum_scale_factor=0.2 인 200건 update wait 후 확인 : autovacuum NOT OK.](https://image.slidesharecdn.com/8-160714105719/85/8-16-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[PostgreSQL]
Vacuum의 거의 모든 것(4차)
autovacuum_vacuum_scale_factor = 0.2
autovacuum_vacuum_threshold = 50
7.
3. autovacuum_vacuum_threshold=50 인 50건 update wait 후 확인 : autovacuum NOT OK.
4. Only 1건 update wait 후 확인 : autovacuum OK.
autovacuum vacuum 대상 조건
변경건수(insert제외) > ( reltuples * 0.2(autovacuum_vacuum_scale_factor) )
+ 50(autovacuum_vacuum_threshold)](https://image.slidesharecdn.com/8-160714105719/85/8-17-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
[MySQL] Lock (1차)
발표자: 연구컨텐츠팀 이대덕](https://image.slidesharecdn.com/8-160714105719/85/8-18-320.jpg)
![02. [MySQL] MySQL Lock
2-1. Global Read Lock
2-2. Table Lock
2-3. String Lock
2-4. Name Lock
Table of Agenda](https://image.slidesharecdn.com/8-160714105719/85/8-19-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
(root@localhost)[(none)] 13:48:51>show status like 'open_tables';
+---------------+-------+
| Variable_name | Value |
+---------------+-------+
| Open_tables | 54 |
+---------------+-------+
1 row in set (0.00 sec)
(root@localhost)[(none)] 13:48:53>flush tables with read lock;
Query OK, 0 rows affected (9.06 sec)
(root@localhost)[(none)] 13:49:10>show status like 'open_tables';
+---------------+-------+
| Variable_name | Value |
+---------------+-------+
| Open_tables | 1 |
+---------------+-------+
1 row in set (0.00 sec)
(root@localhost)[(none)] 14:00:20>unlock tables;
Query OK, 0 rows affected (0.00 sec)
2-1. Global Read Lock](https://image.slidesharecdn.com/8-160714105719/85/8-21-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
(root@localhost)[exem_i] 13:32:41>select connection_id();
+-----------------+
| connection_id() |
+-----------------+
| 14286 |
+-----------------+
1 row in set (0.00 sec)
(root@localhost)[exem_i] 13:33:16>lock table foo write;
Query OK, 0 rows affected (10.97 sec)
2-1. Global Read Lock
(root@localhost)[(none)] 13:34:37>select connection_id();
+-----------------+
| connection_id() |
+-----------------+
| 13 |
+-----------------+
1 row in set (0.00 sec)
(root@localhost)[(none)] 13:34:44>flush tables with read lock;](https://image.slidesharecdn.com/8-160714105719/85/8-22-320.jpg)
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
2-1. Global Read Lock
(root@localhost)[exem_i] 13:33:34>show processlist;
+-------+------+-----------+--------+---------+------+------------------------------+----------------------------+
| Id | User | Host | db | Command | Time | State | Info |
+-------+------+-----------+--------+---------+------+------------------------------+----------------------------+
| 13 | root | localhost | NULL | Query | 20 | Waiting for global read lock | flush table with read lock |
| 14286 | root | localhost | exem_i | Query | 0 | starting | show processlist |
+-------+------+-----------+--------+---------+------+------------------------------+----------------------------+
2 rows in set (0.00 sec)](https://image.slidesharecdn.com/8-160714105719/85/8-23-320.jpg)
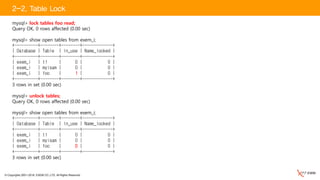
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
LOCK TABLES tbl_name [[AS] alias] lock_type [, tbl_name [[AS] alias] lock_type...
UNLOCK TABLES
• Lock_type : READ [LOCAL] | [LOW_PRIORITY] WRITE
• MySQL레벨에서 테이블 단위로 설정되는 LOCK
• MyISAM, MEMORY Storage Engine에서는 데이터를 변경하는 즉시 묵시적으로 획득 후 변경 후 반환
• 해당 테이블에 LOCK_TABLE 권한 필요
• 서버 레벨이지만 MyISAM스토리지 엔진을 기준으로 한 LOCK이며 InnoDB에서는 사용을 권장하지 않음
• READ LOCK :
해당세션과 다른 세션 모두 Select문장만 수행가능하며 Local 옵션을 사용 하는 경우 Concurrent Insert가능
다른 세션에서 획득한 READ LOCK끼리 호환가능
• WRITE LOCK :
해당 세션에서만 DML,DDL이 가능하며 다른 세션의 읽기,쓰기, TABLE LOCK과 호환불가
LOW_PRIORITY 옵션을 사용하는 경우 Lock 요청 큐에서 낮은 우선순위를 갖게 됨
2-2. Table Lock](https://image.slidesharecdn.com/8-160714105719/85/8-24-320.jpg)
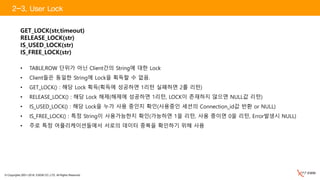
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
(root@localhost)[exem_i] 15:20:06>select connection_id();
+-----------------+
| connection_id() |
+-----------------+
| 14286|
+-----------------+
1 row in set (0.00 sec)
(root@localhost)[exem_i] 14:36:22>lock table foo read;
Query OK, 0 rows affected (0.00 sec)
(root@localhost)[exem_i] 14:36:51>select * from foo;
+------+------+
| c1 | c2 |
+------+------+
| 31 | a |
| 2 | b |
| 123 | a |
+------+------+
3 rows in set (0.00 sec)
(root@localhost)[exem_i] 14:36:57>update foo set c1=1 where c2='a';
ERROR 1099 (HY000): Table 'foo' was locked with a READ lock and can't be updated
2-2. Table Lock](https://image.slidesharecdn.com/8-160714105719/85/8-25-320.jpg)
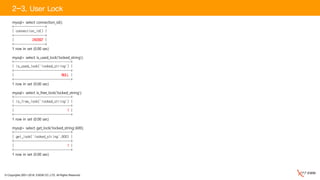
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
(root@localhost)[exem_i] 15:20:06>select connection_id();
+-----------------+
| connection_id() |
+-----------------+
| 13 |
+-----------------+
1 row in set (0.00 sec)
(root@localhost)[exem_i] 15:28:07>select * from foo;
+------+------+
| c1 | c2 |
+------+------+
| 31 | a |
| 2 | b |
| 123 | a |
+------+------+
3 rows in set (0.00 sec)
(root@localhost)[exem_i] 15:28:11>update foo set c1=1 where c2='a';
(root@localhost)[exem_i] 15:27:31>show processlist;
+-------+------+-----------+--------+---------+------+---------------------------------+----------------------------------+
| Id | User | Host | db | Command | Time | State | Info |
+-------+------+-----------+--------+---------+------+---------------------------------+----------------------------------+
| 13 | root | localhost | exem_i | Query | 15 | Waiting for table metadata lock | update foo set c1=1 where c2='a' |
| 14286 | root | localhost | exem_i | Query | 0 | starting | show processlist |
| 25063 | root | localhost | NULL | Sleep | 2833 | | NULL |
+-------+------+-----------+--------+---------+------+---------------------------------+----------------------------------+
3 rows in set (0.00 sec)
2-2. Table Lock](https://image.slidesharecdn.com/8-160714105719/85/8-26-320.jpg)
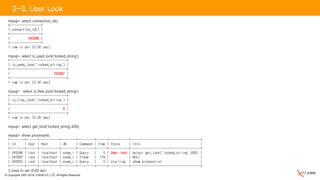
![© Copyrights 2001~2016, EXEM CO.,LTD. All Rights Reserved.
(root@localhost)[exem_i] 15:20:06>select connection_id();
+-----------------+
| connection_id() |
+-----------------+
| 13 |
+-----------------+
1 row in set (0.00 sec)
(root@localhost)[exem_i] 15:34:08>lock table foo read;
Query OK, 0 rows affected (0.00 sec)
(root@localhost)[exem_i] 15:34:15>lock table foo write;
(root@localhost)[exem_i] 15:31:58>show processlist;
+-------+------+-----------+--------+---------+------+---------------------------------+----------------------+
| Id | User | Host | db | Command | Time | State | Info |
+-------+------+-----------+--------+---------+------+---------------------------------+----------------------+
| 13 | root | localhost | exem_i | Query | 5 | Waiting for table metadata lock | lock table foo write |
| 14286 | root | localhost | exem_i | Query | 0 | starting | show processlist |
| 31080 | root | localhost | NULL | Sleep | 147 | | NULL |
+-------+------+-----------+--------+---------+------+---------------------------------+----------------------+
3 rows in set (0.00 sec)
2-2. Table Lock](https://image.slidesharecdn.com/8-160714105719/85/8-27-320.jpg)