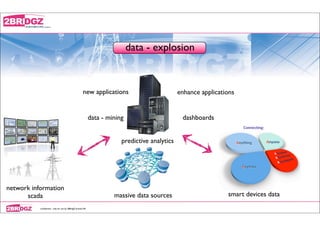
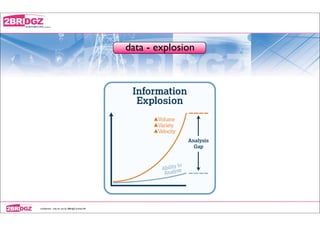
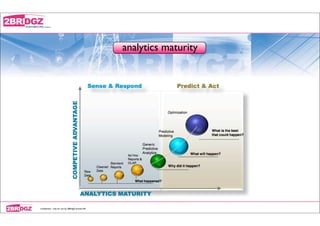
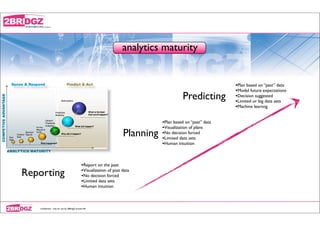
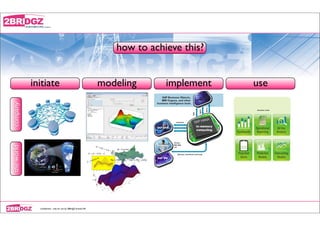
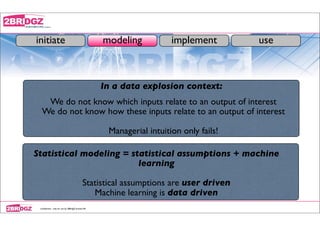
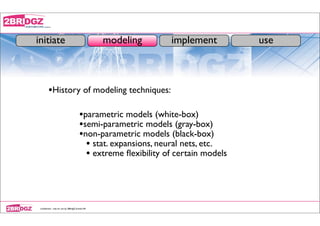
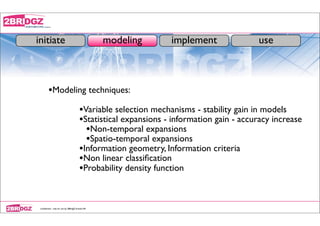
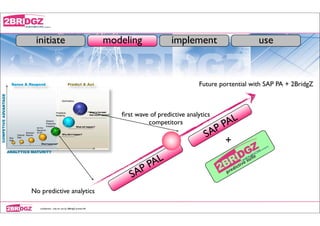
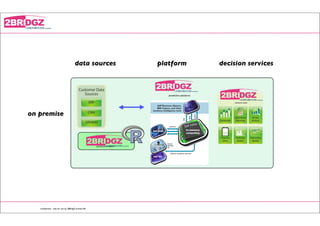
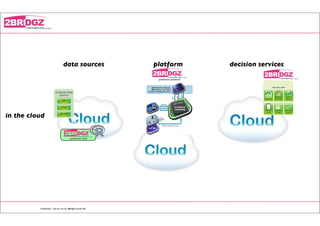
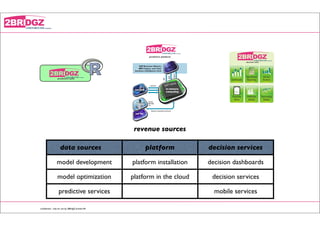
The document discusses predictive analytics and data-driven decision making. It notes that predictive modeling is necessary to make sense of large data sources, as managerial intuition alone is insufficient. Statistical and machine learning techniques can be used to develop predictive models from vast amounts of structured and unstructured data. Once developed, predictive models can be implemented on predictive platforms and used to power decision services and dashboards to guide business decisions. Revenue opportunities exist throughout the development and use of predictive analytics solutions.