The document is a SafeAssign originality report for an IT security policy assignment submitted by Ruthvik Reddy Gidde at New England College, indicating a 75% match to other student papers. It outlines various components of the IT security policy, including data classification, consequences of data handling, and mobile device and network security policies. The assignment also includes various analysis tasks related to pricing strategies in an oligopoly market scenario for a course evaluation.

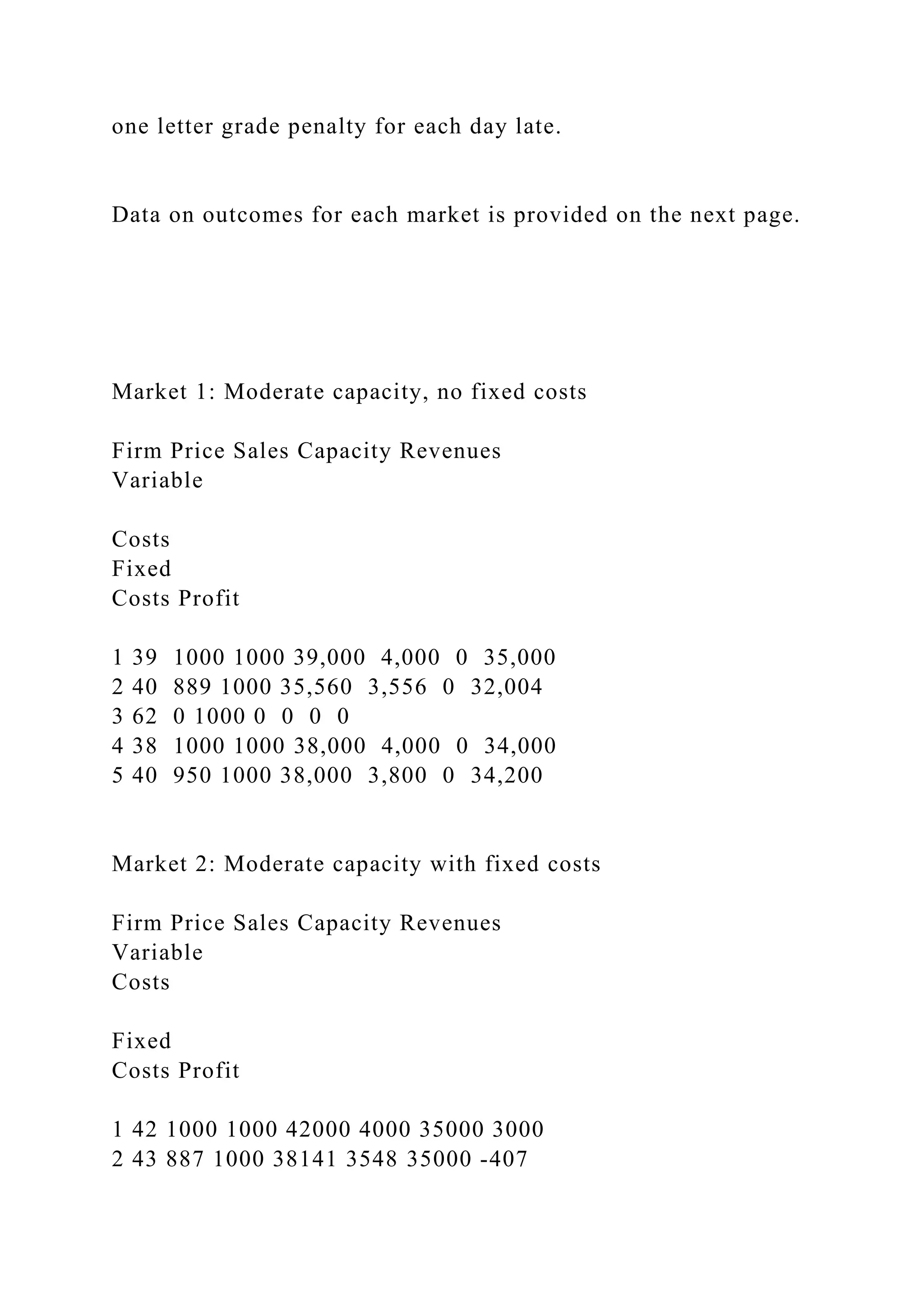
![observed value). Consider two strategies for Firm 1: “matching”
the price charged by its
active rivals by setting �. = �, or “undercutting” all three
active rivals by reducing price
by $1 to �. = � − 1. Bearing in mind Firm 1’s capacity
constraints, what is the *highest*
price � on the demand schedule at which Firm 1 prefers to
match than undercut? How
does this price vary with the capacity constraint �? And what
does this tell you about
Nash equilibrium prices in each market?
[Hint: For a price � to be a symmetric Nash equilibrium, it
must be that no for-profit
firm prefers to undercut when all for-profit rivals charge the
given price. In this
particular game there may in general be many Nash equilibria,
but from the firms’
perspective the best equilibrium will be the one with the highest
price.]
Evaluation: This assignment will count for 10 percent of your
final course grade. In your
answers, I will be looking for a clear discussion of both the key
economic and strategic issues
governing competition in this market, and how predictions of
the underlying theory fit (or
don’t!) the actual prices observed. Note that data *will not* line
up with theory on every
dimension, although in some key dimensions it should. Long
answers are not necessarily better;
the key is to identify and analyze the core questions involved.
Submissions are due via Canvas at midnight on Friday, April
10. Late submissions will receive a](https://image.slidesharecdn.com/492020safeassignoriginalityreporthttpsblackboard-221009213308-60b0c483/75/492020-SafeAssign-Originality-Reporthttpsblackboard-n-19-2048.jpg)