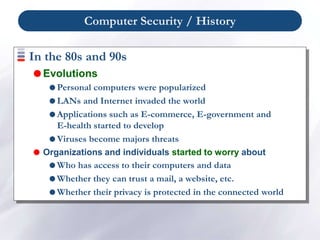
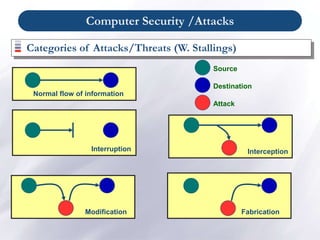
The document provides an overview of computer security and privacy. It discusses the history of computer security from the 1960s to present day, highlighting some famous security problems such as the Morris worm in 1988. It defines key computer security terms and concepts such as threats, vulnerabilities, and countermeasures. It also examines different types of computer security attacks including hacking, denial of service attacks, malware, viruses, worms, and Trojan horses. The document outlines security measures related to physical security, network security, and the importance of the human factor in computer security.


















![Computer Security / Physical Security
Physical security protects your physical computer
facility (your building, your computer room, your
computer, your disks and other media) [Chuck
Easttom].
Physical security is the use of physical controls to
protect premises, site, facility, building or other
physical asset of an organization [Lawrence Fennelly]](https://image.slidesharecdn.com/chapter1-230620101941-0437dd85/85/Chapter-1-ppt-21-320.jpg)