3 Understand the ethical and legislative environment relating to IT
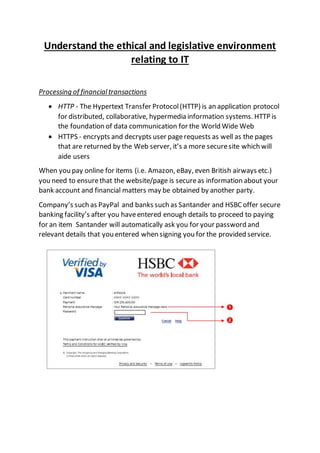
- 1. Understand the ethical and legislative environment relating to IT Processing of financialtransactions HTTP - The Hypertext Transfer Protocol(HTTP) is an application protocol for distributed, collaborative, hypermedia information systems. HTTP is the foundation of data communication for the World Wide Web HTTPS - encrypts and decrypts user pagerequests as well as the pages that are returned by the Web server, it’s a more securesite which will aide users When you pay online for items (i.e. Amazon, eBay, even British airways etc.) you need to ensurethat the website/page is secureas information about your bank account and financial matters may be obtained by another party. Company’s such as PayPal and banks such as Santander and HSBC offer secure banking facility’s after you haveentered enough details to proceed to paying for an item Santander will automatically ask you for your password and relevant details that you entered when signing you for the provided service.
- 2. Tips to aide finacial transactionsonline for companysor personaluse (helping to prevent preventfraud) Check privacy policy of the website your are using Log out of any site you haveregistered closing down you internet browser isntenough to ensureprivacy Keep all electronic recipts or other wisemaderecipts Check for payment in bank statements check for the padlock symbolin the browser noton the screen it may be a fradulent site If using the latest internet browser a trusted site will turn green Pad lock symbol HTTPS secure Trusted site (green address)
- 3. Health and safety Health and safety at work act The Health and Safety at Work etc Act 1974 (also referred to asHSWA, the HSW Act, the 1974 Actor HASAWA) is the primary piece of legislation covering occupationalhealth and safety in GreatBritain. The Health and Safety Executive, with local authorities(and other enforcing authorities) is responsible for enforcing the Act and a number of other Actsand Statutory Instruments relevant to the working environment. When regarding the health and safety aspect of any work environmentthere are strict guidelines that every employee/employer mustfollow and have in place in order to facilitate and promote a safe working environment. Example – the army over the last 13-14 years has been engaged in conflicts in Iraq and Afghanistan, to combat injury`s sustained from any form of incident, be it enemy fire such as explosions or IEDS on operations or vehicle related incidents (collisions etc.) to general training in the UK, the army provideits soldiers with whatis now common called PPEwhich outsideof the army also has the same name but differs depending on what the nature of the job is and the inherent risk it represents. Army PPE- Ballistic helmets Ballistic googles Osprey plate carrier complete with flak jacketinner Durable leather gloves Knee pads Blast resistant under wear and bomb nappy (tier 1 and 2 pelvic protection) Boots and clothing depending of the nature of the environmentsuch as hot and cold climates First aid medicalequipment Blast resistant vehicles These are but a few but it provides a generalunderstanding of health and safety at work all be it a bit extreme
- 4. full PPEworn by yours truly as stated abovethee PPE is down to the nature of the job. Which should be supplied by the employee`s employer. But in the general work placesay a call centre who`s employees are using telephones and computers all day would requirea differenttype of health and safety procedure - Lumbar supporting chairs to preventback injury or ache from being sat in a chair during working hours All electrical devices (phones, computers etc.) mustbe properly earthed All cables and wires must be correctly stowed or placed away correctly in order to preventa trip hazard(s) Accessibleroutes to and from work stations including fire exits and stair wells Firstaid trained members of staff and firstaid stations Fire prevention equipment such as fire extinguishers with the correct type of incident (dry powder, water co2) Fire muster points Emergency alarms A correctand accurate safety brief/meeting delivered to all employee’s Not adhering to any of these basic principles could result in legal action being carried out
- 5. Fines Fixed penalty’s Compensation claims Termination of employment Imprisonment Below are listed acts that are owned and enforced by the HSE which can be found on http://www.hse.gov.uk/legislation/acts.htm Privacy, confidentiality and security Privacy- in a ITor online context allows an individual to Determine what information about them is collected and how it is used Access information about them knowing that it is safe Not having web habits tracked (anonymity) Send and receive emails and messages securely in the knowledgethat they will not be intercepted/red by another party other than the sender and recipient Confidentiality – keeping information secure and secretfrom others, And in an ITenvironment Confidentiality is reinforced by the data protection act 1998 An ethical duty (i.e. between two people, employer and employee) Having computers with confidential information stored on them in a secure, locked a safearea Be awarethat emails can be intercepted
- 6. Implement correctsecurity measures when preparing to send personalinformation Security Statute Year Subject Guidance Explosives Act 1875 (c. 17) 1875 Explosives No specific guidance available Employment of Women, Young Persons, and Children Act 1920 (c. 65) 1920 Workers No specific guidance available Mines and Quarries Act 1954 (c. 70) 1954 Mining No specific guidance available Agriculture (Safety, Health and Welfare Provisions) Act 1956 (c. 49) 1956 Agriculture No specific guidance available Factories Act 1961 (c. 34) 1961 Factories No specific guidance available Pipe-lines Act 1962 (c. 58) 1962 Offshore No specific guidance available Offices, Shops and Railway Premises Act 1963 (c. 41) 1963 Businesses No specific guidance available Mines and Quarries (Tips) Act 1969 (c. 10) 1969 Mining No specific guidance available Mineral Workings Offshore Installations Act 1971 (c. 61) 1971 Mining No specific guidance available Employment Medical Advisory Service Act 1972 (c. 28) 1972 Health services No specific guidance available Health and Safety at Work etc Act 1974 (c. 37) 1974 Businesses No specific guidance available Environment and Safety Information Act 1988 (c. 30) 1988 Chemicals No specific guidance available Offshore Safety Act 1992 (c. 15) 1992 Offshore No specific guidance available Health and Safety (Offences) Act 2008 (c.20) 2008 Enforcement No specific guidance available
- 7. For an ITenvironment this would refer to Secure locations of stored information Up to date internet security (i.e. MacAfee antivirus software) Apporatiate network security Fire wall safeguards Correctmaintenance Reporting anything suspicious aboutthe nature of the information’s stowagedevice (i.e. May havebeen have had unauthorized usage/tampering) In order to make surethat the security of any information is securewould fall in to the data protection act 1998 for which there are severalguidelines. Copyrightand intellectualproperty rights Intellectual property refers to a creative work which can be assetor physical property. Intellectual property rights fall mainly into four main areas, copyright, trademarks, design rights and patents Intellectual property is something unique that you have physically created the idea alone is not intellectual property. For example an idea for a book is not intellectual property however the words you havewritten in it are. Copyright, patents, designs and trademarks areall types of intellectual property protection. Your intellectual property is either protected automatically from theft or copying. By knowing the rights involved and having the correct type of protection you can prevent other parties fromstealing or copying the names of your products or brands your inventions the design or look of your products things you write, make or produce Copyright Copyrightapplies to work that is recorded in some way the rights exist in items such as literary, artistic, musicaland dramatic work as well such as films and
- 8. music and. Itgives the author(s) a specific set of rights in relation to their work and prohibits any unauthorised actions, and allows the author(s) to take legal action against instances of infringement or plagiarism