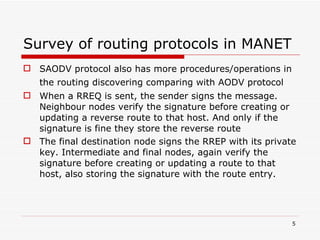
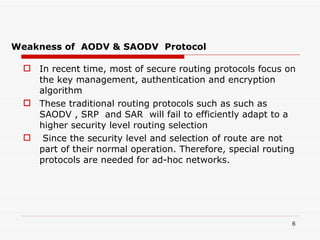
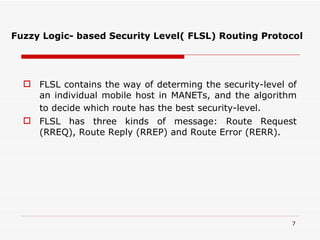
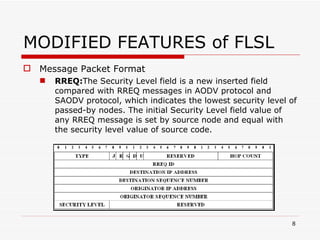
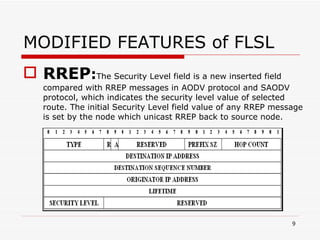
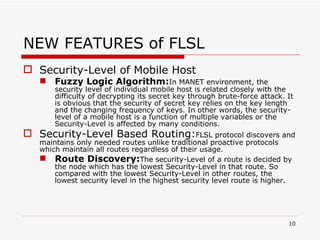
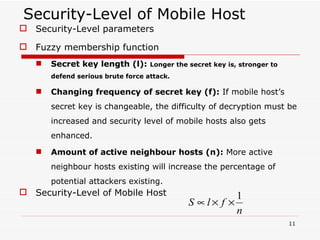
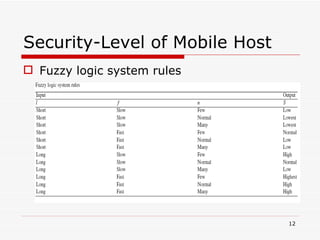
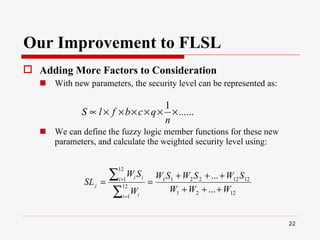
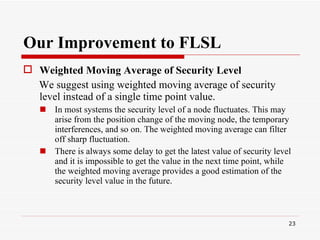
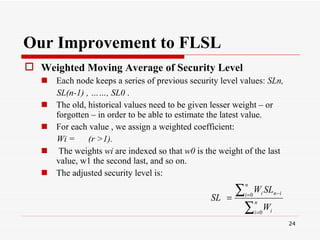
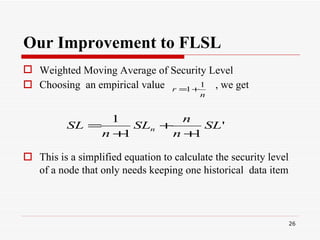
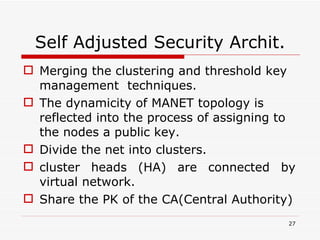
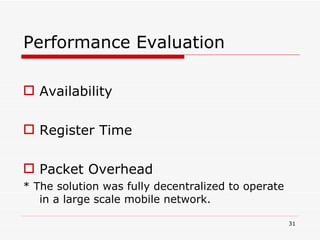
The document presents a survey of security and privacy in mobile ad-hoc networks (MANETs) with a focus on routing protocols such as AODV and its extension SAODV, highlighting their security weaknesses. It introduces a fuzzy logic-based security level (FLSL) routing protocol, emphasizing its advantages over traditional protocols and proposing improvements to enhance its effectiveness, such as incorporating additional factors for security assessment. Finally, the paper discusses the development of a self-adjusted security architecture and the challenges faced in implementing security measures within the dynamic topology of MANETs.
![MANET Topology: Security… Certificate-based authentication scheme Distributed authentication [ T ] Resource awareness [ T ] Efficient certificate [ T ] Heterogeneous certification [ T ] Robust pre-authentication mechanism [ T ]](https://image.slidesharecdn.com/564patelmokbelshushanzsurveyslides-110123011341-phpapp01/85/564-patel-mokbel_shushanz_survey_slides-28-320.jpg)
![References [ 1 ] Jing Nie, JiangchuaWen, Ji Luo, Xin He, Zheng Zhou, 2006, An adaptive fuzzy logic based secure routing protocol in mobile ad hoc networks, Fuzzy Sets and Systems [ 2 ] Lu Jin, Zhongwei Zhang and Hong Zhou, Deliberation and Implementation of Adaptive Fuzzy Logic Based Security Level Routing Protocol for Mobile Ad Hoc Network, Consumer Communications and Networking Conference, 2007 [ 3 ] AZ Ghalwash, AAA Youssif, SM Hashad, R Doss, 2007, Self Adjusted Security Architecture for Mobile Ad Hoc Networks, 6th IEEE/ACIS International Conference on Computer and Information Science (ICIS 2007) pp. 682-687 [ 4 ] P.Zimmermnn , "The Official PGP usrs guide", MIT Press, 1995](https://image.slidesharecdn.com/564patelmokbelshushanzsurveyslides-110123011341-phpapp01/85/564-patel-mokbel_shushanz_survey_slides-38-320.jpg)