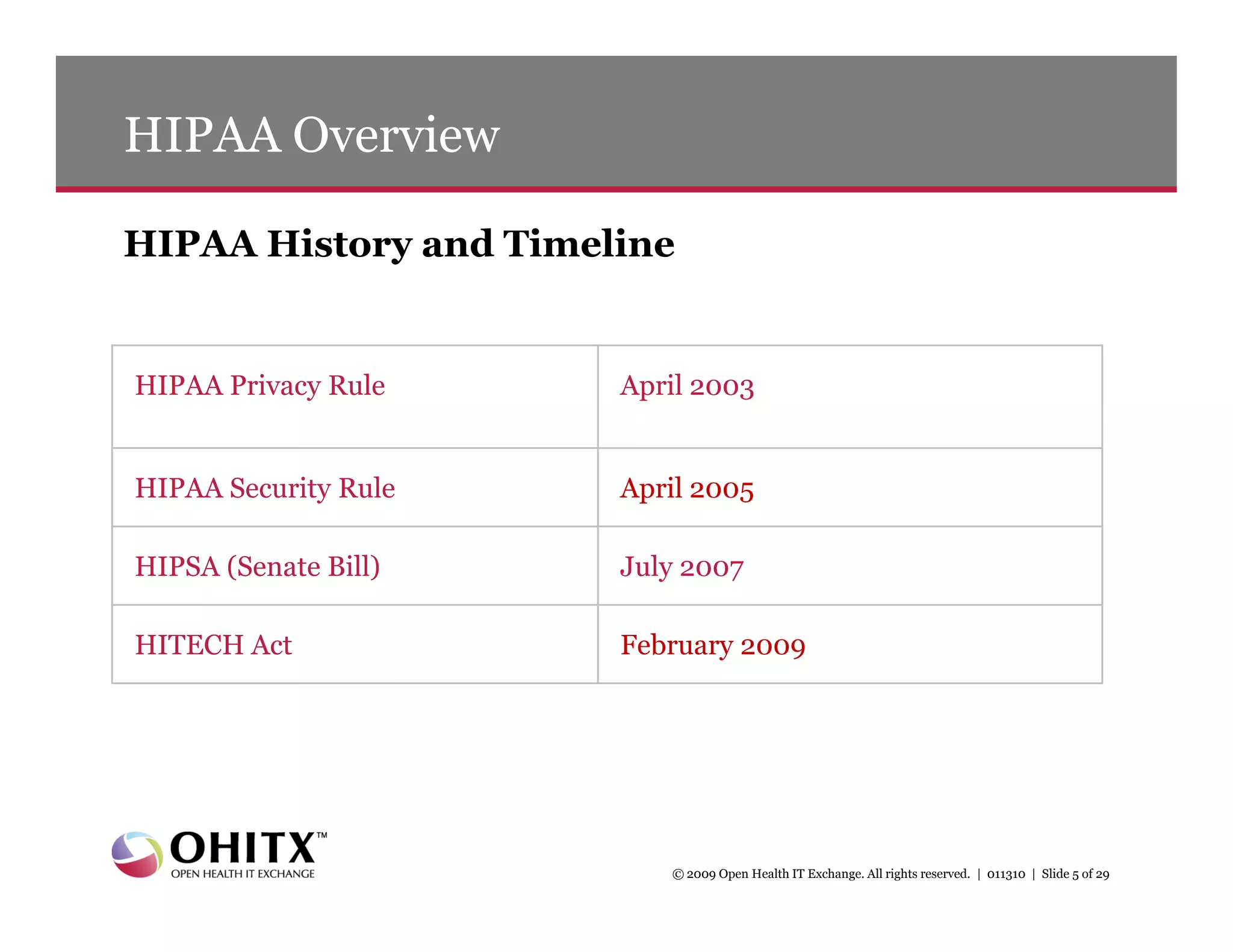
This document summarizes a presentation about new HIPAA privacy and security requirements under the HITECH Act. It includes:
1) An agenda that covers HITECH Act requirements, new privacy and security provisions, breach notification rules, and resources.
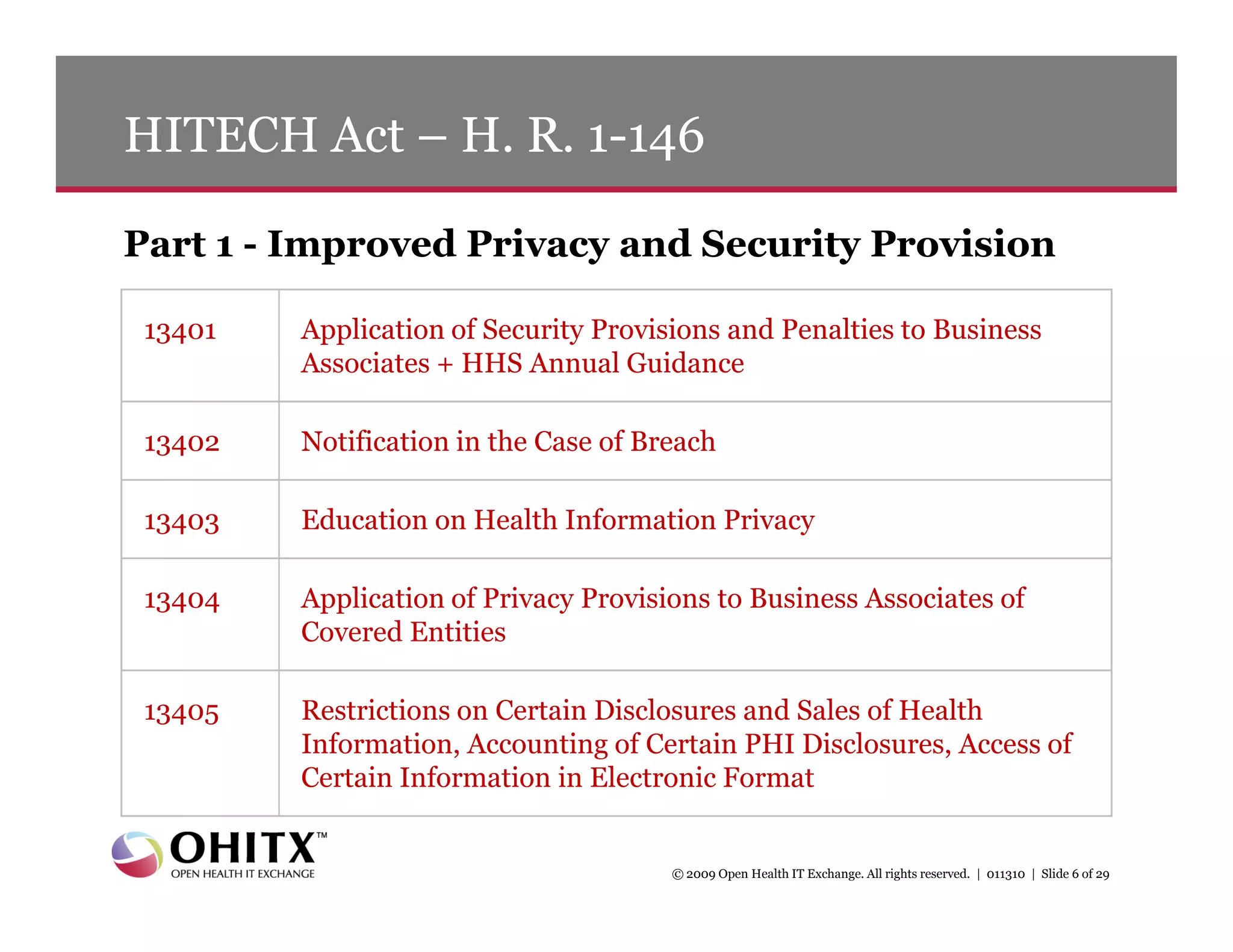
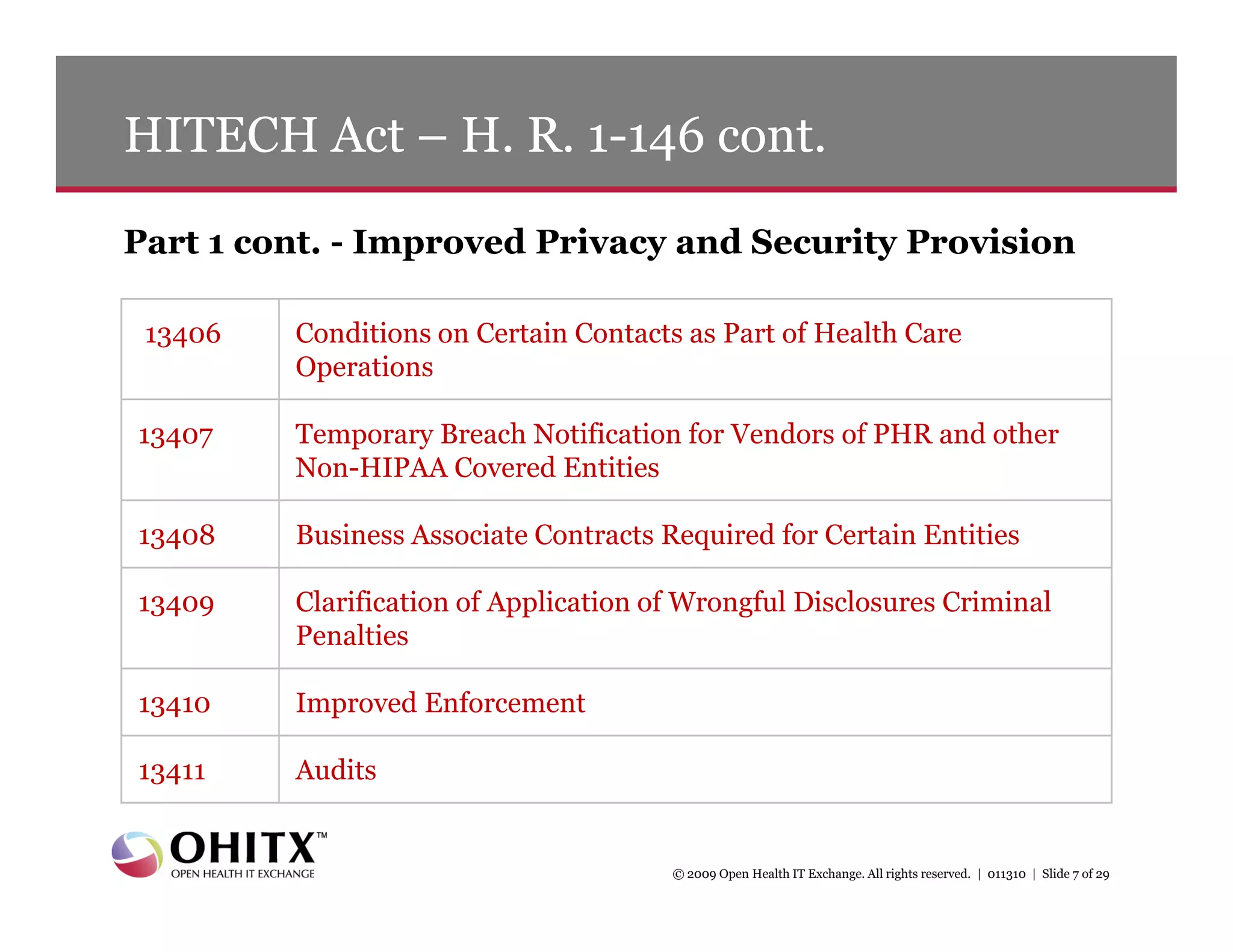
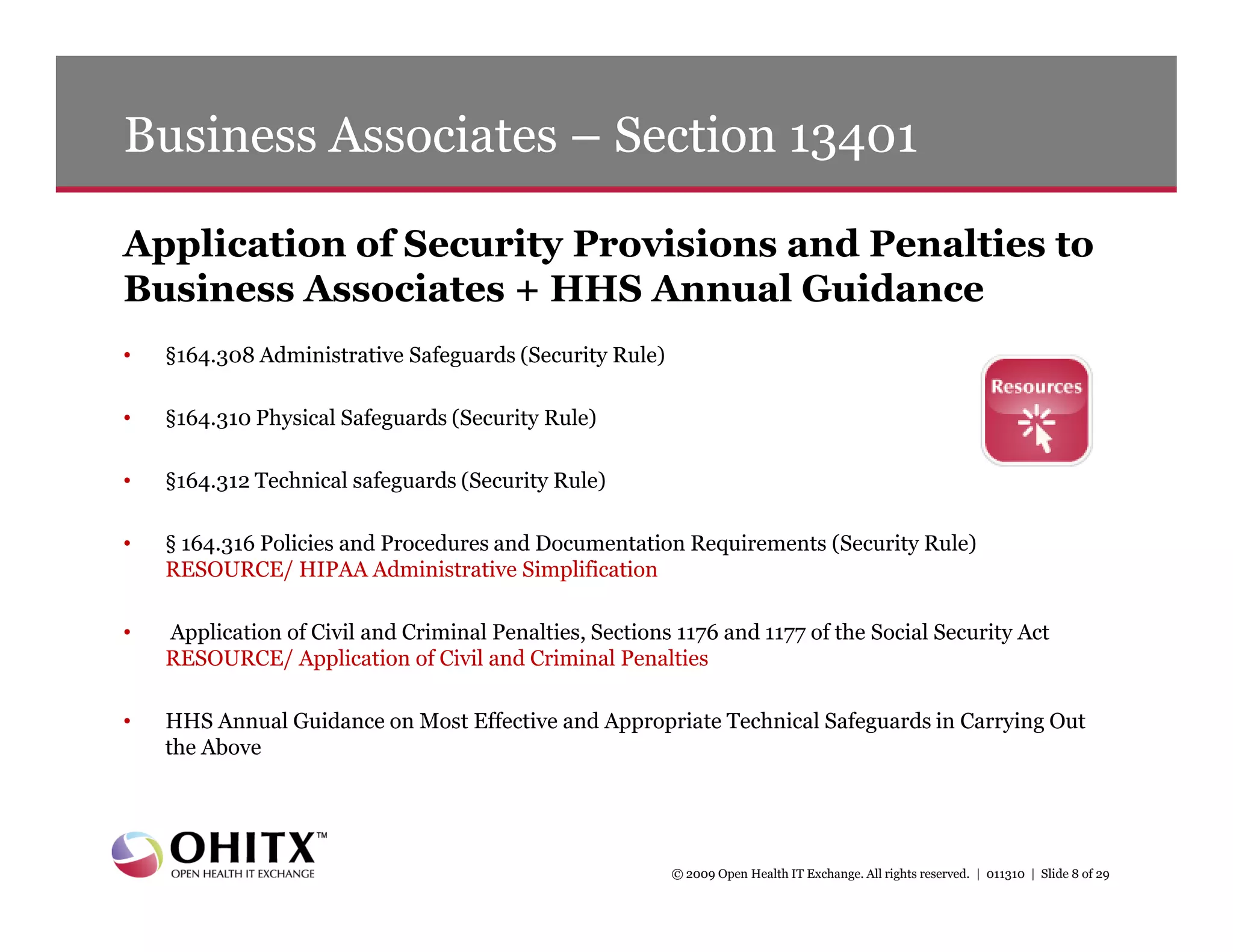
2) An overview of key sections of the HITECH Act that apply security rules and penalties to business associates, require breach notification, improve privacy enforcement, and restrict certain disclosures of protected health information.
3) Details on new breach notification rules under the HITECH Act that require notification of breaches of unsecured health information within 60 days.
![Breach Notification – Section 13402 cont.
Following the discovery of a breach of unsecured PHI
• A covered entity must notify each individual whose unsecured PHI has been, or is
reasonably believed to have been, inappropriately accessed, acquired, or disclosed in
the breach [section 13402(a)]
• Additionally, following the discovery of a breach by a business associate, the business
associate must notify the covered entity of the breach and identify for the covered
entity the individuals whose unsecured PHI has been, or is reasonably believed to have
been, breached [section 13402(b)]
• The Act requires the notifications to be made without unreasonable delay but in no
case later than 60 calendar days after discovery of the breach
© 2009 Open Health IT Exchange. All rights reserved. | 011310 | Slide 11 of 29](https://image.slidesharecdn.com/2010hipaarules011310-12634217710619-phpapp01/75/2010-Hipaa-Rules-011310-11-2048.jpg)