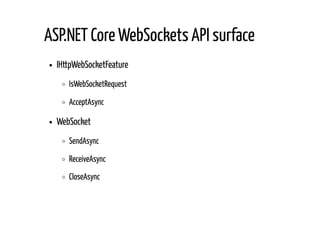
The document covers real-time capabilities in ASP.NET Core web applications, focusing on techniques such as WebSockets, Server-Sent Events (SSE), and push notifications. It details the implementation of WebSocket connections and middleware for handling real-time data, along with security considerations and performance implications. Additionally, it discusses subscribing to push notifications and the use of JSON Web Tokens for authentication in web push scenarios.

![public async Task ReceiveMessagesUntilCloseAsync()
{
byte[] receivePayloadBuffer = new byte[_receivePayloadBufferSize];
WebSocketReceiveResult webSocketReceiveResult =
await _webSocket.ReceiveAsync(new ArraySegment<byte>(receivePayloadBuffer),
CancellationToken.None);
while (webSocketReceiveResult.MessageType != WebSocketMessageType.Close)
{
if (webSocketReceiveResult.MessageType == WebSocketMessageType.Binary)
{
byte[] webSocketMessage = await ReceiveMessagePayloadAsync(webSocketReceiveResult,
receivePayloadBuffer);
ReceiveBinary?.Invoke(this, webSocketMessage);
}
else
{
byte[] webSocketMessage = await ReceiveMessagePayloadAsync(webSocketReceiveResult,
receivePayloadBuffer);
ReceiveText?.Invoke(this, Encoding.UTF8.GetString(webSocketMessage));
}
webSocketReceiveResult =
await _webSocket.ReceiveAsync(new ArraySegment<byte>(receivePayloadBuffer),
CancellationToken.None);
}
CloseStatus = webSocketReceiveResult.CloseStatus.Value;
CloseStatusDescription = webSocketReceiveResult.CloseStatusDescription;
}
Receiving loop in details](https://image.slidesharecdn.com/real-timecapabilitiesinasp-180621074346/85/4Developers-2018-Real-time-capabilities-in-ASP-NET-Core-web-applications-Tomasz-Peczek-8-320.jpg)
![private static async Task<byte[]> ReceiveMessagePayloadAsync(
WebSocketReceiveResult webSocketReceiveResult, byte[] receivePayloadBuffer)
{
byte[] messagePayload = null;
if (webSocketReceiveResult.EndOfMessage)
{
messagePayload = new byte[webSocketReceiveResult.Count];
Array.Copy(receivePayloadBuffer, messagePayload, webSocketReceiveResult.Count);
}
else
{
using (MemoryStream messagePayloadStream = new MemoryStream())
{
messagePayloadStream.Write(receivePayloadBuffer, 0, webSocketReceiveResult.Count);
while (!webSocketReceiveResult.EndOfMessage)
{
webSocketReceiveResult =
await _webSocket.ReceiveAsync(new ArraySegment<byte>(receivePayloadBuffer),
CancellationToken.None);
messagePayloadStream.Write(receivePayloadBuffer, 0, webSocketReceiveResult.Count);
}
messagePayload = messagePayloadStream.ToArray();
}
}
return messagePayload;
}
Receiving loop in details](https://image.slidesharecdn.com/real-timecapabilitiesinasp-180621074346/85/4Developers-2018-Real-time-capabilities-in-ASP-NET-Core-web-applications-Tomasz-Peczek-9-320.jpg)
![public async Task ReceiveMessagesUntilCloseAsync()
{
try
{
byte[] receivePayloadBuffer = new byte[_receivePayloadBufferSize];
WebSocketReceiveResult webSocketReceiveResult =
await _webSocket.ReceiveAsync(new ArraySegment<byte>(receivePayloadBuffer),
CancellationToken.None);
while (webSocketReceiveResult.MessageType != WebSocketMessageType.Close)
{
...
webSocketReceiveResult =
await _webSocket.ReceiveAsync(new ArraySegment<byte>(receivePayloadBuffer),
CancellationToken.None);
}
CloseStatus = webSocketReceiveResult.CloseStatus.Value;
CloseStatusDescription = webSocketReceiveResult.CloseStatusDescription;
}
catch (WebSocketException wsex)
when (wsex.WebSocketErrorCode == WebSocketError.ConnectionClosedPrematurely)
{
// Maybe perform some logging
}
}
Receiving loop in details](https://image.slidesharecdn.com/real-timecapabilitiesinasp-180621074346/85/4Developers-2018-Real-time-capabilities-in-ASP-NET-Core-web-applications-Tomasz-Peczek-10-320.jpg)
![private static Task SendAsync(WebSocket webSocket, byte[] message,
WebSocketMessageType messageType, bool endOfMessage, CancellationToken cancellationToken)
{
ArraySegment<byte> messageSegment = new ArraySegment<byte>(message, 0, message.Length);
return _webSocket.SendAsync(messageSegment, messageType, endOfMessage, cancellationToken);
}
How about sending messages?](https://image.slidesharecdn.com/real-timecapabilitiesinasp-180621074346/85/4Developers-2018-Real-time-capabilities-in-ASP-NET-Core-web-applications-Tomasz-Peczek-11-320.jpg)



![public class ServerSentEventsMiddleware
{
private readonly RequestDelegate _next;
private readonly IServerSentEventsConnectionsService _connectionsService;
public ServerSentEventsMiddleware(RequestDelegate next,
IServerSentEventsConnectionsService connectionsService)
{
_next = next ?? throw new ArgumentNullException(nameof(next));
_connectionsService = connectionsService
?? throw new ArgumentNullException(nameof(connectionsService));
}
public async Task Invoke(HttpContext context)
{
if (context.Request.Headers["Accept"] == "text/event-stream")
{
IHttpBufferingFeature bufferingFeature = context.Features.Get<IHttpBufferingFeature>();
if (bufferingFeature != null)
{
bufferingFeature.DisableResponseBuffering();
}
response.ContentType = "text/event-stream";
await response.Body.FlushAsync();
ServerSentEventsConnection serverSentEventsConnection = new ServerSentEventsConnection(
Guid.NewGuid(), context.User, context.Response);
_connectionsService.AddClient(client);
await context.RequestAborted.WaitAsync();
_connectionsService.RemoveClient(serverSentEventsConnection.Id);
}
else
{
await _next(context);
}
}
SSE middleware implementation](https://image.slidesharecdn.com/real-timecapabilitiesinasp-180621074346/85/4Developers-2018-Real-time-capabilities-in-ASP-NET-Core-web-applications-Tomasz-Peczek-18-320.jpg)



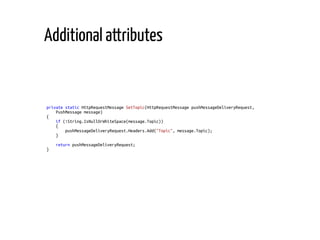
![private static HttpRequestMessage SetUrgency(HttpRequestMessage pushMessageDeliveryRequest,
PushMessage message)
{
switch (message.Urgency)
{
case PushMessageUrgency.Normal:
break;
case PushMessageUrgency.VeryLow:
case PushMessageUrgency.Low:
case PushMessageUrgency.High:
pushMessageDeliveryRequest.Headers
.Add("Urgency", _urgencyHeaderValues[message.Urgency]);
break;
default:
throw new NotSupportedException($"Not supported {nameof(PushMessageUrgency)}.");
}
return pushMessageDeliveryRequest;
}
Additional attributes](https://image.slidesharecdn.com/real-timecapabilitiesinasp-180621074346/85/4Developers-2018-Real-time-capabilities-in-ASP-NET-Core-web-applications-Tomasz-Peczek-33-320.jpg)